Yesterday, the two sides in the Michael Sussmann case submitted the proposed jury questions they agree on and some they disagree on.
Durham objects to questions about security clearances and educational background (presumably Durham wants to make it harder for Sussmann to get people who understand computers and classification on the jury).
Sussmann objects to questions about April Lorenzen’s company and Georgia Tech.
He also objects to a question that assumes, as fact, that the Hillary campaign and the DNC “promoted” a “collusion narrative.”
I suspect Sussmann’s objections to these questions are about direct contact. For all of Durham’s heaving and hollering, while Sussmann definitely met with Fusion GPS, of the researchers, the indictment against Sussmann only shows direct contact with David Dagon. Everything else goes through Rodney Joffe. Plus, a document FOIAed by the frothy right shows that Manos Antonakakis believes what is portrayed in the indictment is at times misleading and other times false, which I assume he’ll have an opportunity to explain at trial.
As regards the campaign, as I already noted, when Sussmann asked Durham what proof the Special Counsel had that he was coordinating with the campaign, Durham pointed to Marc Elias’ contacts with the campaign and, for the first time (over a month after the indictment), decided to interview a Clinton staffer.
Sussmann will probably just argue that Durham’s plan to invoke these things simply reflects Durham’s obstinate and improper treatment of a single false statement charge as a conspiracy the Special Counsel didn’t have the evidence to charge.
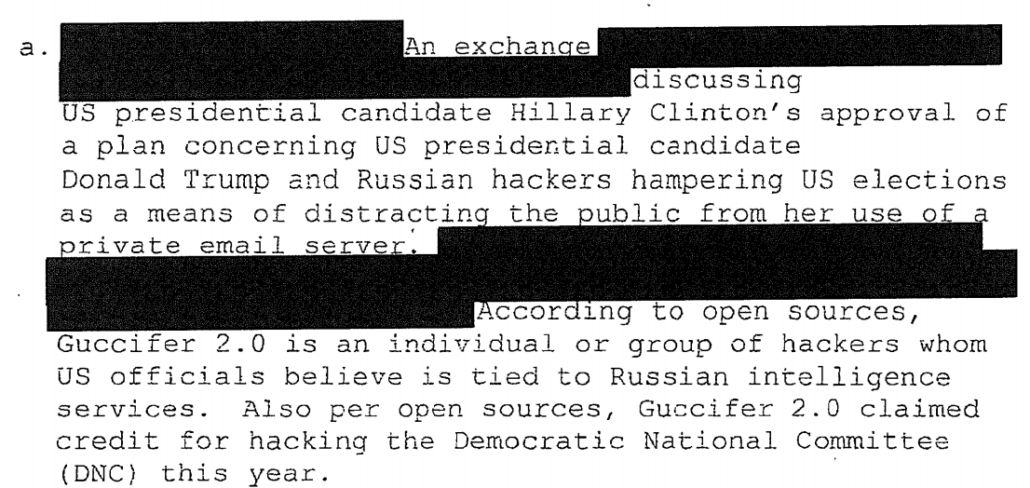
But Durham’s inclusion of it makes me suspect that Durham wants to use an intelligence report that even at the time analysts noted, “The IC does not know the accuracy of this allegation or the extent to which the Russian intelligence analysis may reflect exaggeration or fabrication.” Nevertheless, John Ratcliffe, who has a history of exaggeration for career advancement, declassified, unmasked Hillary’s name, and then shared with Durham.
If Durham does intend to use this, though, it would likely mean Durham would have to share parts of the Roger Stone investigation file with Sussmann. That’s because the report in question ties the purported Clinton plan to Guccifer 2.0.
And as the FBI later discovered, there was significant evidence that Roger Stone had been informed of the Guccifer 2.0 persona before it went public.
That information, along with a bunch of other things revealed about Stone’s activities before this Russian report, suggest the Russian report may actually be an attempt to protect Stone, one that anticipated Stone’s claims in the days after the report that Guccifer 2.0 was not Russian.
Unless Durham finds a way to charge conspiracy in the next two months, Judge Christopher Cooper would do well to prevent Durham from continuing his wild conspiracy theorizing. Because it’s not clear Durham knows where the strings he is pulling actually lead.