Some weeks ago, I noted the language in James Clapper’s letter purportedly “supporting” Patrick Leahy’s USA Freedom Act making it clear he intended to retain the information asymmetry that currently exists in the FISA Court — specifically, ex parte communication with the court.
We note that, consistent with the President’s request, the bill estsablishes a process for the appointment of an amicus curiae to assist the FISA Court and FISA Court of Review in matters that present a novel or significant interpretation of the law. We believe that the appointment of an amicus in selected cases, as appropriate, need not interfere with important aspects of the FISA process, including the process of ex parte consultation between the Court and the government. We are also aware of the concerns that the Administrative Offices of the U.S. Courts expressed in a recent letter, and we look forward to working with you and your colleagues to address these concerns.
The Yahoo documents released a few weeks back illustrate how this might work in practice.
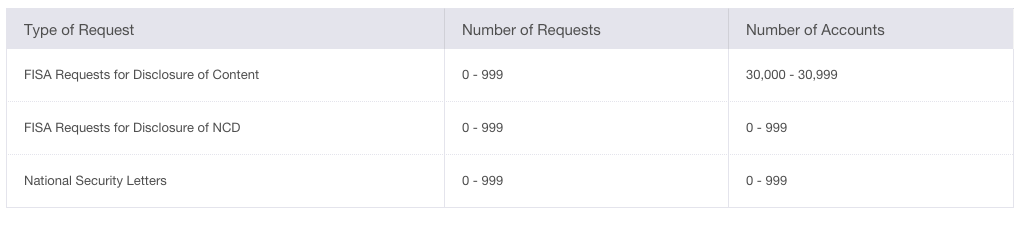
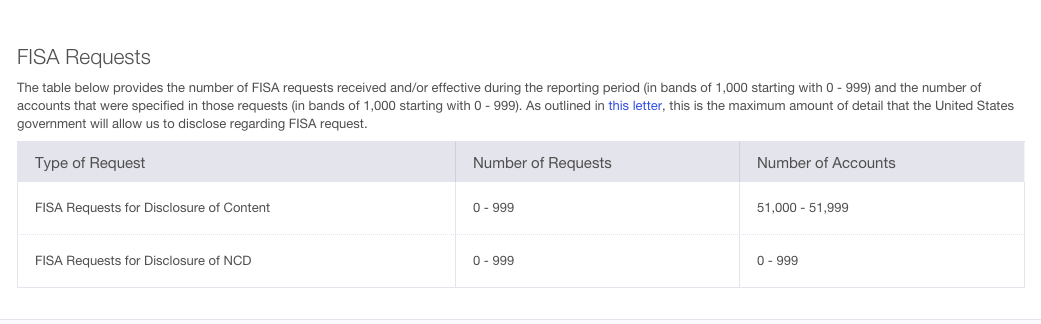
We’ve known since January 2009 that Yahoo (which we then only knew was an Internet company) didn’t receive the materials — perhaps most importantly, the minimization procedures — it needed to adequately challenge the program.
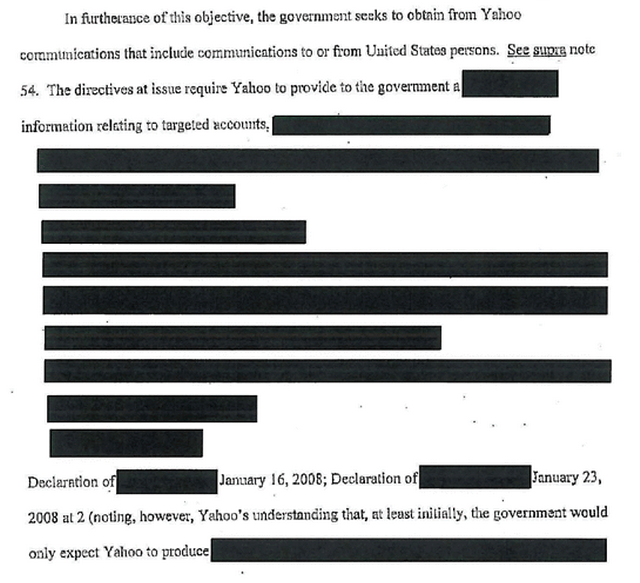
The cover sheet to the ex parte appendix provided to the FISCR illustrates the range of things withheld from Yahoo’s attorney, Marc Zwillinger, who apparently had a Top Secret clearance. In addition to the minimization procedures for NSA and FBI, the government withheld the “linking” procedures used to identify targets (the titles of these documents are redacted in the released version, but this post explains why at least some must pertain to these procedures; note, I think the government also withheld these from Judge Reggie Walton at the FISC level!), and a January 15, 2008 Colleen Kollar-Kotelly FISC opinion assessing the adequacy of the original certifications.
Comparing two versions of Walton’s April 25, 2008 opinions — a version redacted for Yahoo’s use in 2008, and the version redacted for public release now — provides context on the key issues obscured or suppressed entirely from Yahoo’s view. (Note two things about these redactions: first, with the exception of language on the information the government demanded from Yahoo, we’re receiving more information than Yahoo’s cleared attorney received when he was fighting this case. And the older document actually includes two sets of redactions: the more faded redactions used for Yahoo, and a more opaque set done for this release, the latter of which hide details about the Directives given to Yahoo.)
Effectively, the government hid what they changed when they rewrote Certifications underlying their demands to Yahoo just 2 weeks before the law expired. A significant part of those changes involves getting FBI involved in the process (I increasingly suspect those January 29, 2008 Certifications are when the government first obtained official permission for FBI back door searches).
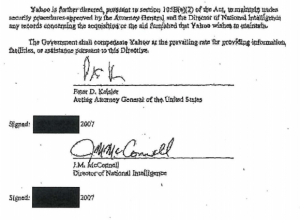
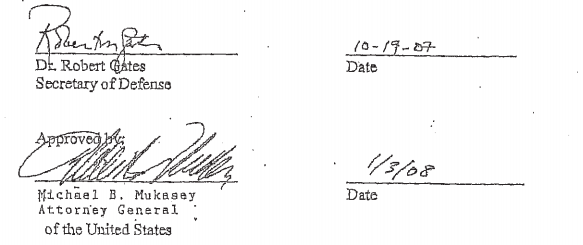
Notice of the new Certificates was given to Yahoo on February 16, 2008, the day PAA expired, and signed by then Solicitor General Paul Clement, though signed as Acting Attorney General (see page 81). One day earlier, Judge Walton had given the government an ex parte order requiring them to address whether the ex parte materials they had submitted to him in December “constitutes the complete and up-to-date set of certifications … applicable to the directives that are at issue in this proceeding.” Walton also required the government to provide notice to Yahoo they were going to submit a new classified appendix.
Apparently, Walton had gotten wind of the fact — but had not been told formally — that the government had submitted entirely new Certifications affecting their treatment of the data they would obtain from Yahoo. So he ordered them to update the record so his review actually considered the surveillance as it would be implemented.
I’ve listed most of the differences between the two memoranda below. While much of it pertains to prior classified decisions and the operation of FISC generally, the biggest sections redacted from Yahoo but released in part to us now describe the new certifications, including FBI’s new role in the process. Of particular concern, the government withheld Walton’s comment admonishing the government for changing the certifications, “without appropriately informing the Court or supplementing the record in this matter until ordered to do so” (page 4), though footnote 4 and page 35 make it clear that Walton revealed some details of the government’s belated disclosures in a February 29 order for more briefing.
More troubling still, they hid Walton’s still significantly-redacted assessment that the changes in the Certifications would not change the nature of the government’s demand from Yahoo (page 38).
Neither type of amendment altered the nature of the assistance to be rendered by Yahoo,40
40 Yahoo has submitted a sworn statement that, prior to serving the directives on Yahoo, representatives of the government “indicated that, at the outset, it only would expect…
I wrote about these changing requests here. And while on paper the changing requests couldn’t have been a result of the changed Certification — Yahoo’s Manager of Legal Compliance described them in a January 23 submission, and the new Certifications were issued the following week — I find the timing, and the government’s failure to notice Walton on them, suspect enough that it’s the kind of thing that should have been briefed. Plus, as I’ll show in a follow-up post, I’m fairly certain the government hid from both FISC and FISCR the degree to which this was about targeting Americans.
Once Walton learned that the government’s requests to Yahoo had changed between the date of Kollar-Kotelly’s initial approval and the expiration of the law, it seems it should have merited more direct briefing, but that would have required admitting that the changes put domestic law enforcement in the center of the program, which presents (or should present) significantly different Fourth Amendment concerns, notably increasing the importance of prior interpretations of the “significant purpose” language instituted under the PATRIOT Act.
In other words, not only did the ex parte nature of this proceeding hide the details Yahoo would have needed to make a robust Fourth Amendment argument, as well as evidence that the government was not being entirely forthcoming to FISC (which would have bolstered Yahoo’s separation of powers claim), it also hid what may be specifically pertinent details behind the government’s last minute changed certifications.
In theory, this shouldn’t happen with the USA Freedom Advocate, because the bill specifically requires the Advocate have access to certifications necessary for her to complete her duties.
(A) IN GENERAL.—If a court established under subsection (a) or (b) designates a special advocate to participate as an amicus curiae in a proceeding, the special advocate—
[snip]
(ii) shall have access to all relevant legal precedent, and any application, certification, petition, motion, or such other materials as are relevant to the duties of the special advocate;
By comparison, the government was challenging Yahoo’s legal standing to take this challenge in the first place.
But I find the apparent basis for withholding information from Yahoo to be relevant. This memorandum, at least, was originally classified Top Secret/ORCON (Originator Controlled); the redacted memorandum given to Yahoo was classified Secret. That means that the changes arose, at least in part, from the ability of the originator (which may be DOJ’s National Security Division, given that Mark Bradley conducted the declassification review) to determine who gets the document. As I noted, there are two bases in USAF that would permit the government to withhold information, classification and privilege. Withholding information under an ORCON claim likely stems from both (though I am checking this).
So while the government should not be able to treat the advocate the same way they treated Yahoo (which, after all, FISC treated as a Congressionally sanctioned challenger to the orders, just as it would the advocate), they seem to have the prerogative to. (Update: I should add that Walton permitted the government to do all the ex parte briefing here under FISA’s ex parte briefing language; given that USAF doesn’t change that for any of the authorities in question, we should assume this precedent will apply to the advocate.)
To be clear, the USAF advocate is not one of the things that I believe sets back a slow reform process (as, for example, I believe the “transparency” provisions and some weakened minimization procedures do). I think it most likely that the advocate will evolve the way PCLOB has, which was first authorized in 2004, thwarted by Executive obstruction (on precisely these kinds of issues), reauthorized as a more effective body in 2007, then slow-walked again — partly by President Obama, though partly by Congress — for another 6 years. That is, if the advocate is at least as self-respecting as Lanny Davis (!), she will quit if the Executive ignores the intent of Congress that she have access to the materials she needs to do her job, exposing the inefficacy of the existing system. All that, of course, assumes she will cop onto what has been withheld. Clearly, Yahoo got a sense of it during this process, though FISC and FISCR seem to have realized only some of the other stuff withheld from them.
That is, judging by the PCLOB example, if all goes well and if USAF were to pass this year, we might have a fully functional advocate by 2023!
The Yahoo materials released show that the government withheld pertinent information from Yahoo, FISC, and FISCR until forced to provide it, and they never provided any of them with all the information they should have.
That it retains the ability to do so under USAF doesn’t bode well for the advocate. But that’s really just a subset to a larger issue that, even when authorized by Congress to provide oversight of this executive spying, the government has consistently, for years, been less than fully cooperative with FISC’s authority to do so.
As I’ve said, the surest way to reform surveillance is to eliminate the FISA Court.
Read more →