Ron Wyden’s Complaints about Section 702
In this post, I reviewed the Intelligence Community’s dubious history of refusing to count how many Americans get swept up under FISA Section 702. Of particular note, I showed that when Wyden first asked for a number of how many Americans were sucked up, the NSA was in the process of conducting a partial count (on how many Americans were caught up in one kind of upstream collection); yet the government neither told Wyden that count was going on or answered his question. Even the limited count NSA conducted resulted in a FISC ruling that the US person collection violated the Constitution.
I wanted to turn, now, to the litany of concerns about Section 702 Ron Wyden laid out earlier this week.
Ultimately, Wyden’s biggest concern is about reverse targeting.
But before he gets there, he lays out a number of ways Americans can be sucked in, some of which are familiar, some of which are less so.
Upstream collection
For example, he lays out MCTs (when a completely unrelated communication is sucked in with a targeted one) and SCTs (when an about communication picks up an entirely domestic communication). About this, Wyden notes no foreigners need to be involved.
The law only requires that one of the parties to the communication who again could be another American is overseas and even that requirement is hard for the government to meet in practice. So the implications here ought to be pretty obvious. You don’t even have to be communicating with one of the government’s targets to be swept up in Foreign Intelligence Surveillance Act collection. You don’t even have to be communicating with a foreigner.
Note, especially, his point that the requirement that one communication be overseas “is hard for the government to meet in practice.”
Tasking errors
Wyden describes accidental targeting — which (given my review of all available reporting, at least) is very closely policed.
The first are targeting mistakes in which contrary to the law, the target turns out to be an American or someone in the United States. The full impact of these mistakes on law-abiding Americans is not readily apparent. The most recent public report on section 702 noted that there were compliance incidents involving surveillance of foreigners in the United States and surveillance of Americans.
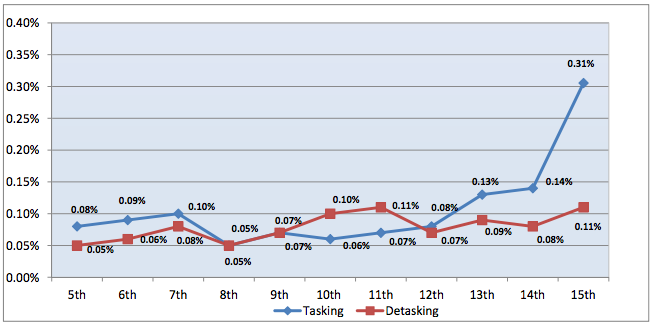
Tasking problems are closely policed, but as Wyden notes, the most recent report showed a number of tasking problems, representing a big spike in the number of such compliance problems.
My working hypothesis is that the increase in identified tasking problems stems from the implementation of additional documentation in response to the PCLOB report. Most of this spike is related to one office completely misapplying a certificate (which makes me wonder if there’s a new, possibly fourth, certificate). But there were also tasking errors. The unredacted section actually says none of these affected US persons and people in the US, but there are three paragraphs redacted that may describe older tasking problems.
One foreigner list-servs
Wyden also notes that it only takes one person on an email to grant the entire email foreignness designation.
It is also important to note that the government is prohibited from collecting communications only when the sender of an e-mail and everyone receiving that e-mail are in the United States. So an American in the United States can send an e-mail to another American in the United States, but if the e-mail also goes to an overseas target, it’s going to be collected. So that then brings us to the different kinds of collection under section 702 and how it affects the liberties of our people in different ways.
Imagine a group of people — say hackers — collaborating on some IRC channel where one known participant was foreign. That would meet the foreignness designation and lead to the collection of everyone, American or not, participating.
American business people doing business overseas
Wyden also emphasizes that the definition of “foreign intelligence” is so broad that the target doesn’t have to be suspected of any wrongdoing.
The statute requires that the collection be conducted, quote, to acquire foreign intelligence information. As implemented the standard for targeting individuals under the program is that the government has reason to believe that these persons possess or are expected to receive or are likely to communicate foreign intelligence information. Obviously that is broad. It doesn’t even require that a target be suspected of wrongdoing.
And it’s in that context that he raises the possibility that an “American business leader” could easily be collected.
[T]hink about how easy it would be for an American business leader to be in contact with a broad set of potential targets of this program. Consider how easy it would be for Americans communicating with other Americans to forward the e-mails of these people. All of this could be collected by the government.
Of course, any business person could be collected in such a way (or scientists, which appears to be what has gotten a lot of Chinese-American scientists in trouble).
Reverse targeting
But as I said, Wyden seems most concerned about the standard for reverse targeting, which he raised as a newly urgent concern in 2013. According to the standard currently implemented, reverse targeting is extremely rare — perhaps just three instances, with the most recent occurring in the December 2014 to May 2015 period.
One of NSA’s tasking errors involved the tasking of a facility that was used by a nonUnited States person located outside the United States that was determined to involve reverse targeting.
[snip]
In this incident, the Attorney General authorized the targeting of the United States person pursuant to Section 705(b) of FISA. This reverse targeting incident resulted from an NSA analyst misunderstanding the reverse targeting prohibition and not because an NSA analyst intentionally attempted to violate Section 702 or NSA policy.
The American being targeted was overseas and got targeted, under Section 705(b) anyway. A completely redacted footnote excuses the analyst’s error.
But Wyden suggests that several other factors may lead to more reverse targeting than gets identified by the current standard of review. He suggests back door searches (which he notes Bush didn’t do, at least not for the first several years of PRISM, though I suspect it actually happened at FBI) make the problem worse.
This issue was concerning in 2008 when the Foreign Intelligence Surveillance Act amendments passed with a prohibition on reverse targeting, but that was before the Congress knew about the collection of e-mails that are only about a foreign target and that could be to and from Americans. That was before the Obama administration sought and obtained authority to conduct warrantless searches for communications to, from and about Americans out of section 702 PRISM collection.
[snip]
Before 2011, the FISA court prohibited, prohibited queries for U.S. persons. I’m going to repeat that: Under the Bush Administration and the first two years of the Obama Administration, it was not possible to conduct these back-door, warrantless searches of law-abiding Americans. Then the Obama Administration sought to change the rules and obtained authority to conduct them.
While he doesn’t provide much detail, he points to the expanded ability of those doing the back door searches (presumably, I’d imagine, those at CIA and FBI) to also nominate people for targeting.
Each of the agencies authorized to conduct these warrantless searches, the N.S.A., the F.B.I., the C.I.A., are also authorized to identify the overseas targets of section 702. The agencies that have developed an interest in Americans’ communications and are actually looking for these communications are the same agencies that are in a position to encourage ongoing collection of those communications by targeting the overseas party.
Such targeting still has to undergo NSA targeting review, meaning the actual target has to be overseas and have, according to NSA’s review team, foreign intelligence value unto himself. But it would be fairly easy for the FBI to target someone known to communicate prolifically with an American to be able to get the American’s side of the conversation. To make things worse, FBI has devolved its targeting to field offices, and I’m not convinced the reviews of field offices are as rigorous as they were at Headquarters. Not all field offices even get reviewed (though I assume the ones doing the most foreign targeting are), and the tracking on US persons caught up in all this has diminished with the devolution.
I share Wyden’s concerns — especially given NSA’s dodgy response to the Snowden documents released last year.
Given the volume of information the NSA and, derivatively, CIA and FBI, collect, it would be very easy to get away with reverse targeting, particularly the more you move targeting into the hands of people leading investigations, as has happened at FBI.
Wyden is not the only one concerned about this. Ted Lieu, fresh off the classified 702 briefing last week, seemed pretty concerned as well (as well as Rand Paul, though I’m not sure if Paul has had briefing on this). We won’t get the kind of granularity we need to understand how big of a problem this is.




LIST-SERVS
Mailing lists. Too numerous to list.
But if you subscribe to a mailing list,
odds are good you are sucked up.
The mailing list server can be anywhere.
But the participants are everywhere.
Consider a mailing list server running mailman
in the US. Only takes *one* subscriber from UK to allow NSA to ‘collect it all’.
Oh geeze.
Overseas spammers.
Boom, you are collected.
Does not even have to reach your inbox.
(you may not notice if went to junk folder)
Does not even have to reach your ISP email server. Just had to cross the border.
You are in the ‘collect it all’ FOLDER and you never knew it happened.
Great loophole. Bet Wyden has not thought of it.
Easily done by darkside/deepstate. You have an email. Once you use it, it is collected via dpi or bought from businesses you ‘do business with’.
That email is then sent to an overseas spammer, They send you a spam email.
Bingo, 702.
The ‘spammer’ is already in the system as a ‘strong selector’ under Upstream (PRISM)