How Did Booz Employee Analyst-Trainee Edward Snowden Get the Verizon 215 Order?
One thing I’ve been pondering as I’ve been going through the Snowden emails liberated by Jason Leopold is the transition Snowden made just before he left. They show that in August 2012, Snowden was (as we’ve heard) a Dell contractor serving as a SysAdmin in Hawaii.
The training he was taking (and complaining about) in around April 5 – 12, 2013 was in preparation to move into an analyst role with the National Threat Operations Center.
That would mean Snowden would have been analyzing US vulnerabilities to cyberattack in what is a hybrid “best defense is a good offense” mode; given that he was in HI, these attacks would probably have been launched predominantly from, and countermeasures would be focused on, China. (Before Stewart Baker accuses me of showing no curiosity about this move, as Baker did about the Chinese invitation to Snowden’s girlfriend to a pole dancing competition, I did, but got remarkably little response from anyone on it.)
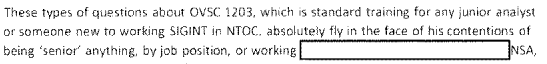
It’s not clear why Snowden made the switch, but we have certainly seen a number of cybersecurity related documents — see the packet published by Charlie Savage in conjunction with his upstream cyber article. Even the PRISM PowerPoint — the second thing released — actually has a cybersecurity focus (though I think there’s one detail that remains redacted). It’s about using upstream to track known cyberthreat actors.
I suspect, given the inaccuracies and boosterism in this slide deck, that it was something Snowden picked up while at Booz training, when he was back in Maryland in April 2013. Which raises certain questions about what might have been available at Booz that wasn’t available at NSA itself, especially given the fact that all the PRISM providers’ names appear in uncoded fashion.
Incidentally, Snowden’s job changes at NSA also reveal that there are Booz analysts, not NSA direct employees, doing Section 702 analysis (though that is technically public). In case that makes you feel any better about the way the NSA runs it warrantless surveillance programs.
Anyway, thus far, all that makes sense: Snowden got into a cybersecurity role, and one of the latest documents he took was a document that included a cybersecurity function (though presumably he could have gotten most of the ones that had already been completed as a SysAdmin before that).
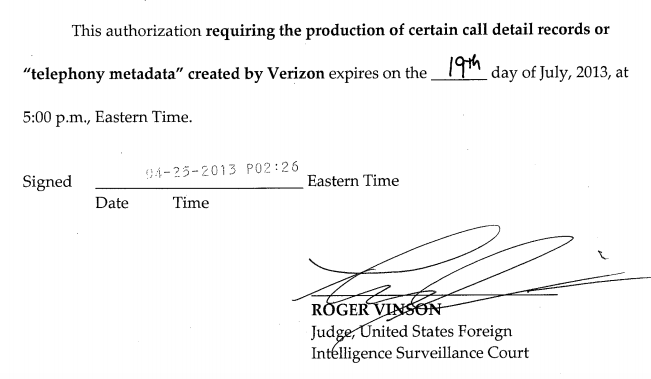
But one of the most sensitive documents he got — the Verizon Section 215 primary order — has nothing to do with cybersecurity. The Section 215 dragnet was supposed to be used exclusively for counterterrorism. (And as I understand it, there are almost no documents, of any type, listing provider names in the Snowden stash, and not all that many listing encoded provider names). But the Verizon dragnet order it is dated April 23, 2013, several weeks into the time Snowden had moved into a cybersecurity analytical role.
There’s probably an easy explanation: That even though NSA is supposed to shift people’s credentials as they move from job to job, it hadn’t happened for Snowden yet. If that’s right, it would say whoever was responsible for downgrading Snowden’s access from SysAdmin to analyst was slow to make the change, resulting in one of the most significant disclosures Snowden made (there have been at least some cases of credentials not being adjusted since Snowden’s leaks, too, so they haven’t entirely addressed what would have to be regarded as a major fuck-up if that’s how this happened).
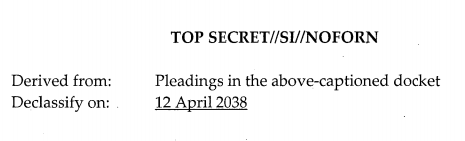
Interestingly, however, the declassification stamp on the document suggests it was classified on April 12, not April 23, which may mean they had wrapped up the authorization process, only to backdate it on the date it needed to be reauthorized. April 12, 2013 was, I believe, the last day Snowden was at Fort Meade.
Whatever the underlying explanation, it should be noted that the most sensitive document Snowden leaked — the one that revealed that the government aspired to collect phone records from every single Verizon customer (and, significantly, the one that made court challenges possible) — had to have been obtained after Snowden formally left his SysAdmin, privileged user, position.


It sounds almost like the data system where I worked, that tracked work orders from creation to completion.
I was doing QC that required one set of permissions, left for a year and a half, and came back, and when they gave me access to that system some time later, I still had the original set of permissions, as well as the ones required for the job I was actually in. (It had a scary lot of things that could be done. I could look at work in progress almost anywhere, as well as moving stuff from queue to queue in my own workgroup.)
Having been in both roles, sometimes simultaneously, it would
normally be a sysadmin responsibility to revoke or change access
to a user whose role has changed (or was terminated).
[Note: control over role and access may be delegated to a
lessor admin group that has some privileges to perform their
role/access responsibility, but they are not true sysadmins in
terms of having root, they basically are clerks and auditors.]
So one must ask, was ES supposed to change his own role (and
access permissions)? Even if he was supposed to revoke his own
access permissions, did he have time to do so? Was there a
replacement sysadmin in place in HI in a timely fashion that ES
could bring up to speed? If so, was the replacement competent
and did ES trust the replacement? If I was in such a situation,
and any of my questions could be answered in the negative,
I would do *nothing*. I would not revoke my own access because
the odds are *so* high that there would be a crisis that I would be
called on to resolve, that if I had revoked my own access, I may not
be able to solve the problem, and I would still end up looking like the bad guy, the scapegoat for the inept management. Bottom line,
ES should not have had to revoke his own access, there should be
proper procedures in place, but it sure appears that what we are
seeing is bureaucracy in ‘action’.
And at this point in spring 2013, ES was quite clear
In his mind that things were fucked up at no such agency.
At some turning point, likely 2013-04-13 or so, he realized
that FISC was a scam. He knew that the reauth should have
already happened at that point. But it did not. Then the reauth
happened but was backdated. So, you think you are doing the
right things for your country, but you see the non-public
machinations happening behind the scenes.
To be clear: there’s no reason to believe the reauth did not happen in timely fashion.
Thank you.
Who knew there was such things as pole-dancing competitions? I mean, I suppose since people who do “things” will compete against other people who do the same “things”, regardless of what those “things” are, just because people compete, it wouldn’t be out of the ordinary for “things” such as pole-dancing competitions to exist.
.
I mean, I was once driving through the Baltimore area and wound up with an AM station on the dial that clearly catered to the black-church market. They were discussing the upcoming church usher team competition. Seriously. But, still….
.
And how did the Chinese know Snowden’s girlfriend was a pole-dancer, let alone one who might compete at it? And how did the Chinese know she as Snowden’s girlfriend? And how did the Chinese know they might be interested in Snowden, through his girlfriend, in the first place.
.
Smells to me like typically lousy ‘Murcan OPSEC.
.
But that’s nothing new – today’s WSJ print edition has a front-pager disclosing that the emails from HRC’s unclassified basement server that people are so agitated about dealt with State Department people conversing with their in-country colleagues on whether State would oppose or support continued use of drones to whack people in Pakistan. In other words, one of the most sensitive – and most closely held – secrets in the ‘murcan panoply of secrets was being discussed in an unclassified forum, and left open for the world (of hackers) to see.
.
Still….
I’m not surprised about the pole-dancing, having competed in weird sports. The networks are pretty tight, and she was in the region.
Also it’s not clear the Chinese did know they were together (tho agree American opsec would suggest they did). Just that when she was invited Snowden told the NSA, as obligated to do.
Worth remembering that, when you sit in the upper deck at the Washington Nationals’ shiny new stadium down in Southeast, your view of the Capitol Dome is blocked by the Booz Allen building. I doubt that was an accident.
Almost all of the NSA’s work is now contracted out.
In wake of the Ed Snowden leaks, a call to reverse the outsourcing
http://www.nytimes.com/2013/06/18/opinion/put-the-spies-back-under-one-roof.html?_r=0
Now, the agency is up to 80% outsourced.
Do you have a link for the 80% number?
I saw it the other day and didn’t give it much thought till I saw the Booz article. The New York Times article linked above assigns a figure of 70 percent to the amount outsourced from the entire intelligence budget, of which the NSA is one agency.
This clarifies my question: how would Edward Snowden gather itelligence while in training?
Further, does Edward Snowden have specific individuals whom he had already targeted for investigation prior to his assigned date with the new position?
There’s zero evidence he investigated any individuals (and that is far harder from an analyst standpoint than from a SysAdmin one). He did, however, collect the names of cooperating companies.
EW: re: Three month reauth. You are correct, I should not have
said backdated. They likely don’t give a damn about backdating
and trying to make things appear legit. In this instance, it appears
they did not even try. My bad gubmint math.
Order expires: 2013-07-19.
Order “signed”: 2013-04-25.
(A week late)
My interpretation: it is all ‘ongoing’, the legal paperwork is
just a ‘clerical’ problem.
This does not mean that it was *not* backdated, but it does miss
the 3 month reauth as you and aclu concluded. Oh, wait. The order
does say 3 months of metadata, ending july 19. So, obviously, the
signing date means nothing, *or*, the companies involved are
*ALREADY* under a separate *ORDER* to *RETAIN*,
*AT ALL TIMES HENCEFOWARD*, all metadata that the gubmint
*may want* (haha). This then would make complete sense, as
the 215 order(s) really have nothing whatsoever to do with collection,
they are just legal instruments to force/allow *delivery* of already
collected metadata. (likely taxpayer money to subsidize telcos to
provide the metadata that the taxpayers generate. Sweet!)
https://www.emptywheel.net/2014/03/29/new-dragnet-order-suggests-spike-in-215-orders-may-include-financial-credit-card-records/
http://genius.com/Aclu-criminal-complaint-against-nsa-james-clapper-annotated
I suspect the ongoing collection is happening under EO 13355,
and *not* directly under 12333 as many point to.
I suspect Mr. Wyden would agree with my conclusion, but alas,
he is not at liberty to discuss such at this point in time.