The crew here has been seasonally busy; there are graduations, returns from college, business and vacation travel, many other demands keeping us away from the keyboard. Bear with us.
That’s not to say we’re not stewing about — well, everything. EVERYTHING. Pick a subject and it’s probably on fire if it’s not smoldering. Touch it and it may burst into flame, kind of like James Comey’s job.
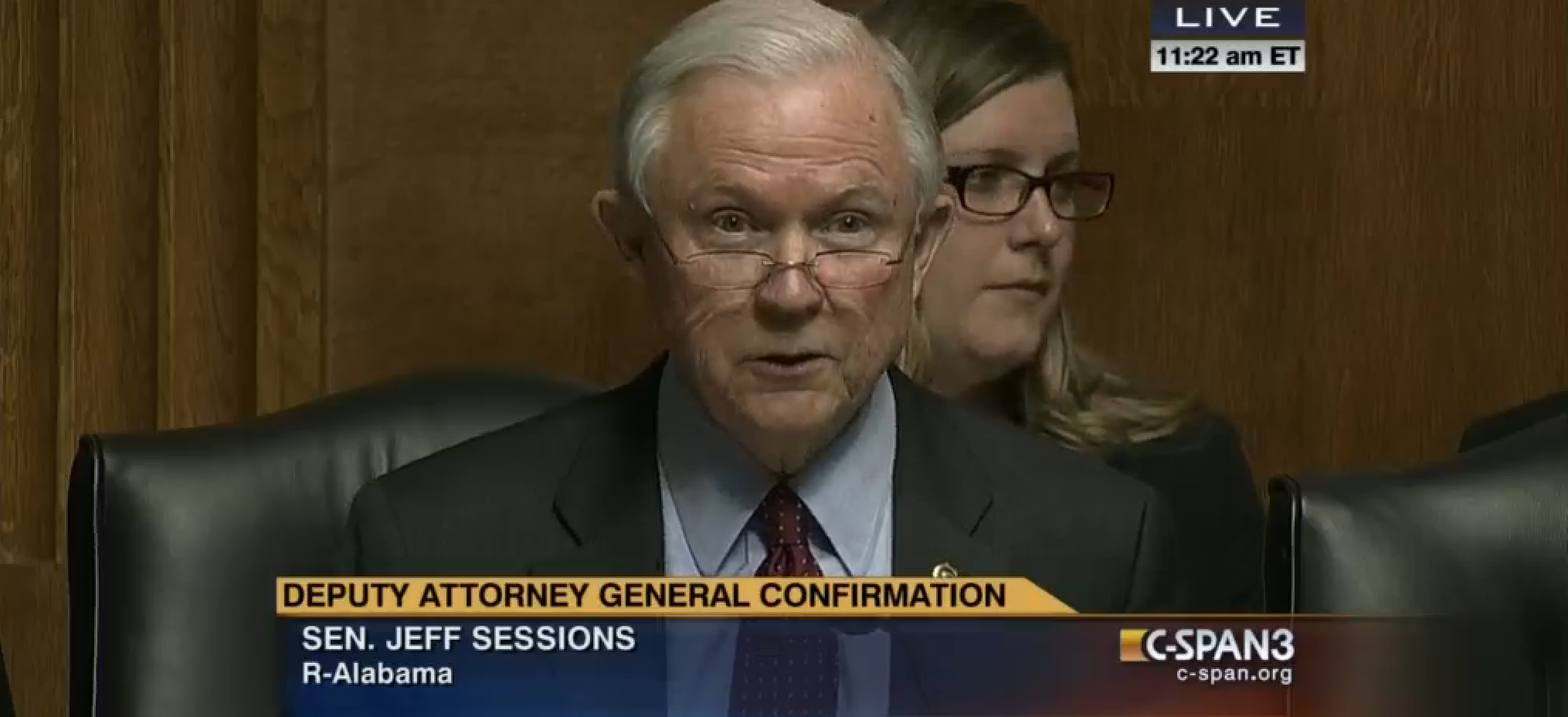
Yesterday’s Senate Judiciary Committee hearing with testimony from Sally Yates and James Clapper is one such topic utterly ablaze. How to even start with what went wrong — like Ted ‘Zodiac Killer’ Cruz and his sidling up to ‘But her emails!’. Or John Kennedy’s [string a bunch of expletives together and insert here] questions which did nothing to further any investigation.
I’m glad Sally Yates laid one across Cruz on the Immigration and Nationality Act of 1965 (INA); he deserved it for his particularly egregious mansplaining.
As you can see from their tweets, I know my fellow contributors have much they wish they could post about the hearing. I know after the closing gavel I had many more questions, not fewer.
Like timing. Timing seemed so inter-related on seemingly disparate issues.
What about the timing of Yates’ discussion with White House Counsel Don McGahn about Lt. Gen. Michael Flynn (ret.) and the timing of the Muslim travel ban, Executive Order 13769?
10-NOV-2017 — First warning about Flynn to Trump by Obama during post-election meeting.
18-NOV-2017 — Flynn named National Security Adviser by Trump.
25-DEC-2017 — Flynn allegedly sends text messages to Russian ambassador Sergei Kislyak including holiday greetings.
29-DEC-2017 — New sanctions announced by Obama, including eviction of 35 Russians (including family members) from two compounds.
29-DEC-2017 — Michael Flynn talks with Kislyak more than once on the same day.
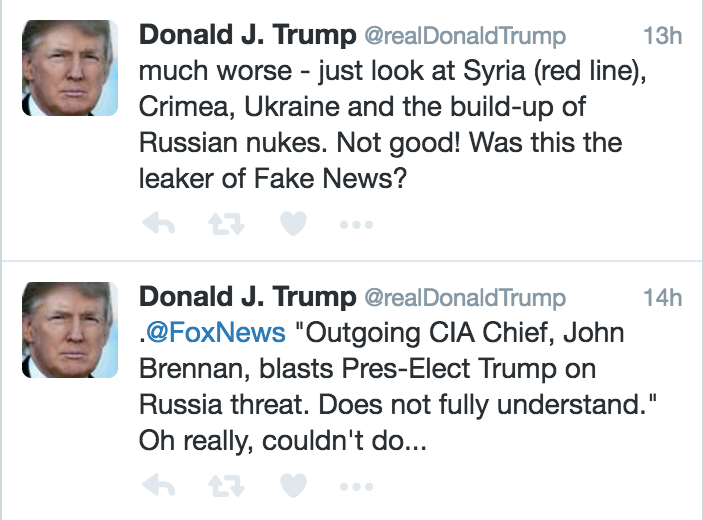
30-DEC-2017 — Trump tweeted positively about Russian president Vladimir Putin’s refusal to retaliate against the new sanctions.
12-JAN-2017 — The Washington Post reported on the Flynn-Kislyak conversations; source cited is “a senior U.S. government official.”
15-JAN-2017 — VP Mike Pence says in a TV interview that he had talked with Flynn about contact with Kislyak:
JOHN DICKERSON: Let me ask you about it was reported by David Ignatius that the incoming national security advisor Michael Flynn was in touch with the Russian ambassador on the day the United States government announced sanctions for Russian interference with the election. Did that contact help with that Russian kind of moderate response to it? That there was no counter-reaction from Russia. Did the Flynn conversation help pave the way for that sort of more temperate Russian response?
MIKE PENCE: I talked to General Flynn about that conversation and actually was initiated on Christmas Day he had sent a text to the Russian ambassador to express not only Christmas wishes but sympathy for the loss of life in the airplane crash that took place. It was strictly coincidental that they had a conversation. They did not discuss anything having to do with the United States’ decision to expel diplomats or impose censure against Russia.
JOHN DICKERSON: So did they ever have a conversation about sanctions ever on those days or any other day?
MIKE PENCE: They did not have a discussion contemporaneous with U.S. actions on—
JOHN DICKERSON: But what about after—
MIKE PENCE: —my conversation with General Flynn. Well, look. General Flynn has been in touch with diplomatic leaders, security leaders in some 30 countries. That’s exactly what the incoming national security advisor—
JOHN DICKERSON: Absolutely.
MIKE PENCE: —should do. But what I can confirm, having spoken to him about it, is that those conversations that happened to occur around the time that the United States took action to expel diplomats had nothing whatsoever to do with those sanctions.
JOHN DICKERSON: But that still leaves open the possibility that there might have been other conversations about the sanctions.
MIKE PENCE: I don’t believe there were more conversations.
20-JAN-2017 — Inauguration Day
21-JAN-2017 — Flynn has a follow-up call with Kislyak with regard to a future phone call between Trump and Putin.
23-JAN-2017 — Answers to questions during a press briefing with White House Press Secretary Sean Spicer didn’t match what Pence said in the 15-JAN interview. Spicer said, “There’s been one call. I talked to Gen. Flynn about this again last night. One call, talked about four subjects. … During the transition, I asked Gen. Flynn that – whether or not there were any other conversations beyond the ambassador and he said no.”(Come on, Spicey. Come the fuck on. Pure sloppiness; this isn’t the time for disinformation.)
24-JAN-2017 — Flynn is interviewed by the FBI and without a lawyer present. Yates informed McGahn about Flynn’s interview.
25-JAN-2017 — Yates reviews Flynn’s interview.
25-JAN-2017 — Draft of the travel ban EO leaked and published by WaPo
A provision about safe zones in Syria appears in this draft. It will not appear in the final EO.
26-JAN-2017 — Yates called McGahn that morning and asked for an in-person meeting about a sensitive topic she could not discuss on the phone. They met later that afternoon at McGahn’s office:
…We began our meeting telling him that there had been press accounts of statements from the vice president and others that related conduct that Mr. Flynn had been involved in that we knew not to be the truth.”
A senior member of the DOJ’s National Security Division accompanied Yates. Yates explained why Flynn was compromised and how his actions set Pence up to make unknowingly false statements to the public.
Spicer has said McGahn immediately notified and briefed Trump after meeting with Yates.
27-JAN-2017 — McGahn called Yates and asked for a second in-person meeting. Yates met him at his office. During their conversation, McGahn asked, “Why does it matter to DOJ if one White House official lies to another?” Yates re-reviews the FBI’s concerns shared the previous day. (I want to ask if McGahn got his JD out of a box of Cracker Jacks.) McGahn asked,
“And there was a request made by Mr. McGahn, in the second meeting as to whether or not they would be able to look at the underlying evidence that we had that we had described for him of General Flynn’s conduct.” (Bold mine; who is ‘they’?)
Yates indicated she would work with FBI team and “get back with him on Monday morning.”
27-JAN-2017 — Travel ban EO signed and distributed. Rex Tillerson has not yet appeared before the Senate in a confirmation hearing. Defense Department’s James Mattis did not see the EO until morning of January 27; the EO is signed later in the day after Mattis was sworn in just before 3:00 p.m. Homeland Security Secretary John Kelly said he saw final EO draft not long before it was signed. Office of Legal Counsel issued a determination about the EO that day, “the proposed order is approved with respect to form and legality.” According to Yates’ SJC testimony the OLC’s determination goes to the form and not the content of the EO.
28-JAN-2017 — Federal Judge Ann Donnelly issued a stay late Saturday on deportations of persons with valid visas.
29-JAN-2017 — Though not yet confirmed as Secretary of State, Tillerson involved in cabinet-level meetings in pre-dawn hours regarding the travel ban.
30-JAN-2017 — Yates called McGahn that morning and told him he could go to FBI to look at “underlying evidence.” McGahn does not reply until the afternoon. Yates didn’t know whether McGahn looked at evidence because “because that was my last day with DOJ.” Yates ordered DOJ not to defend the EO in court
30-JAN-2017 — Yates is fired by the White House Monday night. White House statement said,
“The acting Attorney General, Sally Yates, has betrayed the Department of Justice by refusing to enforce a legal order designed to protect the citizens of the United States … This order was approved as to form and legality by the Department of Justice Office of Legal Counsel. … Ms. Yates is an Obama Administration appointee who is weak on borders and very weak on illegal immigration. It is time to get serious about protecting our country. Calling for tougher vetting for individuals travelling from seven dangerous places is not extreme. It is reasonable and necessary to protect our country.”
08-FEB-2017 — WaPo reports Flynn denied twice discussing Russian sanctions with Kislyak.
09-FEB-2017 — Allegedly, Pence learned this day Flynn was not straight with him about his interactions with Kislyak. WaPo reported Flynn had discussed sanctions with Kislyak prior to the inauguration.
10-FEB-2017 — ABC News reported Flynn wasn’t certain he talked about the sanctions with Kislyak. Pence spoke with Flynn twice this day.
12-FEB-2017 — Stephen Miller dodges questions about Flynn’s status during Sunday morning TV interviews.
13-FEB-2017 — Flynn resigns, 18 days after Yates raised questions with the White House about his vulnerability to compromise.
Yates’ directive not to enforce the illegal travel ban EO is the prima facie reason why she was fired a week after the EO was pushed. But was it really the travel ban or the fact she had not only warned the White House about Flynn’s compromised status but the implication there might be more at stake?
The rushed timing of the EO — pushed out on a Friday night after business hours — and its inception generate more questions about the travel ban.
Who really wrote the travel ban? Some reports say the ‘major architects’ were Stephen Miller and Steve Bannon, neither of whom have law degrees or any experience in legal profession. Wikipedia entry for Bannon indicates he has a master’s in national security studies from Georgetown, but there’s no indication about the date this was conferred and it’s still not a law degree. Miller has a BA from Duke and a bunch of cred from writing conservative stuff, much of it with a white nationalist bent. (Yeah, stuff, because none of it provided adequate background to write effective executive orders.)
There were reports a week after the first travel ban EO was issued which indicated Congressional aides actually wrote the executive order — aides from Rep. Bob Goodlatte’s office.
Who were those aides?
Why Goodlatte’s aides? Was it because Goodlatte is the Chairman of the House Judiciary Committee?
Was it because of Goodlatte’s immigration bills circa 2013:
H.R. 2278, the “Strengthen and Fortify Enforcement Act” (The SAFE Act)
H.R. 1773, the “Agricultural Guestworker Act”
H.R. 1772, the “Legal Workforce Act”
H.R. 2131, the “SKILLS Visa Act”
In other words, did the aides who wrote those bills also assist with and/or write the EO?
If these aides helped the ‘major architects’, why did the travel ban EO look so clearly illegal?
Did these aides ever refer the ‘major architects’ to the Office of Legal Counsel for assistance with the EO’s wording?
Did media try to interview the aides in question? If not, why? If not permitted to do so, why?
Did those aides sign a non-disclosure agreement with the White House? (Why the hell are there NDAs for ANY government employee anyhow, especially those with security clearance of any level? This is OUR government, not the Trump holding company.) Did the aides limit their work to transition team support, or were they working on the EO post-inauguration? Did they take vacation time to do the work? Or were they performing work for the White House on Congress’ dime?
In spite of his iffy-sounding support for their work, did Goodlatte kick those aides in the ass for moonlighting while puncturing the separation between the Executive Branch and the Legislative Branch, making it appear (if tenuously) there was a degree of concurrence between the two branches?
Did Michael Flynn talk about the EO with these aides?
And was Flynn one of the ‘major architects’ of the travel ban EO along with Miller and Bannon as reported in some outlets?
Assuming Flynn was a co-architect/co-author of the EO, was the EO pushed through in a hurry to effect Flynn’s work before he might be terminated and/or prosecuted?
Was the execution of a travel ban EO part of a quid pro quo with a foreign entity?
Is this the reason why Trump reduced the role of chairman of the Joint Chiefs of Staff and the director of national intelligence to “an as-needed basis” on National Security Council — to reduce potential interference by seasoned security professionals who might stop the EO?
Was Miller’s role in the creation of the travel ban EO less about any experience he has but instead related to his former work during 113th Congress with the Gang of Eight on immigration reform? (We come full circle – see Goodlatte’s bills above.)
How might this travel ban EO — banning Muslims from specific countries — help a foreign entity?
Or was the Muslim travel ban EO simply launched early — before the administration even had a Secretary of State, before its content was reasonably defensible — to distract Yates and the DOJ and derail further investigation into Flynn’s compromised status?
I’m sure if I spend any more time re-reading the SJC’s hearing transcript I’ll come up with even more questions. But as events around Flynn and the travel ban EO unfolded as if knit together, I can’t help wondering if they really were of a piece.
How odd that the first thing the first SJC non-chair member did, before asking witnesses any questions, was hand out a timeline of events to all the participants.
And how convenient FBI Director James Comey screwed up his last testimony before congress enough that his firing this evening by the White House would look entirely justified — immediately removing him not only from the next FBI flight from Los Angeles to DC but from any further investigation into Michael Flynn.
What timing.