The Hack or Attack Debate: Answer Old Questions While Waiting to Learn Enough to Answer That One
As people in government, particularly members of Congress posturing for the cameras, start responding to the SolarWinds compromise, some have adopted a bellicose language unsupported by the facts, at least those that are public. Dick Durbin, for example, called it, “virtually a declaration of war.” That has led to some necessary pushback noting that as far as we know, this is an act of espionage, not sabotage. It’s the kind of thing we do as well without declaring war.
As usual, I substantially agree with Jack Goldsmith on these issues.
The lack of self-awareness in these and similar reactions to the Russia breach is astounding. The U.S. government has no principled basis to complain about the Russia hack, much less retaliate for it with military means, since the U.S. government hacks foreign government networks on a huge scale every day. Indeed, a military response to the Russian hack would violate international law. The United States does have options, but none are terribly attractive.
[snip]
The larger context here is that for many reasons—the Snowden revelations, the infamous digital attack on Iranian centrifuges (and other warlike uses of digital weapons), the U.S. “internet freedom” program (which subsidizes tools to circumvent constraints in authoritarian networks), Defend Forward, and more—the United States is widely viewed abroad as the most fearsome global cyber bully. From our adversaries’ perspective, the United States uses its prodigious digital tools, short of war, to achieve whatever advantage it can, and so adversaries feel justified in doing whatever they can as well, often with fewer scruples. We can tell ourselves that our digital exploits in foreign governmental systems serve good ends, and that our adversaries’ exploits in our systems do not, and often that is true. But this moral judgment, and the norms we push around it, have had no apparent influence in tamping down our adversaries’ harmful attacks on our networks—especially since the U.S. approach to norms has been to give up nothing that it wants to do in the digital realm, but at the same time to try to cajole, coerce, or shame our adversaries into not engaging in digital practices that harm the United States.
Goldsmith’s point about the Defend Forward approach adopted under Trump deserves particular focus given that, purportedly in the days since the compromise became known, Kash Patel is taking steps to split NSA and CyberCommand, something that would separate the Defend Forward effort from NSA.
Trump administration officials at the Pentagon late this week delivered to the Joint Chiefs of Staff a proposal to split up the leadership of the National Security Agency and U.S. Cyber Command. It is the latest push to dramatically reshape defense policy advanced by a handful of key political officials who were installed in acting roles in the Pentagon after Donald Trump lost his re-election bid.
A U.S. official confirmed on Saturday that Joint Chiefs Chairman Gen. Mark Milley — who along with Acting Defense Secretary Chris Miller must certify that the move meets certain standards laid out by Congress in 2016 — received the proposal in the last few days.
With Miller expected to sign off on the move, the fate of the proposal ultimately falls to Milley, who told Congress in 2019 that the dual-hat leadership structure was working and should be maintained.
As Reuters has reported, General Nakasone was pretty hubristic about NSA’s recent efforts to infiltrate our adversaries (Nakasone has, in unprecedented fashion, also chosen to officially confirm efforts CyberCom has made, which he must think has a deterrent effect that, it’s now clear, did not).
Speaking at a private dinner for tech security executives at the St. Regis Hotel in San Francisco in late February, America’s cyber defense chief boasted how well his organizations protect the country from spies.
U.S. teams were “understanding the adversary better than the adversary understands themselves,” said General Paul Nakasone, boss of the National Security Agency (NSA) and U.S. Cyber Command, according to a Reuters reporter present at the Feb. 26 dinner. His speech has not been previously reported.
Yet even as he spoke, hackers were embedding malicious code into the network of a Texas software company called SolarWinds Corp, according to a timeline published by Microsoft and more than a dozen government and corporate cyber researchers.
A little over three weeks after that dinner, the hackers began a sweeping intelligence operation that has penetrated the heart of America’s government and numerous corporations and other institutions around the world.
The failures of Defend Forward to identify this breach may raise questions about the dual hatting of NSA and CyberCommand, but there’s no good reason for these Trump flunkies to take any substantive steps in the last month of a Lame Duck period while it is serially refusing briefings to President Elect Biden’s team. All the more so because the more pressing issue, it seems, is giving CISA, the government’s defensive agency, more resources and authority.
More importantly, while it is too early to determine whether this goes beyond traditional espionage, there are questions that we can identify. For example, one detail that might suggest this was intended to do more than espionage is that the hackers stole FireEye’s Red Team tools. There are information gathering purposes for doing so, but they’re probably not important enough to risk blowing this entire operation, as happened. So we should at least consider whether the SolarWinds compromise aimed to pair intelligence (including that gathered from FERC, one of the agencies targeted) with the means to launch deniable sabotage on key critical infrastructure using FireEye’s tools.
Measurements of whether this is a hack or attack must also consider that the hackers are in a position where they could alter data. Consider what kind of mayhem Russia could do to our economy or world markets by altering data from Treasury. That is, the hackers are in a position where it’s possible, at least, to engage in sabotage without engaging in any kinetic act.
Finally, adopting the shorthand the industry uses for such things, there’s a bit of sloppiness about attribution. The working assumption this is APT 29, and the working reference is that APT 29 works for SVR, Russia’s foreign intelligence agency (even though when it was implicated in key hacks in 2016, it was assumed to work for FSB). I’ve been told by someone with more local knowledge that the relationship between these hackers and the intelligence agencies they work for may be more transactional. The people who’ve best understood the attack, including FireEye, think this may be a new “group.”
While intelligence officials and security experts generally agree Russia is responsible, and some believe it is the handiwork of Moscow’s foreign intelligence service, FireEye and Microsoft, as well as some government officials, believe the attack was perpetrated by a hacking group never seen before, one whose tools and techniques had been previously unknown.
Which brings me to a question we should be able to answer, one I’ve been harping on since the DNC leak first became public: what was the relationship between the hackers, APT 28 (the ones who stole files and shared the with WikiLeaks) and APT 29 (who then, and still, have been described as “just” spying). From the very first — and even in March 2017, after which discussions of the hack have become irredeemably politicized beyond recovery — there was some complexity surrounding the issue.
I have previously pointed to a conflict between what Crowdstrike claimed in its report on the DNC hack and what the FBI told FireEye. Crowdstrike basically said the two hacking groups didn’t coordinate at all (which Crowdstrike took as proof of sophistication). Whereas FireEye said they did coordinate (which it took as proof of sophistication and uniqueness of this hack). I understand the truth is closer to the latter. APT 28 largely operated on its own, but at times, when it hit a wall of sorts, it got help from APT 29 (though there may have been some back and forth before APT 29 did share).
When I said I understood the truth was closer to the latter — that there was some cooperated between APT 28 and 29, it was based on what a firsthand witness, who had been involved in defending a related target in 2016, told me. He said, in general, there was no cooperation between the two sets of hackers, but on a few occasions APT 29 seemed to assist APT 28. That’s unsurprising. The attack in 2016 was ambitious, years in planning, and Putin was personally involved. He would obviously have the ability to demand coordination for this operation, so intelligence collected by APT 29 may well have dictated choices made in where to throw GRU’s efforts.
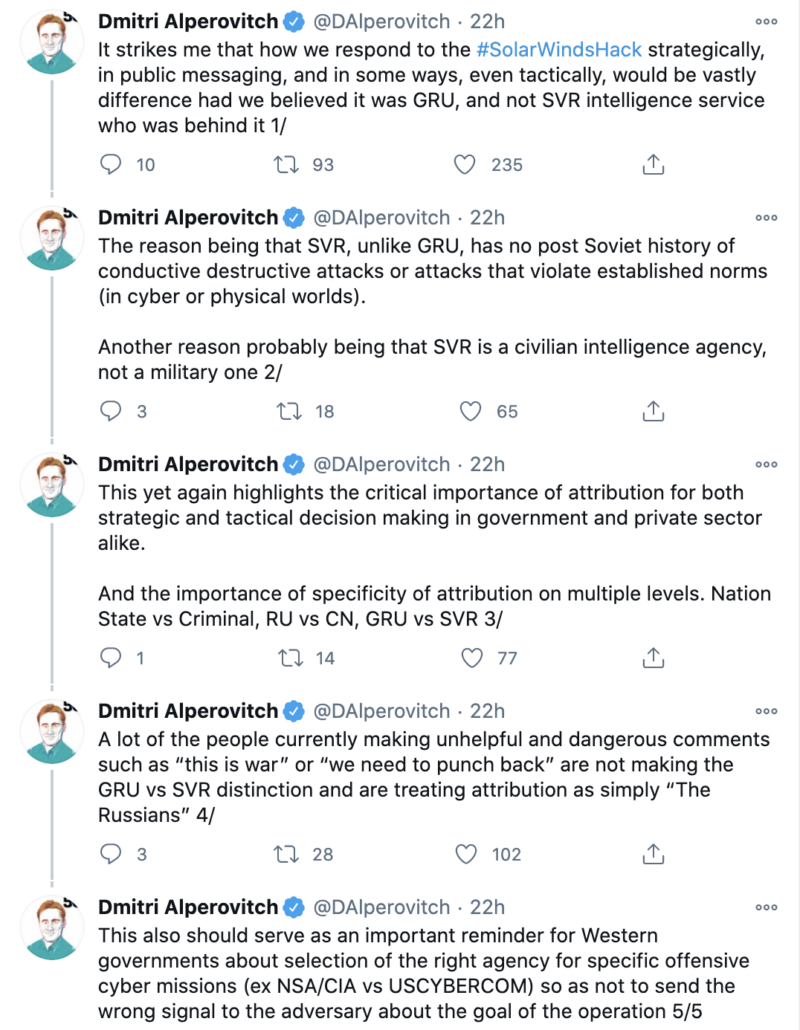
The point is important now, especially as people like CrowdStrike’s former CTO Dmitri Alperovitch recommends responses based on the assumption that this is SVR and therefore that dictates what Russia intends.
So we should assume this is espionage and therefore avoid escalating language for the moment. But having had our assess handed to us already, with a sophisticated campaign launched as we were busy looking for election hackers, it would be a big mistake IMO to rely on easy old categories to try to understand this.
Update: Corrected to reflect that Alperovitch is no longer with CrowdStrike.



 Public domain
Public domain
“Defend Forward” is the sort of euphemism employed to relabel the War Department the Department of “Defense,” but with a much bigger budget.
Despite $ billions on defense, this country can’t protect itself. Our computers are hacked and we’re killing 3000 Americans a day from the virus. The most expensive defense system ever built, a naval carrier group, grounded due to the virus. Now the NSA, despite a huge budget, can’t keep our computers safe.
We’ve lost perspective. We’ve neglected healthcare and education for the expense of security and apparently, the “bread and butter” aspects of security has been neglected too.
Regarding Snowdon, yes, he did reveal that America’s cyber protection was being used against our own people. But don’t forget that Frank Rich reported the same thing years earlier. The real difference is that surveillance was illegal when Rich reported it and ironically, Rich was facing jail for uncovering it.
It’s a bad John LeCarre or Tom Clancy novel.
You mean a bad John LeCarre novel–or a Tom Clancy novel. (The epicure in me speaking.)
I’ve been rolling my eyes at all the caterwauling about war. The hypocrisy is amusing, although I am not unsympathetic. The US is in a very bad place right now. I’m astounded at how bad it is, given that a huge portion of its citizens are essentially cheering on the destruction, and so many of its “leaders” are encouraging the downfall of the nation. This hack comes at a terrible moment, iow. It’s understandable that some of the adults are overreacting somewhat, given the challenges we’re facing. But we ought not lose sight of the fact that the US does this shit all the time.
It was a hell of a punch in the nose, though.
Regarding the FireEye tools, I’d say that it’s a certainty that they were stolen primarily with defense in mind. During the Cold War, when the West would nick a MiG-25 or a surface-to-air system, it was done so as to learn how to defend against it, or to defeat it, not to turn it back against the Soviets. Obviously, these tools represent a weapon that has a much wider range than a single fighter jet, but their motive would have been first to learn how to defend against them. The decision to use them against the US surely came later. (Bonus: they can now use them against their own people, too.)
“That has led to some necessary pushback noting that as far as we know, this is an act of espionage, not sabotage.”
Yeah. The sabotage (after a nine-month-long disinformation campaign, then hacking/vote tampering in 3-4 swing states on election night to steal the election for Trump) happened four years ago–seems a bit too late for the high dudgeon on display currently. Maybe folks are pounding Trump with Kayfabe just to rub it in.
This is great and exactly the analysis I needed towards mentally mapping what may be going on.
Does anyone know, is there a good chart showing the branching relationships and interactions among the RU intelligence agencies and detachments/attachments like the APTs (with respective involvements in both noted* and more obscure prior events — that we’re in unknown territory says to look at their practice work.**)? Finding only rudimentary approximations of what I’m looking for, I don’t know that some results are even safe to click on. [As to a mirror-ish of same re our assets, LMAO at trying to figure out the complexities. Of all the jokes about needing Matrix-like spaghetti plots to map the Mueller investigation … LOL at some notion of simultaneously visualizing all of our trees. Of course the Russian gov apparently “visualized” much of same via the throughput of software vulnerabilities.]
—
*A list of hacks and attacks rapidly becomes unwieldy. Yikes they are busy beavers.
**They’re also super busy all over the African continent, I don’t know why we hear nothing of hacks in countries there, for example (or in the ME), when they’re deploying all other tools (they are in deep in some places w physical presence / mercenaries / government appointment(s), besides ops like Putin’s chef’s trolls riding FB for ideological fun and profit in the CAR, acutely). In other words, their resource extraction gambits _appear_ to be further advanced in some countries there, while mimicking methodologies used here in others. And in exploring whether they’ve run the same plays elsewhere and what that might tell us, versus what they might adapt: What resources do they want of ours besides money, information, useful idiots-cum-“mercenaries” on the ground, time (yeah, let’s not get into the part about them wanting the western seaboard tonight)?
e.g.:
FSI | Cyber | Internet Observatory – Stoking Conflict by Keystroke
https://cyber.fsi.stanford.edu/io/news/africa-takedown-december-2020
Russia Exerts Growing Influence in Africa, Worrying Many in the West
https://www.nytimes.com/2020/01/28/world/africa/russia-africa-troops.html
When do actions of trying over turn the election with completely frivolous lawsuits and White House meetings with convicted felons and coconspirators cross the line to sedition? What entity files the charges and who prosecutes? Or will it be like all trump crimes committed in public view like the hatch act just get swept under the rug. When do we as a public become complicit by acquiescing to this unlawful behavior by a sitting president?
This is a really valuable piece of analysis.
I especially appreciate you calling out the US government for hypocrisy – “gasp – governments use cyber tools for espionage and intelligence-gathering? Whoever could have imagined such a thing???”
I’m just amazed at the acceptance of the US “Clean Networks” initiative designed to freeze Chinese vendors like Huawei vendor out of 5G networks in other countries, as if America has never tried to penetrate networks in other countries for intelligence purposes – or to eavesdrop on its own networks, under (at least) George W Bush, Obama, and Trump.
Have these people ever heard of the the “NSA”? Sheesh.
State Department statement on “Clean Networks” here:
https://www.state.gov/the-clean-network-safeguards-americas-assets/
Propublica article on AT&T cooperation with NSA here:
https://www.propublica.org/article/nsa-spying-relies-on-atts-extreme-willingness-to-help
Espionage instead of sabotage …
“The Journal identified infected computers at two dozen organizations that installed tainted network monitoring software called SolarWinds Orion that allowed the hackers in via a covertly inserted backdoor. It gave them potential access to much sensitive corporate and personal data.
“Among them: technology giant Cisco Systems Inc., chip makers Intel Corp. and Nvidia Corp., accounting firm Deloitte LLP, cloud-computing software maker VMware Inc. and Belkin International Inc., which sells home and office Wi-Fi routers and networking gear under the LinkSys and Belkin brands. The attackers also had access to the California Department of State Hospitals and Kent State University.
https://financialpress.com/staging/2020/12/21/the-wall-street-journal-intel-cisco-nvidia-among-victims-of-solarwinds-hack/
If you look at that list, you might notice some of those folks make the equipment that most of the US as well as large parts of the rest of the world rely on everyday.
These folks listed, if they have any integrity, will be forced to put a lot of resources into painstakingly going through their communications to make certain that current and upcoming products have not in any way been compromised. Those business plans that explore funding options may also have to be scrapped — to prevent inadvertent “hostile” takeovers. Etc. and etc.
So there is some sabotage, just how much is still up for grabs.
Every time I see someone like Brennan going on about “incalculable damage,” I silently beg for a real world example but no one ever has one to offer. So to me this remains a complete but disquieting abstraction.
Re the reorganization of various entities within the Defense/IC realm, where do we suppose Trump got that idea?
Oh, it is real enough:
https://www.forbes.com/sites/forbesagencycouncil/2018/06/01/the-hidden-costs-of-identity-theft/?sh=822f3a9357b5
https://www.experian.com/blogs/ask-experian/the-hidden-costs-of-identity-theft/
That is just with one small part of identity theft.
Another example of identity theft that some time ago was mentioned on this very blog, was the US Government’s Personnel Office was hacked. The information stolen included things like fingerprints, etc. in other words, very detailed information. Information that can be misused to destroy lives.
The information stolen in this hack goes beyond identity theft. It can destroy people, companies, local and regional economies. And amazingly, this type of backdoor is the one being requested by some folks in government.