CNET is getting a lot of attention for its report that NSA, “has acknowledged in a new classified briefing that it does not need court authorization to listen to domestic phone calls.”
In general, I’m just going to outsource my analysis of what the exchange means to Julian Sanchez (I hope he doesn’t charge me as much as Mike McConnell’s Booz Allen Hamilton for outsourced analysis).
What seems more likely is that Nadler is saying analysts sifting through metadata have the discretion to determine (on the basis of what they’re seeing in the metadata) that a particular phone number or e-mail account satisfies the conditions of one of the broad authorizations for electronic surveillance under §702 of the FISA Amendments Act.
[snip]
The analyst must believe that one end of the communication is outside the United States, and flag that account or phone line for collection. Note that even if the real target is the domestic phone number, an analyst working from the metadatabase wouldn’t have a name, just a number. That means there’s no “particular, known US person,” which ensures that the §702 ban on “reverse targeting” is, pretty much by definition, not violated.
None of that would be too surprising in principle: That’s the whole point of §702!
That is, what Nadler may have learned that the same analysts who have access to the phone metadata may also have authority to issue directives to companies for phone content collection. If so, it would be entirely feasible for the same analyst to learn, via the metadata database, that a suspect phone number is in contact with the US and for her to submit a request for actual content to the providers, without having to first get a FISA order covering the US person callers directly. Since she was still “targeting” the original overseas phone number, she would be able to get the US person content without a specific order.
 I just want to point to a part of this exchange that everyone is ignoring (but that I pointed out while live tweeting this).
I just want to point to a part of this exchange that everyone is ignoring (but that I pointed out while live tweeting this).
Mueller: I’m not certain it’s the same–I’m not certain it’s an answer to the same question.
Mueller didn’t deny the NSA can get access to US person phone content without a warrant. He just suggested that Nadler might be conflating two different programs or questions.
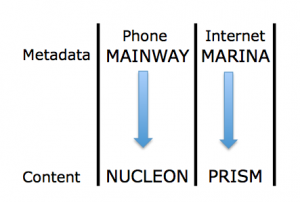
And that’s one of the things to remember about this discussion. Among many other methods of shielding parts of the programs, the government is thus far discussing primarily the two programs identified by the Guardian: the phone metadata collection (which the WaPo reports is called MAINWAY) and the Internet content access (PRISM).
Thus, we are effectively just talking about two programs, and not two that intersect via targeted technology, as MAINWAY would with NUCLEON and MARINA with PRISM. So, while there are a slew of other possibilities for what Mueller might mean by “another question,” one big one is “how may an analyst access NUCLEON information if she had MAINWAY data”?
And, as Sanchez notes in his piece, the way 702 is supposed to work (and indeed, would have to work for the claims made about PRISM’s role in thwarting the Najibullah Zazi attack to be remotely true) is that US person information comes up along with targeted foreign targets. Indeed, as I noted last year during the FISA Amendments Act debate, in an effort to defeat this amendment prohibiting effectively what Sanchez has laid out, Sheldon Whitehouse said that getting US content without a warrant was the entire point.
He referred back to his time using warrants as a US Attorney, and said that requiring a warrant to access the US person communication would “kill this program,” and that to think warrants “fundamentally misapprehends the way in which this program operates.”
The possibility that the government would do this kind of thing has been raised repeatedly since Russ Feingold did so in 2009 during the FISA Amendments Act debates, speaking specifically about the content of calls to people overseas.
It may be that, discussed in isolation, the government can avoid talking about what Feingold and Wyden and others have called a backdoor. Which is probably why they don’t want us to “confuse” (that is, understand the relationship between) the business records and content access.