Trump Fighting for Floating Petri Dishes but Not Life-Saving Ventilators
Trump’s response to learning that the cruise industry — which is almost entirely flagged overseas, in part to avoid US taxes — would not be eligible to tap the $500 billion slush fund for large businesses was to work to find a “legislative fix” so these floating petri dishes could survive a pandemic exacerbated by their industry.
Sr. admin official says bipartisan Senate grp working to ensure they can access one of the facilities–or else will seek a legislative fix in the next package.
He proposed adopting Josh Hawley’s offer, which is that if they registered here they could qualify for this loan package.
Meanwhile, on the same day Trump went out of his way to think creatively about how to fund an industry that has almost no societal value that isn’t already being addressed with extended unemployment benefits, outlets reported that the Trump Administration was balking on a plan — which both Trump and Mike Pence had already celebrated — to back a joint venture between General Motors and ventilator manufacturer Ventec Life Systems to produce up to 80,000 ventilators in Kokomo, IN. The problem: $1 billion was too much to spend to address the acute shortage of ventilators in the country.
The decision to cancel the announcement, government officials say, came after the Federal Emergency Management Agency said it needed more time to assess whether the estimated cost was prohibitive. That price tag was more than $1 billion, with several hundred million dollars to be paid upfront to General Motors to retool a car parts plant in Kokomo, Ind., where the ventilators would be made with Ventec’s technology.
By the end of the day, both Trump and Dr. Deborah Birx questioned the number of ventilators New York Governor Andrew Cuomo has consistently said his state will need.
“I have a feeling that a lot of the numbers that are being said in some areas are just bigger than they’re going to be,” he said. “I don’t believe you need 40,000 or 30,000 ventilators. You go into major hospitals sometimes, and they’ll have two ventilators. And now all of a sudden they’re saying, ‘Can we order 30,000 ventilators?’”
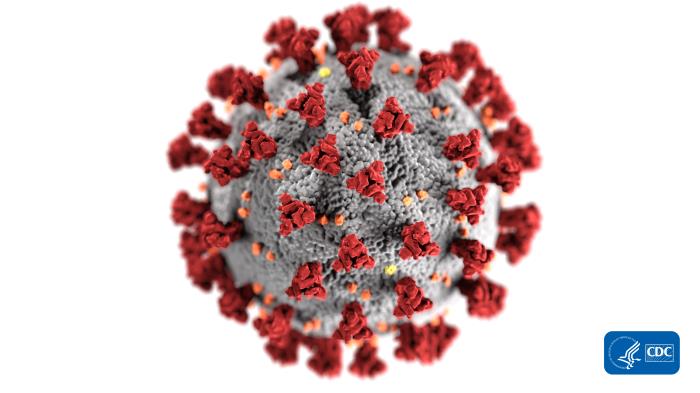
New York has become the new epicenter of the coronavirus outbreak in the United States, with hospitals struggling to keep up with larger patient numbers and limited supplies, including masks, gowns and ventilators. In severe cases of Covid-19, the illness caused by coronavirus, ventilators can allow patients to breathe with incapacitated lungs — a common outcome of the disease.
Dr. Deborah Birx, the White House coronavirus response coordinator, said earlier on Thursday she was told that New York had enough ventilators to meet current needs. While there may be shortages in urban areas like New York City, Birx said, there are other parts of the state “that have lots of ventilators and other parts of New York state that don‘t have any infections right now.“
“There is still significant — over a thousand or two thousand ventilators that have not been utilized yet,” Birx said. “Please, for the reassurance of people around the world, to wake up this morning and look at people talking about creating DNR situations — do not resuscitate situations for patients — there is no situation in the United States right now that warrants that kind of discussion.“
Trump’s interest in thinking creatively to fund the cruise industry as compared with his stinginess regarding crucial medical needs is not just malpractice during a pandemic.
But it doesn’t even serve his own stated priorities.
Trump has said he wants the economy to resume as soon as possible — he has been pushing for an Easter restart. Both WA (where Ventec is headquartered), MI, and IN are under state-wide stay-at-home orders, permitting only essential workers in the state to leave their homes to go to work. With some exceptions, the stay-at-home orders in the Midwest have shut down much of the auto industry.
Redeploying a parts plant in IN to produce ventilators would be a way to shift a facility and its workers from the non-essential category to the essential category, potentially getting them working before the stay-at-home orders are lifted.
Indeed, pushing manufacturers to shift production to items deemed essential, via whatever means (in this case, the venture would be supported only by a purchase agreement, but the Defense Production Act could be used to do even more of this). And even if Cuomo is overestimating how many ventilators he’ll need (there’s no reason to believe he is), if there’s a surge in COVID cases in the southern hemisphere as it shifts into fall, there’ll be plenty demand worldwide to pick up the slack.
Even if it led to a glut, one of the best employment policies right now would be to shift as much short- to medium-term production from goods deemed non-essential to goods deemed essential. Even if the US government overpays for those products, it’d be a better jobs program than restarting the cruise industry.
Trump continues to fool himself about where capitalism ends and state support begins. But he’s also adopting a policy that undermines his own hopes to get as many people back to work as he can.

![[image: Jenni C via Flickr]](https://www.emptywheel.net/wp-content/uploads/2016/01/TuesdayFlipOffCaps_JenniC-Flickr.jpg)