The (Thus Far) Flimsy Case for Republican Cooperation on Russian Targeting
A number of credulous people are reading this article this morning and sharing it, claiming it is a smoking gun supporting the case that Republicans helped the Russians target their social media, in spite of this line, six paragraphs in.
No evidence has emerged to link Kushner, Cambridge Analytica, or Manafort to the Russian election-meddling enterprise;
Not only is there not yet evidence supporting the claim that Republican party apparatchiks helped Russians target their social media activity, not only does the evidence thus far raise real questions about the efficacy of what Russia did (though that will likely change, especially once we learn more about other platforms), but folks arguing for assistance are ignoring already-public evidence and far more obvious means by which assistance might be obtained.
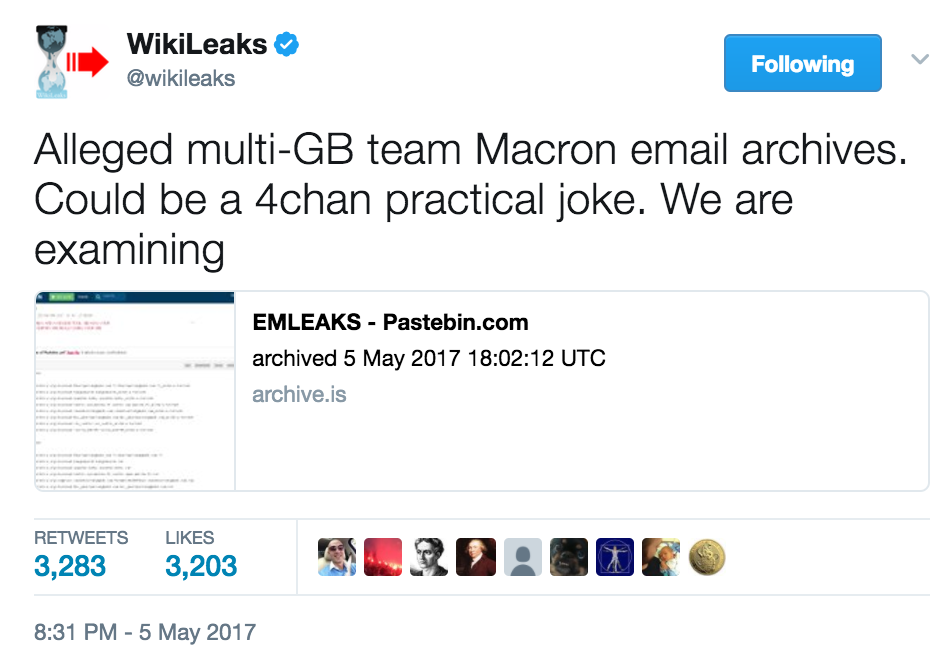
Don’t get me wrong. I’m acutely interested in the role of Cambridge Analytica, the micro-targeting company that melds Robert Mercer’s money with Facebook’s privatized spying (and was before it was fashionable). I first focused on Jared Kushner’s role in that process, which people are gleefully discovering now, back in May. I have repeatedly said that Facebook — which has been forthcoming about analyzing and sharing (small parts) of its data — and Twitter — which has been less forthcoming — and Google — which is still channeling Sargent Schultz — should be more transparent and have independent experts review their methodology. I’ve also been pointing out, longer than most, of the import of concentration among social media giants as a key vulnerability Russia exploited. I’m particularly interested in whether Russian operatives manipulated influencers — on Twitter, but especially in 4Chan — to magnify anti-Hillary hostility. We may find a lot of evidence that Russia had a big impact on the US election via social media.
But we don’t have that yet and people shooting off their baby cannons over the evidence before us and over mistaken interpretations about how Robert Mueller might get Facebook data are simply degrading the entire concept of evidence.
The first problem with these arguments is an issue of scale. I know a slew of articles have been written about how far $100K spent on Facebook ads go. Only one I saw dealt with scale, and even that didn’t do so by examining the full scale of what got spent in the election.
Hillary Clinton spent a billion dollars on losing last year. Of that billion, she spent tens of millions paying a 100-person digital media team and another $1 million to pay David Brock to harass people attacking Hillary on social media (see this and this for more on her digital team). And while you can — and I do, vociferously — argue she spent that money very poorly, paying pricey ineffective consultants and spending on ads in CA instead of MI, even the money she spent wisely drowns out the (thus far identified) Russian investment in fake Facebook ads. Sure, it’s possible we’ll learn Russians exploited the void in advertising left in WI and MI to sow Hillary loathing (though this is something Trump’s people have explicitly taken credit for), but we don’t have that yet.
The same is true on the other side, even accounting for all the free advertising the sensationalist press gave Trump. Sheldon Adelson spent $82 million last year, and it’s not like that money came free of demands about policy outcomes involving a foreign country. The Mercers spent millions too (and $25 million total for the election, though a lot of that got spent on Ted Cruz), even before you consider their long-term investments in Breitbart and Cambridge Analytica, the former of which is probably the most important media story from last year. Could $100K have an effect among all this money sloshing about? Sure. But by comparison it’d be tiny, particularly given the efficacy of the already established right wing noise machine backed by funding orders of magnitude larger than Russia’s spending.
Then there’s what we know thus far about how Russia spent that money. Facebook tells us (having done the kind of analysis that even the intelligence community can’t do) that these obviously fake ads weren’t actually focused primarily on the Presidential election.
- The vast majority of ads run by these accounts didn’t specifically reference the US presidential election, voting or a particular candidate.
- Rather, the ads and accounts appeared to focus on amplifying divisive social and political messages across the ideological spectrum — touching on topics from LGBT matters to race issues to immigration to gun rights.
- About one-quarter of these ads were geographically targeted, and of those, more ran in 2015 than 2016.
That’s not to say sowing discord in the US has no effect, or even no effect on the election. But thus far, we don’t have evidence showing that Russia’s Facebook trolls were (primarily) affirmatively pushing for Trump (though their Twitter trolls assuredly were) or that the discord they fostered happened in states that decided the election.
Now consider what a lot of breathless reporting on actual Facebook ads have shown. There was the article showing Russia bought ads supporting an anti-immigrant rally in Twin Falls, ID. The ad in question showed that just four people claimed to attend this rally in the third most Republican state. Another article focused on ads touting events in Texas. While the numbers of attendees are larger, and Texas will go Democratic long before Idaho does, we’re still talking relatively modest events in a state that was not going to decide the election.
To show Russia’s Facebook spending had a measurable impact on last year’s election, you’d want to focus on MI, WI, PA, and other close states. There were surely closely targeted ads that, particularly in rural areas where the local press is defunct and in MI where there was little advertising (WI had little presidential advertising, but tons tied to the Senate race) where such social media had an important impact; thus far it’s not clear who paid for them, though (again, Trump’s campaign has boasted about doing just that).
Additionally, empiricalerror showed that a number of the identifiably Russian ads simply repurposed existing, American ads.
That’s not surprising, as the ads appear to follow (not lead) activities that happened on far right outlets, including both Breitbart and Infowars. As with the Gizmo that tracks what it claims are Russian linked accounts and thereby gets credulous journalists to claim campaigns obviously pushed by Americans are actually Russian plots, it seems Russian propaganda is following, not leading, the right wing noise machine.
So thus far what we’re seeing is the equivalent of throwing a few matches on top of the raging bonfire that is the well established, vicious, American-funded inferno of far right media. That’s likely to change, but that’s what we have thus far.
But as I said, all this ignores one other key point: We already have evidence of assistance on the election.
Except, it went the opposite direction from where everyone is looking, hunting for instances where Republicans helped Russians decide to buy ads in Idaho that riled up 4 people.
As I reminded a few weeks back, at a time when Roger Stone and (we now know) a whole bunch of other long-standing GOP rat-fuckers were reaching out to presumed Russian hackers in hopes of finding Hillary’s long lost hacked Clinton Foundation emails, Guccifer 2.0 was reaching out to journalists and others with close ties to Republicans to push the circulation of stolen DCCC documents.
That is, the persona believed to be a front for Russia was distributing documents on House races in swing states such that they might be used by Republican opponents. Some of that data could be used for targeting.
Now, I have no idea whether Russia would risk doing more without some figure like Guccifer 2.0 to provide deniability. That is, I have no idea whether Russia would go so far as take more timely and granular data about Democrats’ targeting decisions and share that with Republicans covertly (in any case, we are led to believe that data would be old, no fresher than mid-June). But we do know they were living in the Democrats’ respective underwear drawers for almost a year.
And Russia surely wouldn’t need a persona like Guccifer 2.0 if they were sharing stolen data within Russia. If the FSB stole targeting data during the 11 months they were in the DNC servers, they could easily share that data with the Internet Research Association (the troll farm the IC believes has ties to Russian intelligence) so IRA can target more effectively than supporting immigration rallies in Idaho Falls.
Which is a mistake made by many of the sources in the Vanity Fair article everyone keeps sharing, the assumption that the only possible source of targeting help had to be Republicans.
We already know the Russians had help: they got it by helping themselves to campaign data in Democratic servers. It’s not clear they would need any more. Nor, absent proof of more effective targeting, is there any reason to believe that the dated information they stole from the Democrats wouldn’t suffice to what we’ve seen them do. Plus, we’ve never had clear answers whether or not Russians weren’t burrowed into far more useful data in Democratic servers. (Again, I think Russia’s actions with influencers on social media, particularly via 4Chan, was far more extensive, but that has more to do with HUMINT than with targeting.)
So, again, I certainly think it’s possible we’ll learn, down the road, that Republicans helped Russians figure out where to place their ads. But we’re well short of having proof of that right now, and we do have proof that some targeting data was flowing in the opposite direction.
Update: This post deals with DB’s exposure of a FB campaign organizing events in FL, which gets us far closer to something of interest. Those events came in the wake of Guccifer 2.0 releasing FL-based campaign information.