Deconfliction in Dragnet Databases
I want to return to something that appears in both of the Hemisphere slide decks we’ve seen: Deconfliction.
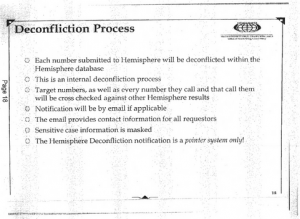
In addition to helping law enforcement find burner phones and contact chains, using connections that include location, Hemisphere helps deconflict between multiple investigative teams.
When multiple teams are working the same targets — in war or criminal investigations — you need to be aware of what other teams are doing. In war, this helps to ensure you don’t shoot a friendly. In investigations, it helps to protect turf and combine efforts.
In investigations — especially drug or terrorism ones that rely on informants — it also helps to distinguish legally sanctioned crime — that of informants — from that which no law enforcement agency is directing. And, as the Declaration deck explains, Hemisphere checks new queries against previous ones, and emails requestors if someone has already chained on that contact.
- Target numbers, as well as every number they call and that call them will be cross checked against other Hemisphere results
- Notification will be by email if applicable
- The email provides contact information for all requestors
In other words, in addition to the way it serves as a quick investigative tool, Hemisphere also helps drug investigators to avoid stepping on each others’ toes (or at least communicate better).
Then there’s this:
- Sensitive case information is masked
This seems to suggest Hemisphere doesn’t, presumably, provide any hints about how the original investigator is conducting their investigation, whether suspected traffickers are bring run or not. That’s the kind of thing that would be “masked.” (Note, this suggests that whoever is running this database would have access to that masked information.)
I raise all this because it poses questions for other databases involving informants. As I have noted, FBI uses the phone dragnet (and therefore presumably the Internet dragnet in whatever form and geographic locale it still exists) to identify potential informants. And one thing FBI does with its back door searches during assessments assessments is review actual content collected under traditional FISA and FAA in its quest for informants.
These dragnet databases play a key role in the selection and recruitment of informants to use in terrorism investigations.
But then what happens?
The example of David Headley — who played a crucial role in one of the most lethal terrorist attacks since 9/11, the Mumbai attack, the early period of which while he served as an informant for the DEA — is instructive. The FBI likes to boast that Section 702 helped stop Headley’s plot against Danish cartoonists. But Headley’s case should, instead, raise real questions about how it is a terrorist can plan a complicated terrorist attack while his known terrorist colleagues, presumably, are being surveilled without detection by the people supposedly handling him.
We know that the metadata dragnets, at least, put some identifiers on a “defeat list.” There’s reason to suspect (in part from the syntax of redacted references to the defeat list) they do so not just for high volume numbers, but for sensitive numbers (perhaps Congress, for example). But I also think they may put informants on a defeat list too. That’s, in part, because if you didn’t do so their handlers would become two degrees from terrorist suspects, which might have all sorts of unintended consequences. That’s just an educated guess, mind you, but if I’m right it would have some interesting implications.
That doesn’t appear to have prevented DEA from tracking Manssor Arbabsiar, the Scary Iran Plotter (I assume he at least used to be an informant, because there’s little else that would explain why the cousin of a top Quds Force Member busted for drug possession would nevertheless get citizenship, and deconfliction discussions show up in what was probably his immigration file).
But it would raise really big questions in other cases.
One way or another they need to give informants special treatment in databases — as they apparently do in Hemisphere. How they do so, however, may have real consequences for the efficacy of the entire dragnet.


Very nice set of Tags here.