The Black Budget
 The Washington Post just published an excellent package on the FY2013 Black Budget for intelligence. I’m reading through the summary now.
The Washington Post just published an excellent package on the FY2013 Black Budget for intelligence. I’m reading through the summary now.
I’ll put working comments below. But one of my first impressions is that all of this is useful information, and in some ways really encouraging information (in others, horrifying).
For that reason, this is one of my favorite parts of the story itself:
Lee Hamilton, an Indiana Democrat who was a former chairman of the House Intelligence Committee and co-chairman of the commission that investigated the Sept. 11 attacks, said that access to budget figures has the potential to enable an informed public debate on intelligence spending for the first time, much as Snowden’s disclosures of NSA surveillance programs brought attention to operations that had assembled data on nearly every U.S. citizen.
“Much of the work that the intelligence community does has a profound impact on the life of ordinary Americans, and they ought not to be excluded from the process,” he said.
“Nobody is arguing that we should be so transparent as to create dangers for the country,” he said. But, he said, “there is a mindset in the national security community — leave it to us, we can handle it, the American people have to trust us. They carry it to quite an extraordinary length so that they have resisted over a period of decades transparency. . . . The burden of persuasion as to keeping something secret should be on the intelligence community, the burden should not be on the American public.”
Hamilton is absolutely right. There’s no reason why information at this level of detail shouldn’t be shared with American taxpayers ponying up the $52.6 billion to pay for it all.
Working comments on Budget Justifications
4: The IC is apparently going to start researching trade disputes. I assume that’ll be primarily targeted at China. But it’s an interesting development.

Un.phoking.believable. This shit is starting to write itself.
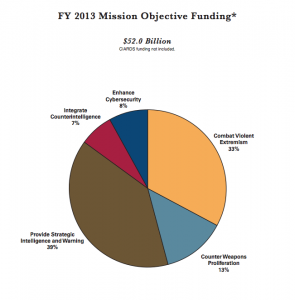
“The document describes a constellation of spy agencies that track millions of individual surveillance targets and carry out operations that include hundreds of lethal strikes. They are organized around five priorities: ”
1. Combating terrorism –
F: missed 9-11, & Boston.
2. Stopping the spread of nuclear and other unconventional weapons – F: Valerie Plame.
3. Warning U.S. leaders about critical events overseas –
D: Arab Spring, Benghazi, Libyan civil war, Pakistan, Taliban, crumbling Euro Enconomy.
4. Defending against foreign espionage – ? (see 1,2,3,5 how would we know?)
5. Conducting cyber operations –
F: Edward Snowden.
Total failure. Yet read another way says we’re losing because we’re not sending enough. A complete waste of taxpayer money, but not so for the mercenary PNAC, 5 Star, National Security 52 billion teat suckling Freedom Fighters. Mentioned this in some previous post that one of the most elaborate high-tec homes built in my little AmericanDreamParadise that would make many a high paid pro athlete salivate is a house with private cellars and courts with this and that state of the art expensive crap. The very private chalet of a cyber security company ceo. Gotta’ spend that money on something other than cadillacs and t-bones. So giving it to The Makers.
I call bullshit on the 52 billion number
The same people that didn’t see the collapse of the USSR coming after decades of the cold war.
The very private chalet of a cyber security company ceo
Tells you a little something about what’s required to feel safe when you know what’s really going on. I doubt Obama’s goal is to provide this level of “feel safe” to the citizenry, tho.
By way of comparison from the Washington Post article:
This despite the fact that the primary conclusion of the 9/11 commission was not that the U.S. lacked the data to make correct choices but that it wasn’t using the data it had properly being faced with so much noise. So what did we do in response to this? Double the budget and spend most of it on additional collection so that the noise is that much louder.
You really don’t want me to get started on the black budget…think financial overlords and mad scientists, including to our pee-on government.
The fact there is a black budget is a disgrace and shame to all Americans.
http://www.intelligence.senate.gov/pdfs/95274.pdf
1977 Senate committee report: “Whether Disclosure of Funds for the Intelligence Activities of the United Sates is in the Public Interest”
“In the late 1960’s William Richardson sued the United States to obtain an account of funds made available to the Central Intelligence Agency. He based his claim on article I, section 9, clause 7 of the Constitution which reads, ‘No Money shall be drawn from the Treasury but in Consequence of Appropriations made by Law; and a regular Statement and Account of the Receipts and Expenditures of all public Money shall be published from time to time.’
Mr. Richardson’s suit was dismissed. A later suit by Mr. Richardson seeking similar information was dismissed on the grounds that Mr. Richardson lacked standing to sue. The United States Court of Appeals for the Third Circuit, however, upheld his standing to sue; this decision was reversed by the United States Supreme Court in U.S. v.Richard8on, 418 U.S. 166, (1974).”
“At the committee’s request, the President asked the Attorney General to examine the constitutional issue and provide a legal opmion as to whether the Constitution requires public disclosure of funds authorized, appropriated, or expended for intelligence activities. By letter dated May 23, 1977 the President advised the committee as follows:
The Attorney General advises that the Constitution does not require public disclosure of the aggregate authorization or appropriation figure, nor does it require publication of an account of the expenditures of the intelligence agencies, individually or as a whole. However, Congress in its discretion can decide as a matter of policy to make public any of these figures.
Regrettably, the committee was not provided with any further basis for this conclusion.”
The President was Jimmy Carter, the Attorney General was Griffin Bell.
Richardson lost his earlier Supreme Court case by 5-4.
http://www.oyez.org/cases/1970-1979/1973/1973_72_885
@C: Yes. As both Shane Harris and I noted, not a lot of this is being spent on analysis.
I have no way of knowing, but I do wonder if we spent more on analysis, using more open source, whether we wouldn’t be a whole lot smarter.
On page 4 describing the investments in SIGINT, there is this statement:
“Also, we are investing in groundbreaking cryptanalytic capabilities to defeat adversarial cryptography and exploit internet traffic.”
It sounds like they believe they are making or have made some kind of cryptanalytic breakthrough. And note the explicit statement about exploiting internet traffic. I guess they believe keeping all encrypted communications is like holding the winning lottery ticket.
@omphaloscepsis: U.S v.Richardson was a 5-4 decision, 4 Nixon appointees plus “Whizzer” White (one of two dissenting on Roe). On the other side were 2 Eisenhower liberals, Thurgood Marshall, and William Douglas.
Douglas in dissent – “From the history of the clause it is apparent that the Framers inserted it in the Constitution to give the public knowledge of the way public funds are expended. No one has a greater ‘personal stake’ in policing this protective measure than a taxpayer. Indeed, if a taxpayer may not raise the question, who may do so? The Court states that discretion to release information is in the first instance ‘committed to the surveillance of Congress,’ and that the right of the citizenry to information under Art. I, § 9 cl. 7, cannot be enforced directly, but only through the (s)low cumbersome, and unresponsive’ electoral process. One has only to read constitutional history to realize that statement would shock Mason and Madison. Congress of course has discretion; but to say that it has the power to read the clause out of the Constitution when it comes to one or two or three agencies is astounding. That is the bare-bones issue in the present case. Does Art. I, § 9, cl. 7, of the Constitution permit Congress to withhold ‘a regular Statement and Account’ respecting any agency it chooses? Respecting all federal agencies? What purpose, what function is the clause to perform under the Court’s construction? The electoral process already permits the removal of legislators for any reason. Allowing their removal, at the polls for failure to comply with Art. I, § 9, cl. 7, effectively reduces that clause to a nullity, giving it no purpose at all.
The sovereign in this Nation is the people, not the bureaucracy. The statement of accounts of public expenditures goes to the heart of the problem of sovereignty. If taxpayers may not ask that rudimentary question, their sovereignty becomes an empty symbol and a secret bureaucracy is allowed to run our affairs.”
http://www.law.cornell.edu/supremecourt/text/418/166#writing-type-16-DOUGLAS
When Holder begs The Supremes wisdom, how far back will Scalia reach? How much will our Constitutional scholar president ignore?
Before the UK parliament vote on attacking Syria, the chances that Obama would ask Congress to vote on the US attacking Syria were slim and none.
After UK PM Cameron got spanked today, slim has been eliminated.
Hamilton’s reticence is part of the problem. What the national security apparatus has in fact been doing for decades is intentionally transgressing whatever legal boundaries (such as they are) are set, and then lying to Congress and the public when questions are asked. That behavior is driven by contempt for democracy and the lack of meaningful control, a combination that spells trouble for the republic. Why this collection of mendacious, weaselly punks continues to be seen as acting in good faith is the enduring mystery.
@Snoopdido: You sure? I’d think he would hate to find out afterwards he wasn’t supported by his own side, which is what Cameron has just discovered. I watched the debate and it was fascinating how much it was clearly influenced by pressure from ordinary folks who reckon their boys would get involved and get killed in due course.
That really is quite new here, and does arise from the fact that Tony Blair lied to us. But then I never have understood why in the USA people aren’t more upset about Cheney’s lies, which are the same ones, as that’s where Blair got them from.
Spend now. Establish legal basis later, if ever. Ensure policy is bipartisan, preventing either party from challenging de facto budget expansion, de facto mega increase in “intel” budget. Deal with dribs and drabs that make it to the public on an ad hoc basis.
@Chetnolian: Just my judgment, but I can’t see Team Obama risking the chance that Congress would turn him down (let’s call it pulling a Cameron) whether from cynical political motives or honest policy disagreement.
Like a lawyer asking questions of a witness in court that he/she doesn’t already know the answer to, I don’t think Team Obama wants to ask this question because the answer may surprise them.
Does this report include the budget to keep tabs on internal dissent? If so, which of the main 5 priorities does it fall under? Combating terrorism? Cyber-ops? Thanks.
Which MP’s voted against? Any Cons vote against, or just Lib-Dems?
Pity about that Congressional oversight. We had it once, but we haven’t seen much of it since the Church/Pike Committees in the mid-1970’s and the Iran/Contra hearings in the late-1980’s. Oh, except for a few years where GOP Congresscritters got their rocks off impeaching a Democratic president for having more sex than they were.
@Phil Perspective: As of now, we don’t know. But based on the debate my guess is that a number of right wing Tories were put off by Nick Clegg’s quite weak winding up and voted no out of sheer badness to punish Cameron for letting Clegg do it instead of Hague.
One item illustrates why the total spend might be so high (assuming these numbers are not underestimates).
The US Postal Service takes digital photos of the front and back of every piece of mail it handles. They also have the data itself – send to, send from, originating and destination PO’s, etc.
That’s about 160 billion pieces of mail every year. It suggests a considerable process: machinery, handling, techies, data collection, storage, retrieval, and analyzing, possibly even systems “management”.
No doubt, much of it is outsourced, under poorly written contracts yielding little oversight or cost control, and whopping charges. Once, begun, it’s the sort of program that would be enhanced but never ended. How many more of these “initiatives” are we paying for? How many have such a low utility-to-cost ratios? How much of the private sectors profits and bonuses are generated this way?
@earlofhuntingdon: Oh, this USPS expenditure is quite likely Not included in the “intel” budget. But it sure amounts to domestic and foreign intel gathering.
The CIA, not exclusively, hacks into “foreign computer networks”. Undoubtedly, those are not limited to foreign government networks, or even foreign govt. contractor-managed networks.
Executive branch agencies, most notably the Pentagon, are expert at manipulating the budget process. Among other tools, the purported purpose for which the money is desired will always pay homage to the threat(s) du jour, regardless of where the money actually goes.
I saw a reference to an increase in CIA personnel from about 17,000 to over 21,000. I saw no mention of the increased use of contractors. Given the profit-margin (and immunity grants from govt) required to justify high-risk ops, given the private sector gouging element – which expands like an inverse square relationship when oversight dwindles – contractors must be a big part of the CIA’s expanded budget.
To omphaloscepsis , reaguns did some legislation that allowed things to spiral. I can’t tell you exactly what it was, but I remember seeing it on the nightly news while my folks were still alive and thinking “Oh Shit, this can only turn out bad.”
Sorry to be nebulus , but I’ve been trying to find and remember what piece of legislation it was for quite a while now. It allowed a HUGE jump in the black budget.
Maybe it was a monetary policy thing.
@der:
very well said.
this a critical point justice douglas makes about citizens being informed.
with hidden info we get fox and cbsabcnbs news, which in turn leads to politicians, democrat and republican, who can and do lie thru their teeth while protecting unconstitutional and/or unnecessary, ineffective programs that drop hundreds of thousands into their re-election campaigns.
@emptywheel: Well we do use a fair amount of open source. Projects like HadOOP which is widely used at Google is, according to prior reporting, the basis for much of the NSA storage.
In general though I think this is a problem of ease. To quote one figure, whose name escapes me, “we are drowning in data and starving for knowledge”. In general we know how to collect info but figuring out what it “means” is really really hard and slow and these groups feel pressured to spot things in advance, or to clean up immediately afterwards.
@thump:
it’s only a tiny line item in the budget, but it has displayed enormous effectiveness in producing budvet increases and in guaranteeing “effective” oversight :))
put more baldly, blackmail works on presidents, congresscattle, and federal judges just like it works on those of us who are peons.
@orionATL:
oh, and another thing –
another 5 to 4 supreme court split – a sure sign, a signature actually, of an authoritarian/statist decision, “whizzer” of course would have been included himself in that distinguished crowd.
@earlofhuntingdon: somewhere I read that there are 83,000 analysts at Fort Meade. That’s a lot of pocket change.
@earlofhuntingdon: You think that’s expensive now, wait until they finish “bankrupting” the USPS and their government employees and double-decker-with-a-cherry-on-top outsource everything to FedEx or UPS. That will be a fun little slice of fascism…
@C:
Thanks for your question and comment. EW great post.
Your question seems to point to what has been addressed here since 2001…it’s not a bug, it’s a feature.