Guest Post: We Need to Talk about DNS
[NB: This is a guest post by long-time community member WilliamOckham. Give him a shout in comments. /~Rayne]
For most people the Domain Name System (DNS) is one of the most boring topics imaginable. However the Department of Justice’s Special counsel John Durham – through a frothy mixture of technical incompetence and apparent malice in his published court filings – generated unusual interest in DNS from a lot of folks who’ve never thought about it before.
To understand DNS better, here’s an explanation simple enough even for lawyers who would like to keep their bosses from embarrassing them in federal court.
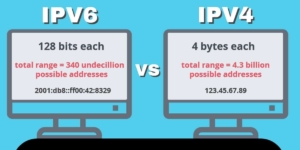
DNS is used to match and link domain names to Internet Protocol (IP) addresses. When one device needs to connect to another device via the internet, it needs to know the other’s IP address. Humans generally prefer to use names. Remembering a person’s or business’s name is much easier than recalling a string of numbers ranging from 12 to 32 digits (32-bits for older IPV4 addresses and 128-bits for newer IPV6 addresses).
I’ll use “example.com” to illustrate a domain name. As you might guess, example.com is a special-use domain which isn’t resolved normally; it can be used to demonstrate how domain names work without inadvertently generating unnecessary DNS lookups.
It’s a lot easier to input www.example.com instead of 2606:2800:220:1:248:1893:25c8:1946 and certainly a lot easier to remember. However your device can’t possibly store the IP address of every damn server in the entire world just to make data entry easier.
Instead, every device on the internet stores the address of one of the thousands of DNS servers. Devices are usually configured to use a DNS server maintained by the internet service provider which provides connectivity for that device.
When your device needs to connect to www.example.com, it sends a DNS lookup request to its primary DNS server. That server doesn’t store the address of every server on the internet either. If you or someone else using that DNS server has asked for that address recently, the DNS server might know the address and send it back to you.
However if it doesn’t have an IP address for example.com, it will issue requests to other DNS servers, looking for one that does know the address. In a worst case scenario, the request ends up going to one of the root DNS servers. They can reach a DNS server for any domain name on the internet.
During the time period subject to Durham’s investigation, virtually all DNS lookups happened in the open, unencrypted. They were recorded by DNS servers. Each time a website address was typed into a browser’s address bar, a DNS server logged the IP address of the device requesting the IP address for some other server. DNS lookup data isn’t proprietary or secret.
Gathering, collating, and analyzing DNS lookup requests, however, is expensive and valuable. It’s a massive amount of data. Billions of DNS requests are issued every day. There are a few companies specializing in managing incredibly large amounts of DNS data. During the time period covered by Durham’s filings, Michael Sussman’s technology executive client (Tech Executive-1) at a U.S.-based Internet company (Internet Company1) worked for such a firm.
Having access to DNS data had nothing to do with hacking servers, spying, surveillance or anything else nefarious. It was part of Tech Executive-1’s job.
Tech Executive-1’s responsibilities included monitoring anomalies in Internet Company1’s DNS database. As one of Durham’s filings indicated, Tech Executive-1’s firm found “that between approximately 2014 and 2017, there were a total of more than 3 million lookups of Russian Phone-Provider-1 IP addresses that originated with U.S.-based IP addresses.”
Contra Durham, 3 million DNS requests for a related IP addresses over a four-year period means these requests are very rare.
For comparison purposes, my best estimate is that my family (7 users, 14 devices) generated roughly 2.9 million DNS requests just from checking our email during the same time frame. That’s not even counting DNS requests for normal web browsing.
If you’re going to make a federal case out of this, at least make some attempt to understand the topic.




Thanks for the explainer, WilliamOckham.
This DNS Lookup stuff is at the heart of the internet, yet most people don’t understand what it is or how it works in spite of using internet services over smartphones, tablets, laptops, and PCs every day.
What Durham’s work has done is like the hacking of the DNC in 2016: a technical peg has been provided around which disinformation could be built, of a technical nature most Americans would be unfamiliar.
This is the “single server” bullshit all over again. There was no “single server” and there was no hacking Donald Trump or his campaign during the 2016 election or the period after the election before inauguration.
You’re right about the “single server” bullshit all over again, etc..
But if Democrats lose the House in 2022, the “single server” bullshit etc. will be real over again and again.
I’m really tired of this argument about Democrats losing the mid-terms when ALMOST EVERYBODY WHO REVILES FASCISM IS SITTING ON THEIR GODDAMNED BUTTS DOING NOTHING.
The Democrats in the House and Senate can’t win unless their base stops whining and does what’s necessary to win. Like being the amplifiers of Democrats’ successes, advocates for their work, getting voters registered AND educated about how to vote in the face of suppression in their own backyards, confronting the suppressive efforts at state and local level.
Do NOT complain about this if you’re doing nothing to defeat the GOP in November. This is an all-hands-on-deck moment in history, after the second Beer Hall Putsch, possibly after the second Reichstag Fire. Get busy winning.
scratch that… (puts glasses back on)
Thanks, WO and Rayne!
We need to talk about editors who slap BS neutral headlines on stories — like the latest debunkings of Dunham’s “investigation” — that convey a nothing-to-see-here vibe. Why is it so hard to call a lie a lie or stupidity stupid?
It would be nice if you offered examples you find egregious.
In general, the media got snookered by the techno talk and their headlines mirror it.
If you’ve got a beef with this post’s headline, too bad. We really do need to have a talk about DNS so the media folks reading this post catch a goddamn clue about Durham’s bad faith investigation and their gullibility.
Who is “We” Kemosabe? Nobody here needs your help, and Mr. Ockham’s post is fine.
Nice explanation, WilliamOckham (speaking as one who has edited a few BIND zone config files).
Thanks again, W.O. I have a feeling I’ll be linking this a lot in the coming days. Unless I can get my SIWOTI (“Someone Is Wrong On The Internet!”) Syndrome under control.
Thank you William. That’s an excellent explanation – certainly better than mine from a couple days ago. However, I think it’s necessary to discuss IP Address assignment so everyone has the full picture. (You probably know more about this than I do, but I’m going to explain it for everyone else.) If you have anything to add, please jump in and do so.
The first possible case in understanding IP Address assignment involves a computer which is a web server, mail server, or something-else server. That server usually has a dedicated IP Address which was set up very carefully by the system administrator, and that address does not change. The server needs a permanent IP Address so every other server can find it.
For example, it’s always possible to contact Google’s DNS server at IP Address 8.8.8.8. That IP Address will only change if Google goes out of business. A server with a permanent IP Address requests Domain Name System service from a dedicated DNS server, also chosen carefully by the system administrator, usually because that DNS server meets an organizations technical or policy goals.
The second possibility for IP Address assignment is that the computer is someone’s laptop, for example, and doesn’t need its own special IP Address. In this case the device is assigned a temporary IP Address via DHCP (Dynamic Host Configuration Protocol) from whatever company is providing Internet service. For example, if you take your laptap to a Starbucks, turn it on, and log into the wifi, your laptop and the Starbuck’s wireless system have a conversation which goes something like this:
LAPTOP: Hi Starbucks!
STARBUCKS: Hi Laptop!
LAPTOP: Hey, could I get an IP Address, some routing information and access to a DNS server?
STARBUCKS: Sure! I’m here to help. Your IP Address is 192.168.1.27. Your gateway to the Internet is 192.168.1.254. Your DNS servers are 132.86.21.145 and 132.86.22.145.
If you take your laptop to Starbucks, then to work, then home, your laptop has this conversation three times and is given three different IP Addresses and three different DNS servers to use. Your laptop’s IP address is not permanent, mainly because it’s not a server and doesn’t need a permanent IP Address.
Note some important issues: First, this happens automatically, and without human intervention. Second, the DNS address given is usually the DNS address of whoever is providing a network connection to the Starbucks (or your work or your house.) Third, DNS is so important that most DHCP servers give out two DNS IP Addresses.
So how does this apply to the Trump case? If you have an AT&T phone, for example, it has the same DHCP conversation with AT&T when you turn it on. And the AT&T DHCP server will always give your phone an AT&T DNS server. A Verizon DHCP server will always give you a Verizon DNS, and so on.
If you’re anywhere in the U.S. neither DHCP nor your server’s admin should ever, under any circumstances, give your device a Russian DNS server. I’ll leave the question of how someone gets a Russian DNS server’s IP Address for those better equipped to answer it, but such a thing should never happen (with the possible exception of a Russian company or the Russian embassy.)
So if any Trump-affiliated device, whether a server, laptop, tablet, phone, or “other” has ever used a Russian server for DNS, something is tragically, terribly wrong, and it’s entirely appropriate for Sussman to go to the FBI and say, “Hey, this looks kinda hinky. I thought I’d let you know.”
If I were working on monitoring DNS Lookups for anomalies and I saw Russian-made devices routing in a way that didn’t match typical US-based traffic on the average Android/iOS device, within a certain network range — let’s say a permanent device IP matching a particular hardware ID, asking for a more direct route to a hinky IP offshore — I think I’d be asking how to contact the FBI.
Especially if I knew there had been cyber attacks on the DoD and the White House beginning in 2014. This was reported in mainstream media.
Given how much ransomware and other forms of cyber attacks have been of Russian origin, I think that would be a wholly normal response. Why wasn’t it seen as normal by the Trump administration?
How much of Durham’s investigation is merely a means to make normal examination of network traffic appear unacceptably abnormal?
I don’t think it is out of the possibility that a Russia phone purchased from a Russian service provider would have a hard coded set of DNS servers. It would be a sneaky yet very simple way for their spies to monitor what’s going on when their folk travel abroad. OTOH its also good opsec which would warrant bringing it to the FBI. I have Google – 8.8.8.8 – set statically as my primary DNS server on plenty of my devices.
On another note… us who work with this tech have a common statement when the network goes tits up. “It’s always DNS”.
When Facebook went down a few month back, DNS was a big part of it.
While it is humbling to reveal my ignorance, curiosity is carrying the day: Is Durham claiming that it is common (3 million, finger to mouth Austin Powers style) for a device in the US to be connected to a Russian DNS server, so neither Sussman nor anyone should have been suspicious of the Trump-associated Russian lookups? And what you smart, diligent (not to say obsessive) people are telling me is that 3 million lookups stand out for being rare and are suspicious on their face? Understand, this question is as basic as it seems. I do get (now) why this has nothing to do with hacking or spying.
I had been called a “hanger-on” around here, with dismissive tone. The description is apt enough; I don’t understand what’s wrong with that. I’m intelligent enough, but I’m never going to do the primary source, Twitter, court ruling, and political press readings the important people here do. I read here daily, follow what I can grasp, and leave with what I hope is the gist of things. From time to time the wit and significance of the discussion impels me to throw in a word or two. I hope not to be annoying. Bottom line is, I care deeply about my country and about truth. Right now, revealing truth is crucial to the survival of my country in any recognizable form. This site gives me a measure of hope in the fog of bs clouding most reporting and discussion. I throw in a couple of bucks, and it’s a bargain. A heartfelt thanks to everyone who make EW what it is.
Yes, Durham explicitly claims 3 million DNS lookups over 4 years is not rare:
(my emphasis)
Thank you. So we have to accept that these traitors lie even about things basic to US security. It’s disgusting.
Just to clarify, it’s ridiculously rare. Something like 300 million Americans have a device capable of reaching the Internet, phone, computer, table, whatever. Every time one of those devices hits a new website a DNS lookup is done. So if each device hits ten websites a day, that’s 3 billion DNS lookups a day, (I’d guess probably more like 30 billion DNS hits daily, though I haven’t looked up the statistics.)
So 3,000,000 Russian DNS hits in three years is about 2740 hits daily, or 0.0000913 percent of our conservative figure of 3 billion DNS hits daily. The number is not just tiny, but microscopic.
In 2012, Google said there were 80 billion DNS lookups every day globally. My best estimate for U.S. only during the 2014 to 2017 time period is ~50 billion.
To give everyone another way to think about this. I fired up a network monitor and captured the DNS traffic on my laptop for six minutes of, relatively speaking, light DNS traffic. There were 75 DNS requests. Multiply times 10, and that would be 750 requests an hour. So, 18,000 a day, or 6.75 million a year from a single laptop. I will grant you that this is mostly Microsoft Teams and Skype (I have to run both of those for work, essentially 24 hours a day). Still, that doesn’t include the DNS traffic from my phone, two tablets, and a couple of IoT devices.
A better comparison would be for one of the servers that I control, directly or indirectly. Unfortunately for you and fortunately for me, I don’t manage any of them on a day-to-day basis anymore (yeah, cloud).
Fifty billion in the U.S. only over what time period? Daily/weekly/monthly/annually? Sorry, but I’m not clear on this.
Per day
I did a little long division and 1 DNS hit out of 18.25 million (or 0000055 percent of all queries) goes to a Russian DNS.
IANAL but I think Durham’s contention that Russian DNS lookups are common could be properly described as a flat-out lie. (Something else he failed to do was consult an expert.)
Well, consulting an expert wouldn’t get Durham the cherry-picked results he wanted, nor offer barely plausible deniability.
No. But I hope it gets him clobbered in court.
I don’t think the average user realizes how many lookups even browsing to a most popular website can generate, like advertising beacons. This stuff has exploded since 2012 so ~50 billion is very conservative for US internet users. Not to mention apps on smartphones.
Fantastic example of how to explain tech stuff. My compliments to WilliamOckham.
I have, a few times in the last 10 years, done business with Russian needlework suppliers (a couple of knitting books and embroidery spring hoops). So my very US computer would show up asking for DNS information leading to Russia.
There will be a LOT of users in the US with traffic to Russian IP addresses and they won’t even know it’s happening. I’ve run across several sites which don’t have About Us and murky registration information, but have an extremely tiny .ru counter on the site.
I’ve wondered what the point was besides planting subtle disinfo, parking domains for future influence operations, or data collection — but it may be that Russian operations want to hide in a larger volume of traffic even as Russia tightens its own internet to limit its citizens’ access to the rest of the world.
Great write up on the DNS. Thank you William Ockham.
To be clear, the DNS analysis, you would need access to the actual DNS server logs, which is the owner of the DNS servers.
For a regular home user, the ISP provider owns the first hop DNS server, then it could use other DNS servers from ISP to the final destination.
For a corporation, they may have internal DNS servers, but that is irrelevant for these discussions, since we are talking about the DNS analysis once it enters the internet.
The tech executive company can get logs from the DSN servers that are part of the internet DNS ‘hops”. Since this traffic is open source, not personal communication, it doesn’t require a court order, I’m assuming they just buy that info. And this is what Trump calls “spying”.
At least this is my understanding.
It’s “spying” in the same way an advertising demographics data purchase from Facebook about semi-anonymized users might be “spying.”
Yet less like “spying” than Aleksandr Kogan’s unethical nonconsensual acquisition of Facebook users’ data later used by Cambridge Analytica/SCL by the Trump campaign.
So much projection on Trump’s part; any and every time he pules about “But they’re spying on me,” we should look for the spying Team Trump is doing.
Yes it is projection, just need to clarify the messaging. The way Trump and enablers operate, they generate outrage about the DNS traffic analysis, then later if there are real issues with what Trump does, he turns around and false equates it with the DNS fake outrage.
Except that’s not how it worked with the hacking of DNC. The hacking to benefit Trump came first long before he’d claimed he’d been hacked. The DNC “single server” bullshit served to inoculate the public’s perception against any other claims of hacking, thanks to media’s inability to cut through the technological fog and its eagerness to sustain anything which looked like “But her emails!” even if unrelated.
Yes, true.
I was just saying that in the future, Trump and co may spin the DNS traffic explanations that are now part of the Sussman case, to equate with some of their cons that may come up, the projection issue.
This is why the messaging is so important in my view, keep it really simple if possible. I should follow my own advise.
They are always one step ahead in their coning. While we explain the current con, they are planning/covering the next 100 cons.
Sorry for the confusions, not good on explaining very well.
Also you just need the DNS server logs for the first DNS server on the ISP side, it will have the destination even when it needs to involve additional DNS hop, for both incoming/outgoing traffic.
MAC, ARP, and RARP oh my.
Your explanation was fine. Every internet device has an IP address. DNS is like a local map. But not a world map. Navigating addresses sometimes means checking several maps.
Durham is serving misinformation.
[Welcome back to emptywheel. Please use the same username each time you comment so that community members get to know you. You used “GrantS” when you were here last, please revert to it as we have more than one user named “Grant.” Thanks. /~Rayne]
It’s pretty clearly a case of just throwing around a technical term and some associated numbers without digging into the details at all.
What I find interesting is that Durham’s filing says “Fewer than 1,000 of these lookups originated with IP addresses affiliated with Trump Tower” to try to attack Sussman and attempts to put it into context by saying “there were a total of more than 3
million lookups of Russian Phone-Provider-1 IP addresses that originated with U.S.-based IP addresses.”
Which means approximately 1 of every 3,000 lookups *nationwide* came only from Trump Tower. And if you think for a second that there are 300,000,000 internet users nationwide, that would make the number more suspicious, not less. If you were talking about strict proportionality, Trump Tower should have had one or two lookups out of those 3,000,000, not 1,000.
But what little I know about DNS lookups though is that you can’t think in terms of simple proportionality, especially when looking at tiny subsections of traffic. You just can’t. This stuff is much too complicated and a refutation like Durham offered is just stupid.
I’m guessing that Sussman didn’t just do a quick back of the envelope look at raw numbers, because those can be wildly misleading on a small scale. You have to look at the details, not a few random numbers, and hopefully that’s what Sussman did.
That specific details about the 1000 lookups were avoided along with the Russian-made devices is intriguing.
The lack of so much detail of the Durham rebuttal is just weird.
It would be like disputing a coroner’s report that someone died of a gunshot wound by pointing out a lack of blood on the victim’s toe.
What he cited is not just something you’d cite if you lacked better evidence. It’s something you’d cite if you didn’t even know what constitutes good evidence.
Looks like bad faith to me when a Special Counsel notes in a filing the defendant’s concern about “supposedly rare, Russian-made wireless phones in the vicinity of the White House” and expects a reasonable response would be to ignore this in spite of Russian hacking DoD in 2014, the White House in 2015, and the DNC in 2016.
Long time ago, worked for a defense contractor.
When Snowden fiasco happened, at work, they send us email to tell us about the WikiLeaks, and to make sure we understand that we should not access the WikiLeaks web side.
We were not supposed to try it even from our home computer.
I suspect if anybody tried to access the WikiLeaks from work would show up in DNS logs, so maybe this is why they send out the email, they didn’t want to risk loosing contracts.
They also worry – a lot – about malware getting into one of their company computers and then into their network.
Very clear and concise, WO. Thank you.
There is so much gaslighting in Durham’s filings, I wouldn’t be surprised if the printed copies aren’t marked “keep away from fire or flame.”
Many thanks to WO and Troutwaxer for a clear and direct explanation. Now I have a question.
The first time my browser on my PC tries to contact a site such as irs.gov, it doesn’t know the IP address (192.168.1.101). So it requests the IP address from DNS.
The second time I surf to the IRS, does my PC retain that IP address? Meaning, no DNS lookup? If so, is this address cached permanently, or for a limited time?
From my limited grasp, I recall one possible explanation for the Trump-marketing email server doing so many DNS lookups of Alfa Bank was that the server administrator had misconfigured the caching of Alfa’s DNS address. I realize that a web browser and an email server are different beasts.
————
The Yota phones are a whole ‘nother issue. It may be weeks or months before enough is known. Why ship / carry a phone from Russia, when anonymous burners can be purchased in hundreds of locations in NYC and DC? Maybe military-grade encryption, maybe to keep logs inaccessible to US law enforcement?
In general, most web browsers will cache the IP address for a server for the duration of a single session. That statement is true for what most people think of when they hear “web browser”, “server”, and “session”. Browsers are not supposed to cache IP addresses across sessions.
The caching that is referred to explain the weird Trump.Org DNS traffic is different. It’s about the server side of the DNS story (one that I studiously avoided in the post in the interest of not confusing everyone). That would be a whole ‘nother explainer…
Thanks, WO. Rather than hand you another ball of yarn to untangle, can you point me to a source laying out the activities between Trump-mail, Spectrum Health, and Alfa Bank?
Crensonsecurity.com posted a chart showing 79% of the DNS lookups came from 2 Alfa Bank servers. Do we know what roles these servers performed? IIRC, when my web browser queries irs.gov, irs.gov has my IP address, and does not query DNS.
Here is the Crebs article:
https://krebsonsecurity.com/2021/09/lawsuits-indictments-revive-trump-alfa-bank-story/
The client (a browser, for example) doesn’t know the IP address of the server, so DNS lookup is required. Once the client has the server’s IP, it sends requests that include both the server’s and the client’s IP addresses. So the server doesn’t need a DNS lookup for the client.
DNS doesn’t say anything about roles. That’s usually specified by another number included in the request: the ‘port’ number (HTTP for example, runs on port 80, DNS is on port 53). You’d need to intercept communication between the client and the server to learn the port number (and only a subset of possible port numbers are explicitly defined, so it might not be definitive).
Note that the information we have is from logs reporting what happened between the client and the DNS server, but we have nothing about the client-to-destination server other than who that destination is (domain name and IP address).
“The caching that is referred to explain the weird Trump.Org DNS traffic is different.”
I’d like to know more about that (and it’s not a subject I have any expertise in.)
WilliamO (or anyone else), would you care to speculate on what kinds of setups might cause such traffic? Some thoughts I’ve had include:
1. an app installed on the Trump server specifically configured to connect to a Russian domain name
2. a (possibly Russian) device connected to a Wifi network that’s calling home from behind a Trump firewall (where the firewall is being called a server)
I’m not sure if either of those would properly explain the traffic, just throwing them out there as possible examples.
I won’t speculate any further because I don’t have enough information about the traffic in question end to end.
This is where I get confused: I interpret Krebs’ chart to mean that the Alfa Bank server initiated 2,764 DNS requests over 4 1/2 months. So when people say “A Trump-linked server communicated with Alfa Bank” I think that is wrong. Please correct me if so.
I have not seen any evidence that trump-email.com or Spectrum Health were requesting a DNS address for Alfa Bank. I don’t doubt the bad intentions on the US side of the interactions, but I just want to know who was doing what.
Forgive me if I am too far down in the weeds, not meaning to derail the discussion. I think 2,764 redundant requests is far more than an accident or a coincidence.
Link to Krebs article:
https://krebsonsecurity.com/2021/09/lawsuits-indictments-revive-trump-alfa-bank-story/
You’re right. The lookups were *for* the Trump server, not from it.
From Krebs’ chart, it’s possible that Alfa Bank sent a lot of emails to mail1.trump-email.com in that four month period. Not necessarily suspicious, although the shutdown once it became public is peculiar. And the start-up activity on the new domain name even more so.
The requests from Heartland Payments could be related to legitimate payroll issues. Spectrum Health could similarly be related to insurance if Trump was using DeVos’s company.
That bit about SPF Records is interesting. Any mail server that receives an email from that IP can look up that SPF record which tells the mail server which domain names are allowed to send email using that IP address. Many email providers (certainly all the big ones: GMail, HotMail, etc) will reject, or mark as SPAM, mail from a domain that’s not listed in the SPF record. So mail1.trump-email.com could only send emails to a mail server that doesn’t perform SPF validation (like a small, privately set up server).
Later he says: “No servers associated with Alfa Bank ever conducted a DNS lookup for trump1.contact-client.com again…”. Sounds like someone did the lookup for the new name, got the IP, and then configured the IP (instead of the domain name) so that no subsequent DNS would occur.
WO pointed out that we don’t know which ports Alfa Bank’s servers were trying to connect on. Which means we don’t know what applications were running on their hardware.
A large server can run a dozen applications concurrently, especially under light demand.
My admittedly ignorant speculation is that there was no communication; the Alfa Bank server was a sigil beacon, running a script.
When the trolls in St Petersburg had a data dump planned, someone would phone Ivan at the bank’s IT department, and Ivan would ‘bump’ the network cable on the server. The server logs would not show any activity causing this. When trump-mail.com stopped getting pings, a text would go out to Brad Parscale / Roger Stone / whoknows, who would prep the right-wing noise machine.
Just my paranoid, uninformed speculation. But the fact that someone in a bank in Moscow knows trump-mail.com, Spectrum Health and Heartland Payment is a curious coincidence.
(Once again, apologies to WO, Troutwaxer and other IT experts if I am muddying the waters here.)
“This DNS Lookup stuff is at the heart of the internet, yet most people don’t understand what it is or how it works..” I for one, sure don’t, but fully expect it to be attacked big time in the near future. Maybe it’s just general depression, because up here the dark comes way too early, plus doc says I got the seasonal affective D, and then there’s no more football, and it’s the 12 degree doldrums with just tanks and tanks and tanks. Whenever you see the tv it’s just commercial sat up-close vids of tanks spinning circles on the frozen tundra like them beauty Russian and Ukrainian ballerinas and figure skaters. WaPo and NYT just said Prez just said spooks just said that war in Europe is coming soon to a tv station near you. Looks like old joe 70 year old vlad just lusts after owning them young Ukranians
meg·a·lo·ma·nia | \ ˌme-gə-lō-ˈmā-nē-ə
, -nyə \
Definition of megalomania
1 : a mania (see mania sense 2a) for great or grandiose performance an outburst of wildly extravagant commercial megalomania — The Times Literary Supplement (London)
2 : a delusional mental illness that is marked by feelings of personal omnipotence and grandeur
Jeux sans frontiers
https://www.youtube.com/watch?v=_2skJCpQFL8
The author of this post is very well known to the proprietors of this joint, and he is very good on this.
You should have stopped after the first two sentences. This isn’t the place to dump your depressive babbling, speaking of mania. Go seek better guidance for dealing with your depression, SAD or not, before DDoSing a thread with this nonsense.
Next comment like this from you I will bounce; after 233 comments to date you know we expect better than this twaddle.