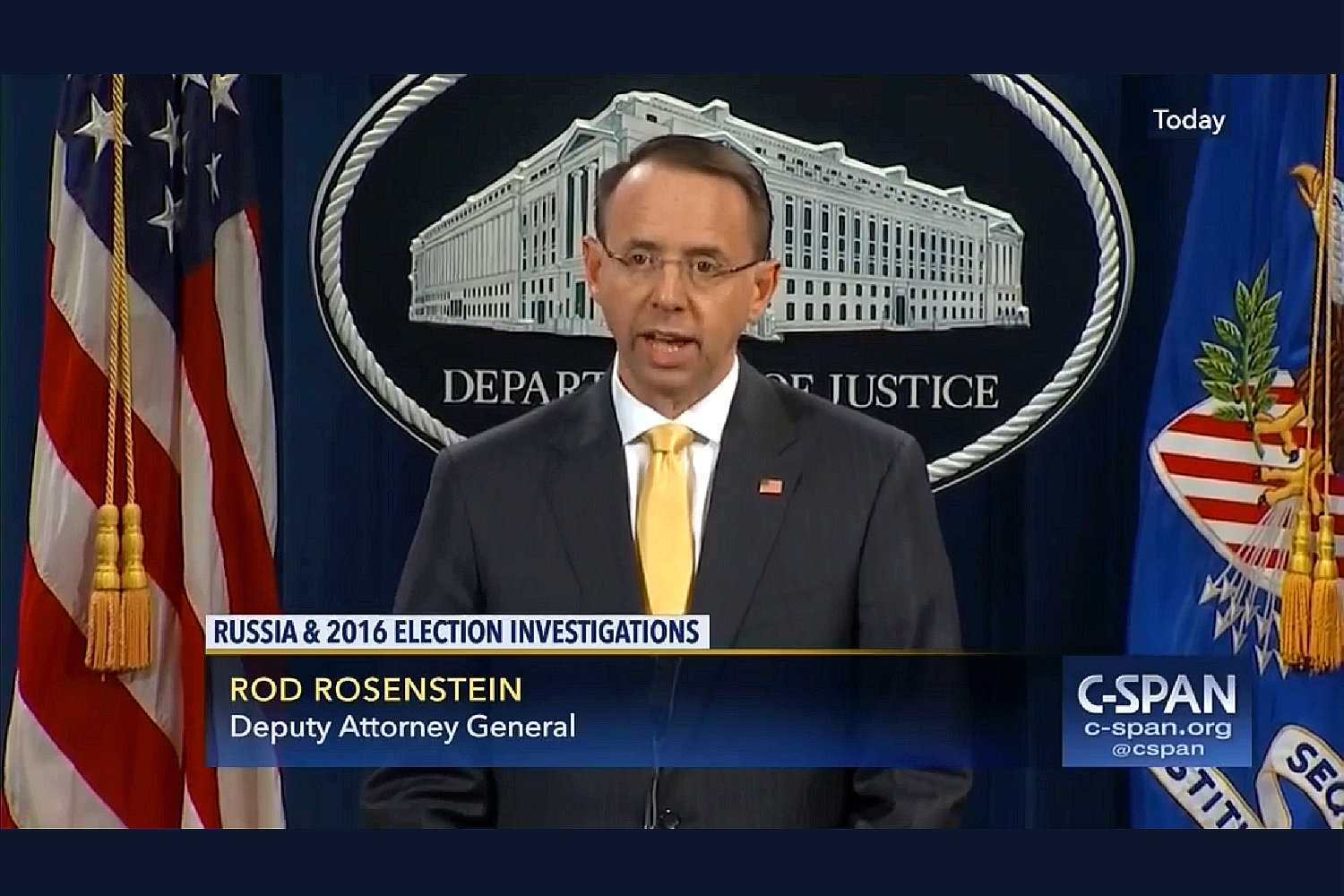
Rod Rosenstein’s Baltimore Club of Men Gunning for the Bidens
In an interview yesterday with Jake Tapper (transcript), Rod Rosenstein exhibited more familiarity with the Robert Hur report, which had been public for just three days, than he was about the Mueller investigation that he oversaw for two years, during ten months of which, Hur played a key role.
Tapper: He was your deputy at the Justice Department. Do you agree with his decision that Biden should not be charged, it was not a prosecutable case?
Rosenstein: Yes, Jake.
And it’s — most people haven’t read the entire report. And I don’t blame them. It’s 345 pages, about 1,400 footnotes. It’s very dense and well-reasoned. And I think, if you read the whole report, you will conclude that Rob reached a reasonable decision that, given all the circumstances, that prosecution is not warranted.
After all, Rod Rosenstein was personally involved in drafting (though did not sign) the Barr Memo making a prosecution declination for Trump for his obstruction-related actions. Yet not even Rosenstein, who had been involved in the investigation from the start, thought to address the pardon dangles — a key focus of Volume II of the Mueller Report — that continued to undermine ongoing investigations.
Then, over a year later and under pressure from Lindsey Graham for having signed the worst of the Carter Page FISA applications, Rosenstein agreed with Graham’s false portrayal of the investigation as it existed on August 1, 2017, when Rosenstein expanded the scope of the investigation.
Lindsey Graham: (35:02) I am saying in January the 4th, 2017, the FBI had discounted Flynn, there was no evidence that Carter Page worked with the Russians, the dossier was a bunch of garbage and Papadopoulos is all over the place, not knowing he’s being recorded, denying working with the Russians, nobody’s ever been prosecuted for working with the Russians. The point is the whole concept that the campaign was colluding with the Russians, there was no there there in August, 2017. Do you agree with that general statement or not?
Rod Rosenstein: (35:39) I agree with that general statement.
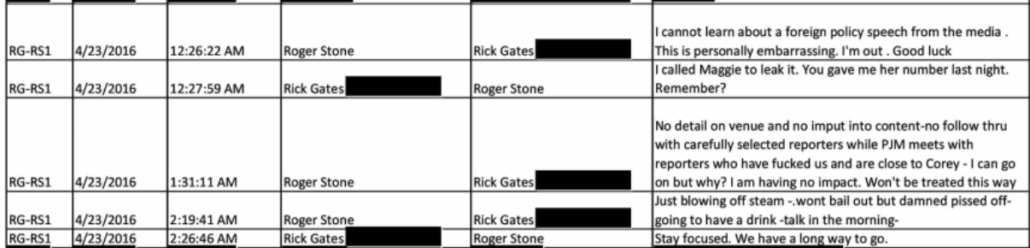
Rosenstein’s endorsement of Lindsey’s statement about the evidence as it existed in August 2017 was egregiously wrong. Mueller had just acquired a great deal of evidence of conspiracy, including several details implicating Roger Stone and Paul Manafort that were never conclusively resolved. Crazier still, George Papadopoulos had just been arrested for lying to cover up when he learned that Russia planned to help Trump, an arrest of which Rosenstein would have personally had advance notice.
By comparison, days after its release, Rosenstein exhibited great confidence in his knowledge of the 1,400 footnotes his former deputy included in the report.
To be sure, Rosenstein’s defense of Hur did not honestly present the content of the Report. For example, the only other reason he provides for why Hur didn’t charge Biden, besides Hur’s opinion that Biden is a forgetful old geezer, involved the tradition of Presidents taking things home.
ROSENSTEIN: I think so, Jake.
And you identified the controversial elements of the special counsel’s report. It’s a very long report, 345 pages, and has a lot of information in there, other reasons why prosecution would not be warranted. And one of them is the history and experience of prior presidents and potentially vice presidents as well taking home classified documents.
This is simply a misrepresentation of the evidence.
Even if you ignore Hur’s misstatement of DOJ’s application of 18 USC 793(e) in cases where there is no other exposure (in something like a leak) or the challenges in applying it to someone who, like both Biden and Trump, didn’t hold clearance, for the primary set of documents he examined — the two folders of Afghanistan documents found in Biden’s garage — Hur admitted he couldn’t prove his already inventive theory of the case. He couldn’t even prove that the documents in question had been in Biden’s Virginia home when Biden made a comment about something classified in his home.
Rosenstein is, as Hur already did, emphasizing the most unflattering part of the declination decision, not the fact that after blowing over $3M and reading through Joe Biden’s most personal thoughts, Hur simply didn’t find evidence to support a charge.
Twice, Rosenstein disputed that Hur’s focus on Biden’s age was the kind of gratuitous attack for which he had made the case for firing Jim Comey, the second time in direct response to a question about the memo he wrote.
Tapper: I want to read from a memo you wrote in 2017 in which you criticized James Comey’s infamous press conference in which he criticized Hillary Clinton’s handling of classified e-mails, even as he declined to prosecute her, a similar circumstance, although he wasn’t a special counsel — quote — “Derogatory information” — this is you writing — “Derogatory information sometimes is disclosed in the course of criminal investigations and prosecutions, but we never release it gratuitously.
“The FBI director laid out his version of the facts for the news media as if it were a closing argument, but without a trial, it is a textbook example of what federal prosecutors and agents are taught not to do” — unquote. By going to the lengths he did to critique Biden’s age and memory, even as he was clearing him of a crime, how do you differentiate between what Robert Hur did that you say is OK from what James Comey did that you say is not?
ROSENSTEIN: Jake, there are several significant differences between those two examples.
One is, most fundamentally, that Jim Comey wasn’t the prosecutor. He was the head of the FBI. His job was to ensure the police collected the proper evidence, submitted it to the prosecutors. And, ultimately, it’s up to the prosecutors in the Justice Department and the attorney general to make a decision about what information is released.
Rob Hur was the prosecutor. It was his job to make that decision, to make that recommendation to the attorney general, who, as you acknowledged, has previously committed to make this report public. That’s one difference.
The second difference is the special counsel regulation. In the ordinary case, Hillary Clinton was not investigated by a special counsel. There was no procedure to make those reasons public. Here, it’s baked into this regulation.
Now we sit, Jake, 25 years down the road. That regulation was passed by Attorney General Reno in 1999. Now we have 25 years of experience. I think it’s worthwhile to sit back and ask whether or not this is the right procedure. Do we really think that we ought to have prosecutors writing reports for public release of everything they discover and all the reasons for not prosecuting?
Or is there a better way to do that without having all the embarrassing information come to public light?
The big tell in Rosenstein’s defense of his former deputy, though, is his suggestion there’s a comparison between Hur’s attacks on Biden’s age with what Mueller — under the direction of Rosenstein and Hur — included in his report, which spent far fewer pages laying out the prosecutorial analysis for far more potential criminal exposure by Trump.
The second issue is what you release in the public. And the problem here with — that’s really baked in the special counsel model is that it’s not really the function of a prosecutor to publicly announce the reasons why they’re not prosecuting.
And so when you layer that into the process, it can result in unfortunate consequences. The Donald Trump report, I think, got people upset in the same way that this one did.
Given his inclusion of Independent Prosecutor Lawrence Walsh here, Rosenstein’s comparison is insane, because he left out the Ken Starr Report (to which investigation, he reminded Tapper, he contributed), which included the most gratuitous descriptions of the subject of the investigation of any of these reports.
Rosenstein’s likening of the Mueller and Hur report is odd for a number of reasons. The part of the Mueller Report focused on Trump was 200 pages, far shorter than the Hur Report yet covering far more overt acts.
Mueller made absolutely no complaint that both Trump and his failson refused to appear before a grand jury whereas Hur’s attacks arose out of Biden’s willingness to sit for several days of a voluntary interview. Mueller let Trump’s decision to invoke the Fifth stand without ascribing criminal motive; Hur made Biden’s cooperation into cause for attack.
But even in smaller details, the reports don’t compare. One thing Hur made up, for example, is that Biden might have alerted his attorneys that there were classified records (in a ratty beat up old box) in his garage, but his team couldn’t find out because if they asked, the answer would be privileged.
We considered the possibility that Mr. Biden alerted his counsel that classified documents were in the garage, but our investigation revealed no evidence of such a discussion because, it if happened, it would be protected by the attorney-client privilege.
This claim only appears in the Executive Summary, where lazy journalists might find it. It appears nowhere in the body of the report (which has to deal with the fact that if Biden had really brought these documents home, he wouldn’t have so willingly let his attorneys search for them). It’s one of the things Biden’s attorneys asked to be corrected.
There are a number of inaccuracies and misleading statements that could be corrected with minor changes:
- ‘We considered the possibility that Mr. Biden alerted his counsel that classified documents were in the garage but our investigation revealed no evidence of such a discussion because if it happened, it would be protected by the attorney-client privilege.” Report at 22. In fact, your investigation revealed no evidence of such a discussion because it did not happen–not because of any privilege. The President testified he was unaware that there were any classified documents in his possession. Tr., Day II, at 2, 41-42. You did not ask him in his interview or in the additional written questions if he had “alerted his counsel” about classified documents; if you had, he would have forcefully told you that he did not.
Hur’s decision to fabricate the possibility of an attorney-client conversation that did not happen — and his obstinate refusal to correct it — is especially telling given Mueller’s hands-off treatment of attorney-client privilege.
For example, Mueller didn’t even try to ask Jay Sekulow about his role in drafting Michael Cohen’s false claims about the Moscow Trump Tower, even though Cohen said Sekulow was involved.
The President’s personal counsel declined to provide us with his account of his conversations with Cohen, and there is no evidence available to us that indicates that the President was aware of the information Cohen provided to the President’s personal counsel. The President’s conversations with his personal counsel were presumptively protected by attorney-client privilege, and we did not seek to obtain the contents of any such communications.
Nor did Mueller attempt to interview John Dowd about whether he left a threatening voicemail for Mike Flynn’s then-attorney Rob Kelner, to find out whether Trump directed Dowd to make the threat.
Because of attorney-client privilege issues, we did not seek to interview the President’s personal counsel about the extent to which he discussed his statements to Flynn’s attorneys with the President.
In both cases, Mueller let privilege close off investigation into more egregious evidence of obstruction.
So where Mueller let Trump hide behind attorney-client privilege as a shield, Hur flipped that, and used a fabricated attorney-client conversation as a shield to insinuate evidence of guilt where none existed.
In short, Rosenstein went on teevee and made a bunch of cynical claims, defending Hur’s attack on Biden even while claiming that the Mueller Report was just as damning.
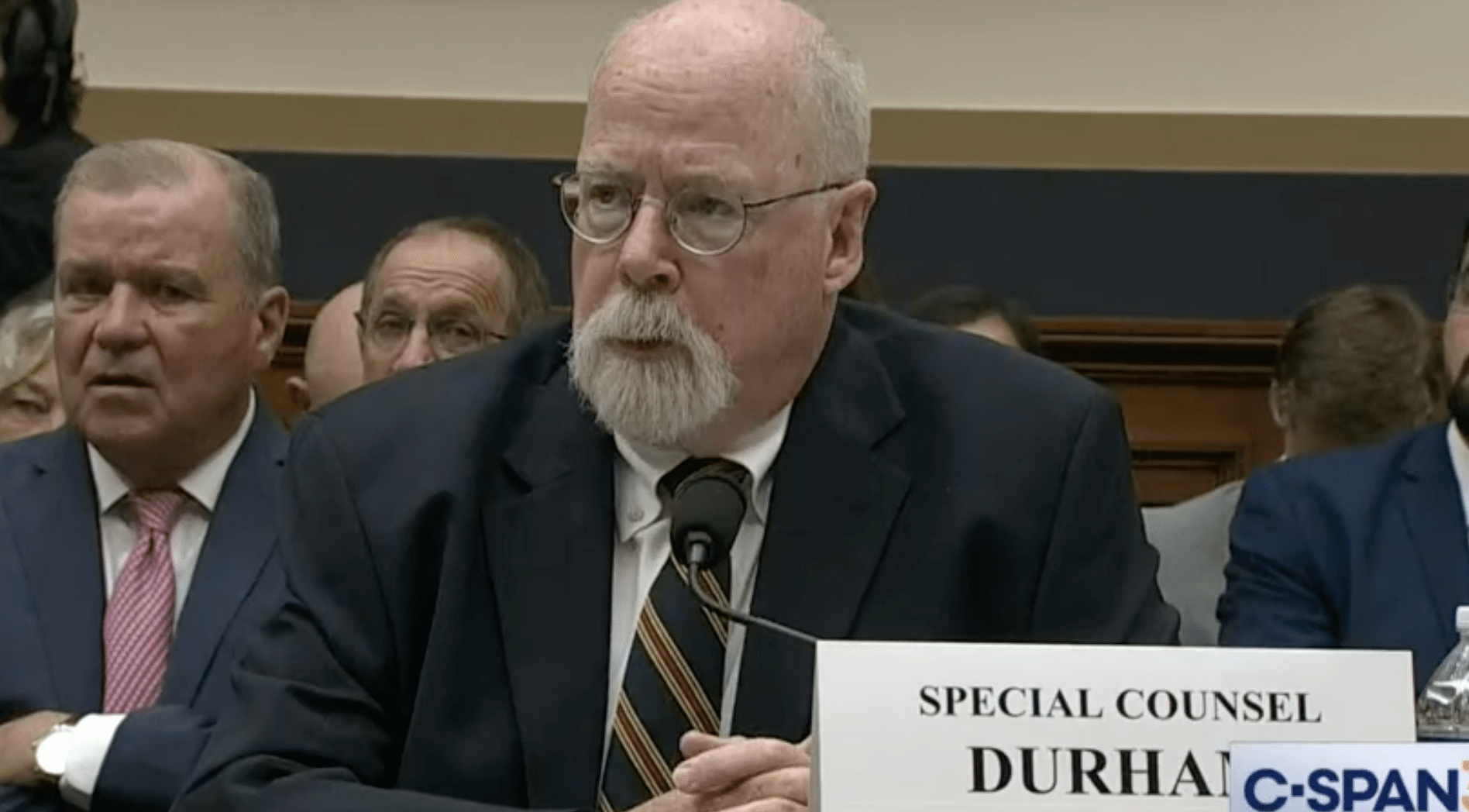
As I and others contemplate how Merrick Garland made such a shitty choice for Special Counsel here, I keep thinking about the fact that there’s a little club of Rod Rosentein associates gunning for the Biden men. There’s Hur, and Rosenstein’s hypocritical and remarkably hasty defense of him.
There’s also the reference that Gary Shapley, who is based partly in Baltimore, made about a prosecutor who became Deputy Attorney General, a reference that can only describe Rosenstein.
Mr. Shapley. No. I think I’ve said it, that this is not the norm. This is — I’ve worked with some great guys, some great prosecutors that went on to be U.S. attorneys and went on to be the deputy attorney general and, I think I have experience enough to where it means something.
After having agreed with the IRS that the case against Hunter Biden couldn’t move forward if Shapley were on the team, David Weiss then decided to appoint two AUSAs who would have worked for Hur and Rosenstein as AUSAs in MD USAO, in the case of Leo Wise, for years.
That is, the cabal of men gunning for Joe Biden and his son — all of whom have already engaged in questionable games — have ties to Rod Rosenstein, who still seems to be trying to make it up to Trump for his role in appointing a Special Counsel.
And Rod Rosenstein, as he demonstrated in that interview, is giving Hur, at least, special license to engage in precisely the kind of conduct for which he endorsed firing Jim Comey.