[NB: check the byline, thanks. This post contains some speculative content. /~Rayne]
Albania is a tiny country. Its population is a little smaller than that of Kansas, all living in a land mass the size of Massachusetts or Hawaii. The U.S. has six counties which are larger in area, and six which are larger in population.
It seems rather odd that two different stories related to Rudy Giuliani happened to involve Albania given its relative size.
While Giuliani was politicking an exiled Iranian dissident/terrorist group each year, often in Albania where the exiles waited regime change, an FBI special agent was schmoozing Albanians about oil drilling rights among other things.
What are the chances these two story arcs are wholly unrelated?
Items in the following timeline related to Charles McGonigal including some related to Russia are in italics; Albanian-specific items are noted in boldface.
– – –
2014-2019 — Giuliani met with the People’s Mojahedin Organization of Iran, or Mojahedin-e-Khalq Organization (MEK) at least once each year; he never registered under FARA, appearing at MEK-related events in Poland, Albania, Paris and Washington (NBC News, Oct 2019)
– – –
April 2017 — Approximate time relationship between then-Special Agent Charles McGonigal and Allison Guerriero began (earliest date of requested documents from Nov. 2021 subpoena)
Spring 2017 — Giuliani and ally Michael Mukasey met with Iranian dissident group MEK.
01-JUL-2017 — John Bolton met with MEK members in Paris, advocating Trump admin push for regime change in Iran.
17-JUL-2017 — John Bolton tweeted, “Withdrawing from the Iran #NuclearDeal should be a top @realDonaldTrump administration priority.”
05-SEP-2017 — Date given in the DC District indictment for second count against McGonigal, for false statements under 18 USC 1001(a)(2), related to filing of an FD-772b for travel beginning two days later.
07-SEP-2017 — McGonigal met with Person A and negotiated terms of compensation; he traveled by air with Person A to Albania, met Person B and other foreign nationals.
09-SEP-2017 — McGonigal met with Person B and Albania‘s Prime Minister, during which McGonigal lobbied against Albania awarding oil field drilling licenses to Russian front companies. Person A and Person B both had financial interests in Albania‘s award decision.
September 2017 — While in Albania, Person A introduced McGonigal to an Albanian businessperson/politician who asked McGonigal to launch an investigation into an alleged plot to kill the Albanian businessperson/politician.
10-SEP-2017 — McGonigal traveled with Person A and others, from Albania to Kosovo. He met a Kosovar politician. McGonigal then returned to the US with Person A, traveling together.
September 2017 — McGonigal continued a relationship with Albania‘s prime minister after returning from Albania.
Fall 2017 — McGonigal received cash from Person A at Person A’s residence in separate payments of $80,000 and $65,000. McGonigal told Person A the money would be paid back.
05-OCT-2017 — Allison Guerriero saw “a bag full of cash” in FBI’s SA Charles McGonigal’s Park Slope apartment.
16-OCT-2017 — Date given for third count against McGonigal, for false statements under 18 USC 1001(a)(2), related to filing of an FD-772b.
15-NOV-2017 — Date given for fourth count against McGonigal, for false statements under 18 USC 1001(a)(2). McGonigal submitted a false FD-772 in advance of “official” travel to Austria. He did not disclose Person A was traveling with him; he did not indicate travel expenses would be covered by another party; he did not indicate he would be traveling to Albania as well as Austria; he did not disclose any other expected foreign contacts.
17-NOV-2017 — McGonigal flew to Austria.
18-NOV-2017 — With Person A acting as an interpreter, McGonigal along with a DOJ prosecutor (?!) interviewed the Albanian businessperson/politician McGonigal met in September. McGonigal did not submit paperwork for authorization of interpreter services or their payment, nor was an official FBI record filed of the interview.
18-NOV-2017 — McGonigal and Person A traveled from Austria to Albania after the interview, meeting again with the Albanian businessperson/politician. No DOJ prosecutor was present. The Albanian businessperson/politician discussed business opportunities with McGonigal and Person A.
21-NOV-2017 — McGonigal flew from Albania to Austria and then the US. Neither McGonigal nor the FBI paid for his lodging during his stay in Albania.
24-NOV-2017 — McGonigal received information from Person B about a US citizen registered to lobby on behalf of a Albanian political party in opposition to the Albanian PM’s party.
25-NOV-2017 — McGonigal informed the DOJ prosecutor involved in the November 18 interview of a potential new criminal investigation involving the US citizen who was a lobbyist for an Albanian opposition party.
December 2017 — Washington DC: McGonigal dined with Person A and Albanian government officials. New York City: McGonigal dined with Person A and Albania‘s PM.
– – –
04-JAN-2018 — McGonigal received information from Person A about the Albanian opposition party’s US citizen-lobbyist. He forwarded the information to another FBI NY special agent on 05-JAN-2018.
22-JAN-2018 — Date given for fifth count against McGonigal, for false statements under 18 USC 1001(a)(2). McGonigal filed a false FD-772b about the November trip to Austria. He did not report his trip to Albania; he did not report his meeting with Person B or Albania‘s PM; he did not report he had disclosed his FBI employment to foreign nationals on non-FBI business.
21-FEB-2018 — Through 24-FEB, McGonigal traveled with Person A to Albania without reporting the trip on FD-772 or FD-772b forms.
26-FEB-2018 — FBI-NY opened a criminal investigation into the Albanian opposition party’s US citizen-lobbyist at McGonigal’s request. FBI-NY later identified Person A as a confidential human source for the investigation; Person A provided information during the investigation. At a later date, Person B helped facilitate a meeting between FBI-NY and witnesses in Europe, including paying for witness travel expenses. McGonigal did not report his relationship with Person A, nor did he report contacts with Person B on form FD-981 as required.
04-MAR-2018 — McGonigal shared a meal with Person A, Albania‘s PM, a former FBI special agent who then worked at an international professional services firm and others in Washington DC.
20-MAR-2018 — Giuliani met with MEK leader Rajavi at MEK event in Tirana, Albania.
22-MAR-2018 — Trump announced by tweet that John Bolton would become National Security Adviser.
06-APR-2018 — Treasury Dept. identifies Russian oligarch Oleg Deripaska as a Specially Designated National (SDN) subject to sanctions.
09-APR-2018 — John Bolton began as National Security Adviser.
26-APR-2018 — Through May 2, McGonigal traveled with Person A to Europe including Albania; he did not report the travel on FD-772 or FD-772b forms.
27-APR-2018 — McGonigal met with Person C (a national of Bosnia and Herzegovina) and Person D (a national of Bosnia and Herzegovina) in Germany. C and D asked to meet with the US Ambassador to the United Nations or another high-level US govt. official to request US support for a political purpose affecting Bosnia and Herzegovina.
08-MAY-2018 — McGonigal asked FBI’s liaison to UN for assistance arranging a meeting requested by Person C and Person D.
08-MAY-2018 — Trump unilaterally exited the P5+1 JCPOA agreement with Iran.
09-MAY-2018 — US to reimpose sanctions on Iran — 180-day countdown to implementation began.
Spring-Summer 2018 — Deripaska’s connection, former translator for Russian Federation’s Ministry of Foreign Affairs Sergey Shestakov, asks McGonigal to help Agent-1 obtain an internship for Agent-1’s daughter in counterterror/intel/international relations. McGonigal agreed.
10-JUN-2018 — Date given for sixth count against McGonigal, for false statements under 18 USC 1001(a)(2). Until May 2019, McGonigal created and submitted a false OGE-278 report which failed to include $225,000 in payments from Person A. An eighth count was charged under 18 USC 1519 for falsification of a record or document.
25-JUN-2018 — McGonigal proposed to Person A that Person A and Company A contract with Person D and Person D’s pharma company, by which Company A would be paid $500,000 by Person D and their pharma company (located in Bosnia and Herzegovina) in exchange for arranging a meeting between Person D’s pharmaco and a US delegation rep to the UN.
28/30-JUN-2018 — German, French and Belgian police broke up an assassination/terror plot to set off an explosive device at an MEK gathering in Paris. Iranian intelligence (MOIS) was believed to be behind the plot; Giuliani had been in attendance at the event. Four Iranians were eventually arrested including Assadollah Assadi, an Iranian intelligence officer assigned to Vienna under diplomatic cover.
01-JUL-2018 — McGonigal sent electronic message to Person A confirming he resent proposed contract, asking Person A to protect his name.
03-JUL-2018 — Iran’s President Hassan Rouhani traveled to Switzerland and Austria to attempt to salvage the JCPOA.
18-JUL-2018 — Person A proposed the contract to Person D as described on 25-JUN.
26-JUL-2018 — McGonigal provided to FBI’s UN liaison dates proposed for a meeting requested by Persons C and D.
06-AUG-2018 — First series of sanctions reengaged and next 180-day countdown began.
13-AUG-2018 — During a meeting, McGonigal provided information to a senior official for US delegation to UN about the meeting request by Persons C and D. McGonigal didn’t disclose Person A’s financial interest or McGonigal’s financial relationship with Person A.
22-AUG-2018 — Giuliani lobbied Romania on behalf of Freeh Group; Freeh’s client was not specified. Giuliani’s letter was in opposition to U.S. State Dept. policy on Romanian anticorruption efforts.[1]
September 2018 — Charles McGonigal left FBI and began working as Senior VP at Brookfield Properties, a subsidiary of Brookfield Asset Management which is owned in part by Qatar. Brookfield signed a 99-year lease on Jared Kushner’s 666 5th Avenue building in August 2018.
04-NOV-2018 — Second series of sanctions reengaged including purchasing fossil fuels from Iranian oil companies.
Late 2018 — McGonigal broke up with Guerriero. “A few months later” she ratted on McGonigal to William Sweeney, FBI-NY office.
– – –
2019 — Shestakov and McGonigal introduced Agent-1 to an international law firm so that Agent-1 could work to have Deripaska delisted as an SDN, lifting sanctions. Throughout the year, McGonigal traveled to meet Deripaska in London and Vienna at Deripaska’s residences. The law firm was to pay McGonigal $25,000 out of $175,000 it received for its services to Agent-1.
XX-FEB-2019 — Trump discussed replacements for DNI.
06-MAY-2019 — Date given for first count against McGonigal, for concealment of material facts under 18 USC 1001(a)(1) for filing false forms FD-772, FD-772b, FD-981, and OGE-278 which did not include information about his travel, compensation for travel-related expenses, relationships with foreign nationals, and the $225,000 received from Person A. The OGE-278 filed after his retirement was submitted this date for which a seventh count was charged under 18 USC 1001(a)(2). A ninth count was charged under 18 USC 1519 for falsification of a record or document.
20-JUN-2019 — In retaliation for downing a U.S. drone, Trump approved strikes on Iran which were abruptly aborted.
11-JUL-2019 — Giuliani spoke to MEK in Albania and met with its leader Maryam Rajavi.
28-JUL-2019 — Director of National Intelligence Dan Coats’ departure and John Ratcliffe nominated as replacement announced by Trump via Twitter. (Ratcliffe later removed himself from consideration.)
08-AUG-2019 — Primary Deputy Director DNI Sue Gordon resigned effective 15-AUG-2019, without additional prior notice, as ordered. Resignation letter without handwritten note.
15-AUG-2019 — Coats’ last day as DNI.
30-AUG-2019 — Trump tweeted a high-resolution satellite image of Iran’s failed Safir SLV launch while claiming the U.S. was not involved. The image may have been classified and ‘insta-declassified’ by Trump.
09-SEP-2019 — Trump asked for Bolton’s resignation and tweeted about it the next morning.
10-SEP-2019 — Bolton tells Fox’s Brian Kilmeade by text that he quit.
11-SEP-2019 — Bloomberg reported Bolton pushed back Monday-Tuesday at Trump over Iran sanctions; Bolton wanted maximum pressure while Trump wanted to encourage a meeting with Iran’s Rouhani later in September.
20-SEP-2019 — Mukasey registers as representative for MEK, claiming no compensation for this work; Giuliani remains unregistered.
27-DEC-2019 — K1 military base in/near Kirkuk, Iraq attacked by Kataib Hezbollah, a group linked to Iran. The group denied responsibility. A US contractor was killed and US soldiers wounded.
29-DEC-2019 — Trump ordered retaliatory airstrikes in western Iraq and eastern Syria targeting Kataib Hezbollah’s locations.
30-DEC-2019 — While golfing, Trump told Sen. Lindsey Graham about a plan to assassinate Iran’s Gen. Soleimani.
31-DEC-2019 — US Embassy-Baghdad stormed by Kataib Hezbollah. Sen. Graham tweets about meeting with Trump regarding the embassy.
31-DEC-2019 — Trump threatens Iran by tweet.
– – –
02-JAN-2020 — Trump authorizes assassination of Iran’s General Soleimani by missile strike.
March 2020 — Law firm and McGonigal’s work on behalf of Agent-1 ended.
– – –
Spring 2021 — Agent-1 negotiated with Shestakov and McGonigal to work directly for Deripaska on sanctioned matters, bypassing the law firm.
August 2021 — McGonigal, Shestakov, and Agent-1 drafted a contract for business intelligence services paid to an intermediary corporation owned by McGonigal’s “friend” who then paid McGonigal.
November 2021 — DOJ investigation of McGonigal underway; Guerriero received a subpoena.
– – –
Early Jan 2022 — McGonigal left employment at Brookfield.
Mid-July 2022 — Albania suffered a serious cyberattack for which it blamed Iranian groups.
07-SEP-2022 — Albania severed diplomatic ties with Iran over the cyberattacks; it had considered invoking Article 5 as a member of NATO.
– – –
I couldn’t help think of the relationship between Albania and Iran during the last week of January when an Iranian military industrial facility located in Isfahan province was attacked by drones which appeared to be under Israeli control.
The possibility crossed my mind that all of this effort with McGonigal working for Russians and Albanian opposition, and Giuliani and Bolton propping up MEK against Iran was intended to squeeze Albania between larger geopolitical players, possibly spreading destabilization to other neighboring countries. Montenegro, for one, has been under various forms of pressure for years by Russia because of its accession to NATO against which Russia pushed back.
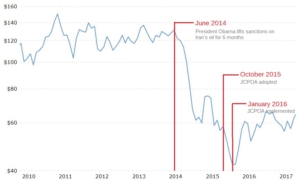
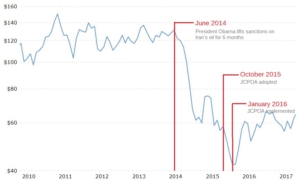
Nor could I help but think of crude oil and gas market price fluctuations[2], and the threat to the EU due to Russia’s war on Ukraine and subsequent sanctions on Russia.
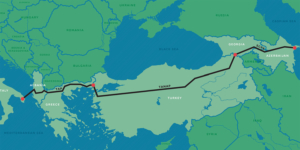
Where Albania fits into that picture along with Bosnia and Herzegovina, and with Romania, is the Southern Gas Corridor running from Azerbaijan through Turkey and finally through Albania, with a leg to the north from Turkey through Bulgaria and Romania to Ukraine.
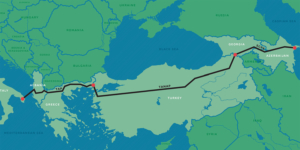
Have Giuliani and McGonigal been used to increase instability in Albania in order to disrupt gas distribution to NATO member states in EU?
Have both of these corrupt hacks been used to increase instability in Albania to put pressure on a couple of the smallest NATO members, including Albania’s neighbor Montenegro which also plays a role in gas pipelines to EU states?
_________
[1] This item added because it seems like such an odd item. Tirana, Albania is a four-hour flight from Bucharest, Romania, though.
[2] This is a guesstimated amount Putin/Russian oil companies lost after Obama eased sanctions on Iranian oil during P5+1 JCPOA negotiations until the eventual implementation of the JCPOA. It does not include the amount lost after implementation.
8614.21 BBL/D/1K x 7 days x 73 weeks x -$45/BBL =
(8614.21 x 1000) x (511 days) x -$45/BBL =
-$198,083,758,950 lost
Based on average daily production 1992-2022 (see: https://tradingeconomics.com/russia/crude-oil-production) and at one-half the difference between WTI’s highest price in June 2014 and its price in January 2016.








 public domain
public domain
