The Info Ops Unit at GRU, Not the Technical Hacking Unit, Hacked the State Boards of Election Servers
As I laid out a few weeks ago, I provided information to the FBI on issues related to the Mueller investigation, so I’m going to include disclosure statements on Mueller investigation posts from here on out. I will include the disclosure whether or not the stuff I shared with the FBI pertains to the subject of the post.
Yesterday, there was a big to-do on Twitter about a story (which subsequently got pulled) claiming that vote totals got changed as part of the Russian attack on the 2016 election. I don’t care to engage the story — which I understand was very weak — directly. There are multiple ways for Russian efforts to have affected the outcome of the election, and the evidence increasingly supports a conclusion that that happened, without vote totals getting changed.
That said, given the focus on changing vote tallies, I want to note something about Mueller’s GRU hacker indictment that has gotten almost no attention. Twelve men were indicted, from two different units of GRU, Units 26165 and 74455. The indictment describes the activities of each department in a way that generally suggests a division of labor, with Unit 26165 carrying out core hacking activities and Unit 74455 carrying out information operations. Here’s what that breakdown looks like.
Unit 26165
Address: 20 Komsomolskiy Prospekt (this is the location spied on by the Dutch intelligence agency, AIVD).
Charged individuals:
- Viktor Netyksho: Commands Unit 26165
- Boris Antonov: “Head of Department” that oversees spear-phishing targeting
- Dmitriy Badin: “Assistant Head of Department” conducting spear-phishing targeting
- Ivan Yermakov: works for Antonov, uses identities Kate Milton, Kames McMorgans, Karen Millen. Hacked at least two email accounts the contents of which were released by DCLeaks. Helped hack DNC emails server released through WikiLeaks.
- Aleksey Lukashev: Senior Lieutenant in Antonov’s department. Uses identities Den Katenberg, Yuliana Martynova. Sent spear-phishing emails to Clinton campaign, including the one to John Podesta.
- Sergey Morgachev: Lieutenant Colonel who oversaw department that developed and managed X-Agent.
- Nikolay Kozachek: Lieutenant Captain. Used monikers including “kazak” and “blablabla1234565.” Developed, customized, and monitored X-Agent used to hack DCCC.
- Pavel Yershov: Helped customize and text X-Agent before deployment against DCCC.
- Artem Malyshev: Second Lieutenant in Morgachev’s department. Used handles “djangomagicdev” and “realblatr.” Monitored X-Agent implanted in DCCC and DNC servers.
- Boris Antonov: “Head of Department” that oversees spear-phishing targeting
Charged actions attributed to named defendants:
- ¶21-22: Spear-phishing targets
- ¶23-25: Hacking into DCCC
- ¶29-30: Stealing DCCC and DNC documents
- ¶33: Persistence in DCCC and DNC servers
Crimes charged to named defendants:
- Count One: CFAA
- Counts Two through Nine: Aggravated Identity Theft
- Count Ten: Conspiracy to Launder Money
Unit 74455
Address: 22 Korva Streett, Khimki (the Tower)
Charged individuals:
- Aleksandr Osadchuk: Colonel and commanding officer of 74455, which assisted in release of stolen documents through DCLeaks, Guccifer 2.0, and the publication of anti-Clinton propaganda on social media.
- Aleksey Potemkin (!!): A supervisor in department responsible for administration of computer infrastructure used to assist in release in DCLeaks and Guccifer 2.0 documents.
- Anatoliy Kovalev: officer assigned to 74455 involved in hacks of State Boards of Election.
Charged actions attributed to named defendants:
- ¶38: Operating fictitious personas promoting DCLeaks
- ¶71-78: Hacking into State Boards of Election (SBOEs) and VR Systems
Crimes charged to named defendants:
- Count One: CFAA
- Counts Two through Nine: Aggravated Identity Theft
- Count Ten: Conspiracy to Launder Money
- Count Eleven: Conspiracy to Commit an Offense against the US
Generally, the indictment describes Unit 26165 as being in charge of the technical hacking, including excruciating detail on what named officer played what role in phishing and malware deployment activities (probably thanks to the AIVD intelligence). The description of the information operations — running DC Leaks and Guccifer 2.0 and working with WikiLeaks — is less specific as to which officer did what, but the indictment clearly assigns those activities to Unit 74455. In any case, the indictment appears to suggest a division of labor, where Unit 26165 carries out the technical hacking and Unit 74455 carries out the information operations.
All 12 GRU officers are charged in Counts One through Ten.
Count Eleven, the ConFraudUs charge, is an outlier, however, in two ways. First, just Unit 74455 officers — Osadchuk and Kovalev — are charged in this operation. And aside from the indictment’s description that Potemkin (!!) runs the infrastructure for Unit 74455, just the description of the phish of the State Boards of Election and VR Systems includes specific details about which Unit 74455 officer was involved in activities attributed to that unit.
All of which is to say that, for some reason, what is described as an information operations unit — Unit 74455 — conducted the hack of election infrastructure, not the technical hacking unit that carried out the other phishes of Democratic targets.
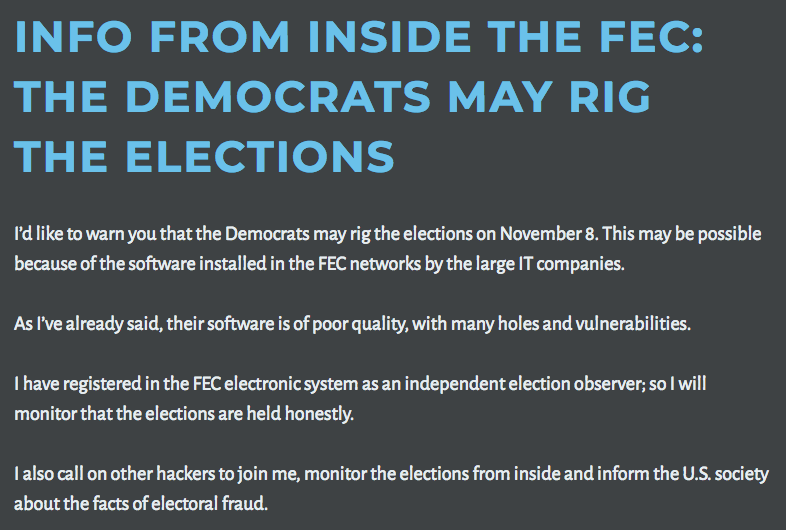
Perhaps the division of labor between these two units is not so clearcut as the indictment lays out. But if it is, then there may be an explanation why the information operations department would be hacking election infrastructure. Remember that in the days leading up to the election, Guccifer 2.0 — according to the indictment, a Unit 74455 operation — predicted the Democrats might “rig the elections.”
Hacks on SBOEs and election vendors would be an easy piece of evidence to point to to claim that Democrats had stolen the election. That is, it could be that these hacks (which, given that Illinois was targeted most aggressively, weren’t going to alter the presidential election) may have been propaganda designed to undermine the Hillary win that never materialized.
Mind you, I still await the results of the investigation into whether there was a tie between the VR Systems hack and oddities in Durham County, NC on election day, something that would amount to voter suppression rather than altering vote tallies.
But it is at least possible that the attacks on our voting infrastructure were designed as propaganda, this time at least, rather than as an attempt to use the information obtained.




Trump has said recently that the Russians were going to hack the midterms in favor of the Democrats because he was so tough on the Russians.
I would not be surprised if they’re thinking about some mischief in some strong blue races on behalf of Democrats to support this narrative, and I would not be surprised if Trump knows it. They could discredit some Dems who would have won anyway, push back on the 2016 narrative, and maximize GOP paranoia and aggrievement.
And quite frankly I could see a good part of the pundit class using such incidents to push a stupid narrative that victorious Dems need to ease up on the GOP and act like centrists in the crazy idea that the GOP will be centrists too and join to fight the Russian hackers. And when the extremists further their hold on the GOP, it will be the fault of Democrats for not being conciliatory enough.
The Russians seem to subscribe to the Underpants Gnome Business Model. The actual result of their actions is simply to enrage the very class of Americans (liberals) that have supported dialogue and negotiation, and empower the Buck Turgidsons of the Defense establishment.
So, you may well be right about the plan, but I wouldn’t bet on the outcome.
Hacking vote counts usually means hacking hundreds or thousands of precincts, or more easily the hacking of the tally gathering servers. Verification of county tallies of precincts must be added to precinct by precinct checks during recounts. Even with the best laid plans stuff happens and one may want to check for abnormalities between servers for those counties with multiple tally gathering servers and variances in down ballot elections..
All to say I agree it is much much easier if the voting database was used to feed back through CA or Nationbuilders for the dark advertising and other voter suppression efforts. Finally the provocation is not the tampering with the database it is in the access to the database.
This sort of operation, which creates chaos no matter what happens, seems to be almost no-lose.
At the very least, doubt is cast onto the legitimacy of the election. If they fail and the winner is Hillary, it empowers years of Republican investigations. If the winner is Trump, he’s in hock to the Russians for his victory; they have kompromat far more devastating than pee tapes.
If they succeed in breaking into voter databases, they can create records of phony (e.g., non-citizen) voters to validate GOP conspiracy theories, or delete Democratic voters to convince them that elections are rigged. If they fail, but don’t get outright nailed, it creates distrust that feeds into conspiracy theories on both sides.
If they succeed in actually changing votes, then they control American politics outright. If they fail, but don’t get caught outright, then confidence in elections is destroyed.
They almost can’t lose. Unless, of course, they have been penetrated from the start, and all they do is ignite American rage and a new Cold War.
When I saw “Potemkin” on the front page of the indictment, I laughed. But I missed the part later on where it said that Potemkin is in charge of infrastructure. Does that make Putin into Catherine the Great?
More seriously . . .
I think you are right to consider the division of labor between these two groups to be solid. Yes, they may cooperate, and certain things may overlap, but every organizational structure has divisions of labor to get things done — especially in the military. I agree with your picture that there’s one group here dedicated to obtaining actionable intelligence, and another group who takes that intelligence and asks “how can we make best use of it?”
When Trump first made his “the elections are going to be rigged so Hillary can win” comment, I took this as typical Trump bluster to lay the groundwork for a day-after speech blaming everyone but himself for his loss. The thing that nagged at me about this was that it suggested that Trump was publicly admitting that he was losing — something he never did directly. He always had a positive poll to cite, or shiny object to point to, indicating that he believed he would win.
Now, though, with what you lay out above, I’m rethinking that. In isolation, the Illinois hack never made sense if this was to influence the 2018 race. The scale of votes you’d have to tinker with in IL would create a result so out of the ordinary that it would immediately set off alarm bells and an investigation would be mounted. It might start with a simple “Did we count those votes correctly” and “did we add up the county-by-county results correctly” to asking deeper more troubling questions down the road. No, the news of this hack said to me that this had to be a 50 state strategy of tampering and the folks in IL were the easiest nuts to crack.
I wonder how Team Mueller has approached interviewing people on this, trying to ascertain the answer to the question “Where did Donald Trump get the notion that the race was being rigged to favor the Dems?” That would be a very interesting trail to follow — especially if the name Mariia Butina shows up along the way.
Thanx Marcy. This post explains enough to me to take one foot off the ledge but as far as November’s election is concerned, North Carolina is obviously a target field that has already been cultivated and is the lynch pin to turning south east Dixie back toward democracy. Do you have any idea about if any sort of counter and prophylactic measures are in place or being built within our federal counter intelligence machinery to protect 2018?
Thank you again.
Thank you Marcy.
If “the boys” had access to DNC/DCCC/ etc. and so on files, could they not change registration data for just one group, say, Democrats, and upload the database to the same place they got it from, overwriting the “old” file with their modified database. One would have to restrict oneself to a small percentage of registrants in order to avoid notice. To me, it would be interesting how many people were turned away from polling places in 2016.
Hence the Durham reference in Norskie’s post:
Read the article. There was chaos in the Democratic stronghold of Durham, with people delayed in voting or prevented from voting entirely. It may have been the result of Russian tampering. The state showed no interest in investigating. Since it was noted in a half dozen precincts, it probably didn’t swing the presidential election. But I don’t think to this day that we know how many votes were affected.
Thanks for drawing attention to this in this thread.
It has been difficult to make sense of all the various snippets of news about electoral hacks.
Clearly voter suppression has been one of the threads/purposes of some of the hacks and the stories created in consequence of the hacks.
But it occurs to me that the example you have given may also have been intended to play into narratives of “widespread voter fraud – multiple voting, the dead voting etc” which Trump made much of with his phoney commission.
I don’t have sufficient grasp of the detail to recall whether the Durham story you cite played any part in that particular Trumpian narrative.
I am also intrigued by the idea that the ground was seeded for the “election was rigged” narrative but it was not followed up on.
This is suggestive of, as one possibility, the Russians toying with Trump and the electoral system issues, being the ones setting the pace and outcome of that agenda. And that in turn is suggestive of dangling and withdrawal of ongoing-quids for ongoing-pro-quo-s.
Of course it was followed up on. It just blew up in Trump’s face. Not that that has stopped their efforts.
Yeah, it seems very clear to me from Trump’s whipped dog appearance whenever he’s on-stage with Putin that there’s an ongoing… relationship.
All large-scale elections will look iffy under the scrutiny of real-time observation amplified by social media: isolated technical failures or overzealous volunteers aren’t as significant threats to a free and fair election as understaffed polling places or purged rolls or flyers saying police will arrest anyone with outstanding traffic tickets. “Free and fair” is about defining acceptable levels of pollution.
The problem as it relates to the US, of course, is multifold: when there’s no consistent benchmark from state to state and county to county with no real auditing standard, who’s to say what’s acceptable? Extreme fragmentation might theoretically limit the scope of any exploit, but the electoral college also magnifies local effects.
Aiming exploits at election infrastructure could well just be a headfuck or a way to set things up for a “results were rigged” scenario, but if it were an attempt to fuck with the actual vote, how might we tell to any degree of certainty?
Most people think that power is based on position or authority. But in a democratic system, power is based on the sense of legitimacy. Thanks to Bush v. Gore and the legitimacy issues it raised, Dubya was a weak president until on 9/11 Americans surrendered power to him.
So the greatest vulnerability of a democratic system is elections. If those are not seen to be fair, elected officials gain no sense of popular legitimacy. You don’t have to stuff the ballot box. Just start wild rumors about “illegals” voting or screw up poll books.
Now, authoritarians want certainty, and the only way to get that is to control the results. Putin stuffs the ballot box to ensure his party controls things. If he can do so in this country, he will. But it will only happen if Republicans let him.
As a counterpoint, I’d argue that “fair” is contextual. A lot of US states have no tradition of free and fair elections, and any attempt to make them so is treated as illegitimate because it comes from outside the ruling infrastructure. For instance, the current NC state legislature derives its capacity to fuck with elections and assert power over the executive and judicial branches from an unfair electoral system, but it’s not going anywhere, because there’s a tradition of undemocratic state government but there’s no tradition of overthrowing undemocratic state government.
I personally believe they were checking voter rolls to cross reference with facebook accounts.
Would make sense for info ops.
Wouldn’t the path of least resistance there would be to exfiltrate them from party/campaign/marketing orgs that have already paid states for bulk voter roll access?
If it’s an info op, then I think the indictment points the way: perhaps not a search for tech vulnerabilities, but for human ones, i.e. phishing targets. Hence the initial search for domains used by parties as well as public officials.
As I’ve suggested previously, paragraph 76 is a kind of cliffhanger. The narrative of the indictment begins (para 21) with Unit 26165 researching and spearphishing DCCC, DNC and Clinton campaign officials, and lays out the consequences as they use the information and access they acquire. Count Eleven describes Unit 74455 researching and spearphishing targets connected to the elections, and stops. We’re not told what happened after the spoofed Vendor 1 emails went out to various counties in Florida. Maybe nothing happened, or the investigators haven’t been able to pin it down, or maybe it’s just not necessary to specify it for the purpose of that charge. But it’s notably tight-lipped when the other counts are happy to dive into details for both the hackers and those hacked.
Thanks Marcy. This sounds correct to my ears. I couldn’t stop shaking my head while reading that Root article. I particularly enjoy the style of the author so it was pretty lame how bad that post was.
This is what happened psychologically to me. This path is hard to admit. It may only have been my experience. But I suspect, while it sounds impossible weak sauce, that such a phenomena could have been much more potent that we all care to admit, even to ourselves. For me, in the the lead up to vote for Clinton, I almost gave up. Lost the wind in my Sails to vote for her. The Comey announcement, second one, yearly did me in. I had a brief moment where I questioned whether I would vote, stand proud, or just sit out. I felt demoralized. (I am probably a far cry more emotional than the likes of most brains on this site. And I live in the Midwest. About as mid as you can get.) I got my butt to this site and a few others and felt the life come back. Enough so that I was able to make it special, and vote together, with my daughter, just 19 years old, her first national election. But I am right now remembering how hard it was to feel positive. I noticed my faced book page working overtime to convince me there were going to be constant legal hassles. New charges. I began to remember the resistance against Obama. It felt hopeless. Also I noticed on Facebook that my Strongest Bernie supporter friends had begun to post reactions to stories that I could not see. I remember seeing outrageous stories that reminded me of “The National Inquirer”. My scary realization, is, how close my brain came to being convinced to give up. How powerful propaganda really is. It’s clear and yet, “they hacked the election” ! , feels more satisfying. Like, “I was critically wounded by a Beebe gun”, verses “I was critically wounded by the newest most powerful rifle”.
I am sure their were specific strategies in Twitter and face book. Perhaps low info, average info, high info voters. It’s really hard to admit to myself that I was swayed. Affected. I imagine I am not the only one. And now to sound like a therapist for a moment. I cannot change what I don’t accept. It feels like saying this out loud is the only way to take the power out of it! I have known others were swayed. But it was my harder to admit to myself, that the stories influenced me as well.
It will be interesting to see what Mr. Mueller’s investigation reveals about Russian interference, but the election was decided by Republican state governments who suppressed the vote in their states by both new and old methods. Republicans simply can’t win a fair election, as most people, even at this stage of our intellectual decline, recognize which side their bread is buttered on.
https://www.gregpalast.com/election-stolen-heres/
Look, Facebook ID’d “bad actors” that joined with known Progressive groups, using divisive social issues like colonialism and sexism to influence the 2018 election.
https://talkingpointsmemo.com/muckraker/facebook-identified-political-influence-campaign-midterms.
Lawmakers were briefed by FB.
There you go. Trump has already said the Russians support the Democrats and will be helping them this year.