On Same Day Alexander Tells BlackHat, “Their Intent Is to Find the Terrorist That Walks Among Us,” We See NSA Considers Encryption Evidence of Terrorism
Thirty minutes into his speech at BlackHat yesterday, Keith Alexander said,
Remember: their intent is not to go after our communications. Their intent is to find the terrorist walks among us.
He said that to a room full of computer security experts, the group of Americans probably most likely to encrypt their communications, even hiding their location data.
At about the same time Alexander made that claim, the Guardian posted the full slide deck from the XKeyscore program it reported yesterday.
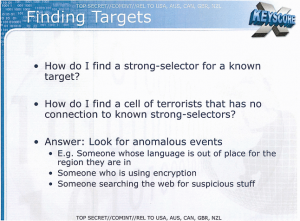
How do I find a cell of terrorists that has no connection to known strong-selectors?
Answer: Look for anomalous events
Among other things, the slide considers this an anomalous event indicating a potential cell of terrorists:
- Someone who is using encryption
Meanwhile, note something else about Alexander’s speech.
13:42 into his speech, Alexander admits the Section 702 collection (this is true of XKeyscore too — but not the Section 215 dragnet, except in its use on Iran) also supports counter-proliferation and cybersecurity.
That is the sole mention in the entire speech of anything besides terrorism. The rest of it focused exclusively on terror terror terror.
Except, of course, yesterday it became clear that the NSA considers encryption evidence of terrorism.
Increasingly, this infrastructure is focused intensively on cybersecurity, not terrorism. That’s logical; after all, that’s where the US is under increasing attack (in part in retaliation for attacks we’ve launched on others). But it’s high time the government stopped screaming terrorism to justify programs that increasing serve a cybersecurity purpose. Especially when addressing a convention full of computer security experts.
But maybe Alexander implicitly admits that. At 47:12, Alexander explains that the government needs to keep all this classified because (as he points into his audience),
Sitting among you are people who mean us harm.
(Note after 52:00 a heckler notes the government might consider BlackHat organizer Trey Ford a terrorist, which Alexander brushes off with a joke.)
It’s at that level, where the government considers legal hacker behavior evidence of terrorism, that all reassurances start to break down.
Update: fixed XKeystroke for XKeyscore–thanks to Myndrage. Also, Marc Ambinder reported on it in his book.
Update: NSA has now posted its transcript of Alexander’s speech. It is 12 pages long; in that he mentioned “terror” 27 times. He mentions “cyber” just once.

Encryption is a legitimate issue. It can, and to some extent will, be used to hide bad intent. But it is a big leap to make all encryption a selector for terrorism.
NSA has struggled with encryption for decades, and the policy of treating all encryption as hostile is consistent with their history. When they were focused on foreign communications that was not a constitutional issue. That changed when their mission turned inward after 911.
The idea that any communication NSA cannot view is a selector for terrorism is broader than encryption. As long as that is the mind set, collection will continue to increase. The 4th Amendment will remain dead. From his recent defense of the practices, it is clear that is how BO views it.
@Lefty665: Encryption is the bread-and-butter of everyone at Black Hat. These are the security industry folks, who spend large amounts of time and money developing better and better encryption and security measures, to protect corporate secrets and protect the products and services these folks deliver.
From an NPR piece reported before Alexander’s speech:
And the solutions — which will center around better encryption — will be evidence of terrorist intent?
*facepalm*
I’d love to hear Alexander make his next speech on this topic to the Chamber of Commerce types, who spend non-trivial amounts on money on encryption to prevent corporate espionage.
Doesn’t freedom by its very nature consist of “anomalous events”?
Interesting that “use of encryption” would be designated indicative of Terrorism. Certainly not inconsistent with the philosophy of “if you aren’t doing anything wrong you have nothing to fear,” I guess, but it’s certainly a stretch to suggest that if you are encrypting you’re likely doing something wrong and that this justifies law enforcement singling you out for capture and review of your communications.
Any empirical Terra-finding confirmations? How about the series of numbnuts the FBI and CIA have been ferreting out, inducing and then arresting as “would be Terraists”– have any of those people “with Terra inclinations” been identified and targeted because they were encrypting communications? Even one? Sure, once you have a haystack it cries out to be searched for needles — but it’s more than a little bit unsettling to argue that there’s a basis for targeting people for criminal investigation because they might be utilizing available technology for the same reason the government or industry uses it: to be secure in communications. Who is the “enemy”, again?
CNBC got an interesting walk-and-talk hallway interview with Alexander right after his speech.
Would love Marcy’s thoughts on it.
I always knew those Wall Street types were terrorists. I assume their communications are among some of the most heavily encrypted, so by this logic they therefore are among the most dedicated to terror.
Arrest them all, throw them in Gitmo and let God sort them out.
Or something like that…
@Jim White: I think what these folks are really trying to get across and they just don’t know how to because of their resistance to dropping into a tone of gut-wrenching earnestness is that in this post-transparency age, that the very true definition of government is “encryption monopoly.”
@Peterr: NSA’s involvement in private (corporate as opposed to USG) encryption goes back at least to the Data Encryption Standard (DES) proposed by the National Bureau of Standards in the mid 70’s. Despite their assertions that DES was secure, NSA was able to read it. How hard they have to work to break commercial encryption has been an issue ever since.
If the standard now is that anything NSA cannot access is a selector for terrorism, it is profound.
Sort-of-OT: Holder is praising Mueller as ‘setting the standard’ for FBI directors.
That’s kind of a low bar, isn’t it?
@Lefty665:
When I took a cryptography class in college, around 1983, the assumption was that if NSA liked a standard, they had a way to defeat it, possibly back-door. (We weren’t nearly so paranoid, 30 years ago, as we are now.)
The name of the program is XKEYSCORE not XKEYSTROKE (unless you were trying to be cute). Slides from an XKEYSCORE presentation (likely this one) were displayed by Brazilian media two weeks ago. It included a slide that is probably the fully redacted one the Guardian published that showed an SSO in Columbia:
SILVER ZEPHYR
US 3273
Network access point through US partner STEELKNIGHT. Operates under transit authority
DNR – Metadata, voice, fax
DNI – content and metadata
So the Guardian didn’t break the existence of the program however they did provide more of the slide deck and thus more details than the Brazilian media were given.
As the NSA/GCHQ revelations reveal, the US wants access to every phone/internet user, anywhere, all the time. Encryption, especially if the boys can’t easily break it, signals that someone is not with the program, ought to be hired, or ought to be dealt with with prejudice.
@P J Evans: Doesn’t seem much has changed, except for the paranoia, does it?
@P J Evans:
Indeed. And the unspoken implication in that slide (“Someone who uses encryption”)is not only that they will focus on that person, but can break the encryption.
The classic example is the Swiss company Crypto AG:
https://www.schneier.com/blog/archives/2008/01/nsa_backdoors_i.html
https://en.wikipedia.org/wiki/Crypto_AG
@Mindrayge:
XKEYSCORE is a software interface to make it easier to access various databases, it’s not the name of an intelligence program. XKEYSCORE is a tool used in other intelligence programs and the existence of this tool has been known for a while.
SAIC and Raytheon have active job openings for engineers who know this software.
http://www.simplyhired.com/a/jobs/list/q-xkeyscore+engineer/l-columbia,+md
Marc Ambinder wrote about it in his book and again yesterday
http://theweek.com/article/index/247684/whats-xkeyscore
Its not a mistake. They really do consider everyone at BlackHat a terrorist. As Greenwald and others have noted, “terrorist” has taken on new meaning. To the NSA, a terrorist is anyone they don’t have absolute control over. It doesn’t matter if they are blowing stuff up or “spreading subversive ideas.” That’s why Alexander blew it off as a joke. The truth is terrifying. They aren’t really looking for people who’re search for pressure cookers. That’s just the excuse they give. They are building a profile of everyone who is or might ever be resistant to control and a stack of material to keep them in line. Hackers, academics, socialists. Every totalitarian regime goes after the same groups of people first.
Notice how the DOJ now says it must notify defendants if evidence against them came from the NSA. This is just to get more stories out about how this is all for our own good and minimize all the abuse. They pretend its for transparency, but its really information control.
@Mindrayge: thanks for the correction on spelling.
Alexander and the NSA are terrorists
Keith Alexander is working for al-Qaeda. There is no other reasonable explanation of his lying to Congress, violating court orders, violating the Constitution, and arranging to spy on Americans.
It’s “giving aid and comfort to the enemy”.