On Presidential Powers to Destabilize Entire Regions
In his latest installment on Trump and the powers of the American presidency, Ben Wittes manages to avoid calling his adversaries delusional while making delusional arguments himself, which makes for a much more intriguing post. In this one, he shifts his focus to the topics his adversaries had originally focused on, which Wittes calls “U.S. arms and war powers” but which for the moment I’ll call “national security.”
Wittes argues that the degree of authority granted the President in matters of war is scary, but less scary than not having such a powerful President.
It was a few years ago, on a panel at American University’s Washington College of Law, that I heard Brad Berenson—who served in the White House Counsel’s office under President Bush—make an arresting statement about the American Presidency.
The Presidency, Berenson argued, is an office of terrifying power. There is no legal question—at least as a matter of domestic constitutional law—that the president has the authority to order a preemptive nuclear strike on Tehran. Indeed, there is really only one thing, Berenson said, that is scarier than a president who has such power in his sole command: a president who does not have that power.
[snip]
“Energy in the Executive,” wrote Hamilton, “is a leading character in the definition of good government. It is essential to the protection of the community against foreign attacks. . . .” The reason? “A feeble Executive implies a feeble execution of the government. A feeble execution is but another phrase for a bad execution; and a government ill executed, whatever it may be in theory, must be, in practice, a bad government.” Translation: If you want government to do things, you have to have an executive capable of it.
Wittes admits that presidency doesn’t have to be this way — indeed, that Israel, which he describes as “another democratic country that has ongoing security issues and fights wars semi-regularly” doesn’t have it. Me, I’d call Israel a partially democratic country that faces far greater security issues, but which has nevertheless thrived for 70 years without it. Which is another way of saying, right in the middle of his post arguing for the necessity of a unitary presidency, Wittes provides a counterargument that suggests that, at least in some circumstances (Israel has had a lot of help, after all), it’s not actually necessary.
Nevertheless, Wittes likes what we’ve got because it gives us decisiveness and accountability.
The American system has a lot to recommend it. It generates not merely decisiveness of action, but also political accountability for that action—what Hamilton called “a due dependence on the people” and “a due responsibility.” Divide up the executive authority and nobody really knows who gets credit for success and who gets blame for failure. Nobody is responsible for anything in Israel, for example. Give all the responsibility to one president, and that is not really a problem. Nobody doubts who is responsible for Obamacare, for example, or for the Iraq war.
It’s definitely true we know who to hold responsible for Obamacare. Getting into the Iraq War, too — though there’s far less certainty among the public about who is responsible for the failure to negotiate a SOFA, which led to the withdrawal timeline, and (arguably) to the resurgence of what would become ISIS. Both Obama and Bush get blamed.
But it’s an interesting argument particularly in light of Wittes’ prior dismissal of Conor Friedersdorf and Jennifer Granick’s concerns about drones and surveillance, because on those issues and many more, the Executive is shielded from much political and all legal accountability. Presidents have authorized a vast range of covert action over the years that have led to a great deal of blowback that they by definition cannot be held accountable for. Hell, as recently as 2013, the Executive was stone-walling SSCI member Ron Wyden about what countries we were conducting lethal counterterrorism operations in, and it took years of requests, starting before the Anwar al-Awlaki killing and continuing for some time after it, before Wyden was permitted to see the authorization for that.
No one may doubt who is responsible for Obamacare, but even select oversight committees, and especially voters, simply don’t know all the things they might want to hold a president accountable for.
And on the issues that (I think) Wittes would lump under “national security,” such secrecy, such unilateral power, actually may lead to rash and often stupid decisions. Setting aside what you think about the need for the President to have authority to order preemptive nuclear strikes (the “Bomb Power” that Garry Wills argues created the necessity for such secrecy), with such authority also comes the ability to create significant harms to the US by a thousand cuts of stupid covert action. We helped to create modern Sunni terrorism via such secret authority, after all.
Add in the fact that the Intelligence Community now claims cyberattacks are the biggest threat to the US. That’s an area where there has been a distinct lack of accountability, even after catastrophic failures.
But one thing never happens in either of those worlds: accountability.
On the national security side, I have long noted that people like then Homeland Security Czar John Brennan or Director of National Security Keith Alexander never get held responsible when the US gets badly pawned. The Chinese were basically able to steal the better part of the F-35 program, yet we still don’t demand good cyber practices from defense contractors or question the approach the NSA used on cyber defense. A few people lost their job because of the OPM hack, but not the people who have a larger mandate for counterintelligence or cybersecurity. Indeed, the National Security Council apparently considers cyber a third category, in addition to public safety and national security.
As a result, whereas we assume (wrongly) that we should expect the NatSec establishment to prevent all terrorist attacks, no one thinks to hold our NatSec establishment responsible if China manages to steal databases of all our cleared personnel.
Finally, our supposedly nimble presidency has been distinctly unable to act decisively in two areas that have been a bigger threat to the US than Iran or terrorism of late: financial recklessness and crime, and climate change. The reasons for inaction are dramatically different (though both have a lot to do with the way big money dominates our elections), but the effect is that the President has a lot of power to kill Americans in secret, but doesn’t wield that same power to prevent systemic catastrophes of another sort.
Wittes ends his piece by blaming the electorate — a stance I’m not unsympathetic with.
I want to suggest, in closing, that the problem here is not a structural flaw in the executive branch. That we are contemplating our fears of a Trump presidency reflects, rather, a flaw in the electorate that would contemplate his election and in the political leadership of one of our major political parties—leadership that prefers to back him than repudiate him. In a democracy, the people, generally speaking, get the president they ask for. And if the populace asks for an abusive, erratic, proudly ignorant figure of no coherent policy vision, it’s going to get that.
But I’m far more struck by this passage, which seems a much better argument for reversing some of what even Wittes admits has been growing power of the presidency.
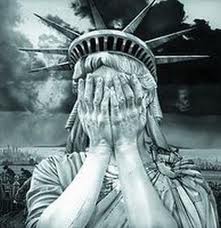
[I]n the ordinary course of business, nobody gets to remove from the hands of the president the vast powers that he lawfully wields: the power to destabilize regions, launch military adventures, abrogate agreements, and destroy alliances. These powers are inherent features of powers of the presidency, and they are inherent powers that we actively need.
Wittes argues we can’t impose any limits on the President (even ones that existed as recently as 15 years ago), because we need the ability to do stupid things with little oversight.
Given how damaging those powers have already been, in the hands of purportedly sane Presidents, why do we think we want to keep it that way?