Refusing to Take Yes for an Answer: Remember the Pardons in the Desk Drawer
One notable aspect of yesterday’s hearing on Trump’s absolute immunity claims is the fact that James Pearce — and through him, Jack Smith — refused to take yes for an answer.
They refused to accept what Judge Florence Pan, at least, seemed to suggest would be the quickest way to get to trial.
Throughout the hearing, Judges Michelle Childs and Pan seemed persuaded by American Oversight’s amicus argument that Midland Asphalt prohibits this appeal. While Childs never seemed to fully concede that point, after Pearce responded to a Childs’ argument by stating that because this involves a President, the immunity analysis is different, Pan asked Pearce why he wasn’t adopting the American Oversight argument. Pearce responded, first, by emphasizing the goal of “doing justice” and so getting the law right, and only secondarily getting to trial quickly.
Judge Pan: Why aren’t you taking the position that we should dismiss this appeal because it’s interlocutory? Doesn’t that advance your interests?
Pearce: Our interests are two-fold. One, as in United States versus Nixon, it is in doing justice. And the second is to move promptly to satisfy the public’s and the defendant’s interest in a prompt resolution of this trial. But doing justice means getting the law right, and our view is even if a dismissal on jurisdiction might move this case faster — actually, empirically, that’s hard to know — we just don’t think that’s the right analysis here, on either immunity or the second claim.
So Pan set about figuring out how they could use the hypothetical statutory jurisdiction to reach the merits even if she and, especially, Childs still had doubts they were allowed to do that.
Pan: If we have discretion to reach the merits versus just dismissing this case under Midland Asphalt, which I think is a strong precedent which which suggests that this appeal is interlocutory and does not fall under the collateral order doctrine, how should we determine how to exercise that jurisdiction, about whether or not we should reach the merits?
Pearce: So I think in the American Hospitals decision, the 2020 decision, the court said, the formulation was something like, we’re doubtful as to our jurisdiction but nonetheless, invoking the line of cases you’ve just described, went on to decide the merits. We would urge the court to do the same here, even if it entertains doubts with respect to the jurisdiction. Yes, hypothetical statutory jurisdiction is available under the law of the circuit. The court should use that to reach the merits.
At least some of the panelists on this worthwhile Lawfare Podcast about the hearing took that “doing justice” line to be fluff, and took the “empirical” questions about whether rejecting this appeal on jurisdictional grounds would really speed things up.
But I’m not so sure.
Granted, later in the hearing, Pearce provided some explanation for why a rejection on jurisdictional grounds might not help move things along. It came as part of a discussion of two questions: Childs’ question about whether the panel should rule on the broad question of presidential immunity, as Judge Chutkan had, or whether — as Judge Henderson at least entertained — they should assess whether a president was immune from prosecution for the crimes, as charged in the indictment, as most Motions to Dismiss are treated. In the same discussion, Henderson asked twice about how to apply the Blassingame decision in this context. Both these questions are about whether Trump can be prosecuted only because of the nature of the charges in the indictment, or whether as an ex-President he can be charged, regardless of what the charges are.
But as the discussion proceeded, Pearce voiced some of the concerns about what a more narrow ruling would do to the prosecution.
Childs: Are we to look at the broader question that was dealt with by Judge Chutkan with respect to Presidential immunity, no, absolutely immunity for no criminal prosecution of official acts, versus looking at this indictment and accepting as true the allegations that are brought there. Or both?
James Pearce: So we have a strong preference that the court adopts the former view, and looks at the question — in the way, as the District Court did, which is to say, based on questions of separation of powers, of constitutional text, history, precedent, Is there, in fact, immunity for a former President?
We think the answer to that is no, for of course all the reasons we put in the brief and I’m happy to sort of address here. Candidly, I think if the court gets to that second question, there are some hard questions about the nature of official acts. And frankly, as I think Judge Pan’s hypothetical described, I mean, what kind of world are we living in if, as I understood my friend on the other side to say here, a President orders his Seal team to assassinate his political rival and resigns, for example, before an impeachment? Not a criminal act.
President sells a pardon. Resigns, or is not impeached? Not a crime.
I think that is [an] extraordinarily frightening future, and that is the kind — if we’re talking about a balancing and a weighing of the interests — I think that should weigh extraordinarily heavily in the court’s consideration.
Henderson: Let me ask you about the effect of Blassingame. How does it either bind us. How is it persuasive to us.
Pearce: So, I think it, formally, has no application at all, because of course very early on in the opinion, the court says, “we’re not dealing with any questions of immunity in the criminal context.” I tend to agree with my friend on the other side that in many respects, it does reinforce the nature of the Fitzgerald standard outer perimeter standard. It says, you don’t look at intent, or you don’t look at purpose. Context plays a more important role than — often — the content of communications. I think the significant change of course is the acknowledgement of looking at a President — whether that President is acting in his or her role as office-seeker or office-holder.
But, again, to go back to my response to Judge Childs’ question, although that would change the nature of whether — it may change the nature of whether certain things are or are not official acts in the indictment, we just think that’s entirely the wrong paradigm to use. We think that under Fitzgerald — in fact, that would be inconsistent with Fitzgerald’s reasoning — and it’s also just irreconcilable with the nature of how criminal law works. I mean, to say that we’re not going to take account of motive or intent? There are plenty of acts that, everyday, I mean, for example, if I were going to encourage someone not to testify at trial because I wanted to go on a hike with that person, it’s not a crime. If I were to encourage someone not to go on a hike because their testimony a trial — sorry, encourage them to skip their trial testimony because their testimony was going to incriminate me?
It’s the same underlying act.
And now, when you map that onto the criminal–onto the Presidential context, you come up with some of the frightening hypotheticals where as long as something is plausibly official, even if it involves assassinating a prominent critic, or a business rival? That would seem to then, be exempt, potentially, from criminal prosecution, we certainly wouldn’t concede that. If that’s the world we need to live in. I think we would advance plenty of arguments below, but we really — but those arguments themselves would create satellite litigation that are an additional reason not to go down this route.
Childs: But looking, and thinking about your answer about potentially not looking at, your argument about motive and intent, when there is a criminal prosecution, that mens rea and that intent is part of the actual statute charged criminally.
Pearce: Yes. Precisely. And that’s why it wouldn’t make sense to use this non-motive — as I understand how Fitzgerald outer perimeter standard might work, it could say, “those types of official acts, official conduct, that is something from which a President is immune.” You don’t ever get to that second question of, well, did that person act with mens rea, can we prove it beyond a reasonable doubt, because at least under a theory where it’s not available at trial, then there’s no way to reach that conduct.
Childs: When we’re looking at this indictment, though — back to Judge Henderon’s question about the use of Blassingame. Some of the acts are the same or similar, and there was direct discussion of that in that opinion as determining whether it was office-seeker versus office-holder. So do we use Blassingame, at least for that?
Pearce: So if this court decides the case the way the district court does — did, pardon me — then I don’t think Blassingame has any role to play at all. Because there is no question of whether, you know, is this act official, or were these sets of allegations official? The question is, based on a Fitzgerald analysis and history, precedent, et cetera, is there any quantum of immunity for a former President. We think the answer to that question is no. There’s no reason, as the district court also found, to turn to the indictment and consider the outer perimeter, this civil outer perimeter standard.
Henderson: How about if you don’t decide it? On the Blassingame. [inaudible]
Pearce: If you don’t, [inaudible, cross talk] so there are a lot of different ways this court could not decide it that way. I think, to pick up on my response to Judge Childs, we certainly stand by our view in the brief that some substantial number of allegations would fall outside of an outer perimeter, and that, I think, is enough to affirm, I think either party is encouraging the court at that point to send the case back to the District Court. I think that would then create a series of challenging questions that I mentioned earlier: What are the evidentiary theories under which that evidence could potentially come in? And, but it would be our strong view and we would want, if the court followed that route, which we would urge the court not to, to make clear that immunity is an on-off switch. Right? This is the immunity appeal. If the court says, we affirm, we send it back, there’s no immunity. Then other things become evidentiary questions, or questions of jury instructions, which any appeal is then an appeal from a final judgment, if any final judgment.
Childs: And the immunity defense is never lost?
Pearce: Um, well, I don’t think it’s immunity at that point. I think this court, in what I’ve just described, will have said there is no immunity. There may be some other types of challenges, as evidence comes in at trial, but again, I think that would lead to this extraordinarily complicated litigation that is, not the topline reason, but certainly among the reasons why the court should not go down that path. [emphasis added]
As Childs and Pearce laid out, one problem with defining immunity in the criminal context with regards to official (in Blassingame, actions taken as an office-holder) and non-official (in Blassingame, actions taken as an office-seeker) acts is that criminal law, including the laws charged here, pivot on mens rea. Trump can’t be convicted of obstructing the vote certification, for example (assuming SCOTUS sustains its adoption with January 6), unless prosecutors can prove he had “corrupt purpose” in doing so, however that ends up being defined.
But also, if you’re going to split presidential immunity based on a categorization about official and unofficial acts, the evidentiary disputes become impossible. It would draw out that phase of litigation, probably requiring several hearings, but also would create expansive basis for appeal.
One argument John Sauer made yesterday, for example, is that because in Knight, the Second Circuit held that Trump’s Twitter account was a public forum on which he could not conduct viewpoint discrimination, it made his Tweets official acts. If the DC Circuit rules on an official/unofficial split, Trump would undoubtedly argue that under Knight none of his Tweets could come in as evidence, at least three of which are among the most critical pieces of evidence in the case.
But, as Pearce said, the difficulties such a split would create was not the topline concern here. They want DC Circuit to reach the merits, and they want DC Circuit to rule broadly, as Chutkan did.
I don’t think that “doing justice” comment is fluff. Immediately after Pearce presented his not-topline concern about how a categorical ruling would affect the prosecution, he and Pan returned to the theme of the hearing: The Seal Team Six assassination.
And also, selling pardons.
Immediately after that exchange — which was close to the end of Pearce’s time — Pan came back to what, as this really accessible George Conway column lays out, she had stripped things down to be the key issue.
Pan: Since President Trump concedes that a President can be criminally prosecuted under some circumstances — he says that is true only if he is first impeached and convicted by Congress, do you agree that this appeal largely boils down to whether he’s correct in his interpretation of the Impeachment Judgment Clause? That is, if he’s correct, that the Impeachment Judgment Clause includes this impeachment-first rule, then he wins, and if he’s wrong, if we think the Impeachment Judgement Clause does not contain an impeachment-first rule, then he loses?
Pearce: So I think that’s basically right. I mean, the defendant’s theory over the course of this litigation has evolved a bit, and I think, now, before this court, I understand the argument to be the principle submission to be as you’ve just described — what we call in our brief the conditioned precedent argument. That there is only liability — criminal liability for a former president — if that President has been impeached and convicted.
And that is wrong for textual, structural, historical reasons, and a host of practical ones, one of which I’ll start with again, to just amplify the point. It would mean that if a former President engages in assassination, selling pardons, these kinds of things, and then isn’t impeached and convicted? There is no accountability for that, for that individual. And that is frightening. [my emphasis]
While Pearce addressed Sauer’s historical argument briefly, this was close to the end of Pearce’s argument, and really the key point of the hearing. Pan had (as Conway laid out) stripped the issues down to whether Trump’s view on impeachment is correct, and then Pan had demonstrated, using hypotheticals, how impossibly absurd that outcome would be.
James Pearce and Florence Pan don’t want to give Joe Biden an easy way to legally assassinate Trump, only Trump is asking for that.
Pan’s laser focus on those hypotheticals provided Pearce opportunity to repeatedly do what he did far more subtly starting in October. As I argued then, the five hypotheticals that Pearce floated in October were all near analogues for Trump’s known actions.
- Trading pardons to dissuade criminal associates from testifying against someone
- Ordering the National Guard to murder his critics
- Ordering an FBI agent to plant evidence on his political enemy
- Taking a bribe in exchange for a family member getting a lucrative contract
- Selling nuclear secrets to America’s adversaries
Todd Blanche (one of the lawyers representing Trump in both the stolen election and stolen documents cases, and so someone who is intimately familiar what kind of paperwork DOJ discovered, along with hundreds of classified documents, that Trump took with him when he left office) responded to this line of argument by calling the hypotheticals treason and suggesting they might be private acts, but arguing, as Sauer did yesterday that there would still be a remedy: impeachment.
10 Ignoring actual lessons from history, the Government provides a list of lurid hypotheticals that have never happened—including treason and murder. Response, at 20 (speculating that a President might “murder his most prominent critics” or “sell[] nuclear secrets to a foreign adversary”). Some or all of these hypotheticals, depending on the facts, would likely involve purely private conduct, rendering them irrelevant here. See id. Yet even if such examples somehow were within the outer perimeter of a President’s duties, it is overwhelmingly likely the House impeach and the Senate would convict, and the offending President would then be subject to “Indictment, Trial, Judgment and Punishment” by criminal prosecution. U.S. CONST. art. I, § 3, cl. 7. That is the process the Constitution provides, and the prosecution may not ignore it here. [my emphasis]
As Pan had laid out, though, one part of Trump’s argument for immunity is actually bigger than that, arguing for immunity regardless. Indeed, that’s how Pearce presented this very same argument in his appellate response. He took Trump’s claims of absolute immunity at his word, describing that these scenarios — but not the pardon one — would be flat-out legal.
The implications of the defendant’s broad immunity theory are sobering. In his view, a court should treat a President’s criminal conduct as immune from prosecution as long as it takes the form of correspondence with a state official about a matter in which there is a federal interest, a meeting with a member of the Executive Branch, or a statement on a matter of public concern. That approach would grant immunity from criminal prosecution to a President who accepts a bribe in exchange for directing a lucrative government contract to the payer; a President who instructs the FBI Director to plant incriminating evidence on a political enemy; a President who orders the National Guard to murder his most prominent critics; or a President who sells nuclear secrets to a foreign adversary, because in each of these scenarios, the President could assert that he was simply executing the laws; or communicating with the Department of Justice; or discharging his powers as Commander-in-Chief; or engaging in foreign diplomacy. Under the defendant’s framework, the Nation would have no recourse to deter a President from inciting his supporters during a State of the Union address to kill opposing lawmakers—thereby hamstringing any impeachment proceeding—to ensure that he remains in office unlawfully. See Blassingame v. Trump, 87 F.4th 1, 21 (D.C. Cir. 2023) (President’s delivery of the State of the Union address is an official act). Such a result would severely undermine the compelling public interest in the rule of law and criminal accountability. [my emphasis]
An analogue for Pan’s (more vivid) Seal Team Six hypothetical was in there: the National Guard order. And an analogue for her military secrets was in there: selling nuclear secrets.
But pardons aren’t in that brief. The only discussion of pardons in it pertained to the Nixon pardon.
Indeed, it was Sauer who briefed pardons, not Pearce. In an attempt to “prove” that presidents had committed crimes that had not been charged before, he cited the Marc Rich pardon — or rather an Andy McCarthy paywalled column about it — to imply that Bill Clinton committed a crime that had not been prosecuted.
The government argues that the absence of any prior criminal prosecution of a President in American history merely “reflects … the fact that most presidents have done nothing criminal.” Resp.Br.37 (citation omitted). This claim is untenable. App.Br.17 (citing examples of Presidents accused of crimes in official acts, from John Quincy Adams to Barack Obama). American history contains many such examples—President Reagan’s alleged involvement in Iran-Contra, President Clinton’s pardon of Marc Rich, President Bush’s claims of “weapons of mass destruction,” President Nixon’s firing of Archibald Cox, etc. 5 None of the above conduct was prosecuted. “Perhaps the most telling indication of a severe constitutional problem” with this prosecution “is a lack of historical precedent to support it.” Seila Law LLC v. CFPB, 140 S. Ct. 2183, 2201 (2020) (cleaned up).
5 Tim Arango, Ex-Prosecutor’s Book Accuses Bush of Murder, N.Y. TIMES (July 7, 2008), https://www.nytimes.com/2008/07/07/business/media/07bugliosi.html; Andrew C. McCarthy, The Wages of Prosecuting Presidents for their Official Acts, NAT’L REVIEW (Dec. 9, 2023), https://www.nationalreview.com/2023/12/the-wagesof-prosecuting-presidents-over-their-official-acts/; The Editors, Iran-Contra Scandal Begins with Shredded Documents, HISTORY (Nov. 13, 2009), at https://www.history.com/this-day-in-history/oliver-north-starts-feeding-documentsinto-the-shredding-machine.
With regards to Iran-Contra, Pearce noted that “in Chapter 27” of Special Prosecutor Lawrence Walsh’s report, “assumes that President Reagan is subject to prosecution and says, but we didn’t get there evidentiarily.”
In response to Judge Pan’s hypotheticals yesterday, he returned to noted authority, Andy McCarthy’s opinion, about Marc Rich, then said again that pardons had come up historically and not been charged. Pan raised it as a hypothetical, but Sauer wanted to make good and sure that pardons could not be charged because, he said, Andy McCarthy says so.
But then both times Pearce mocked the implications of Sauer’s logic, he did raise selling pardons, even though he left it off his response brief. And he added the scenario of corruptly getting someone not to testify against oneself by inviting them on a hike!
Incidentally, according to Anna Bower, Walt Nauta — the aide who has refused to explain what he knows about what happened to the stolen classified documents that got brought to Bedminster in 2022 — along with his attorney Stan Woodward (and of course Boris Epshteyn), were at yesterday’s hearing.
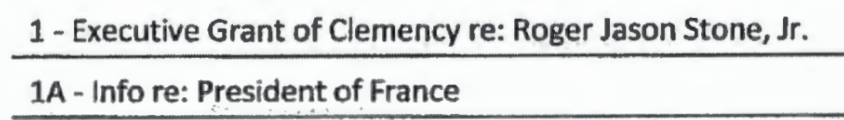
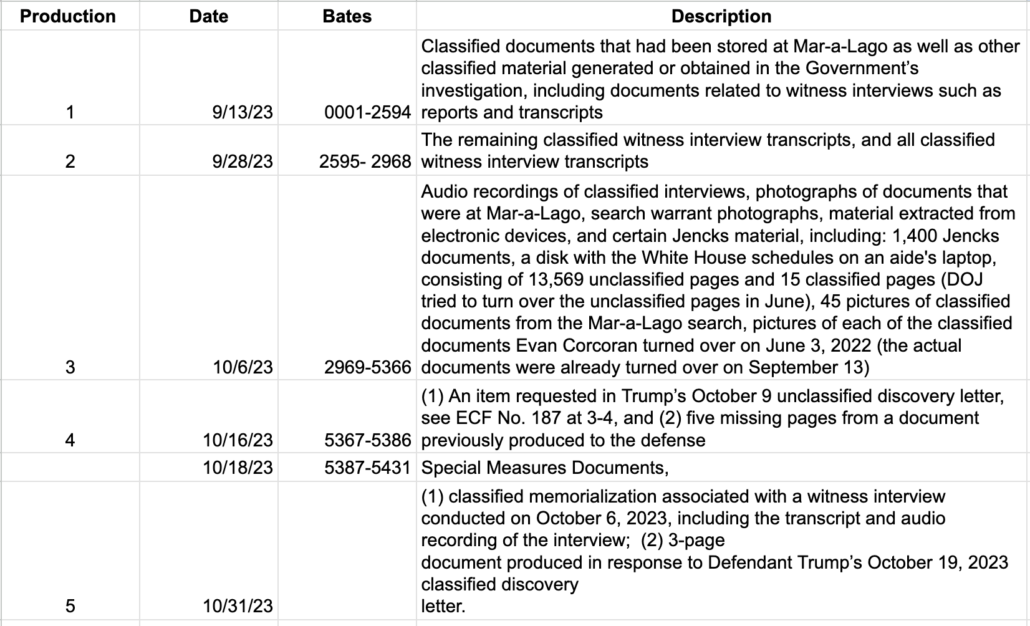
But the reason — one reason — why I find the way the way pardons have gotten floated repeatedly in this claim of absolute immunity is that, along with hundreds of documents, including nuclear secrets, found at Mar-a-Lago on August 8, 2022, DOJ found documentation about clemency granted by Donald Trump, probably including that of:
Oh, and also, some kind of clemency document — one that has some tie to Emmanuel Macron and therefore possibly a pardon beyond the one we know about — for Roger Stone, the guy who was convicted after refusing to disclose the substance of conversations he had with Donald Trump about advance knowledge of the Russian hack-and-leak. The same guy who, in 2020, was allegedly plotting assassinations with his former NYPD buddy Sal Greco.
It’s certainly possible that James Pearce — and so Jack Smith — want to have a clear decision that presidents can be prosecuted for their official acts simply out of getting the law right.
But both sides in this argument seem to understand there’s something more going on.