After previous reporting had already claimed US credit for the kill,
A Cardiff man who is one of three from the city to have joined a jihadist group in Syria has died, BBC Wales has been told.
Reyaad Khan, 21, was killed in a US drone strike at the end of August.
And after the WaPo rolled out claims that our latest “secret” drone killing theater operates under new-and-improved rules,
The CIA and U.S. Special Operations forces have launched a secret campaign to hunt terrorism suspects in Syria as part of a targeted killing program that is run separately from the broader U.S. military offensive against the Islamic State, U.S. officials said.
[snip]
Hussain, the 21-year-old British militant killed last month, was moved toward the top of the target list after being linked to one of two gunmen killed in Garland, Tex., this year after opening fire at a cartoon contest that invited participants to draw pictures of the prophet Muhammad.
Hussain is not known to have been directly involved in the Islamic State’s gruesome beheadings of Western hostages or other violence. The decision to kill him makes clear that even militants involved only in the Islamic State’s media efforts are regarded as legitimate U.S. military targets.
In the past, the Obama administration has stressed that it was not targeting terrorism suspects involved only in propaganda. When Anwar al-Awlaki, an American cleric, was killed in Yemen in 2011, officials emphasized that he had become directly involved in terrorist operations.
A senior administration official said that Hussain “was more than a propagandist. He was actively involved in recruiting [Islamic State] sympathizers in the West to carry out attacks, and he was specifically focused on orchestrating operations targeting U.S. service members as well as government officials.”
Hussain was tracked in part by monitoring his online activities, according to officials who said that the British government had been consulted on the decision to make him a target.
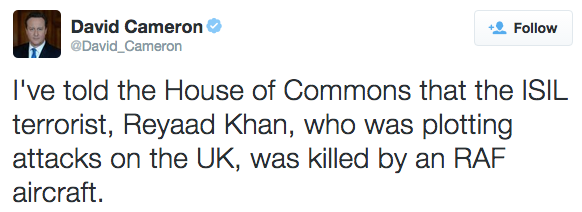
David Cameron has now claimed credit for killing.
The UK government ordered an RAF drone strike which targeted and killed two British Islamic State fighters in Syria last month, David Cameron has said.
Cardiff-born Reyaad Khan was targeted in Raqqa on 21 August and died alongside Ruhul Amin, from Aberdeen, and another fighter, the PM told MPs.
Khan, 21, had been plotting “barbaric” attacks on British soil, he said.
The “act of self defence” was lawful, Mr Cameron said, despite MPs previously ruling out UK military action in Syria.
Khan was killed in a precision strike by a remotely piloted aircraft, “after meticulous planning”, while he was travelling in a vehicle, the prime minister said.
Another British national, Junaid Hussain, from Birmingham, was killed in a separate air strike by US forces in Raqqa on 24 August, the prime minister confirmed.
Both had been planning to attack “high-profile public commemorations” taking place in the UK this summer, he said.
Lawyers on both sides of the Atlantic are already raising questions about the legality of this strike (and given European Human Rights law, it’s at least possible Cameron will have to offer more of an explanation than Obama has offered for killing Anwar al-Awlaki). I’m also interested in what has changed from the time when the UK stripped people of their nationality so we could drone kill them (as we’ve done repeatedly in Somalia). And why a country that was so sensitive about British Telecom’s role in drone operations in Djibouti is proudly announcing this now.
Is it because this strike helps to lay the case for more war-making in Syria?
But there’s something else I’m wondering. Who is flying what over Syria? The US and UK can’t fly drones without either Bashar al-Assad’s blessing or certainty what used to be considerable air defenses have been neutralized.
Moon of Alabama has been wondering the same thing too.
[T]he most curious issue in the piece is the description of the “drone” attack that helped to fend off attacking Nusra fighters. No drone I am aware of and certainly not the “Predator” are equipped with automatic weapons like machine guns. The Drones carry fire-and-forget missiles or bombs but no drone has the necessarily heavy rotating tower and swiveling weapon holder that would allow the use of automatic weapons. “Automatic fire from the sky” as the reporter describes from the video he has seen can only have come from manned helicopters. Or is there some other explanation that I miss?
If there were helicopters who’s birds were these? U.S. or Turkish? Are there more of these flying over Syria and to what purpose? And what would be the Search & Rescue assets that could be used should such a bird come down involuntarily?
Something we are not told about is happening at the Turkish-Syrian border. Is that the reason why the Russians, despiteU.S. efforts to hinder them, prepare air fields for the delivery of new air assets to the Syrian army?
Russia is being painted as the aggressor here. But the story of trans-Atlantic drone successes, whatever the underlying truth, suggests some outside force has been successful at doing more than winning ground battles.
Update: Meant to include this, from the WaPo story, because I find it interesting a story about drones introduces ambiguity both about where the drones might have been launched, but also an acknowledgement there’s more coming out of Jordan (and presumably Turkey).
The U.S. military and European allies operate fighter jets and other aircraft from the Muwaffaq Salti Air Base in Jordan, a highly secured compound that was used earlier this year by a Jordanian pilot who was captured by the Islamic State and burned alive.
The United States also flies drones from bases in Turkey, Kuwait, Saudi Arabia, the United Arab Emirates and Qatar, where the al-Udeid Air Base serves as the Middle East headquarters of the U.S. Special Operations Command.
Update: In his tweet on this, Cameron said the Brits used an RAF “aircraft;” he didn’t say drone (which uses fewer characters).
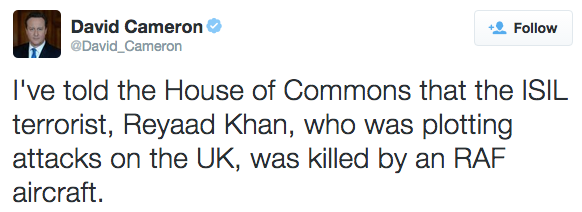
Update: Though in Cameron’s statement, he clearly says it was a remotely piloted aircraft.
Mr Speaker, in recent weeks it has been reported that 2 ISIL fighters of British nationality who had been plotting attacks against the UK and other countries have been killed in airstrikes. Both Junaid Hussain and Reyaad Khan, were British nationals based in Syria who were involved in actively recruiting ISIL sympathisers and seeking to orchestrate specific and barbaric attacks against the West, including directing a number of planned terrorist attacks right here in Britain, such as plots to attack high profile public commemorations, including those taking place this summer.
We should be under no illusion. Their intention was the murder of British citizens. So on this occasion we ourselves took action. Today I can inform the House that in an act of self-defence and after meticulous planning Reyaad Khan was killed in a precision air strike carried out on 21 August by an RAF remotely piloted aircraft while he was travelling in a vehicle in the area of Raqqah in Syria.
In addition to Reyaad Khan who was the target of the strike, 2 ISIL associates were also killed, 1 of whom – Ruhul Amin, has been identified as a UK national. They were ISIL fighters and I can confirm there were no civilian casualties.
Mr Speaker, we took this action because there was no alternative. In this area, there is no government we can work with. We have no military on the ground to detain those preparing plots. And there was nothing to suggest that Reyaad Khan would ever leave Syria or desist from his desire to murder us at home. So we had no way of preventing his planned attacks on our country without taking direct action.
The US administration has also confirmed that Junaid Hussain was killed in an American airstrike on 24 August in Raqqah.