There May Well Have Been an Intelligence Failure in Afghanistan
Almost as quickly as Republicans and Democrats rushed to blame the other for the humiliating fall of Afghanistan, and as quickly as bipartisan NeoCons and bipartisan anti-Imperialists blamed the other for victory of the Taliban, the Intelligence Community and DOD have rushed to blame each other.
This story is just one example, but there are many.
In 2019, U.S. spy agencies delivered a sweeping assessment known as a National Intelligence Estimate of the conflict that warned many of America’s often-stated objectives were in jeopardy even with a continued U.S. military presence, and without direct American backing all but destined to collapse.
“We would run into really serious battles with the Pentagon, which would say, ‘We’ve got boots on the ground, we know the truth,’ ” said a former senior U.S. intelligence official.
The diverging views on the war were a reflection of the institutional predispositions of military planners groomed to accept even the most daunting missions and find ways to deliver results.
In Afghanistan, “you had good people who tried mightily believing they could do it,” the former intelligence official said. “And in the end are forced to face the reality that they couldn’t.”
One thing all these parties are fighting over is whether there was an intelligence failure.
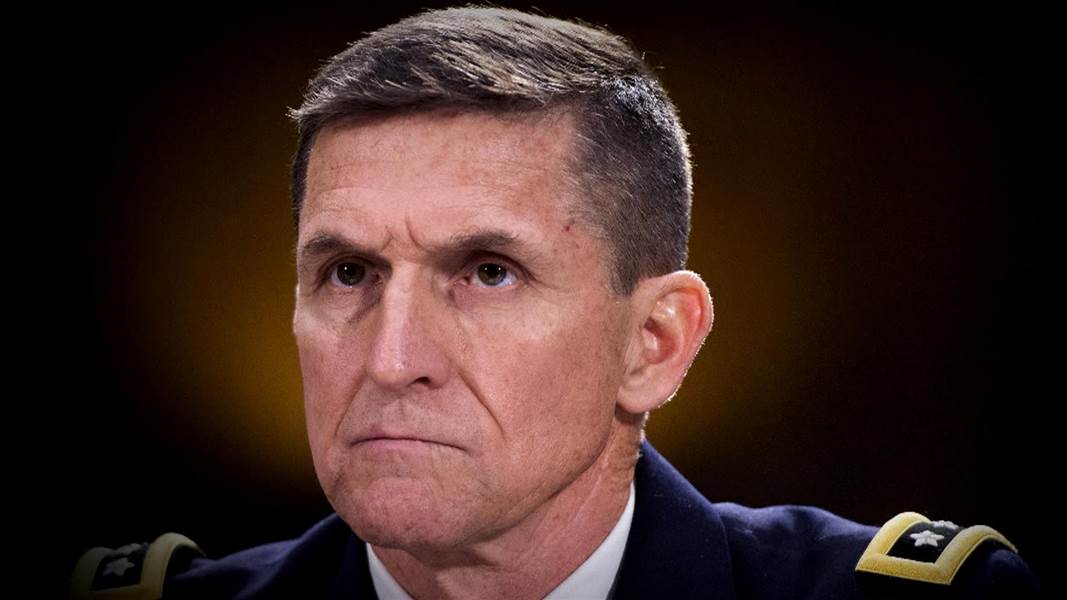
Mike Morell, like many of the spooks being interviewed, says it wasn’t his fault.
Michael Morell, the former acting and deputy director of the CIA wrote on Twitter: “What is happening in Afghanistan is not the result of an intelligence failure. It is the result of numerous policy failures by multiple administrations. Of all the players over the years, the Intelligence Community by far has seen the situation in Afghanistan most accurately.”
And he’s right: Anyone who didn’t know, going back well over a decade, that an Afghan regime would collapse without US backing simply wasn’t paying attention.
That said, just days ago the most dire intelligence predicting that the Afghan government would fall to the Taliban spoke in terms of a month, not a weekend.
The Biden administration is preparing for Afghanistan’s capital to fall far sooner than feared only weeks ago, as a rapid disintegration of security has prompted the revision of an already stark intelligence assessment predicting Kabul could be overrun within six to 12 months of the U.S. military departing, according to current and former U.S. officials familiar with the matter.
One official, who like others spoke on the condition of anonymity due to the issue’s sensitivity, said Tuesday that the U.S. military now assesses a collapse could occur within 90 days. Others said it could happen within a month. Some officials said that although they were not authorized to discuss the assessment, they see the situation in Afghanistan as more dire than it was in June, when intelligence officials assessed a fall could come as soon as six months after the withdrawal of the U.S. military.
At the same time, spooks saying that they didn’t know the effect that a quick withdrawal would have on the timing, even though others note the timing has always been known — including by the Taliban and our regional adversaries. That is, the IC didn’t fail to warn about how fragile the Afghan government was, but they seem to have been surprised by the snowball effect.
There are discrete decisions that do require accountability, such as the decision — apparently made by Mark Milley — that keeping Bagram running until we exited was not “tactically necessary.”
[Congressman Doug] Lamborn asks if it is “at all possible” for the United States to keep open Bagram Airfield. Gen. Milley responds that it is not tactically necessary.
If things get really bad in the days ahead, it will be because US armed forces rushed in to maintain order while the US evacuates are working at the airport rather than Bagram, which is far easier to secure.
But I do wonder whether there was not, in fact, a really dire intelligence failure having largely to do with how Ashraf Ghani and other Afghan leaders were paid off to cede power.
On top of weakened morale and lack of air support, the best explanation for the Taliban’s quick success has to do with “surrenders” that became the only viable option for Afghan soldiers after Trump’s deal with the Taliban last year.
The spectacular collapse of Afghanistan’s military that allowed Taliban fighters to walk into the Afghan capital Sunday despite 20 years of training and billions of dollars in American aid began with a series of deals brokered in rural villages between the militant group and some of the Afghan government’s lowest-ranking officials.
The deals, initially offered early last year, were often described by Afghan officials as cease-fires, but Taliban leaders were in fact offering money in exchange for government forces to hand over their weapons, according to an Afghan officer and a U.S. official.
Over the next year and a half, the meetings advanced to the district level and then rapidly on to provincial capitals, culminating in a breathtaking series of negotiated surrenders by government forces, according to interviews with more than a dozen Afghan officers, police, special operations troops and other soldiers.
[snip]
The negotiated surrenders to the Taliban slowly gained pace in the months following the Doha deal, according to a U.S. official and an Afghan officer. Then, after President Biden announced in April that U.S. forces would withdraw from Afghanistan this summer without conditions, the capitulations began to snowball.
As the militants expanded their control, government-held districts increasingly fell without a fight. Kunduz, the first key city overrun by the militants, was captured a week ago. Days of negotiations mediated by tribal elders resulted in a surrender deal that handed over the last government-controlled base to the Taliban.
Soon after, negotiations in the western province of Herat yielded the resignation of the governor, top Interior Ministry and intelligence officials and hundreds of troops. The deal was concluded in a single night.
This, too, was obviously known and knowable.
What I wonder is how far up in the Afghan government such discussions went, and if that was also known.
A really worthwhile thread from Afghanistan’s former Central Bank Governor, Ajmal Ahmady, describes rumors that the decision came from higher up.
There were multiple rumors that directions to not fight were somehow coming from above. This has been repeated by Atta Noor and Ismael Khan. Seems difficult to believe, but there remains a suspicion as to why ANSF left posts so quickly. There is something left unexplained
It describes how he kept going to work even while learning that Ghani had fled.
On Saturday night, my family called to say that most government had already left. I was dumbfounded. A security assessment accurately forecast Taliban arrival to Kabul within 36 hours and its fall within 56 hours I got worried & purchased tickets for Monday as a precaution
[snip]
Saw VP Danish leaving – reportedly for Qatar. By then it was rumored that VP Saleh had left. Ministers + others were waiting for a Fly Dubai & Emirates flights. Both were cancelled I secured a Kam Air flight Sunday 7pm. Then the floor fell: the President had already left
Almost immediately after Ghani fled, Russian news sources reported that he had taken mountains of cash with him.
Russia’s embassy in Kabul said on Monday that Afghan President Ashraf Ghani had fled the country with four cars and a helicopter full of cash and had to leave some money behind as it would not all fit in, the RIA news agency reported.
That’s not unlikely — it’s just rather curious that Russia was the first to know of it.
Even as and because that happened, a diplomatic effort to negotiate a transitional government failed.
The weeks leading up to Kabul’s collapse saw a flurry of diplomatic activity by the U.S. and its allies in Qatar aimed at heading off exactly the chaotic scenes in the Afghan capital that have so horrified the world and put Joe Biden’s presidency on the defensive.
Among those efforts was a tantalizing agreement that could have guaranteed calm. Afghan and Taliban negotiators tentatively reached a deal in which all sides would declare a two-week cease-fire in exchange for President Ashraf Ghani’s resignation and the start of talks on setting up a transitional government, according to two people familiar with the matter, who asked not to be identified discussing private deliberations.
That opportunity, which hasn’t been previously reported, was lost when Ghani fled the country, according to the people. Ghani’s decision to leave Afghanistan — he said he did so to avoid a bloodbath — surprised his negotiating team in Doha, American diplomats and even his chief of staff and other top aides, said the people.
This, it seems to me, is where the real intelligence failure begins. Not even Ghani’s own ministers, according to current reports, knew he was going to flee, possibly with a chunk of cash.
And that has repercussions that may explain the rest. In his speech on Afghanistan last night, Biden described Ghani refusing to do any of the things Biden asked for in June and July. Of particular interest, Ghani seems to have refused to engage with the diplomatic effort that was undermined by Ghani’s capitulation.
I always promised the American people that I will be straight with you. The truth is: This did unfold more quickly than we had anticipated.
So what’s happened? Afghanistan political leaders gave up and fled the country. The Afghan military collapsed, sometimes without trying to fight.
[snip]
When I hosted President Ghani and Chairman Abdullah at the White House in June and again when I spoke by phone to Ghani in July, we had very frank conversations. We talked about how Afghanistan should prepare to fight their civil wars after the U.S. military departed, to clean up the corruption in government so the government could function for the Afghan people. We talked extensively about the need for Afghan leaders to unite politically.
They failed to do any of that.
I also urged them to engage in diplomacy, to seek a political settlement with the Taliban. This advice was flatly refused. Mr. Ghani insisted the Afghan forces would fight, but obviously he was wrong.
No one can claim to be surprised that the Afghan military folded. That it would has been clear for over a decade.
There are real questions, though, about whether the intelligence community knew how far up the Afghan government the plans to capitulate in exchange for payment went. And that question drives further intelligence questions. Ashraf Ghani has been privy to our Afghan intelligence collection. Hamid Karzai, who is playing a clear broker role but it’s not yet clear with and for whom, likewise was privy to a lot of our intelligence collection. The Taliban have had twenty years to learn how to evade our surveillance. Russia has been stealing key technical data for the last decade, focusing closely on our Afghan operations, and they seem quite chuffed with recent events.
If some or all those people have been working in concert, and may well have been since Trump acceded to this plan last year, it would be child’s play for them to hide from US intelligence how far up the chain of command would cede to the Taliban, if not actively disinform US intelligence. And that, in turn, would make it far easier to take over the country so quickly that the Taliban were even shocked.
If that happened, then it was a real intelligence failure that explains why the US wasn’t better prepared for the collapse of the Afghan government, even without excusing self-serving claims that the Afghan military might have lasted a week or a month or a year longer than they did.