As I noted several weeks ago, Jeffrey Sterling challenged his conviction based on the absence of evidence actually implicating him in the crime. On Monday, the government responded. And while I expect the government will succeed in defeating Sterling’s challenge I am still struck by some very big problems with their story.
As they did at the trial (especially in closing arguments) they argued that Sterling had knowledge of what they claim was the leak, he had a motive to leak it, and he had the pre-existing relationship with James Risen that would explain that he would go to Risen to leak it. So far so good.
They also argued that because Sterling was the only one favorably treated in Risen’s chapter, Sterling must be a source for Risen, which logically doesn’t hold at all.
But in the filing, the government also returns to its efforts — played out in the indictment, rehearsed briefly as both sides tried to make narratological arguments neither was equipped to make, introduced at the opening, but largely dropped during the trial — to a claim that Sterling lied to both the Senate Intelligence Committee and Risen to get them to show interest in his story. Not just that, but they claim Sterling told the same lies to both. This is where their argument starts to fall apart, and fall apart in ways that identify more problems for their argument.
He not only possessed the facts about Classified Program No. 1, he had a motive to spin them in a way that would do maximum damage to the agency. That is exactly what the evidence reflects. Risen’s spin on the program—i.e., that it was botched and risked enabling the Iranian nuclear program—is the same spin the defendant used when he met with Vicki Divoll and Donald Stone from the Senate Select Committee on Intelligence (SSCI) on March 5, 2003, GX 101, the day after he filed his second lawsuit, GX 99, and about a month after his last settlement offer expired. GX 96. Indeed, the only time anyone expressed the concerns Risen parroted in Chapter 9 was when Sterling went to SSCI.
This is wrong on two counts.
First, what Sterling told SSCI was not spin. Here’s what the SSCI report (Exhibit 101) — which Donald Stone claims he wrote on Bill Duhnke’s direction after he informed Stone of an investigation (in which Duhnke was then the prime suspect, for some unknown reason) — says Sterling said.
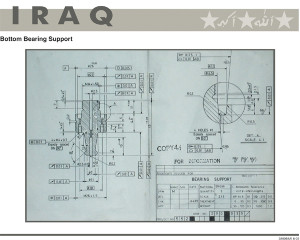
The operation entailed a CIA asset providing Iran with faulty plans for a Russian based nuclear fire set. Although the plans had been modified by the National Laboratories, Mr. Sterling feared they were insufficiently flawed to prevent a Russian scientist hired by the Iranians from identifying and correcting the mistakes. His concern was based on the fact that the CIA asset recognized the plan’s flaws almost immediately after being shown them. He would have preferred to string the operation out by giving pieces of the plan out over time. In the end, the entire plan was turned over to the Iranians without any means for further follow up. However, CIA supposedly deemed the operation a success. Mr. Sterling fears the CIA gave the Iranians too much information that they can either use themselves or sell to someone else.
And here’s what Stone told the FBI Sterling had told them, but which (in his memo written after he knew of the investigation) he didn’t include in the investigation.
Which is why the details Stone provided the FBI, which would have been captured in his notes but which didn’t show up in the report, are so interesting. First, Sterling said that “they did the equivalent of throwing it over a fence,” an admission of how shoddy the pass-off of the blueprints was. Then, that one of CIA’s two assets involved “got cold feet,” an admission that Merlin almost backed out just before the trip to Vienna. And that one asset (it actually sounds like Stone might have meant Human Asset 2, the other Russian, which the records actually support) “recognized the plans were faulty.”
Every single one of these details are true, not spin. Not only did Merlin immediately say the plans “would not work” (and in testimony said the real plan would have been “100 times more complicated than it was shown in drawing and the schematics”), but the other Russian involved — the guy who gave the plans to the CIA in the first place — apparently had problems with them as well. The National Lab got the plans to work in 3 months (not 5, as Walter C testified under oath), at least according to CIA’s own cables. And the entire operation was premised on the assumption that Iran had access to Russian engineers.
In addition, Merlin did get cold feet, as extensively documented by CIA cables, and confirmed — once he presented it as protecting his own family — by the Russian’s testimony.
But the most important evidence from Sterling’s report to the SSCI is that he complained that “the entire plan was turned over to the Iranians without any means for further follow up,” largely because “they did the equivalent of throwing it over a fence.” Not only are those claims absolutely true — as confirmed by both Bob S and Merlin’s sworn testimony at the trial — but they are one of the two key points of his whistleblower complaint to Congress. Not only did CIA give Iran a nuclear blueprint. But they did so, Sterling worried (according to the SSCI), in such a way as to make further follow-up and intelligence gathering almost impossible. He would have rather strung out the operation so as to collect intelligence.
And that’s important, because that complaint doesn’t show up in Risen’s book with the details that substantiate it, appearing only as “the CIA also gave the blueprints to the Iranians without any certain way of monitoring their use by Iranian scientists.”
Indeed, there are details in Risen’s book that are inconsistent with both the real basis of Sterling’s worry and the facts as presented by CIA cables, Bob S, and Merlin, though not with the instructions originally given to Merlin. The book repeats the instructions that Merlin was not supposed to hide that he lived in the US.
The Russian was also told not to try to hide the fact that he now lived in the United States.
And it includes the final line of the letter it claims Merlin left, indicating his contact information was on the next page.
My contact info on next page.
The thing is, probably because of Bob S’ suppression of the actual details of the operation as executed — Bob S’ false spin, not Sterling’s! — the CIA documents included these details, but they are inaccurate, per both Bob S and Merlin. Merlin did everything he could to ensure any tie with the US was hidden. “Nobody likes United States in the world,” Merlin testified, “I’m not stupid. I can put in danger my family.” And he had been doing so for almost a year by the time of the operation. And according to Merlin — and Bob S claims he knew this at the time — Merlin did not provide the contact information the Iranians would need to contact him.
In other words, a key part of Sterling’s concern, that as Merlin executed the operation, he had left the Iranians no way to contact him and therefore largely prevented any follow-up contact, doesn’t show up in Risen’s book. The “spin” is not the same, and in fact Risen’s version misstates a key concern Sterling shared with SSCI.
If Sterling had wanted to get Risen to publish the same story he told to SSCI, he surely would have foregrounded that Merlin refused to do as he told with respect to leaving his contact information.
And that’s important for two reasons.
First, as I noted, FBI proved unable ultimately to find the version of the letter Merlin left (or the letter that appears in Risen’s book, which is almost certainly a different thing). And FBI proved unbelievably incurious about why Risen was quoting from a report on Merlin’s trip that Bob S claims never existed, a report that included the details that Bob S suppressed in his own reporting of the operation.
Here’s how the government’s filing deals with their inability to produce the actual letter.
The evidence at trial established that over a period of months, the defendant, Robert S., and Merlin worked on drafting and editing a letter for Merlin to provide to the Iranians. See, e.g., DE 435 at 22-23. The document went through multiple drafts. On January 12, 2000, the defendant sent a cable containing the then-current version of the letter. GX 35. Two days later, on January 14, 2000, Robert S. responded in another cable, requesting certain changes, including that the letter make explicit that the schematics were being provided for “free.” GX 36 at 1. There were no additional changes reflected in any cable traffic. The version of the letter that appears in Chapter 9 is the January 12, 2000, formulation, with Robert S.’s suggested changes from January 14 incorporated into the document—i.e., the final version. Compare GX 35 at 2, and GX 36 at 102, with GX 132 at 13-14
This is false. As I laid out, not only did Bob S’ instructions include agreement that the letter should be stripped of “puffery” that it retains in the Risen version, but Bob S himself testified that the letter that appeared in the book was not the final letter either.
In response on January 14, 2000, Bob S wrote (Exhibit 36),
We agree with [Sterling’s] comments that the verbiage needs to be tightened up still further to make sure the Iranians understand what he has and on what terms. He should say explicitly that he is offering the schematic and associated parts list free to prove that he can provide further information, and acknowledge that what he is providing initially is incomplete. There should be a very clear message that he expects to be paid for the rest of the details they will need if they want to build the device.
[snip]
Each iteration of his draft letter is better than the previous one, so [Sterling]‘s patience seems to be paying off. It is worth our while to take the extra time to make sure he finally gets it just right, since the letters will have to do much of the work for us with the target.
Now, given Merlin’s payment strike at the following two meetings, it is possible CIA never got around to making the changes Bob S wanted. The fact that Bob S, not Sterling, wrote the cables from those meetings means we would never know, because unlike Sterling, Bob S never included the text of correspondence in cables he wrote (as I laid out here). But Bob S — who ran both the remaining meetings before the Vienna trip with Merlin — clearly wanted changes. And while the letter appearing in Risen’s book retains what Sterling called Merlin’s “puffery” language, it does reflect two of the changes Bob S asked for: reiteration that this package was meant as an assessment package, and an indication Merlin had emailed IS2 to alert him to the package (though see my questions about whether he really did in the update to this post).
In his testimony, Bob S claimed that what appeared in the book was the “nearly final draft,” explaining that the reference to Merlin getting paid was “sharpened” still further after the version that appears in the book. If true, given the way the final meetings worked out, Bob S may have been the only one who would know that.
In spite of the abundant evidence that Bob S was more likely to have these late iteration letters than Sterling, the government goes further to argue — as they prevented Sterling from arguing at trial — that he probably didn’t do his job and that’s why there isn’t a final version of the letter.
It would be entirely reasonable for a jury to conclude that an individual, who was terminated for failure to perform his assigned duties, GX 62 at 1, might also fail to properly document all of his contacts with an asset.
This would require that Merlin and Sterling made changes Bob S knew about, did not document them verbatim as was Sterling’s (but not Bob S’) consistent practice, and Bob S never noticed. Indeed, Bob S insisted at trial that the CIA writes everything down (in contradiction to the evidence that, while Sterling did, he did not). It’s just not possible.
And, as I mentioned, the motion never deals with — as the entire trial didn’t either — the report which Merlin and Bob S say never existed but gets quoted extensively in Risen’s book, which included information which Bob S suppressed in official CIA communications but admits are factually correct.
But the mistranslation of Sterling’s concern is important for another reason: the errors in Risen’s book, errors which Sterling not only knew to be errors (per trial evidence), but errors that make no sense given FBI’s claimed spin. The big one — the one that pissed Merlin off the most — was the claim he was a defector (I’m less convinced that Risen’s claim that CIA helped Merlin get citizenship is entirely false, because there’s reason to believe they did accelerate his green card and treat it differently to allow him to do the Vienna trip).
That is, while there are details that (according to FBI) only Sterling, Bob S, and Merlin knew that weren’t documented (though the majority of those were in the report they didn’t look for), there are also a slew of details that show someone ill-informed, but not in a way that matches’ Sterling’s actual or purported concerns, was talking to Risen.
All this is probably moot. The government will succeed with this motion on evidentiary grounds and the interesting venue argument will be revisited in the Appeals Court.
But it is worth noting that the government’s narrative, even as laid out in a careful motion, continues to make no sense.