A World War of Economic Attrition
[NB: check the byline as usual, thanks. /~Rayne]
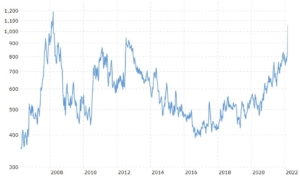
We’ve discussed in comments this past week the possibility Russia’s invasion of Ukraine will deeply affect the global wheat market. It’s already affected wheat futures pricing dramatically.
But wheat futures are only the tip of the iceberg. We are looking at the unfolding of a world war aimed at economic attrition; its effects need to be gamed out.
An important if informal assessment by Maxim Mironov, professor at IE Business School—Madrid (Instituto de Empresa, S.L.), was shared in a Twitter thread (translated here from original Russian into English):
Many people ask me to comment on the sanctions.
In short, my scientific conclusion as a professor of finance, doctor of the University of Chicago is FUCKED.And double fucked up that the inhabitants of Russia, even the educated, for the most part do not understand what awaits them.
I explain on….. fingers.
Very soon, the Russians will face a shortage of basic products. I’m not talking about all kinds of iPhones, the import of which has already been banned, but about food, clothes, cars, household appliances, etc.
Russia is very strongly integrated into world trade. And already the largest operators refuse …
…send containers to Russia. But even if a miracle happens and Russia finds someone who is ready to send containers to Russia for three meters, the question is how to pay for it? Export earnings will decrease significantly, as all buyers will try to abandon Russian …
..goods. We see that even non-sanctioned oil companies cannot find buyers for their oil. Gazprom, the main exporter of gas, is already under sanctions, that is, it is generally unclear how it will receive foreign exchange earnings.
The Russian Central Bank has accumulated a huge money-box, 650 billion ….. dollars. Only more than half of these reserves have already been arrested, and what to do with gold is also not very clear. Few banks in the world will want to buy it from the Russian Central Bank, so as not to fall under sanctions or huge fines themselves.
Many people think that Russia over the past years ….. built a bunch of factories, only all these factories – automobile, aviation, household appliances, etc. actively use imported components. That is, in the coming months, we will face the shutdown of entire industries with all the ensuing consequences – a shortage of goods, mass…
… unemployment, respectively, a fall in tax collection and, as a result, problems with the payment of salaries to state employees.
Planes even within Russia will also soon stop flying. After all, almost all of them are imported, and the West has already been banned from supplying spare parts. Therefore, we will soon see a massive…
.. decommissioning of aircraft.
The Internet as we knew it will also be shut down. They have already blocked a bunch of information sites, one of these days they are going to block Wikipedia. Twitter and Facebook are already slowing down. Going to shut down YouTube.
About agriculture. Are you aware that....in Russia, the share of imported seeds is almost 40%? And for potatoes, the share of imported seeds is 90%? That is, of course, farmers will come up with something over time, but at least in the short term, we should expect a shortage of basic agricultural products and a sharp rise in prices. And that’s not all either..
..Everyone who can leave the country will start to leave. Already actively felled. The government understands this, which is why they introduced a bunch of measures today to keep IT people. Only they won’t work. Therefore, it is very likely that exit visas will soon be introduced for certain categories or completely …
… will close the country.
The only plus from this story is that those who are nostalgic for the USSR will be able to feel all its delights in their own skin. And it will not be a relatively herbivorous USSR like Khrushchev-Brezhnev-Gorbachev, but a USSR headed by a crazy dictator.
P.S.
Here is today’s news, illustrating the scenario described in the thread. Avtovaz has already stopped. And it seemed that it should not depend on imports at allAvtovaz will suspend the assembly of cars due to a shortage of electronic components. Work was stopped for four days
(link to news article at https :// tass. ru/ekonomika/13943115 embedded)
Fucked. Double fucked. That’s Russia’s economy.
A wide swath of Russians have no idea how big and bad this fucking will be thanks to Putin’s suffocating grip on media which has only tightened in the last two weeks.
However early assessments tell us failures will begin in another week or two — airlines are a good example:
I work in the aviation sector, and I can tell you that for all intents and purposes Russian aviation has – at best – about three weeks before it’s show over.
One aspect is the fact that airspace available to Russian aircraft is very, very limited now. However, there is more:
— Jan Nedvidek (@janedvidek) March 1, 2022
.
BREAKING: Boeing is “suspending parts, maintenance and technical support services for Russian airlines.” The company will be suspending “major operations” at its Moscow offices, which do a significant amount of fleet support and design work.
— Jon Ostrower (@jonostrower) March 2, 2022
.
Amadeus IT Group and Sabre, two of the world’s biggest airline ticket-booking systems, are evaluating their exposure to Russia in the wake of sanctions on the country https://t.co/ywyKJfflAT
— Bloomberg (@business) March 2, 2022
.
Russian airlines now having their jets seized at international airports by the leasing companies, according to Meduza. S7 has canceled its international flights after having a jet seized in Armenia. Could end most Russian international flights if correct. https://t.co/eLswdCUBc0
— Andrew Roth (@Andrew__Roth) March 3, 2022
All this inside a couple of days. Other businesses will similarly experience problems with payments, acquiring other goods and services, disruptions in supply chain far worse than COVID created.
What happens when reality finally catches up with the average Russian who may already have experienced problems with banking and travel? What happens when pay for government employees is disrupted, when unemployment cascades out to successive failing businesses and industries?
~ ~ ~
Let’s go back to wheat futures. What Mironov wrote is challenging enough — from where will Russia buy the wheat seed needed? (Depending on source, there’s a disparity in what percentage of wheat seed Russia imports, but it’s between 18-40% depending on spring, hard wheat, or other type.) Will it buy from China and India, leaving Russia more vulnerable to influence of these two countries? Are these two countries willing to accept rubles? Or will they expect something else in trade, like fossil fuels?
That’s all well and good, but will this happen inside the next several weeks? Because the planting season can begin as early as April in the southernmost areas growing wheat.
With wheat futures rising so rapidly, will the price of wheat seed also reflect this increase? Will Russia be able to keep up with this considering their markets have crashed?
What happens to other crops like potatoes? Russia had already forecast a shortage this year because of drought last year which will now be exacerbated by sanctions.
Expand mental modeling across all of Russia’s crops — time is already eating away at the 2022 growing season even though there’s still snow cover.
(I’m not even going to explore the challenges of tractor and other farm equipment maintenance due to sanctions. The problems will mirror that of the Russian military.)
~ ~ ~
I wrote “world war of economic attrition” because the impending challenge to Russia’s wheat crop and wheat futures doesn’t stop at Russia’s border.
Ukraine, the fifth largest wheat producer, will likely have problems putting in its crop due to military action. If we assume Putin does his worst, we can expect farmers in tractors chased down by aircraft.
The countries which buy wheat from both Ukraine and Russia will suffer for any decrease in availability and increase in price — more so for those which import from Ukraine since it ships as much as 80% of its wheat. Two articles worth reading and in this order:
Reuters: Concerns rise over Black Sea spring crops amid Russia-Ukraine war – March 1, 2022
Al Jazeera: MENA faces a crisis as the world’s key wheat producers are at war – March 1, 2022
Reuters looks at the wheat market, Al Jazeera looks at more closely at the consumption end. Neither paint a pretty picture; the drought in parts of north Africa add substantial risk of increased geopolitical instability which would likely spread through the Middle East.
Nor will the risks stop in the eastern hemisphere. Brazil imports wheat because it can’t grow enough for its own consumption. It dedicated more land to soybean production after Trump’s misbegotten trade war with China cut substantially into US soybean sales to the same. Brazil might try to increase more acreage to wheat but any more new Brazilian acreage comes at the expense of climate which we will all feel. How will the change in wheat futures affect Brazil politically when it’s sure to result in inflation?
~ ~ ~
Game out the simulation even further: how will sanctions affect the rest of Russia, and why should Putin’s leadership of Russia survive even another quarter? We may worry about Ukraine’s ability to bear up under a kinetic war of attrition, but how long will Russians suffer under the corresponding economic war of attrition?
Why should the rest of the world have to suffer the ensuing fallout and forbear Putin’s inability to sell Ukrainians on the idea they are part of Russia without the use of force?
The sanctions imposed on Russia because of his personal beliefs about Ukraine are the equivalent of a economic nuclear weapon, the fallout from which will reach the rest of the world.
It needs to be clear to every global citizen touched this fallout the sole reason any sanctions have been levied is Putin and his screwed-up genocidal beliefs that Ukraine is not a country, that only Ukrainians he accepts as good Russians should survive.
Fucked. Double fucked. This may be Russia’s economy in the very near term and the world’s bread basket over the course of the the next year, but this should be Putin’s epitaph.
Putin the Double Fucked.