Verizon Gets Out of the Upstream Surveillance Business
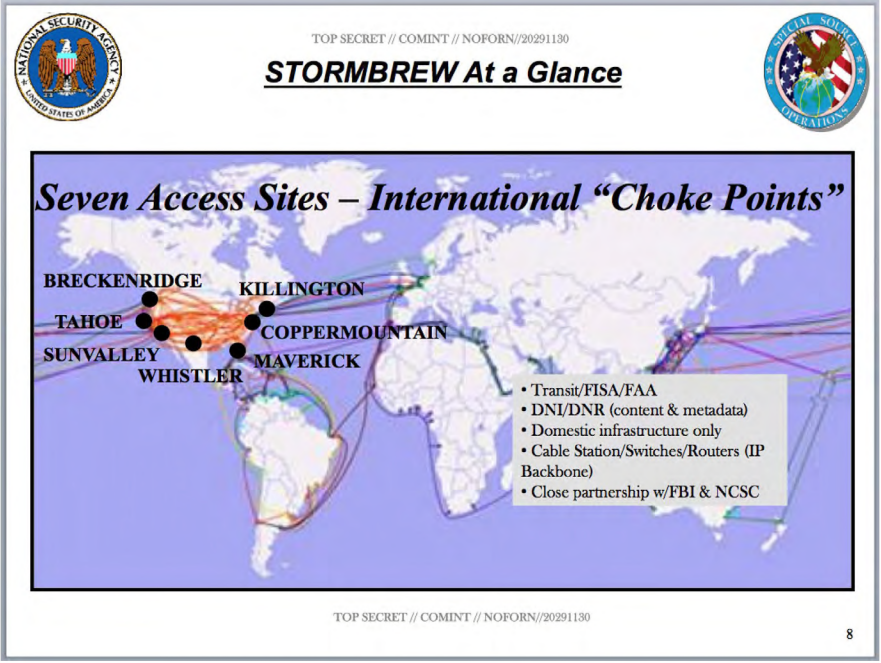
Even as the privacy world has been discussing how NSA got out of one kind of the upstream collection business on April 28, most people overlooked that someone else got out of the upstream collection business almost entirely just a few days later. That’s when Verizon finalized its sale of a big chunk of its data centers — including the ones used for Stormbrew collection — to Equinix. (h/t to SpaceLifeForm for reminding me)
When Equinix announced the $3.6B cash purchase in December, it emphasized the Miami data center — though which much of the traffic from Latin America passes on to the rest of the world — and the Culpepper site serving the National Security world.
- The NAP (Network Access Point) of the Americas facility in Miami is a key interconnection point and will become a strategic hub and gateway for Equinix customer deployments servicing Latin America. Combined with the Verizon data centers in Bogotá and the NAP do Brasil in São Paulo, it will strategically position Equinix in the growing Latin American market.
- The NAP of the Capital Region in Culpeper, VA is a highly secure campus focused on government agency customers, strengthening Equinix as a platform of choice for government services and service providers.
The purchase also expands Equinix’s presence in Silicon Valley.
Mind you, spying infrastructure has continued to evolve since Snowden documents elucidated where the Stormbrew collection points were and what they did. So maybe these data centers are no longer key “chokepoints’ (as the NSA called them) of American spying.
But if they are, then Verizon is no longer the one sifting through your data.





Many thanks.
In Feb 2003 $EQIX traded at $3.45/share.
Now it’s north of $426/share.
Is there any basis for their confidence in their Miami disaster recovery plan?
Wow.
OT:
Bad zero-day out there. Remote Code Execution. Of course you do not even have to guess the platform.
Look for the alleged ‘patch’ 2017-08-08.
If not related to the following link, I will be surprised.
https://www.google.com/amp/www.infoworld.com/article/2616828/microsoft-windows/flash-is-on-windows-8–but-that-s-just-part-of-the-story.amp.html
Wow. Already patched. Not flash related at all, but was Windows Defender. How ironic.
https://bugs.chromium.org/p/project-zero/issues/detail?id=1252&desc=5
https://arstechnica.com/information-technology/2017/05/windows-defender-nscript-remote-vulnerability/
Microsoft on Monday patched a severe code-execution vulnerability in the malware protection engine that is used in almost every recent version of Windows (7, 8, 8.1, 10, and Server 2016), just three days after it came to its attention. Notably, Windows Defender is installed by default on all consumer-oriented Windows PCs.