FISC Opinions as Legal Cover
WSJ has a story on how the FISA Court came to render the phrase “related to” — which has been used for 7 years to collect the phone records of almost all Americans — entirely meaningless.
The history of the word “relevant” is key to understanding that passage. The Supreme Court in 1991 said things are “relevant” if there is a “reasonable possibility” that they will produce information related to the subject of the investigation. In criminal cases, courts previously have found that very large sets of information didn’t meet the relevance standard because significant portions—innocent people’s information—wouldn’t be pertinent.
But the Foreign Intelligence Surveillance Court, FISC, has developed separate precedents, centered on the idea that investigations to prevent national-security threats are different from ordinary criminal cases. The court’s rulings on such matters are classified and almost impossible to challenge because of the secret nature of the proceedings. According to the court, the special nature of national-security and terrorism-prevention cases means “relevant” can have a broader meaning for those investigations, say people familiar with the rulings.
The story specifically says FISC issued the decision authorizing the use of Section 215 to collect phone records in May 2006, in the wake of the exposure of Dick Cheney’s illegal dragnet (and after Congress had included the “relevant to” language in the PATRIOT Act reauthorization).
But in May 2006, the secret court agreed that, even with the addition of the word “relevant,” bulk phone records could also be collected under the law.
The legal interpretations required to make this change were “aggressive,” says Timothy Edgar, a former top privacy lawyer at the Office of the Director of National Intelligence and the National Security Council in the Bush and Obama administrations. Still, considering that the program previously had less congressional or court oversight, many lawmakers saw this as a step forward, he says.
“It wasn’t seen that we’re pushing the boundaries of surveillance law here,” Mr. Edgar says. “It was the very opposite. You’re starting from a huge amount of unilateral surveillance and putting it on a much sounder legal basis.”
Indeed, the way Edgar justifies this crazy distortion of the term “relevant” is by pointing to Cheney’s illegal program, as if that made it right.
But WSJ also describes this May 2006 decision as one in a series of decisions starting in “mid-2000s.”
In classified orders starting in the mid-2000s, the court accepted that “relevant” could be broadened to permit an entire database of records on millions of people, in contrast to a more conservative interpretation widely applied in criminal cases, in which only some of those records would likely be allowed, according to people familiar with the ruling.
The timing is significant. Remember, FBI hadn’t used Section 215 in the post-9/11 era until the period Jack Goldsmith and Jim Comey started challenging the illegal program’s legality; FBI got their first Section 215 order approved — MIRACLES! — on May 21, 2004. FBI at least temporarily sidestepped DOJ’s Office of Intelligence Policy and Review to employ this standard.
On March 23, 2004 at noon, less than two weeks after the dramatic hospital confrontation and threats to quit reportedly got the Administration to agree to stop data mining Americans, FBI Director Robert Mueller had a meeting with Dick Cheney, at the Vice President’s request, in the Vice President’s office. In his notes, Mueller doesn’t describe what the VIce President wanted, nor am I aware that it has even been reported in the press.
The next day, the Chief Division Counsel of some Division of the FBI wrote a memo to the FBI General Counsel noting that FBI was using a “new standard” with Section 215 of the PATRIOT Act and indicating that a “recent decision” had been made to bypass the review of the Office of Intelligence Policy and Review on Section 215 applications.
In part, the apparent decision to bypass OIPR, which had rejected the premise of the previous Section 215 orders FBI had submitted in the past, reflected no more than a concerted effort on FBI’s part to make sure it could start using all the PATRIOT authorities it had been granted in 2001 in anticipation of renewal discussions that would take place the following year. Yet the timing of this change is particularly curious, given that we now know Section 215 has been used to collect data that could be used for data mining Americans, precisely the problem that had caused the hospital confrontation 12 days earlier.
At the very least, however, it shows that sometime around the same time as Jim Comey and others at DOJ tried to stop the data mining of Americans under NSA’s illegal program, FBI claimed to have eliminated one review step for Section 215 orders and changed the standard used for them. That reference notwithstanding, DOJ Inspector General at least reported that OIPR continued to have a role. (Note, the office that got cut out of the process, OIPR, is where one of the key whistleblowers on the illegal program, Thomas Tamm worked, though I have asked him if he knew whether they used Section 215 to accomplish the same program and he didn’t know anything about it.)
On May 21, 2004, just as the the confrontation was settling down, FBI got its first Section 215 order approved. MIRACLES! the memo subject line read. “We got our first business record order signed today. It only took two and a half years.”
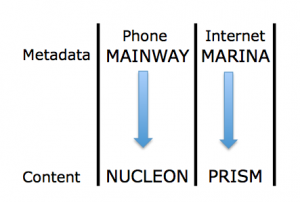
And consider the other odd thing about all this. There is a part of FISA specifically designed to return phone records, the Pen Register/Trap & Trace procedure (the one used starting in 2004 for Internet metadata). So why didn’t they use that?
In any case, this increasingly appears to be the end result of an effort on the part of FISC to remain relevant by distorting law in secret, in the hopes that an unconstitutional expansion of the law in secret was better than actually stopping an illegal program conducted by bypassing the court altogether.
The reason the law is so twisted is because no one wanted to — or believed they had the ability to –rein in gross violations of law conducted by Dick Cheney.