I started unpacking this Maggie Haberman story yesterday morning.
It was an unusual story. Love or hate Maggie, she’s a really hard working journalist. But her forté is working phones, not documents.
Nevertheless, Maggie set out alone, without the involvement of an expert on documents generally or the FEC specifically (someone like David Fahrenthold) to explain why Jack Smith’s prosecutors are subpoenaing vendors of Trump’s Save America PAC.
The Justice Department has been subpoenaing documents from vendors paid by the PAC, including law firms, in an effort to determine what they were being paid for.
It seemed to be a follow-up to this story, which, by suggesting that JP Cooney had only joined the team with Smith’s hiring, falsely implied that DOJ had only started pursuing this angle after his appointment.
Three of his first hires — J.P. Cooney, Raymond Hulser and David Harbach — were trusted colleagues during Mr. Smith’s earlier stints in the department. Thomas P. Windom, a former federal prosecutor in Maryland who had been tapped in late 2021 by Attorney General Merrick B. Garland’s aides to oversee major elements of the Jan. 6 inquiry, remains part of the leadership team, according to several people familiar with the situation.
In addition to the documents and Jan. 6 investigations, Mr. Smith appears to be pursuing an offshoot of the Jan. 6 case, examining Save America, a pro-Trump political action committee, through which Mr. Trump raised millions of dollars with his false claims of election fraud. That investigation includes looking into how and why the committee’s vendors were paid.
In December, CNN reported that Cooney had been following the money for a year by that point, and even the NYT noted overt signs of that prong in September.
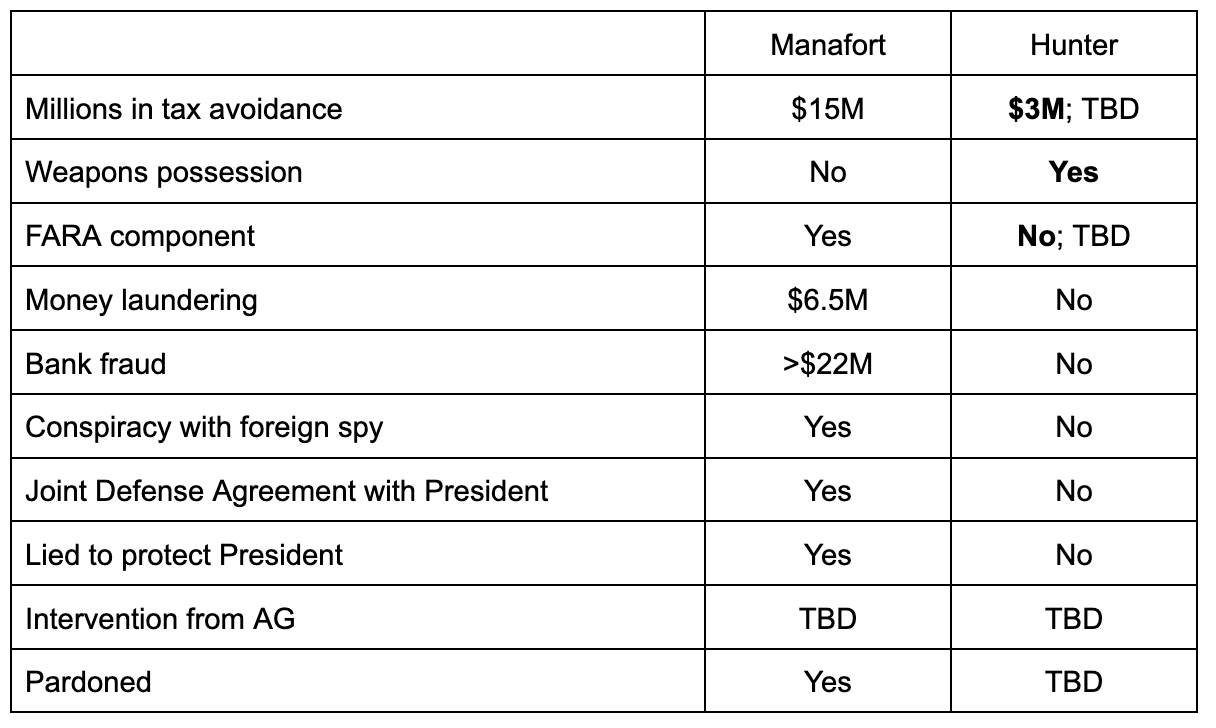
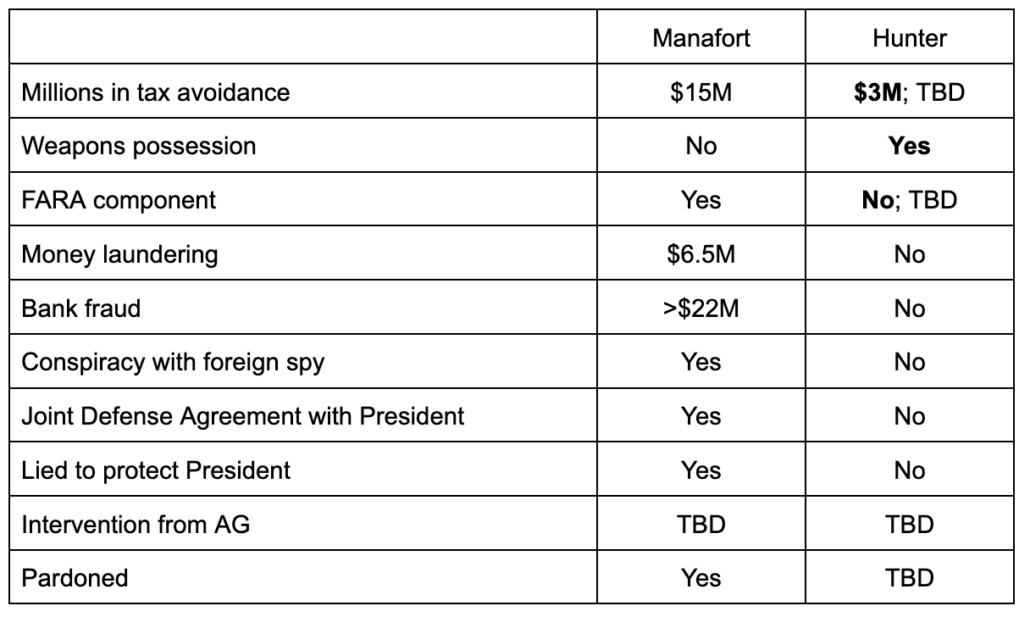
That earlier story nodded towards the same thing that this Daily Beast story, the January 6 Committee Report appendix on following the money, and this Campaign Legal Center complaint (the latter, focused on the 2020 campaign) did: Trump has apparently been treating campaign fundraising like a money laundering vehicle.
Go figure.
But Maggie, writing on her own, focuses instead on prospective crimes: the possibility that continuing to pay legal bills out of money raised starting in 2020 would be a different campaign finance violation.
Some of the $16 million appears to have been for lawyers representing witnesses in investigations related to Mr. Trump’s efforts to cling to power. But the majority of it — about $10 million — went to firms directly representing Mr. Trump in a string of investigations and lawsuits, including some related to his company, the filings showed.
Back in November, CLC did a report noting that Trump was doing that more generally, not just with lawyers.
All that’s not actually why I was interested in the story, but if you want an accounting of how much PAC money Trump is spending on legal services, Daily Beast’s tally includes the money spent by the MAGA PAC as well, adding up to $29.1 million since leaving office.
After I started unpacking Maggie’s story, I got distracted with the possibility that DOJ will tie Trump and Rudy Giuliani and John Eastman directly to the almost-murder of Michael Fanone. So, in the interim, Maggie broke the news that Smith’s prosecutors had subpoenaed Jared and Ivanka.
That story, written with Mike Schmidt, is exceptional only for the fact that they managed to avoid most of the hype about “aggressive steps” that peppers most reporting on Jack Smith. It pointed to things like the morning Oval Office meeting (Ivanka’s response to which her Chief of Staff Julie Radford was likely already questioned about, since — as the J6C Report noted explicitly — Radford was far more candid about it than Ivanka) and efforts to get Trump to call off his mob as likely topics of questioning.
Smith no doubt wants to get Jared and Ivanka’s stories about such topics locked in. Given questions about their candor before J6C, too, Smith will likely also give them an opportunity to revise their prior answers so they more closely match known facts.
Back to Maggie’s solo endeavor to read FEC filings.
There are two reasons I was interested in the story. First, having looked at FEC filings, Maggie seems to have discovered that the $195,000 in services that Boris Epshteyn billed to Save America PAC last year were not for legal services, but instead strategic consulting.
Another $1.3 million went to Silverman Thompson Slutkin and White, the firm of Evan Corcoran, a lawyer who began working with Mr. Trump last spring. Mr. Corcoran was brought into Mr. Trump’s orbit by Boris Epshteyn, a strategist who has played a coordinating role with some of the lawyers in cases involving Mr. Trump, as the investigation related to the Mar-a-Lago documents was heating up. (Mr. Epshteyn’s company was paid $195,000, but for broader strategic consulting, not legal consulting specifically.)
This is an important point, but one Maggie did not highlight (nor issue corrections on past stories). For the entirety of the time that Epshteyn was quarterbacking Trump’s response to the stolen documents probe, someone in his immediate vicinity has been telling reporters that he was playing a legal function, all the while billing Trump for the same old strategic consulting his firm, Georgetown Advisory, normally provides (though the two payments the campaign made to Epshteyn after Trump formalized his candidacy, totalling $30,000, were filed under “communications and legal consulting”).
NYT has, in various stories including Maggie in the byline, described Epshteyn’s role in the stolen documents case as “an in-house counsel who helps coordinate Mr. Trump’s legal efforts,” “in-house counsel for the former president who has become one of his most trusted advisers,” and “who has played a central role in coordinating lawyers on several of the investigations involving Mr. Trump.” Another even describes that Epshteyn “act[ed] as [a] lawyer [] for the Trump campaign.” The other day, Maggie described his role instead as “broader strategic consulting.”
All the time that NYT was describing Epshteyn as playing a legal role — and NYT is in no way alone in this — he was telling the Feds he wasn’t playing a legal function, he was instead playing a strategic consulting one. Many if not most of these stories also post-date the time, in September, when the FBI seized Epshteyn’s phone, which would give him a really good reason to try to claim to be a lawyer and not a political consultant.
DOJ is more likely to take FEC’s word on this issue than claims Epshteyn made to the press after his phone seizure.
Like I said, virtually every media outlet seems to be repeating the claim that Epshteyn has been playing a legal, not political role. But there’s one Maggie story, in particular, where the question of Epshteyn’s role is central: This story, quoting Eric Herschmann calling Epshteyn (and Evan Corcoran) idiots, a habit that made Herschmann a star witness for the January 6 Committee. Herschmann’s glee about calling Sidney Powell, Jenna Ellis, John Eastman, and now Epshteyn and Corcoran idiots always distracted from sketchier aspects of Herschmann’s behavior, such as Keith Kellogg’s puzzlement about why a lawyer sat in the Oval Office while Trump ordered Mike Pence to break the law and said nothing.
Anyway, this Maggie story focusing on Epshteyn’s role not only called him an idiot, but also insinuated he was witness tampering.
To the extent anyone is regarded as a quarterback of the documents and Jan. 6-related legal teams, it is Boris Epshteyn, a former campaign adviser and a graduate of the Georgetown University law school. Some aides tried to block his calls to Mr. Trump in 2020, according to former White House officials, but Mr. Epshteyn now works as an in-house counsel to Mr. Trump and speaks with him several times a day.
Mr. Epshteyn played a key role coordinating efforts by a group of lawyers for and political allies of Mr. Trump immediately after the 2020 election to prevent Joseph R. Biden Jr. from becoming president. Because of that role, he has been asked to testify in the state investigation in Georgia into the efforts to reverse Mr. Biden’s victory there.
Mr. Epshteyn’s phone was seized by the F.B.I. last week as part of the broad federal criminal inquiry into the attempts to overturn the election results and the Jan. 6 assault on the Capitol.
[snip]
In his emails to Mr. Corcoran and Mr. Rowley, Mr. Herschmann — a prominent witness for the House select committee on Jan. 6 and what led to it — invoked Mr. Corcoran’s defense of Mr. Bannon and argued pointedly that case law about executive privilege did not reflect what Mr. Corcoran believed it did.
Mr. Herschmann made clear in the emails that absent a court order precluding a witness from answering questions on the basis of executive privilege, which he had repeatedly implored them to seek, he would be forced to testify.
“I certainly am not relying on any legal analysis from either of you or Boris who — to be clear — I think is an idiot,” Mr. Herschmann wrote in a different email. “When I questioned Boris’s legal experience to work on challenging a presidential election since he appeared to have none — challenges that resulted in multiple court failures — he boasted that he was ‘just having fun,’ while also taking selfies and posting pictures online of his escapades.”
[snip]
In language that mirrored the federal statute against witness tampering, Mr. Herschmann told Mr. Corcoran that Mr. Epshteyn, himself under subpoena in Georgia, “should not in any way be involved in trying to influence, delay or prevent my testimony.”
“He is not in a position or qualified to opine on any of these issues,” Mr. Herschmann said.
Mr. Epshteyn declined to respond to a request for comment. [my emphasis]
The story ends by reporting that Herschmann’s, “testimony was postponed.”
I’m not aware of any report that describes Herschmann has been called back to testify.
The story is dated September 16, 2022.
Two days earlier, Cassidy Hutchinson had testified to the January 6 Committee (after already beginning to cooperate with DOJ) that after she testified on May 17 that Herschmann was present for a conversation about Trump saying that “Hang Mike Pence” chants were justified, her then-lawyer Stefan Passantino seemingly contacted Herschmann who then called Hutchinson and told her, “I didn’t know that you remembered so much.”
Ms. Cheney. When Stefan said “I’ll talk to some people,” do you know who he was referring to?
Ms. Hutchinson. I didn’t ask. assume it was the same entourage of people that he had been conferring with for the past few weeks.
You know, I had also received a call from Eric Herschmann, I believe on Friday, May 20th. I believe it was Friday, May 20th. It was, because this was after the interview.
And Eric called me that evening, and I just apologized. And he was like, you know, “I didn’t know that you remembered so much, Cassidy. Mark [Meadows] really put you in bad positions. I’m really sorry that he didn’t take care of you better. You never should’ve had to testify to any of that. That’s all of our jobs. I don’t know why they didn’t ask us, they asked you instead.”
And I was just like, “Look, Eric like, it is what it is.” And he kind of talked for — it was probably a 30-minute conversation.
In the same J6C appearance two days before that Maggie story painting Ephsteyn as a witness tamperer, Hutchinson told the committee that she suspected that Passantino had spoken to Maggie about her testimony, something that, if true, would have had the effect of sharing her testimony with other witnesses without appearing to obstruct the investigation. She also described Alex Cannon to be involved in the outreach to Maggie.
The next day, September 15, Hutchinson provided the committee more detail about Passantino’s alleged efforts to share her testimony with Herschmann and others. Passantino told her to call Trump’s lawyer, Justin Clark, as well as Alex Cannon and Eric Herschmann, Hutchinson told the committee on September 15.
The day after my third interview with the committee, on Wednesday, May 18th, Stefan let me know that I — he spoke with Justin Clark, Alex Cannon, and Eric Herschmann and suggested that I call — that I have a call with all three of them.
I reached out to initiate the call with Alex Cannon and Justin Clark per Stefan’s instruction. And the that Friday, May 20th, received a call on Signal from Eric Herschmann.
So on September 14, Hutchinson told J6C about behavior involving Herschmann resembling witness tampering, including behavior involving Maggie Haberman! On September 15, Hutchinson told J6C about behavior involving Herschmann resembling witness tampering. And on September 16, Maggie Haberman quoted Herschmann blaming Epshteyn for any witness tampering.
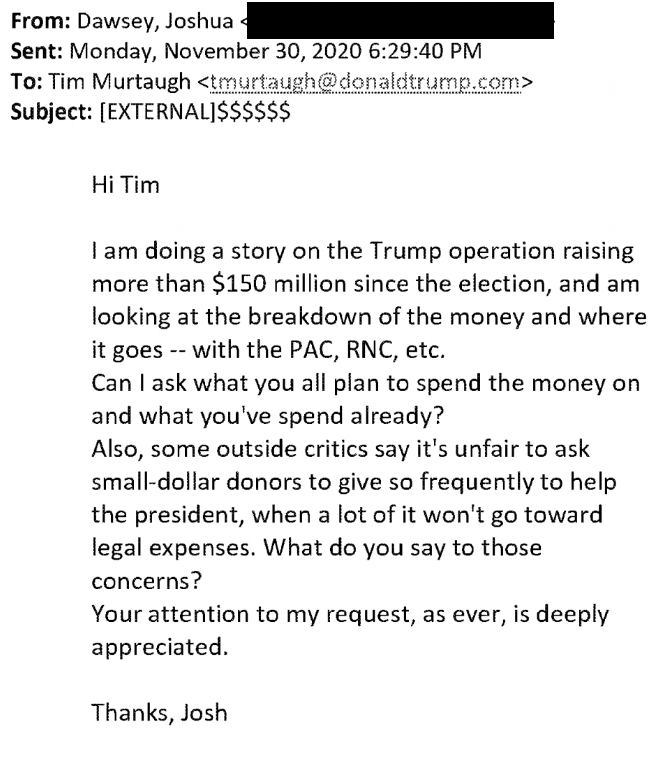
All that background is why I find the way Maggie ended her foray into campaign finance journalism so interesting. She quotes anonymous sources — not the public J6C transcripts showing that Passantino and Alex Cannon were sourcing her earlier reporting on this — attributing Hutchinson’s testimony as the genesis of this focus on paying law firms.
The questions of which lawyers and vendors have been paid, and for what, intensified after the House select committee investigating Mr. Trump’s efforts to cling to power told the Justice Department that it had evidence that a lawyer representing a witness had tried to coach her testimony in ways that would be favorable to Mr. Trump. The witness in question was later identified by people familiar with the committee’s work as Cassidy Hutchinson, a former White House aide.
Her lawyer at the time, Stefan Passantino, was a former White House deputy counsel under Mr. Trump and was paid through Save America.
The reason I’m interested in this is because the point of Passantino’s alleged efforts to coach Hutchinson’s testimony was not, primarily, to protect Trump. According to Hutchinson’s testimony, at least, it was to protect Eric Herschmann, someone who has had tremendous success (like his close associate Jared Kushner) laundering his reputation through Maggie Haberman.
Ms. Hutchinson. ~ You previously asked about individuals he had raised with me. In my conversation with him earlier that afternoon, when I [sic] asking him about the engagement letter, I did also ask Stefan if he was representing any other January 6th clients. And he had said, “No one that I believe that you would have any conflicts with.”
And I said, “Would you mind letting me know?” Now, again, to this day, I still don’t know if that’s really a kosher question to ask an attorney, if they can share their clients with me, but I wanted to make sure that there actually weren’t any conflicts, because I didn’t have anything in writing.
He wouldn’t tell me anybody he was representing before the January 6th Committee, but he did tell me that he had previously represented Eric Herschmann and Jared Kushner and Ivanka Trump in unrelated matters.
And in that same conversation, he said, “So if you have any conversations with any of them, especially Eric Herschmann, we want to really work to protect Eric Herschmann.”
And I remember saying sarcastically to him, “Eric can handle himself. Eric has his own resources. Why do I have to protect Eric?” He said, “No, no, no. Like, just to keep everything straight, like, we want to protect Eric with all of this.”
Ms. Cheney. Did he explain what he meant?
Ms. Hutchinson. No. And, to be honest, I didn’t ask. I didn’t have anything with Eric anyway that I felt that I had to protect. And I say that because, at the time of being back in Trump world — this is where I look back and regret some of this, but — like, I did feel a need to protect certain people. But with somebody like Eric, I didn’t feel that need, I didn’t find it necessary. didn’t — I didn’t think that Eric did anything wrong at the time.
Ms. Cheney. Did it have something to do with NARA?
Ms. Hutchinson. He never really explained to me what it was exactly that we wanted to protect Eric on. I sort of erred on the side of: Maybe he just represents Eric in ongoing litigation, whether it’s financial disclosures or whatever it might be.
And, again, I just didn’t prod too much on that either, because, you know, I was under the impression that Eric helped set me up with Stefan, so I didn’t — I was worried that Stefan would then go back-channel to Eric and — this is my very paranoid brain at the time, but I was worried that if I, you know, pushed this subject a little too much, that he would then go back to Eric Herschmann and say, “Cassidy asked a lot of questions about you, like, why she needs to protect you.” So just didn’t really press the subject too much on that.
And as Hutchinson learned somewhat belatedly, Passantino had business ties to Alex Cannon and, possibly, Herschmann.
So I — “I want to make sure that I’m getting the dates right with these things?
He goes, “No, no, no.” He said, “Look, we want to get you in, get you out.
We’re going to downplay your role. You were a secretary. You had an administrative role. Everyone’s on the same page about this. It’s extremely unfair that they’re” “they’re” being the committee – “that the committee is putting you in this position in the first place. You really have nothing to do with any of this. It’s Mark’s fault that you’re even involved in this. We’re completely happy to be taking care of you now. We had no idea that you weren’t being taken care of this last year. So we’re really happy that you reached back out to us. But the less you remember, the better. I don’t think that you should be filling in any calendars or anything.”
[Redacted] When he said a
Ms. Cheney. Go ahead.
[Redacted] So everyone’s on the same page about this, did he explain who he was referring to when he said “everyone”?
Ms. Hutchinson. He didn’t at that moment. Then there are times throughout my working relationship with Stefan where he said similar things that I asked.
Later that day, sort of put together that the “they” he was referring to then were Justin Clark, Alex Cannon, Eric Herschmann. I think that’s — yeah, think that’s all of them.
Ms. Cheney. And how did you put that together?
Ms. Hutchinson. Because he — he had said that — Justin — yeah, Justin Clark. Stefan had told me that — towards the end of the day that because he was involved with Elections, LLC, and tangentially, I guess Trump’s PACs, he had law partners. And unless I was extremely unwilling for him to share, he said it would be natural for him to have to share that information with the people that he works with that are his partners that are involved in Trump world.
That is, Hutchinson testified that Passantino’s alleged effort to coach her testimony was not (necessarily) an effort to protect Trump. It was an effort to protect his business scheme, a business scheme that may have included Herschmann.
In Maggie’s foray into campaign finance journalism, she did not calculate payments to Elections LLC in her discussion of law firms paid by Save America PAC, though it was paid upwards of $400,000 since Trump left office. The last of those payments — for $10,000 — was on December 7, after Trump formalized his 2024 presidential bid. So if Maggie’s right that these payments are illegal, then that $10,000 would be one of the first overt acts in this new criminal exposure.
As it happens, all this ties back to Maggie’s newest story breaking the news of a subpoena to Ivanka and Jared. I’m sure Jack Smith wants to ask Ivanka and Jared about their efforts to get dad to call off his mob.
But he may also want to know why Herschmann — a lawyer whose legal status in the White House remains entirely unexplained — why Herschmann, according to Pat Cipollone’s testimony, told the White House Counsel not to join in that Oval Office meeting where Trump ordered Pence to break the law because “this is family.”
“This is family,” Cipollone said Herschmann told him before he walked in the door. “You don’t need to be here.”
I would imagine that Jack Smith wants to know why, at that moment when Trump prepared to give his Vice President an illegal order, Herschmann was treated as family.
Update: Anna Bower informed me that Epshteyn told the Fulton County Grand Jury that he,
served as a legal, communications, and policy advisor to President Trump’s 2020 re-election campaign; and he continues to serve as legal counsel to President Trump to this day.
He cited NY state’s bar rules to argue that his ethical obligations extend well beyond attorney-client privilege.
In contrast, the client confidences that Mr. Epshteyn is required to safeguard as a New York-licensed attorney pursuant to Rule 1.6 of the New York Rules of Professional Conduct (“NYRPC”)4 reach a broader and less easily identifiable array of communications and information. Like its corollary rule in virtually every U.S. jurisdiction, NYRPC 1.6 provides that “[a] lawyer shall not knowingly reveal confidential information … or use such information to the disadvantage of a client or for the advantage of the lawyer or a third person” absent client consent or “to comply with other law or court order.” NYRPC l.6(a)-(b). The rule defines “Confidential Information” to mean “information gained during or relating to the representation of a client, whatever its source, that is (a) protected by the attorney-client privilege, (b) likely to be embarrassing or detrimental to the client if disclosed, or ( c) information that the client has requested be kept confidential.” NYRPC 1.6(a)(3). The duty to preserve client confidences under Rule 1.6 is much broader that the attorney-client privilege, it includes any information gained during the representation regardless of its nature or source, and it necessarily includes information that is not subject to any other privilege or protection, provided that it is not already generally known in the community.
Epshteyn has always had a far stronger case he was working in a legal role starting in April or May of last year than while he was on the campaign (where he was described by other witnesses, like Jenna Ellis was also described, as playing a PR role).
In public comments from Emily Kohrs, she suggested that Rudy, who was barred in NY still when he represented Trump during the 2020 election, provided thoughtful question by question answers about whether he could answer questions.