Glenn Greenwald Keeps Bitching about a Law Requiring Notice If You’re Funded by Russian Spies
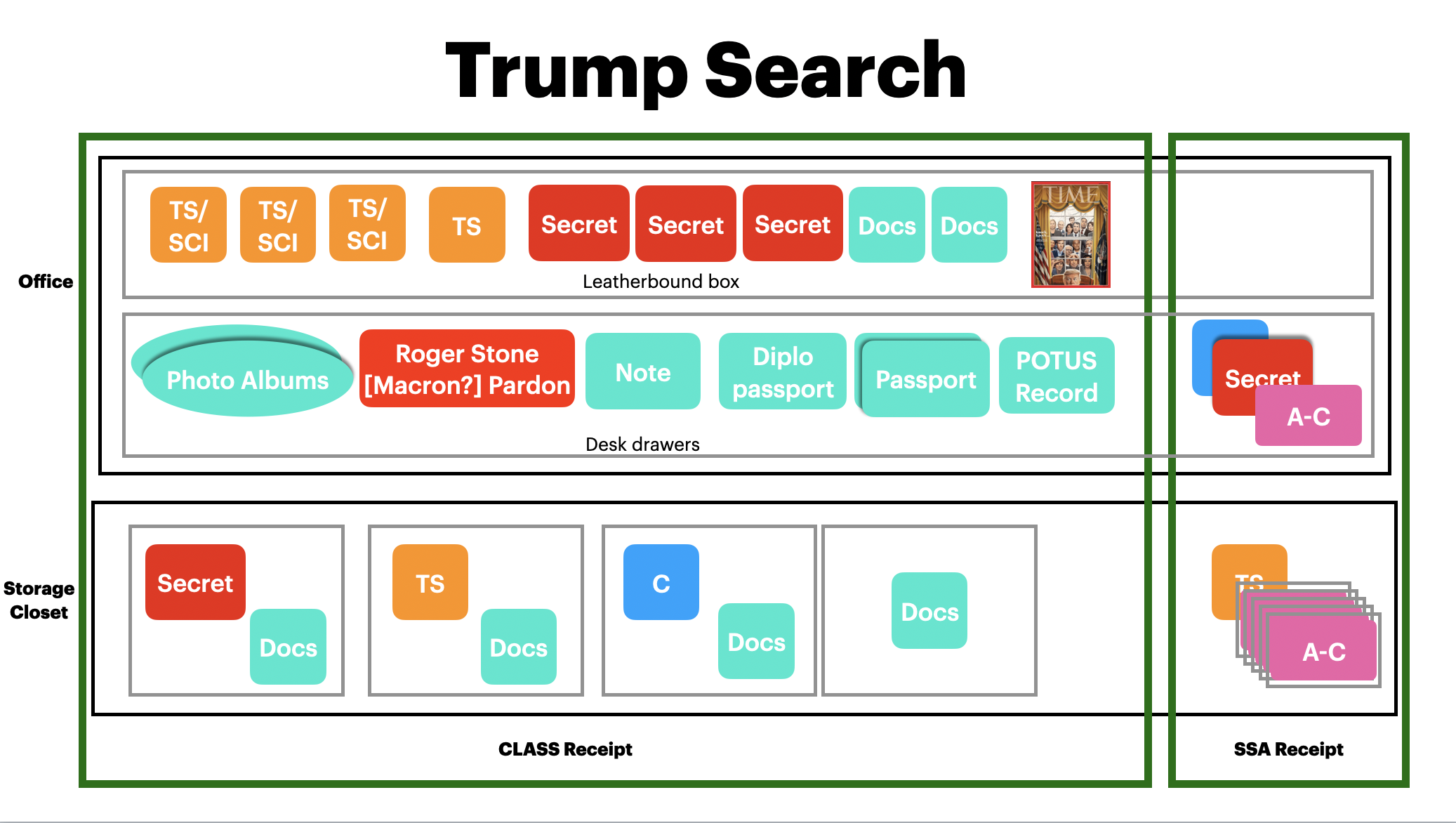
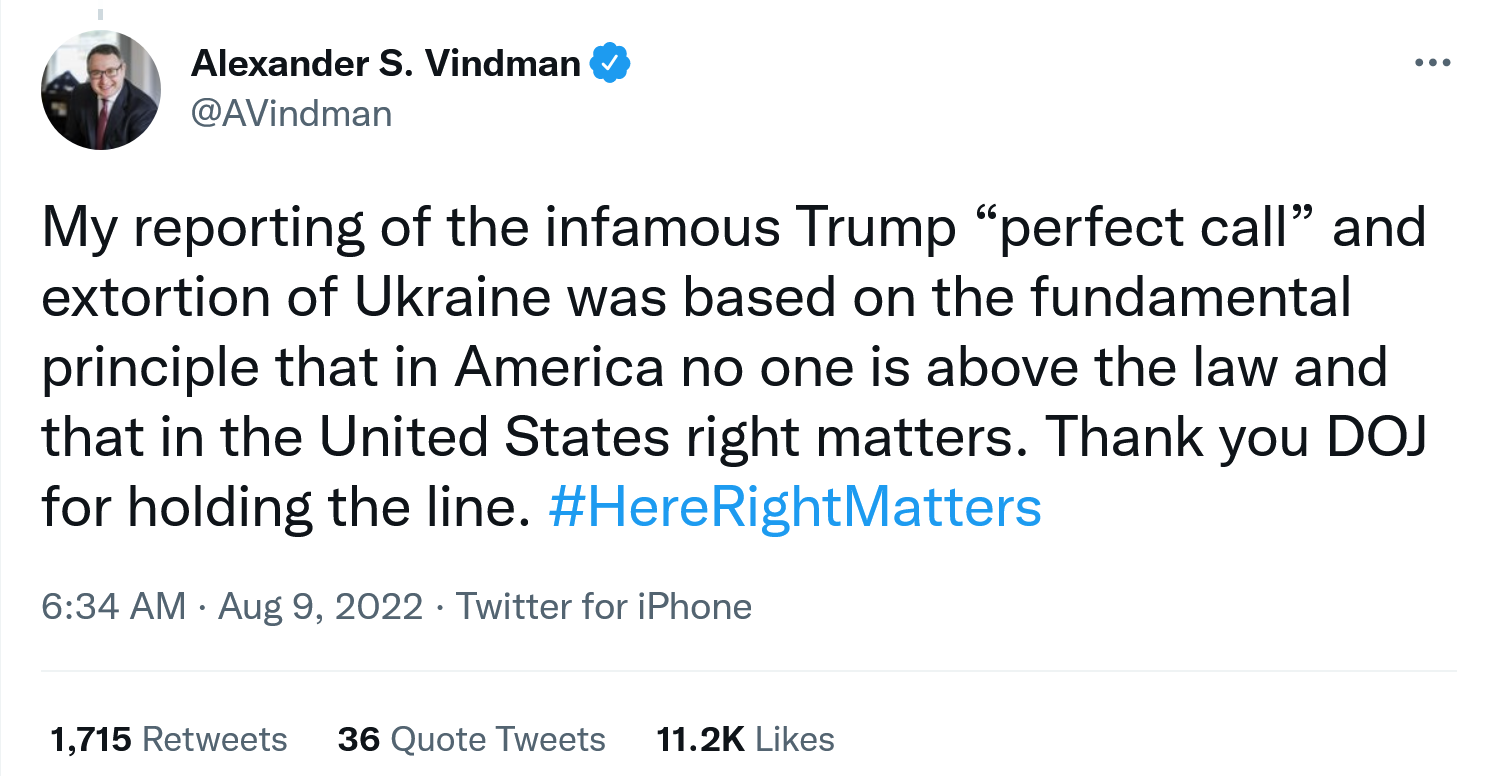
The other day, DOJ announced charges in two cases related to FSB efforts to recruit in the US and overseas. Neither set of allegations was entirely new. But what got added to the allegations is of some interest.
Certainly, the fact that American citizens got charged in a Florida case for not disclosing that their political activism was funded, in part, by the FSB, seems to be of interest to Glenn Greenwald. The charges, along with a few overt acts, and the names of two FSB colleagues are what got added to an earlier indictment against the FSB handler, Aleksandr Ionov, filed last July.
Glenn won’t shut up about those charges, making appearances on Glenn Beck and Tucker Carlson’s show so all of them could lie about why members of the African People’s Socialist Party were charged.
The members of the APSP weren’t charged because they disagree with Joe Biden. They weren’t charged because they oppose the war in Ukraine.
They were charged because after one, Omali Yeshiteli, went on an all-expenses paid trip to Russia in 2015, the group started getting funding and completing requests for their FSB handler, Aleksandr Ionov, who ran a front called the Anti-Globalization Movement of Russia. For example, shortly after the trip, Ionov wrote the group and asked them to start a petition against the genocide of the African people in the US so that AGMR could start using it as propaganda. And when Russia needed someone to legitimize the “Donetsk People’s Republic,” in 2020, Ionov contacted the Floridians to publicly do so. And when Russia wanted to protest Twitter’s restrictions on Russian disinformation after the Ukraine invasion, Ionov flew one of the Americans to San Francisco to make it happen.
Russia wanted to be able to point to a certain kind of dissidence in the US, so they paid money to help sustain it. And the Americans didn’t disclose that they knew they were working with agents of Russia.
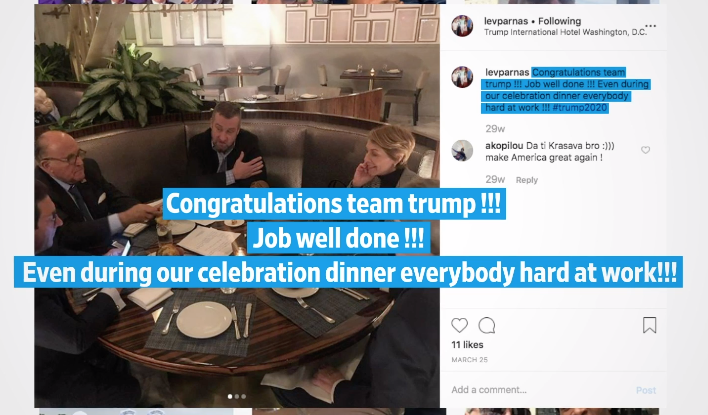
Glenn thinks only rich people like Tony Podesta should be held to foreign agent laws (Podesta wasn’t charged under a different law, FARA, for hiding his ties to a Ukrainian front group that Paul Manafort set up because he was paid by Manafort, and in any case, Glenn didn’t think much of Manafort’s charges for hiding the ties in real time). Glenn doesn’t think other people should have to disclose if they’re taking money — after they go on trips to Russia and start spouting Russian talking points non-stop from that point forward — from Russian spies.
It’s an interesting cause for Glenn and Tucker — who has his own curious tale about Russian ties — to champion.
Which brings us to the other case.
It charges Natalia Burlinova with attempting to do what Ionov succeeded in doing: getting Americans and others to unwittingly act as agents of Russia by recruiting them through her Russian government backed NGO, Creative Diplomacy, or PICREADI.
Burlinova was sanctioned — along with Ionov — last year, which suggests they may have a tie, perhaps the FSB officer they both report to.
Since she was already sanctioned, which would likely prevent her from traveling in any case, this complaint serves largely as a speaking document, which allows everyone she has had prior association with to understand her ties to the FSB.
For example, the complaint provides a detailed description of a trip she made to the US in 2018 and the emails the American participants sent to Burlinova after meeting with her. It doesn’t provide the content of the emails — but it makes those who sent them aware that the FBI knows what got sent.
Of even more interest is an article a former participant of Burlinova’s event wrote in 2020. Without explaining how he received it, Burlinova’s FSB handler sent it to her and said it’d be a really huge deal if it were published.
On October 30, 2020, the FSB Officer forwarded to Burlinova an article written by a participant in the 2019 Meeting Russia program, which argued that Russian malign influence efforts were actually legitimate uses of state soft power. The FSB Officer commented to Burlinova that the article was a huge result for them and would be revolutionary if printed by a named English-language newspaper in the United States and a named English-language newspaper in Europe.
The complaint doesn’t tell us whether it was published (update: it was this one, which was also posted on Burlinova’s site; h/t Alex Finley). But the description would be plenty for its author to understand that it had been the focus of internal discussion at the FSB.
Both these indictments necessarily focus on the US, but both conspiracies are international. Laying out the charges in the US and arresting anyone that would one day be arrested might something the FBI would want to do before sharing the underlying intelligence with allies.
And some of the details describe the greater international success of this effort. One of Burlinova’s biggest successes, for example, came in seeing two former participants in her yearly event elected to parliament.
On October 5, 2018, Burlinova informed the FSB Officer about two prior participants in another Russian public diplomacy program in which Burlinova had been involved. Burlinova reported that the two prior participants, both of whom resided in a European country, were running for public office. Burlinova stated that these were the results that take years to come into fruition. The FSB Officer responded that this was truly the result for which they were striving and requested that Burlinova provide more information about these prior participants and the election for public office so that the FSB Officer could prepare a report. The two candidates ran for parliamentary positions; one won in that election, and the other was elected subsequently to parliament.
Again, we don’t know which members of parliament these are and in which country, but others in their country likely recognize it.
A report in the WaPo — the timing of which may be coincidental or may explain why DOJ rolled out the charges earlier this week — describes the stakes. It describes the Kremlin’s involvement in the red-brown coalition opposing the Ukraine war in Germany.
The coming together of political opposites in Berlin under the banner of peace had been percolating for months, though the union remains ad hoc and unofficial. But marrying Germany’s extremes is an explicit Kremlin goal and was first proposed by senior officials in Moscow in early September, according to a trove of sensitive Russian documents largely dated from July to November that were obtained by a European intelligence service and reviewed by The Washington Post.
The documents record meetings between Kremlin officials and Russian political strategists, and the Kremlin’s orders for the strategists to focus on Germany to build antiwar sentiment in Europe and dampen support for Ukraine. The files also chronicle the strategists’ efforts to implement these plans and their reports back to the Kremlin. The documents do not contain any material that records communications between the Russian strategists and any allies in Germany. But interviews show at least one person close to Wagenknecht and several AfD members were in contact with Russian officials at the time the plans were being drawn up.
Like the Florida effort, the German one features manifestos written by the Kremlin.
The aim of a new political formation, according to a document dated Sept. 9, would be to win “a majority in elections at any level” in Germany and reset the AfD to boost its standing beyond the 13 percent the party was polling at then. The reset, laid out among the documents in a proposed manifesto for the AfD that was written by Kremlin political strategists, includes forging the AfD into the party of “German unity” and declaring sanctions on Russia as counter to German interests.
[snip]
It is not clear from the documents how the political strategists working with the Kremlin attempted to communicate with members of the AfD or other potential German allies about Moscow’s plans. But soon after the Kremlin gave the order for a union to be forged between Wagenknecht and the far right, AfD deputies began speaking in support of her in parliament and party members chanted her name at rallies. Björn Höcke, chairman of the AfD in Thüringen in eastern Germany, publicly invited her to join the party.
This is the same kind of effort — but much more impactful — as the Ionov one was fostering in the US (though the right wing secessionist described in it as an unindicted co-conspirator, understood to be Louis Marinelli, was not arrested).
And it’s the kind of horseshoe leftist that Greenwald once posed as before he joined up with Tucker full time … most recently to claim these socialists were arrested for their dissidence and not because they were hiding ties with Russian spies.
Update: RFERL did a bunch of interviews with people who attended Burlinova’s program, some who were shocked about the FSB tie, some who were quite blasé about it.