In the middle of his explanation for why he believed that Joe Biden had willfully retained classified records pertaining to Afghanistan but that he couldn’t prove that beyond a reasonable doubt, Special Counsel Robert Hur admitted that jurors “who are unwilling to read too much into” what Hur describes as an 8-word utterance would find his case lacking.
But reasonable jurors who are unwilling to read too much into Mr. Biden’s brief aside to Zwonitzer–“I just found all the classified stuff downstairs”–may find a shortage of evidence to establish that Mr. Biden looked through the “Facts First” folder, which is the only folder known to contain national defense information. These jurors would acquit Mr. Biden of willfully retaining national defense information from the “Facts First” folder.
I’m puzzled how this is not a confession that he, Hur, was really reading too much into two file folders the FBI found in a box in Biden’s garage.
Indeed, that’s what two bizarre chapters in his story are, Hur the novelist, spinning a story about this box because, he admitted much earlier, this is the best he’s got.
As explained in Chapter Eleven, the strongest case for criminal charges against Mr. Biden relating to the Afghanistan documents would rest on his retention of the documents at the Virginia home in 2017.
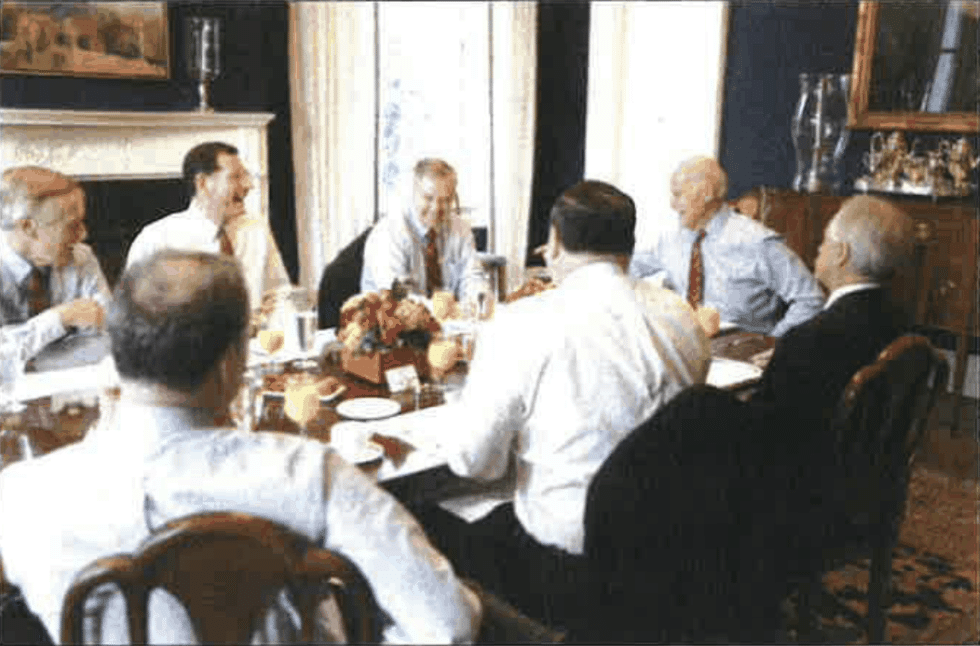
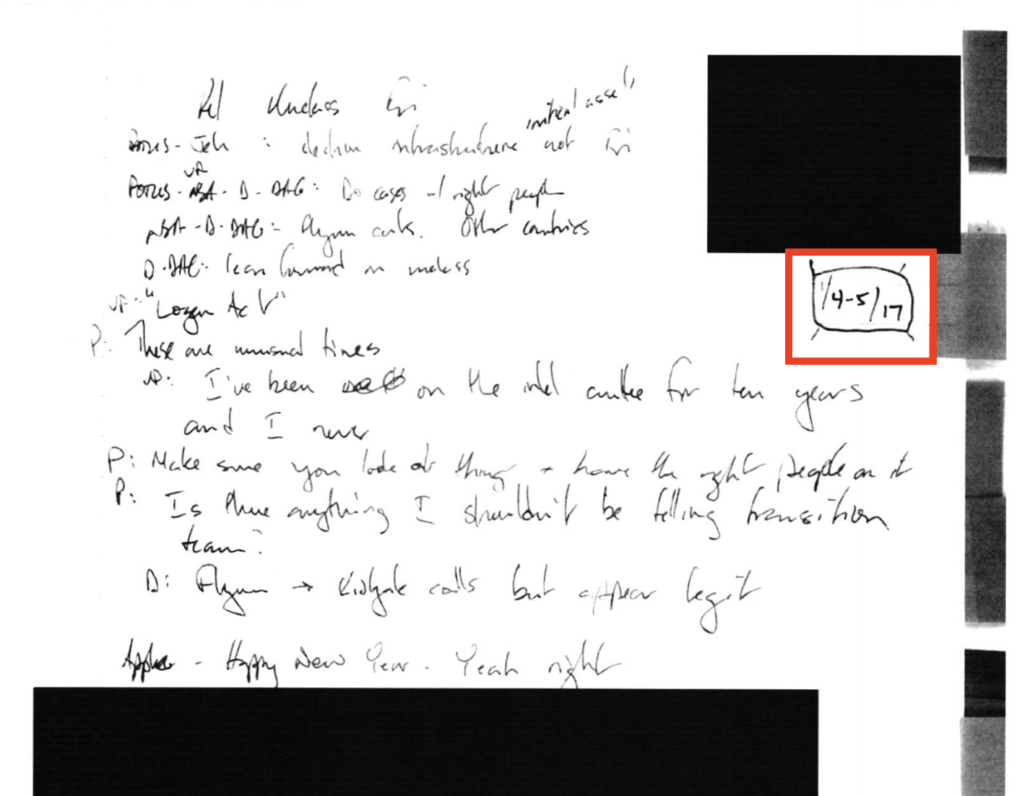
The only other retained documents he even considered charging were Biden’s diaries, which Biden seems to have kept under the Presidential Records Act’s exclusion of diaries from the definition of Presidential Records (though Hur included a picture of Biden taking notes in one of these notebooks during a key meeting in the Situation Room, so that notebook, at least, was a Presidential Record).
(3) The term “personal records” means all documentary materials, or any reasonably segregable portion thereof, of a purely private or nonpublic character which do not relate to or have an effect upon the carrying out of the constitutional, statutory, or other official or ceremonial duties of the President. Such term includes–
(A) diaries, journals, or other personal notes serving as the functional equivalent of a diary or journal which are not prepared or utilized for, or circulated or communicated in the course of, transacting Government business;
To sustain his claim that those notebooks represented willful retention that he couldn’t prove, Hur got in a squabble about the precedent set by Ronald Reagan’s diaries, which similarly included classified information, but which weren’t charged even after they became key evidence in the Iran-Contra investigation. Biden had a precedent to rely on, and so Hur didn’t charge.
So left with only the box in the garage to appease the Republicans, Hur worked backward from this reference in a conversation Biden had with his ghost writer in 2017, the 66-word utterance on which he built a 388-page report:
So this was – I, early on, in ’09-I just found all the classified stuff downstairs-I wrote the President a handwritten 40-page memorandum arguing against deploying additional troops to Iraq-I mean, to Afghanistan-on the grounds that it wouldn’t matter, that the day we left would be like the day before we arrived. And I made the same argument … I wrote that piece 11 or 12 years ago. [my emphasis]
Only Hur didn’t call it a 66-word utterance. He called it an 8-word utterance, repeating those bolded eight words 23 times in the report without mention of the 40-page memorandum that Biden mentioned in the same sentence. Only once did he provide the full context.
Biden’s attorneys argued that given that Biden mentioned it in the very same sentence, it’s more likely that Biden was referring to that memo than two folders of documents found in a box in Biden’s garage.
We believe that an accurate recitation of the evidence on this point would recognize the strong likelihood that the President was referring in the recording to his private handwritten letter to President Obama — the one mentioned on this recording immediately after the eight words that you are focused on — rather than the marked classified Afghanistan documents discovered in the Wilmington garage.
There were drafts of the memo — which Biden wrote over Thanksgiving in 2009 in an attempt to dissuade President Obama from surging more troops into Afghanistan — in the box in the garage, but the FBI found the hand-written memo itself stored elsewhere in Biden’s Wilmington home. It too had classified information in it, but Hur treated it like the diaries it was found in, something Biden wrongly treated as a personal document.
Because these documents on Afghanistan were the only thing he had, Hur went to some length to spin a story that might be consistent with Biden finding those documents in a rental house in Virginia in early 2017 and, just weeks after having sent other marked classified documents back to the Naval Observatory, deciding to keep them.
Part of that involved telling two stories, which narratively collapse events from 2017 with the discovery of the documents in question, to provide motive.
Hur’s first attempt suggested that Biden willfully retained these documents to help write his book, Promise Me, Dad, on which he was working with the ghost writer to whom he mentioned classified documents.
MR. BIDEN’S SECOND BOOK, PROMISE ME, DAD, AND THE DISCOVERY OF CLASSIFIED AFGHANISTAN DOCUMENTS
Like many presidents, Mr. Biden has long viewed himself as a historic figure. Elected to the Senate at age twenty-nine, he considered running for president as early as 1980 and did so in 1988, 2008, and 2020. During his thirty-six years in the Senate, Mr. Biden believed he had built a record in both domestic and foreign affairs that made him worthy of the presidency.
In addition to the notebooks and notecards on which he took notes throughout his vice presidency, Mr. Biden collected papers and artifacts related to noteworthy issues and events in his public life. He used these materials to write memoirs published in 2007 and 2017, to document his legacy, and to cite as evidence that he was a man of presidential timber.
Only, that story didn’t work, because Promise Me, Dad wasn’t about Afghanistan, it was about Beau’s death and Biden’s subsequent decision not to run for President in 2016. And while Hur tried to fudge what surely was the result of a classification review, that book had no classified information in it.
As Biden’s attorneys noted, not only wasn’t Promise Me, Dad about Afghanistan, but Biden never wrote a book — never intended to write a book — about this Afghanistan policy dispute.
Your report erroneously (and repeatedly) makes statements about the value of the marked classified Afghanistan documents to President Biden, such as President Biden had a “strong motive” to keep them and they were an “irreplaceable contemporaneous record” like the notebooks. Report at 203. 231. These statements are contrary to the evidence and the documents themselves. First the President forcefully testified that he “never thought about writing a book about the 2009 Afghanistan policy review. Tr., Day II at 22. Thus, the President had no need to retain the documents for that purpose.
So Hur tried again in the following chapter. This time his story — one relying primarily on books other people wrote — Obama, Stan McChrystal, and Robert Gates, with only Ron Klain backing it with witness testimony — was that Biden needed the documents for vindication, when Afghanistan turned into America’s Vietnam. Secret vindication, I guess, given that Biden didn’t use this in the 2020 election.
To fully appreciate Mr. Biden’s references to Afghanistan in his conversation with Zwonitzer on February 16. 2017, it is helpful to understand Mr. Biden’s place in the fraught debate about American policy in Afghanistan in the early days of the Obama administration.
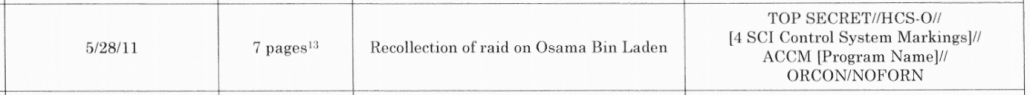
In that debate. Mr. Biden played a conspicuous role. He strongly opposed the military’s effort to send large numbers of U.S. troops to Afghanistan, and this opposition culminated in the lengthy handwritten memo Mr. Biden sent President Obama over the Thanksgiving holiday in 2009. By 2017, Mr. Biden believed his judgment as reflected in the memo had been vindicated by history. Years later, in December 2022 and January 2023. FBI agents found the handwritten Thanksgiving memo and marked classified documents containing his advice to President Obama in Mr. Biden’s Delaware home.
This is a closing argument. This language is wildly inappropriate in a declination memo, because Hur didn’t find the evidence to back this story!
Worse still, it’s stupid. Because all Biden needed for vindication was that 40-page memo, the one he mentioned in the very same sentence as he mentioned the classified documents. The one stored inside the house, not in a discarded box in the garage. The one he never used during the 2020 election.
But Hur was undeterred by a stupid motive argument.
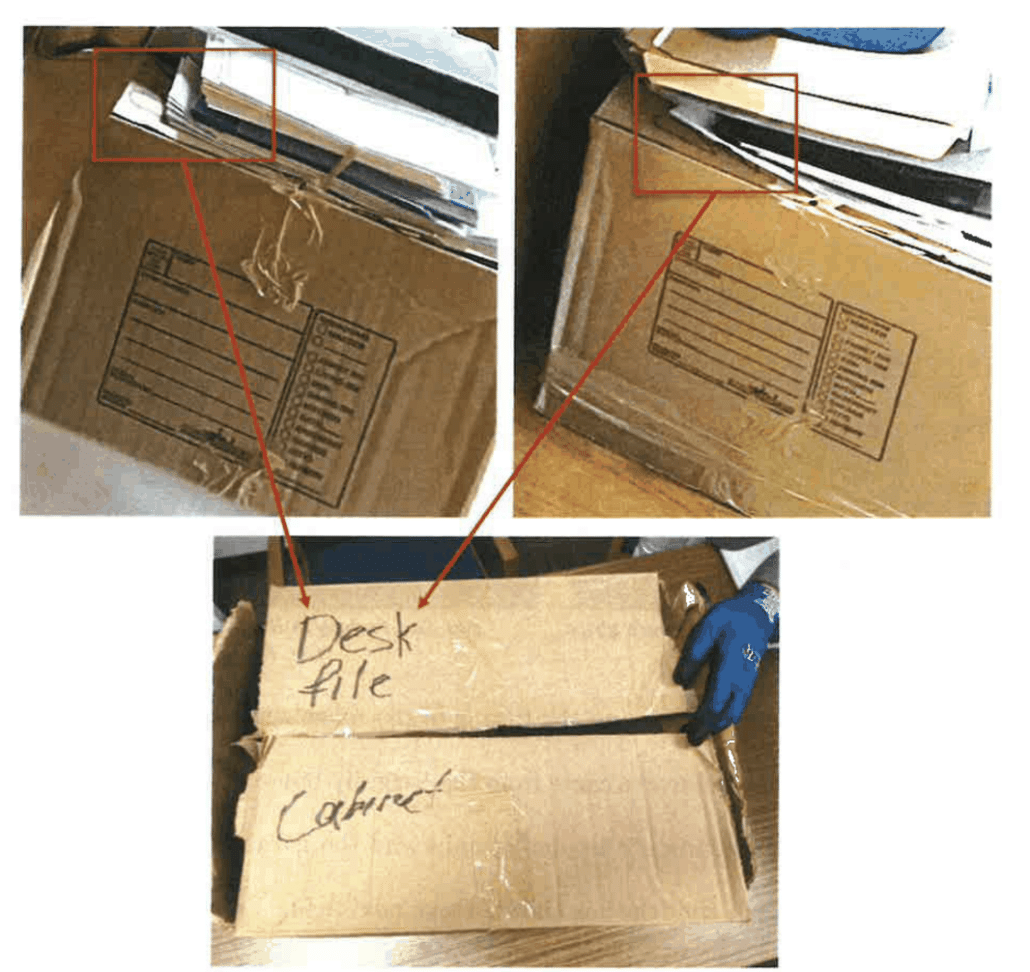
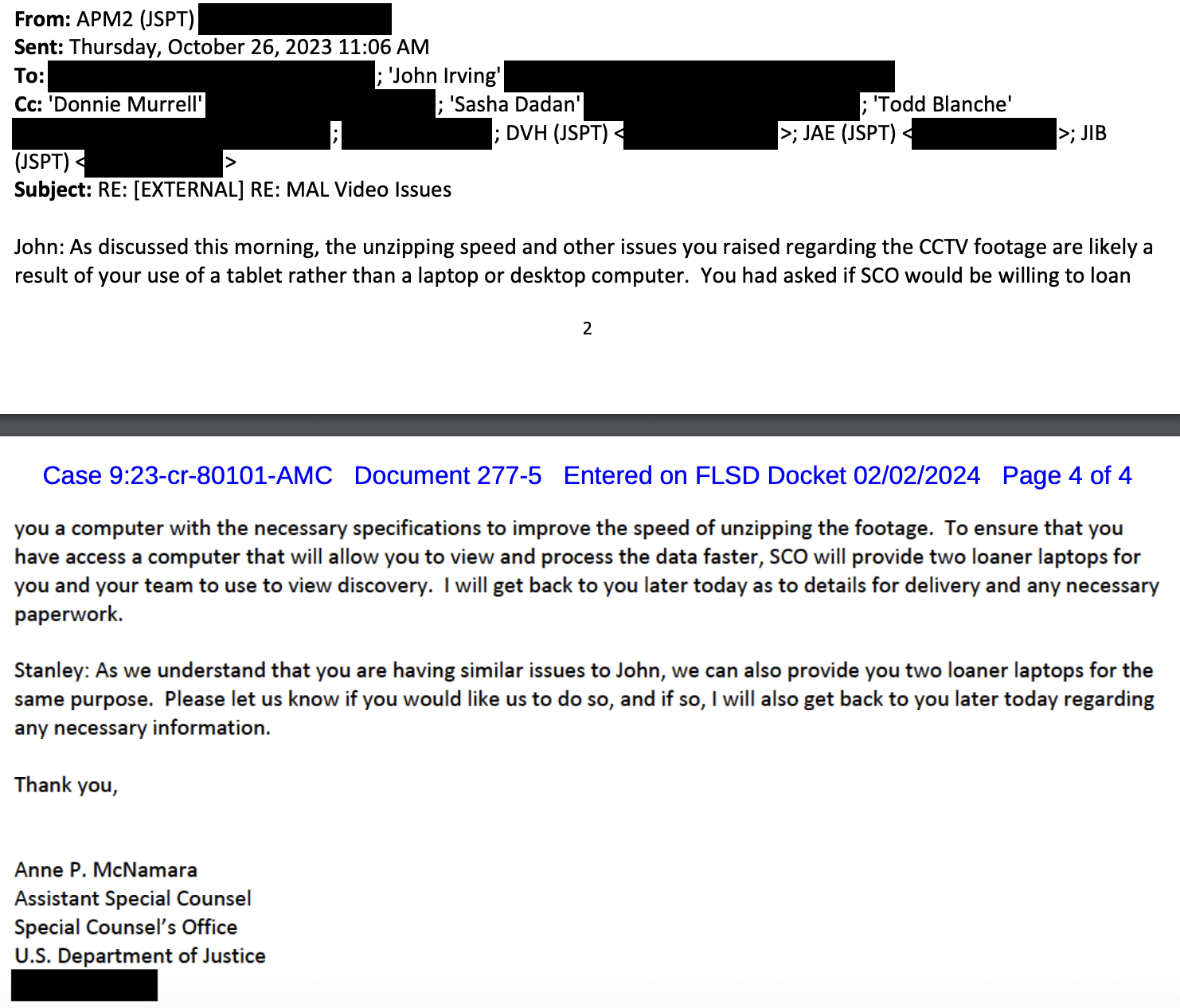
Next, after admitting that the FBI never succeeded in tracing the Afghan documents, much less proving they were in the basement of the Virginia house, he used this photo analysis to claim that the box found in the garage is the same one that appeared in two pictures taken in Biden’s Wilmington office in 2019, shortly after everything was shipped from Virginia to Delaware.
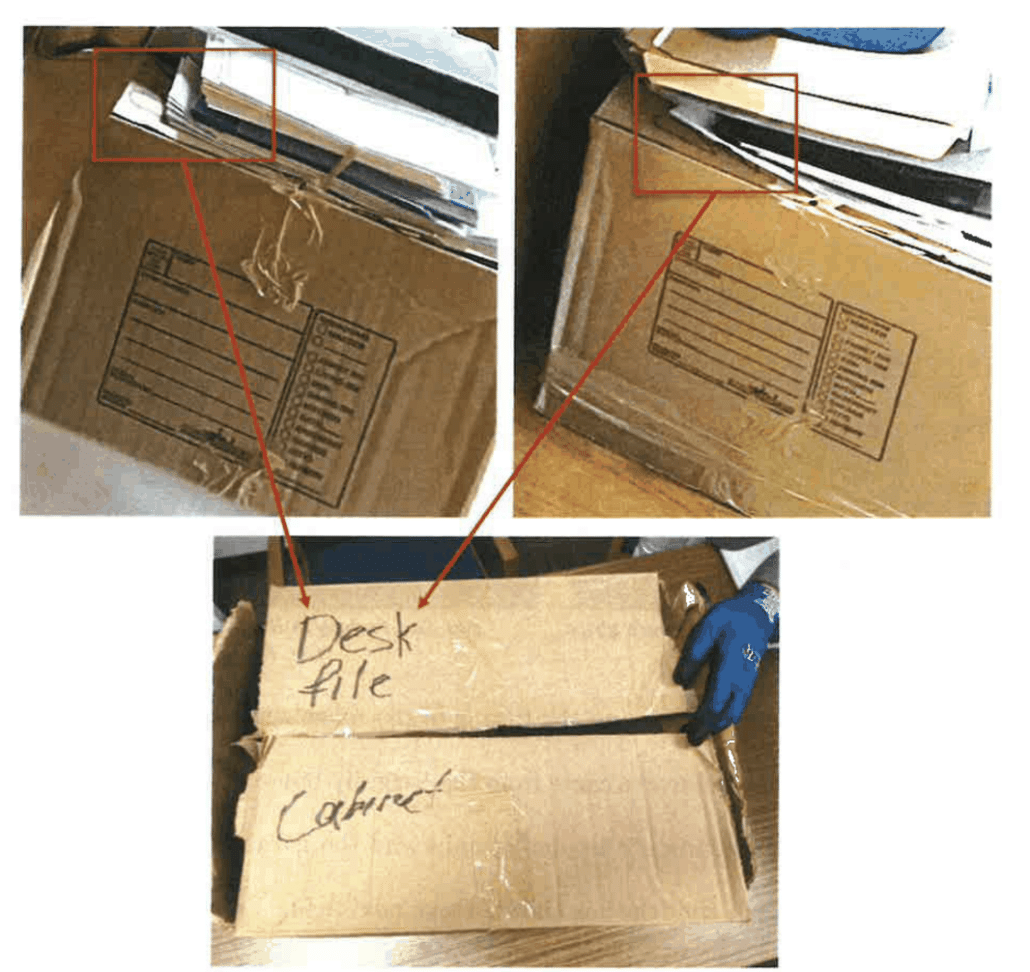
Maybe that’s right? Or maybe (as some people argued in this thread on Xitter) the D on the box in the garage is shaped differently and in a different place on the box lid than the one in the picture. Whatever it is, it’s no smoking gun.
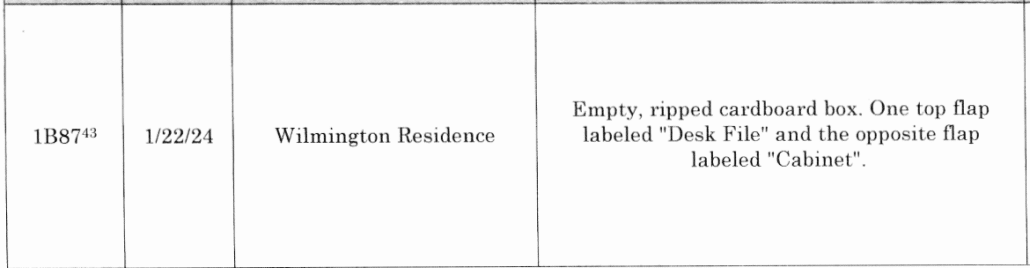
Finally, Hur goes to the contents of the box, claiming — with some justification — that some of the things in the box date to the same period when Biden uttered those 8 or maybe 66 words to his ghost writer.
Several folders in the garage box contained materials that Mr. Eiden appears to have accessed both shortly before and shortly after February 16 2017, the day Mr. Biden told Zwonitzer he had “just found classified documents downstairs. 582 For example, in January 2017 less than a month before told Zwonitzer he had just found the classified documents downstairs, Mr. Biden appears to have accessed documents later found in the box. On January 23, 2017. Biden wrote a notebook entry about a call scheduled for later that to finalize a deal with Creative Artists Agency (CAA), a talent agency that went on to represent him in negotiating his book deal for Promise Me, Dad. 583 The same entry also referenced Mr. Biden’s work with his sister on his “S Corp.”584
The box found in Mr. Biden’s garage contained a corresponding file folder, labeled “Signed Contracts Penn, CAA,” which contained the signature page of a final agreement between Mr. Biden and Creative Artists Agency.585 Mr. Biden signed the agreement, which was dated a few days after the notebook entry, on January 26, 2017.586 The folder also contained the final agreement between Mr. Biden and the Penn Biden Center-Mr. Biden’s primary employer after his vice presidency-which Mr. Biden signed, also on January 26, 2017. 587 And the folder contained a W-9 tax form for Mr. Biden’s S corporation, CelticCapri, which Mr. Biden used to receive income from book deals and speeches, among other purposes.588 The W-9 form listed Mr. Biden as the president of the S corporation and was signed by Mr. Biden and dated January 30, 2017-less than three weeks before Mr. Biden told Zwonitzer he had just found classified documents downstairs.589
The argument would be more persuasive, admittedly, if Hur didn’t confess that the FBI got the documents that had been in the box out of order when they repackaged them.
When FBI agents repackaged the contents of the ripped garage box into a new box on December 21, 2022, it appears the order of a few of the materials changed slightly. This chapter discusses in detail below two folders that contained marked classified documents about Afghanistan: the manila “Afganastan” folder and the red “Facts First” folder. It appears the “Afganastan” folder was near the “Facts First” folder in the garage box when agents recovered the box, but the precise original location of the “Afganastan” folder at that time is unknown.
Dudes. This was a consensual search of the President’s home, and you couldn’t even repackage documents competently? Really?
This argument would be more persuasive still if Hur weren’t ignoring some of the other things that were found in the box, that had nothing to do with Biden’s transition in 2017, which Biden’s attorneys described this way:
Your characterization of the box in the garage as containing only matters of “great personal significance” to the President is inconsistent with the facts. The evidence shows that this tattered box contained a random assortment of documents. including plainly unimportant ones such as: a short-term vacation lease; a VP-era memorandum on furniture at the Naval Observatory for purchase; talking points from speeches; campaign material; empty folders; a 1995 document commemorating Syracuse Law’s 100-year anniversary; and other random materials. In his interview. President Biden commented regarding one of the folders, which read “Pete Rouse”: “Christ that goes back a way,” confirming that he had not encountered that material in recent years. Tr., Day I, at 144. When asked how things like a binder labeled “Beau Iowa” got into the “beat-up” box. the President responded “Somebody must’ve, packing this up, just picked up all the stuff and put it in a box, because I didn’t.” Id. at 146. When asked about the later-dated material, the President responded: “[s]ee, that’s what makes me think just people gathered up whatever they found, and whenever the last thing was being moved. So the stuff moving out of the Vice President’s residence, at the end of the day, whatever they found. they put – they didn’t separate it out, you know, Speakers Bureau and Penn or whatever the hell it is. or Beau. They just put it in a single box. That’s the only thing I can think of.” Id. at 147. Some of the documents in the box contain what appears to be staff handwriting–including a D.C. tax return and a W2-further indicating that the box was likely filled by staff. We believe that an accurate recitation of the evidence on this point would include a description of these facts.
The true jumble of the box is particularly important because, elsewhere, Hur used the similar miscellany in a different box to rule out the possibility of willful retention for some of the documents found at the Penn Biden Center.
Finally, several of the files in the box where the EYES ONLY envelope was found appear to have been forgotten files of little value to Mr. Biden, such as the file about a 2011 ski trip. The files, therefore, do not appear to be a set that Mr. Biden personally curated. Nor do they appear to be the type of files people keep close as a matter of course in their everyday lives.
Hur adopted a different standard where it was clear only staffers were involved in packing a box than he did with a box that was central to “the strongest case for criminal charges against Mr. Biden.” Hur needed this box to be personally curated by Joe Biden, and so he omitted a bunch of random stuff that would debunk his story.
Still, this entire investigation should never have gotten this far, to where Hur was doing desperate last interviews three months after Biden’s own interview, to where Hur was spending 156 pages describing his declination decisions, and so in the process describing every single document at length.
To get there, Hur did something almost unheard of in declination decisions for 18 USC 793(e) cases: He treated “failure to deliver” as affirmative. Bizarrely, when he gets to the part of his discussion of the statute where he describes having to prove that Biden refused to deliver National Defense Information documents to an appropriate government official, he pivots, changes the subject, mid-paragraph.
Finally, the government must prove that a defendant willfully retained the material and failed to deliver it to an officer or employee “entitled to receive” the information. The statute does not define who is “entitled to receive” the information, so again, courts have looked to the governing rules concerning the handling of classified materials, primarily the executive order. 758 Generally, those entitled to receive the information are people with the requisite security clearance and the need to know. 759 Willfulness is a heightened mens rea, which as articulated by the Supreme Court in Bryan v. United States, requires proof “that the defendant acted with knowledge that his conduct was unlawful.” 760 Under the Espionage Act, an act is willful when “it is done voluntarily and intentionally and with the specific intent to do something that the law forbids. That is to say, with a bad purpose either to disobey or to disregard the law.” 761 While willfulness requires proving an intent to disobey the law, courts have applied Bryan’s standard of “simple willfulness” to Section 793(e) and rejected any need for the government to prove an intent to cause harm. 762
Accordingly, to prove a violation of Section 793(e) we would need to show that Mr. Biden knowingly retained national defense information and failed to deliver it to an appropriate government official, and that he knew this conduct was unlawful. [bizarre pivot] As discussed in more detail below, because of the interrelation between “national defense information” and “classified information,” when evaluating a potential Section 793(e) charge, the Department considers whether the information the person possessed was classified and whether the person knew it was classified.
In doing so, he dodges (here) the difficulty with charging a President with 793(e): That unlike actual clearance holders, Biden was never processed out of a clearance, which is where prosecutors fulfill that prong of the elements of offense when charging 793(e) along with other crimes, like leaking. When people with clearance leave their job, they’re reminded they have to give stuff back; because he wasn’t processed out of a clearance, Biden never got that talk.
Hur then wanders off a little ways, then returns to the question of delivering classified documents to someone entitled to receive them, by purporting to distinguish 793(e) from 793(d).
Subsection (d) also does not apply, because it requires a failure to deliver materials on demand, and when asked to return any classified materials from his vice presidency, Mr. Biden consented to searches and returned all potentially classified materials that were discovered. 767
Nuh uh! That’s not the difference between (d) and (e). The main difference is whether someone is authorized to have classified information or not.
(d) lawfully having possession … or willfully retains the same and fails to deliver it on demand to the officer or employee of the United States entitled to receive it;
(e) unauthorized possession … or willfully retains the same and fails to deliver it to the officer or employee of the United States entitled to receive it
Even for dirtbags like Jeremy Brown, DOJ generally only charges a retention charge absent something else after an officer asks for documents back. In Brown’s case, for example, they called an officer who had asked for the specific charged documents back to testify at trial to prove that prong of the elements of offense. And because Joe Biden was never processed out of a clearance, because the Archives never came looking for these, no one ever asked him to give the documents back.
Until he offered the documents up.
This entire report, all 388 pages of it, is based on a wild misrepresentation of how DOJ approaches Espionage Act prosecutions. And to the extent it’s not — to the extent that Hur is clinging to events caught on tape back in 2017 — the Statutes of Limitation have long expired.
And that gives up the game, even more than Robert Hur’s confession that jurors who weren’t, as he spent a year doing, “read[ing] too much into” some documents found in a box, would never convict on this.
Hur spent a year trying to find facts that would allow him to charge Joe Biden, charge a President, doing backflips with the evidence along the way, and then writing up a report that provides far more evidence about 40 year old documents covered by Speech and Debate than we’ll ever learn about the stolen documents at Mar-a-Lago.
This was never an ethical prosecutorial pursuit. It was always about writing a novel for a rabid audience.
Or, as you might consider it, just an exercise in box-ticking for partisan ends.
Update: I’ve been corrected: The SOL on Espionage Act is 10 years.