Just Before Obama Weighs in on the Russian Hack, John Brennan Tells Everyone What He Says Others Said
At 2:20, WaPo published a story basically saying, “Anonymous source says CIA Director Wrote a Letter Claiming FBI Director and Director of National Intelligence Agree with Him,” but you wouldn’t know that from the headline.
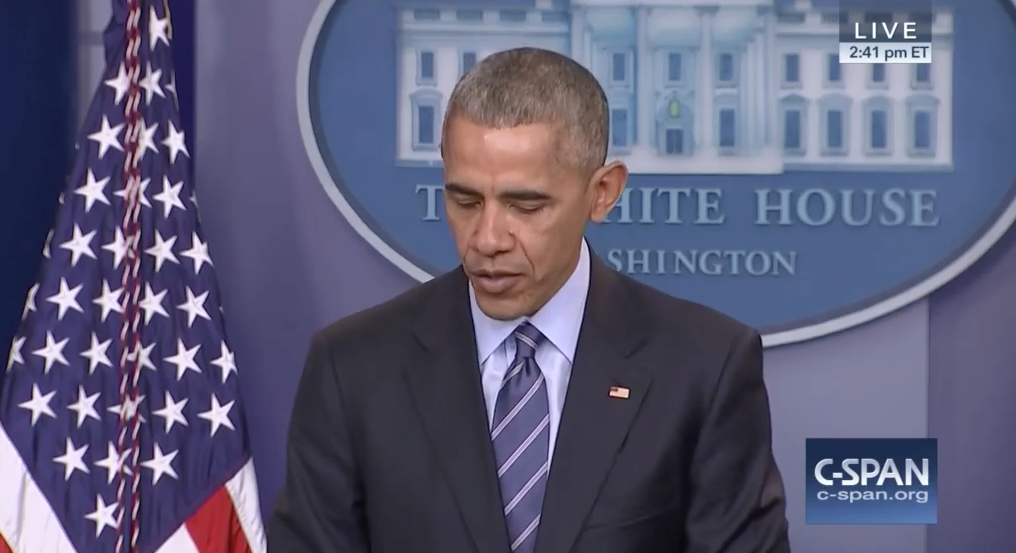
At 2:40, President Obama entered the White House briefing room to give his last press conference of the year, which was scheduled to start at 2:15. Everyone anticipated, correctly, the presser would be dominated by questions about Russia’s role in the election.
So:
2:15: scheduled start for the President to comment on Russia’s hacking and what the intelligence says.
2:20: WaPo tells you what an anonymous leaker says CIA’s Director says FBI’s Director and Director of National Intelligence say, which differs somewhat from what Obama says.
2:40: Obama walks to the podium as, presumably, everyone waiting is reading WaPo’s scoop.
Who says only Vladimir Putin is good at information ops?
Mind you, once you get into the body of the article, there’s a significant difference between what WaPo says CIA says today and what its anonymous sources said CIA said a week ago, the last time it stomped on Obama’s efforts to introduce some deliberation into the claims about Russia’s hacks. Last week, WaPo said the CIA view was this:
“It is the assessment of the intelligence community that Russia’s goal here was to favor one candidate over the other, to help Trump get elected,” said a senior U.S. official briefed on an intelligence presentation made to U.S. senators. “That’s the consensus view.”
[snip]
The CIA shared its latest assessment with key senators in a closed-door briefing on Capitol Hill last week, in which agency officials cited a growing body of intelligence from multiple sources. Agency briefers told the senators it was now “quite clear” that electing Trump was Russia’s goal, according to the officials, who spoke on the condition of anonymity to discuss intelligence matters. [my emphasis]
Goal, singular.
Here’s what the lead says in today’s article.
FBI Director James B. Comey and Director of National Intelligence James R. Clapper Jr. are in agreement with a CIA assessment that Russia intervened in the 2016 election in part to help Donald Trump win the presidency, according to U.S. officials.
With this further elaboration below.
The CIA shared its latest assessment with key senators in a closed-door briefing on Capitol Hill about two weeks ago in which agency officials cited a growing body of intelligence from multiple sources. Specifically, CIA briefers told the senators it was now “quite clear” that electing Trump was one of Russia’s goals, according to the officials, who spoke on the condition of anonymity to discuss intelligence matters.
CIA and FBI officials do not think Russia had a “single purpose” by intervening during the presidential campaign. In addition to helping Trump, intelligence officials have told lawmakers that Moscow’s other goal included undermining confidence in the U.S. electoral system. [my emphasis]
WaPo still makes no mention of the most obvious goal, that Russia hacked Hillary to retaliate for real and perceived slights covertly carried out by Hillary and CIA, something that Hillary claimed just before the WaPo story and the Obama presser.
In any case, if you look at CNN’s far more sober version of this, it appears that there is still some difference in emphasis about whether Russia was trying to elect Trump (and Brennan’s statement appears not to lay out what the consensus view is).
The nuance lay in a stronger view by the CIA that the hacking was intended to help elect Trump, and the CIA leans more strongly in that view than the FBI does.
Ah well, in the waning days of a great empire, who cares about deference to the outgoing President?
Update: This exchange between Obama and Martha Raddatz most directly addresses what Obama wants to say about the hack (elsewhere he says there was no evidence Russia hacked any polls).
Q Mr. President, I want to talk about Vladimir Putin again. Just to be clear, do you believe Vladimir Putin himself authorized the hack? And do you believe he authorized that to help Donald Trump? And on the intelligence, one of the things Donald Trump cites is Saddam Hussein and the weapons of mass destruction, and that they were never found. Can you say, unequivocally, that this was not China, that this was not a 400-pound guy sitting on his bed, as Donald Trump says? And do these types of tweets and kinds of statements from Donald Trump embolden the Russians?
THE PRESIDENT: When the report comes out, before I leave office, that will have drawn together all the threads. And so I don’t want to step on their work ahead of time.
What I can tell you is that the intelligence that I have seen gives me great confidence in their assessment that the Russians carried out this hack.
Q Which hack?
THE PRESIDENT: The hack of the DNC and the hack of John Podesta.
Now, the — but again, I think this is exactly why I want the report out, so that everybody can review it. And this has been briefed, and the evidence in closed session has been provided on a bipartisan basis — not just to me, it’s been provided to the leaders of the House and the Senate, and the chairman and ranking members of the relevant committees. And I think that what you’ve already seen is, at least some of the folks who have seen the evidence don’t dispute, I think, the basic assessment that the Russians carried this out.
Q But specifically, can you not say that —
THE PRESIDENT: Well, Martha, I think what I want to make sure of is that I give the intelligence community the chance to gather all the information. But I’d make a larger point, which is, not much happens in Russia without Vladimir Putin. This is a pretty hierarchical operation. Last I checked, there’s not a lot of debate and democratic deliberation, particularly when it comes to policies directed at the United States.
We have said, and I will confirm, that this happened at the highest levels of the Russian government. And I will let you make that determination as to whether there are high-level Russian officials who go off rogue and decide to tamper with the U.S. election process without Vladimir Putin knowing about it.
Q So I wouldn’t be wrong in saying the President thinks Vladimir Putin authorized the hack?
THE PRESIDENT: Martha, I’ve given you what I’m going to give you.