
"Are You Still Talking about Jeffrey Epstein?"
More than perhaps any moment of his ten year career, Trump just lost his cool -- about a Jeffrey Epstein question -- because he is helpless to dictate the focus of attention.

Pam Bondi Admits She Must Fire Kash Patel and Dan Bongino
If the joint DOJ/FBI memo declaring there's no there there to the conspiracy theories Kash Patel and Dan Bongino fueled is true, then Pam Bondi must demand their resignation for discrediting the Bureau.

How Trump Plans to Dodge Accountability Again
Trump's policies have and will get people killed. Will we find a way to hold him accountable, this time?

Seeing Language as a Tool of Authoritarianism
When you speak on social media, are you saying or are you doing?

Three Things: Hope Within Us
This could be us, rowing together. Hope is your paddle.

No Kings Day Reflections from an American-Irish in the Home of Her Ancestors
On this No Kings Day, remember that America is a tapestry of from-ness that Kings failed to stamp out.

The Anti-Democracy Project Of John Roberts
John Roberts doesn't believe in our system of checks and balances.

POS BFB in da' House: Be Water, My Friend
The situation in the House is fluid. We should be, too — keep calling your representatives.
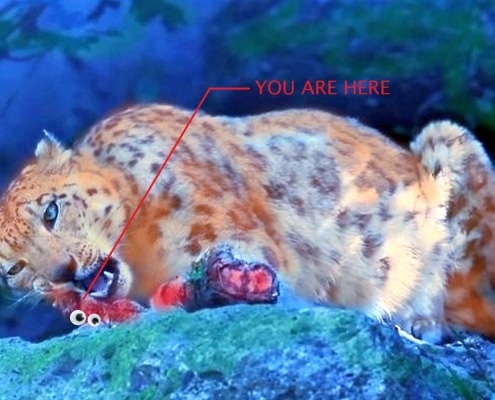
The Sound of Teeth on Bone: Leopard Eating Leopards [UPDATE]
Keep your hands and feet inside the cab, stay clear of the leopards as they begin to gnaw on their own.

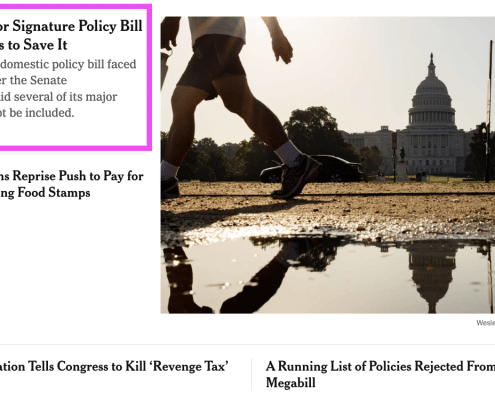
Making America Gross Again: Big Fugly Bill Hits the Senate Floor [UPDATE]
The Senate votes this morning on the Big Fugly Bill. Contact your senators and tell them not to vote for this POS BFB.
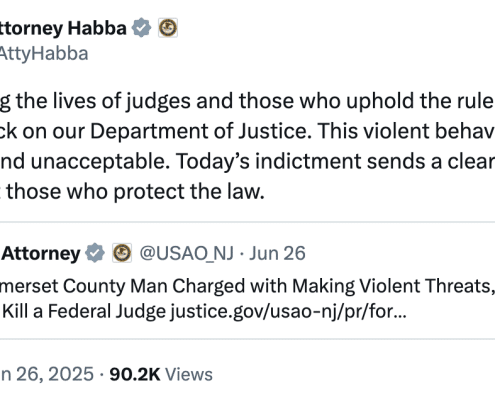
"Egregious Behavior:" Alina Habba Confesses She Must Prosecute Donald Trump
Alina Habba says that under her tenure, the New Jersey US Attorney's Office will prosecute threats against judges of the type her client and boss made and makes all the time.

Fridays with Nicole Sandler, Going, Going, Gone Fishing Edition
We talked a lot about the horrible Supreme Court decisions.

Open Thread: End of 2024-2025 Term, The Last Decisions
The Supreme Court's last batch of decisions for the 2024-2025 term will be issued this morning.
How the Newslettification of News Reifies Trump's Power Rather than Exposing His Lies
The NYT's newsletter structure turned Donald Trump, not Parliamentarian Elizabeth MacDonough, the primary actor in MacDonough's serial rulings throwing out many of the worst provisions of the Big Ugly reconciliation bill.
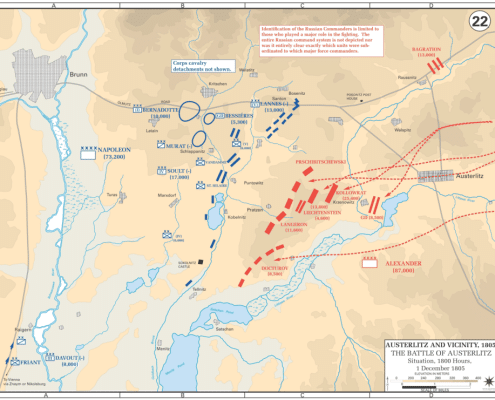
The Republican Hundred Year War On Democracy
The Republican attack on democracy has come out into the open under Trump, with major help from John Roberts
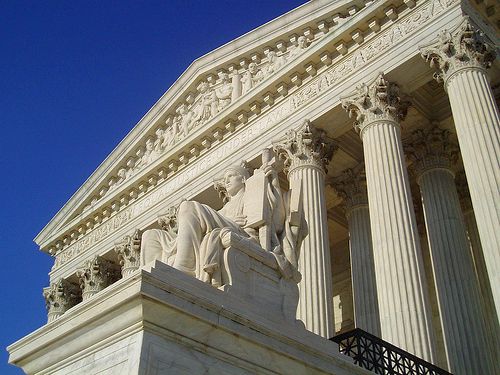
Open Thread: SCOTUS Decisions, End of Term Ahead
This is the last week of the 2024-2025 term for the Supreme Court. SCOTUS is expected to release multiple decisions at least twice this week; what follows is the first batch.

Judge Stringer Bell: Emil Bove Confirms Erez Reuveni's Allegation that He Tried to Avoid Paper Trails
While Emil Bove dodged a lot of questions in his short confirmation hearing, he confirmed one thing alleged by both Danielle Sassoon and Erez Reuveni: He doesn't like when his lawyers take notes on a criminal fucking conspiracy.

DOJ's Past Lies Continue to Backfire
DOJ has made its problems so much worse by refusing to do the right thing with Kilmar Abrego Garcia . And because they've charged him, that may actually finally backfire.

What We Talk About When We Talk About AI (Part Three)
Proteins, Factories, and Wicked Solutions
Part 3- But What is AI Good For?
(Go to Part Two)
There are many frames and metaphors to help us understand our AI age. But one comes up especially often, because it is useful, and perhaps even a…

John Thune's Flopsweat about Funding Stephen Miller's Gulag
John Thune has taken up Susie Wiles' marching orders to get the Big Ugly bill done by July 4. The time pressure may come from immigration pressures, not financial ones.
