FBI Busts the Guy Who Saved the World from NSA’s Malware
Yesterday, the FBI arrested Marcus Hutchins as he was leaving Las Vegas after Black Hat/Defcon.
Hutchins is best known as the malware researcher, MalwareTechBlog, who inadvertently saved the world from NSA’s repurposed hacking tools by registering what has been assumed to be the sand boxing domain, effectively turning it into a killswitch.
But the government accuses him of making the Kronos banking malware sold on AlphaBay. In an indictment signed July 11 (6 days after AlphaBay got seized and), the government asserts simply that Hutchins made the malware. Motherboard first reported the arrest.
It also accuses him of conspiring with a co-defendant whose name is redacted, going back to July 2014, of selling it.
There’s a lot of skepticism about this indictment in the infosec community, in part because no one took Hutchins for a black hat, though others point to a past identity under which he may have engaged in carding. Plus, the timing is curious. The press release for the arrest notes “the Kronos banking Trojan … was first made available through certain internet forums in early 2014.”
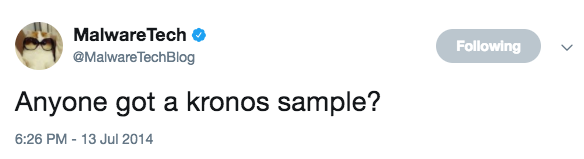
On July 13, 2014, Hutchins put out an ask for a sample of the malware.
That’s also the day the indictment describes an advertising video first being posted to AlphaBay on how Kronos worked.
In remarkably timed news, between 3:10 and 3:25 AM UTC this morning (8 PM last night Mountain Time), someone emptied out all the WannaCry accounts.



![[Photo: Annie Spratt via Unsplash]](https://www.emptywheel.net/wp-content/uploads/2017/08/Books_AnnieSpratt-Unsplash_mod1-80x80.jpg)

Fuck. I’m drinking and it’s 86 degrees. I find out that Mueller has empaneled a grand jury. Whoa, Trump will try to fire him. That fucking Trump is such a fucking Con Man and fiendish prick. Thank God for the judiciary
I was reading this article as well. Seriously, if the indictment is true, why wait until now? What was presented at DefCon that made it necessary to nab him right there and then?
Anyone that believes the USG will have their back after this is kidding themselves. That is the price of deception, JeffBo, no one will want to talk to you after this. I think the idea that he inconveniently revealed what was a NSA virus is the best explanation until more is reported. However, NSA shouldn’t have said anything to draw attention to the code, it only reveals tendencies that can point to other NSA landmines.
The new DC grand jury is distinct from the VA GJ that is looking at Flynn, and I suspect that the report of it means that indictments are on the way (and not for Flynn). Does this mean Flynn is singing? I think so, with the VA GJ there to keep him in tune, so to speak. I think Caesar Disgustus will try to fire Mueller, but one of the GOP senators is on record as saying that if that happened they’d hire Mueller as their investigator. As far as that warning goes, I consider this as the same level of seriousness as their “troubling” rumblings over AHCA / BCRA that they voted for anyway. Nonetheless, the public nature of this disagreement is a sign.
Hutchins did not expose anything. Any other researcher that took the time using a VM would have found it very quickly.
But, he found it, and got the domain.
The attackers allegedly screwed up.
Maybe they did not. Maybe the point of the exercise was to catch a researcher actually doing the ‘right thing’.
Cobb spin. Unaware? BS.
Accelerates the conclusion? Damn straight.
They want this to disappear ASAP.
Not gonna happen. We are looking at a minimum of 8 years of judicial proceedings.
Probably longer.
http://thehill.com/homenews/administration/345212-mueller-establishes-grand-jury-in-trump-russia-probe-report
Mueller’s spokesman declined to comment to the newspaper, while White House special counsel Ty Cobb said he was unaware of the new development.
“Grand jury matters are typically secret. The White House favors anything that accelerates the conclusion of his work fairly,” Cobb said in a statement. “The White House is committed to fully cooperating with Mr. Mueller.”
[Yeah sure. And I have a bridge to sell to Cobb]
OT?: Lawyering up. When you buy extra legal insurance, you know the train ride will be rocky.
http://www.cnn.com/2017/08/03/politics/mueller-investigation-russia-trump-one-year-financial-ties/index.html
CNN has learned some of the investigators involved in the probe are buying liability insurance out of concern they could become targets of lawsuits from those who are being investigated, according to one of the people familiar with the probe. The Justice Department covers legal fees for employees sued in the course of their duties, but some of the lawyers want extra protection.
Still OT, sorry. However, this would have greatly aided in finding out about Junior’s meeting since Page was a vocal supporter of the Trump campaign.
http://www.rawstory.com/2017/08/former-trump-campaign-aide-carter-page-has-been-under-surveillance-since-2014-report/
Back on topic.
Where to start?
Kronos author (Vinny) may be BTC-E dude just arrested, Alexander Vinnik. Not Hutchins.
Indictment is old. They (FBI) knew Hutchins going to DEFCON from CC and hotel reservation data. He could have been arrested in UK before he flew to US.
Some group in IC is confusing other IC people.
Wildly off-topic: legendary pottymouth strikes again. Geez, Marcy, you trying to get DemocracyNow knocked off the air?
On-topic: if making a video showing how malware works is now a crime, MalwareBytes is in deep doo-doo. They routinely look at how hacks work.
OT: balky, 27-year-old heating and cooling system.
Maybe the tweetness will subside?
Ha. I kid. It is those balky 71 year old systems one can worry about.
But after the install, all will be cool. :-)
https://www.washingtonpost.com/politics/whitehouse/trump-set-to-embark-on-1st-vacation-since-inauguration/2017/08/03/431daae8-7819-11e7-8c17-533c52b2f014_story.html
Well I wrote this about this over at NC. I’m not sure because very little has come out about this after the arrest. I have a new lose fitting tin-foil-hat and I do believe he might have closed the vile program earlier than it’s masters wanted. Those wonderfully girls and boys of the 3 letter part of Amerikas govt.
O/T but bmz will you have time for Trash Talk? I’m having the jones if not I’ll have to get my fix somewhere else if there is even somewhere else;-)
OT: The quid pro quo must be awesome.
Maybe Trump wants to heat the WhiteHouse with coal.
https://www.washingtonpost.com/news/the-fix/wp/2017/08/03/west-virginias-governor-is-switching-parties-and-democrats-just-hit-a-new-low/
West Virginia Gov. Jim Justice announced Thursday he is leaving the Democratic Party, just six months after taking office, and becoming a Republican. An extra twist of the knife for Democrats: He did it alongside President Trump, at a rally in West Virginia.
Gov. Justice ought to write a book on the Art of the Deal or something like that, after selling his coal business to Russians for $600M and then buying it back for $5M a handful of years later.
Folks could learn a few things from a book like that.
Like Clinton’s commodity training, money laundering?
Little difference in scale of profit. And a little difference between foreign agents and domestic, if you want to assume bad faith in ~both~ cases. I’m curious whether Justice’s sale went through CFIUS review since energy is critical infrastructure.
Or Hillary could write one on the almost $5 million the Clinton’s raked in for brokering the deal that sold U.S. uranium deposits to the Russians. You could illustrate it with the picture of Bill yukking it up with Putin when he was in Moscow to collect a cool half million for a speech. NYT article and picture here http://www.gettyimages.com/photos/bikini-atoll?excludenudity=true&sort=mostpopular&mediatype=photography&phrase=bikini%20atoll
Debunked by Snopes 10/25/2016 (BEFORE the election).
At least get new material, “lefty”.
In her thread Rayne asked: “If a white hat codes malware in part or whole to investigate capabilities, they are only separated from criminal malware producers/sellers/distributors by intent. How does law enforcement determine intent?” Hummm, could it be those selling and distribution thingies?
Orin Kerr weighs in.
The Kronos indictment: Is it a crime to create and sell malware?
https://www.washingtonpost.com/news/volokh-conspiracy/wp/2017/08/03/the-kronos-indictment-it-a-crime-to-create-and-sell-malware/
[This will be interesting. Can this backfire? What happens in regard to malware given away for free? Yes, I know the counter to that, that no malware would ever be created unless there is a profit motive. But, that counter assumes facts not in evidence. Malware exists that is not directly tied to money, but tied to intel which then indirectly leads to future money. I.E., economic espionage]
[What about malware that is leaked/stolen? Example EternalBlue and DoublePulsar? Is not NSA and/or ShadowBrokers complicit in a conspiracy to damage computers?]
Maybe the arrest is all about getting control of the WannaCry ‘killswitch’?
Logical. But, maybe FBI could have just asked Hutchins to give it up? He probably would have.
Could be an OpSec thing. Likely.
https://mobile.twitter.com/msuiche/status/893497181725962240
Is Monero tied to TLA via SB and WannaCry?
Is that why after Hutchins arrest the bitcoins were pulled? Because Bitcoin is not annonymous?
Fits if the ‘killswitch’ domain was somehow tied to the bitcoin.
The ‘story’ about cashing out after bitcoin split, is just that, a story.
Some dots between WannaCry, Hutchins, BTC-e, and Flynn?
As I expected BTC-e would not really die.
First link (lots there) seems to reveal some info that may have been leaked, IMO. I.E., some info that investigators would have likely preferred kept quiet for a bit longer. But, maybe not. Maybe some bait.
https://www..nytimes.com/2017/08/04/us/politics/robert-mueller-michael-flynn-turkey.html
WASHINGTON — Investigators working for the special counsel, Robert S. Mueller III, recently asked the White House for documents related to the former national security adviser Michael T. Flynn, and have questioned witnesses about whether he was secretly paid by the Turkish government during the final months of the presidential campaign, according to people close to the investigation.
Though not a formal subpoena, the document request is the first known instance of Mr. Mueller’s team asking the White House to hand over records.
https://www.coindesk.com/troubled-btc-e-exchange-claims-control-of-databases-and-bitcoin-wallets/
A forum account tied to the cryptocurrency exchange BTC-e has issued a new statement, claiming to be in control of databases and bitcoin wallets days after the site’s domain was seized by law enforcement agencies.
[The last 5 words is your hint]
[A parallel to Wannacry ‘killswitch’ domain]
Hutchins to get out monday on 30k bail so he can travel to wisconsin court. GPS monitor, no internet. Why the indictmemt is tied to wisconsin, who knows?
https://mobile.twitter.com/ChristyNews3LV
https://mobile.twitter.com/MabbsSec/status/893624617142759425
Have you read the indictment? The jurisdiction is spelled out within it. Seems to meet the minimal contacts. Not saying that may not be lame jurisdiction, but it does seem initially minimal. Agree WI is an unusual place for something like this, but it is not per se inappropriate…..yet.