NSA’s Section 702 Success: 150 Gigs of Defense Contractor Data Protected
 Over four months ago, I noted that the most impressive success touted in James Clapper’s fact sheet on Section 702 pertained to cybersecurity, not terrorism.
Over four months ago, I noted that the most impressive success touted in James Clapper’s fact sheet on Section 702 pertained to cybersecurity, not terrorism.
Communications collected under Section 702 have provided significant and unique intelligence regarding potential cyber threats to the United States, including specific potential network computer attacks. This insight has led to successful efforts to mitigate these threats.
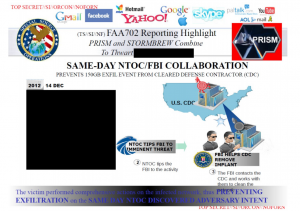
Le Monde, as part of its package on US spying on France, published yet another version of the PRISM slide presentation, including this slide (and 2 others that haven’t been published before; h/t Koen Rouwhorst).
While I’m not sure we’re yet looking at the complete PRISM slideset, at least as it stands, this slide tells the sole success story in the presentation. It describes how, on December 14, 2012, the NSA/CSS Threat Operations Center alerted the FBI to an implant on a Defense contractor’s network. The FBI and the contractor managed to take action that same day to prevent the exfiltration of 150G of data.
And thus using upstream collection (the slide cites Stormbrew), the NSA managed to do something equivalent to stopping China from getting yet another module of data on the F-35 development to go along with all the other data it has stolen.
While I’m glad the NSA prevented yet more tax dollars to be wasted on secrets China (or someone like them) was going to steal anyway, I am rather interested that this gets touted internally as Section 702’s big success story.
After all, Keith Alexander has been chanting terror terror terror terror for the last four months. It turns out — as I’ve been saying all along — it’s not about the 54 mostly overseas plots Section 702 has helped to thwart, it’s about cybersecurity.
Moreover, it doesn’t involve someone’s personal communications access via PRISM. It involves upstream collection (this also suggests when NSA describes searching for “selectors” in upstream collection, it searches on more than just emails and phone numbers, as it has previously suggested).
Again, this success is in no way a bad thing–kudos to the NSA for catching this.
It just highlights how we’re being sold a dragnet to protect against hackers based on fear of terrorists.
Update: In a Guardian post today, I argue Obama should use the replacement of Keith Alexander as an opportunity to break up NSA.
Metaphorically, the NSA has pursued its search for intelligence by partly disabling the locks to all our front doors. Having thus left us exposed, it demands the authority to be able to enter our homes to look around and see if those disabled locks have allowed any nasty types to get in.
Given the way the NSA’s data retention procedures have gone beyond the letter of the law to allow them to keep Americans’ data if it presents a threat to property (rather than just a threat of bodily harm), while the NSA is looking for nasty types, they might also make sure you don’t have any music or movies for which you don’t have a receipt. Thus it has happened that, in the name of preventing invaders, the NSA has itself invaded


OK, then. So as “concrete, definitive successes” go, we’ve got (1) Section 702 surveillance achieving the prosecution of a $10,000 donation to al-Shabab in Somalia from someone in San Diego, and (2) under Section 215, the prevention of the hacking of 150 gigabytes of data. Does that mean that, to price these out on a per-success cost-benefit basis, we should divide them into a $52 Billion/year cost, or instead spread it over the total cost of eleven years of these electronic surveillance programs?
It seems only right to exclude from this analysis the “non-US plots” the NSA would prefer to list, since those obviously benefit foreign nations who doubtless asked for this help and certainly are contributing their share to its expense (right?), and also omit the “plots” we actually dreamed up ourselves and incited as well as the plots foiled by other investigative efforts like being alert or having passengers in the nearby seats on the plane. I wouldn’t even suggest a reduction or discount for the plots not detected at all (Boston Marathon?).
Freedom is not free — that’s for sure if you try to do the math on these programs.
Sorry, that’s backwards — 702 is the data, 215 was al-Shabab. Still only counts as two….
i’m glad to see your analyses more widely distributed with today’s guardian article.
its not a critcism but rather a point of personal prejudice that it really bothers me that making the internet accessible to all americans, faster with more capacity, more secure from nuisance and harmful viruses, trojans, rootkits, personal info theft, etc has not become a part of the obama admin’s approach to the “nsa’s future debate (to the extent there even is one).
the internet is THE communications channel of the future for both individuals, businesses, and government. it is now a sort-of private charity. it is also phenomenally insecure. nor does it seem to have a plan for growth and development. further, in at least the part of the u.s. where i live, there is zero competition to increase services and reduce costs for consumers. the internet is a at&t, verizon, comcast monoploly.
the nsa has set the terms of the debate by its conduct. that needs to change. the debate needs to broaden out from illegality, privacy, overreach and incompetence to include internet access, internet development, and internet security for citizens and institutions.