US Indicts Chinese Hackers for Stealing Information on Trade Negotiations
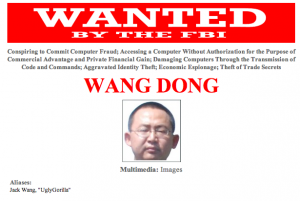 DOJ just announced the indictment of 5 Chinese People’s Liberation Army hackers (complete with Most Wanted posters) for breaking into a bunch of companies — and the United Steel Workers — in Pittsburgh.
DOJ just announced the indictment of 5 Chinese People’s Liberation Army hackers (complete with Most Wanted posters) for breaking into a bunch of companies — and the United Steel Workers — in Pittsburgh.
I’ll have more to say about the indictment later, but for now there are two parts of it I find to be particularly interesting.
The indictment was brought by the US Attorney for Western PA, David Hickton, not EDVA (the Defense Industry) or SDNY (Wall Street) where the US complains more loudly about hacking. The victims include Pittsburgh’s most important companies — US Steel, Westinghouse, and Alcoa. After watching the presser, I would be shocked if Hickton is not planning on running for higher office in Western PA.
But there’s another detail about Western PA that may be of interest. In addition to these blue chip industrial companies, Pittsburgh is also home to Carnegie Mellon’s CERT, a public-private venture on fighting cyberthreats. That is, I suspect this indictment came out of Pittsburgh because it has the facilities to investigate such crimes.
But the other interesting aspect of this indictment coming out of Pittsburgh is that — at least judging from the charged crimes — there is far less of the straight out IP theft we always complain about with China.
In fact, much of the charged activity involves stealing information about trade disputes — the same thing NSA engages in all the time. Here are the charged crimes committed against US Steel and the United Steelworkers, for example.
In 2010, U.S. Steel was participating in trade cases with Chinese steel companies, including one particular state-owned enterprise (SOE-2). Shortly before the scheduled release of a preliminary determination in one such litigation, Sun sent spearphishing e-mails to U.S. Steel employees, some of whom were in a division associated with the litigation. Some of these e-mails resulted in the installation of malware on U.S. Steel computers. Three days later, Wang stole hostnames and descriptions of U.S. Steel computers (including those that controlled physical access to company facilities and mobile device access to company networks). Wang thereafter took steps to identify and exploit vulnerable servers on that list.
[snip]
In 2012, USW was involved in public disputes over Chinese trade practices in at least two industries. At or about the time USW issued public statements regarding those trade disputes and related legislative proposals, Wen stole e-mails from senior USW employees containing sensitive, non-public, and deliberative information about USW strategies, including strategies related to pending trade disputes. USW’s computers continued to beacon to the conspiracy’s infrastructure until at least early 2013.
This is solidly within the ambit of what NSA does in other countries. (Recall, for example, how we partnered with the Australians to obtain information to help us in a clove cigarette trade dispute.)
I in no way mean to minimize the impact of this spying on USS and USW. I also suspect they were targeted because the two organizations partner together on an increasingly successful manufacturing organization. Which would still constitute a fair spying target, but also one against which China has acute interests.
But that still doesn’t make it different from what the US does when it engages in spearphishing — or worse — to steal information to help us in trade negotiations or disputes.
We’ve just criminalized something the NSA does all the time.
Update: Adding, one other reason they’re probably bringing this indictment with industrials as victims is because their information is not as sensitive as Defense Contractor or Wall Street victims is.
Update: These guys are named in Mandiant’s most recent report on China’s hacking. So that’s a lot of what they used for the indictment, presumably. But they indicted with companies that aren’t as sensitive as some of Mandiant’s other clients.
Update: Correction: only Wang Dong was on Mandiant’s list, meaning 2 of their ID’ed people were not indicted.

hubris, to be sure,
but also the application of the maxim that the best defense is a good offense – avoiding domestic criticism of nsa spying by defending our interests against the electronic spying depredations of the golden hoard.
question: how does one correctly identify a member of the pla (chi version) by name and photo in preparation for an indictment? look! over there!
question: are we getting back in the groove – captain obama, protector of our nation – just in time for 11/14?
“When the NSA does it … that means that it is not illegal.”
.
Impeach the guys these goons work for. Kill the NSA.
.
Forgive me for being childish, but the hacker’s name made me immediately think of the “names” of the pilots of Asiana 214. Reminder: http://www.youtube.com/watch?v=k-GEhArUuZ8
mandiant company report:
http://intelreport.mandiant.com/
the federal government can indict on the basis of a private company’s information gathering?
if yhou want some fun reading, gho to the mandiant report cited above, then download the pdf reporting on chinese hacking.
then go to pp. 51 ff and enjoy reading about “ugly gorilla” and two other chinese hackers.
you read it here first, but twice is better than once.
http://america.aljazeera.com/opinions/2014/3/cybersecurity-nsaalexandersnowden.html
NSA cries “Thief! Thief!
Pot. Black. Kettle. How did we end up this way?
https://www.youtube.com/watch?v=YMJ2VDTQWSI
Amendment IV The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall NOT be violated, and no Warrants shall issue, but upon probable cause, supported by Oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.
Is that sooooooo hard to understand, dear NSA?
What part of “NOT” don’t you understand?
Heck, it’s not even in code!
http://www.democracynow.org/2014/5/13/collect_it_all_glenn_greenwald_on
http://www.pbs.org/wgbh/pages/frontline/united-states-of-secrets/
A little known, seldom sung stanza of America the beautiful:
America! America! God mend thine every flaw,
Confirm thy soul in self-control, Thy liberty in law!
great comment.
tx