In Mistaking Surveillance for Sabotage, NYT Fearmongers Nukes Again
Last night, the NYT had an alarming story reporting that suspected Russian spies were compromising engineers that work at nuclear power plants across the United States. Amber! the story screamed.
Since May, hackers have been penetrating the computer networks of companies that operate nuclear power stations and other energy facilities, as well as manufacturing plants in the United States and other countries.
Among the companies targeted was the Wolf Creek Nuclear Operating Corporation, which runs a nuclear power plant near Burlington, Kan., according to security consultants and an urgent joint report issued by the Department of Homeland Security and the Federal Bureau of Investigation last week.
The joint report was released on June 28. It was obtained by The New York Times and confirmed by security specialists who have been responding to the attacks. It carried an urgent amber warning, the second-highest rating for the severity of the threat.
After screaming “Amber,” the story went on to scream “bears!”
The origins of the hackers are not known. But the report indicated that an “advanced persistent threat” actor was responsible, which is the language security specialists often use to describe hackers backed by governments.
The two people familiar with the investigation say that, while it is still in its early stages, the hackers’ techniques mimicked those of the organization known to cybersecurity specialists as “Energetic Bear,” the Russian hacking group that researchers have tied to attacks on the energy sector since at least 2012.
Ultimately, the story worked its way up to invoke StuxNet, an attack on the actual enrichment processes of a nuclear facility.
In 2008, an attack called Stuxnet that was designed by the United States and Israel to hit Iran’s main nuclear enrichment facility, demonstrated how computer attacks could disrupt and destroy physical infrastructure.
The government hackers infiltrated the systems that controlled Iran’s nuclear centrifuges and spun them wildly out of control, or stopped them from spinning entirely, destroying a fifth of Iran’s centrifuges.
In retrospect, [former chairman of the Federal Energy Regulatory Commission] Mr. Wellinghoff said that attack should have foreshadowed the threats the United States would face on its own infrastructure.
And yet, in the fourth paragraph of the story, NYT admitted it’s not really clear what the penetrations involved. With that admission, the story also revealed that the computer networks in question were not the control systems that manage the plants.
The report did not indicate whether the cyberattacks were an attempt at espionage — such as stealing industrial secrets — or part of a plan to cause destruction. There is no indication that hackers were able to jump from their victims’ computers into the control systems of the facilities, nor is it clear how many facilities were breached.
Still further down, the report admitted that this involved phishing and watering hole attacks on engineers, not attacks on control systems.
In most cases, the attacks targeted people — industrial control engineers who have direct access to systems that, if damaged, could lead to an explosion, fire or a spill of dangerous material, according to two people familiar with the attacks who could not be named because of confidentiality agreements.
[snip]
Hackers wrote highly targeted emails messages containing fake résumés for control engineering jobs and sent them to the senior industrial control engineers who maintain broad access to critical industrial control systems, the government report said.
[snip]
In some cases, the hackers also compromised legitimate websites that they knew their victims frequented — something security specialists call a watering hole attack.
That is, even while screaming “Amber Russian bear OMIGOSH StuxNet!!” the article admitted that this is not StuxNet. This amounts to spies, quite possibly Russian, “hunting SysAdmins,” just like the United States does (of course, the US and its buddy Israel also assassinate nuclear engineers, which for all its known assassinations, Russia is not known to have done).
That distinction is utterly critical to make, no matter how much you want to fearmonger with readers who don’t understand the distinction.
There is spying — the collection of information on accepted targets. And there is sabotage — the disruption of critical processes for malicious ends.
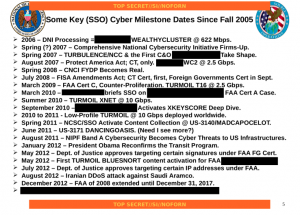
This is spying, what our own cyber doctrine calls “Cyber Collection.”
Cyber Collection: Operations and related programs or activities conducted by or on behalf of the United States Government, in or through cyberspace, for the primary purpose of collecting intelligence – including information that can be used for future operations – from computers, information or communications systems, or networks with the intent to remain undetected. Cyber collection entails accessing a computer, information system, or network without authorization from the owner or operator of that computer, information system, or network or from a party to a communication or by exceeding authorized access. Cyber collection includes those activities essential and inherent to enabling cyber collection, such as inhibiting detection or attribution, even if they create cyber effects. ( C/NF)
That doesn’t mean Russian spying on how our nuclear facilities work is not without risk. It does carry risks that they are collecting the information so they can one day sabotage our facilities.
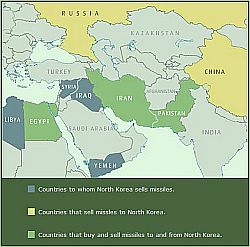
But if we want to continue spying on North Korea’s or Iran’s nuclear program, we would do well to remember that we consider spying on nuclear facilities — even by targeting the engineers that run them — squarely within the bounds of acceptable international spying. By all means we should try to thwart this presumed Russian spying. But we should not suggest — as the NYT seems to be doing — that this amounts to sabotage, to the kinds of things we did with StuxNet, because doing so is likely to lead to very dangerous escalation.
And it’s not just me saying that. Robert M. Lee, who works on cyber defense for the energy industry and who recently authored a report on Crash Override, Russia’s grid-targeting sabotage tradecraft (and as such would have been an obvious person to cite in this article) had this to say:
So while the threat to nuclear from cyber is a real concern because of impact it’s very improbable and “what about Stuxnet” is a high bar
Or said more simply: phishing emails are lightyears removed from “what about Stuxnet” arguments. It’s simply otherworldly in comparison.
There’s one more, very real reason why the NYT should have been far more responsible in clarifying that this is collection, not sabotage. Among the things Shadow Brokers, with its presumed ties to Russia, has been threatening to expose is “compromised network data from Russian, Chinese, Iranian, or North Korean nukes and missile programs.” If the NYT starts inflating the threat from cyber collection on nuclear facilities, it could very easily lead to counter-inflation, with dangerous consequences for the US and its ability to monitor our adversaries.
There is very real reason to be concerned that Russia — or some other entity — is collecting information on how our nuclear and other power facilities work. But, as Lee notes, conflating that with StuxNet is “otherworldly.”


![[Source: Google Trends and Google Finance]](http://www.emptywheel.net/wp-content/uploads/2014/03/Trend_Ukraine-Venezuela_Petro-Gas_02MAR2014-e1393824251507.jpg)