James Wolfe: The Distinction Between FBI’s Investigation of Leaking Classified versus Non-Public Information
There’s something about the James Wolfe case that has stuck with me. For an article published after Wolfe’s indictment was released, Ali Watkins’ lawyer, Mark MacDougall, tempered his concern about Watkins’ call records being seized by suggesting that the scope of charges might somehow legitimate it.
Watkins’ attorney, Mark MacDougall, had described the seizure as “disconcerting.”
“Whether it was really necessary here will depend on the nature of the investigation and the scope of any charges,” MacDougall said in a statement.
While MacDougall has gone silent since then, this comment suggested there might be a reasonable premise for DOJ to seize all of Watkins call records for her entire journalistic career, which is fairly shocking. FBI gets all the call records of someone, these days, to identify all the devices she uses to check that activity as much as they do so to identify specific calls made. There’s nothing revealed by the indictment that would justify that, and a lot (notably, the evidence they had ready access to Wolfe’s phone content) that suggests it wasn’t justified.
With that in mind, I want to look at some details about the known timeline of the investigation:
March 2017: Exec Branch provides SSCI “the Classified Document,” which includes both Secret and Top Secret information, with details pertaining to Page classified as Secret.
March 2, 2017: James Comey briefs HPSCI on counterintelligence investigations, with a briefing to SSCI at almost the same time.
March 17, 2017: 82 text messages between Wolfe and Watkins.
April 3, 2017: Watkins confirms that Carter Page is Male-1.
April 11, 2017: WaPo reports FBI obtained FISA order on Carter Page.
June 2017: End date of five communications with Reporter #1 via Wolfe’s SSCI email.
June 2017: Using pretext of serving as a source, CBP agent Jeffrey Rambo grills Watkins about her travel with Wolfe.
October 2017: Wolfe offers up to be anonymous source for Reporter #4 on Signal.
October 16, 2017: Wolfe Signals Reporter #3 about Page’s subepoena.
October 17, 2017: NBC reports Carter Page subpoena.
October 24, 2017: Wolfe informs Reporter #3 of timing of Page’s testimony.
October 30, 2017: FBI informs James Wolfe of investigation.
November 15, 2017: 90 days before DOJ informs Ali Watkins they’ve seized her call records.
December 14, 2017: FBI approaches Watkins about Wolfe.
Prior to December 15, 2017 interview: Wolfe writes text message to Watkins about his support for her career.
December 15, 2017: FBI interviews Wolfe.
February 13, 2018: DOJ informs Watkins they’ve seized her call records.
June 6, 2018: Senate votes to make official records available to DOJ.
That the Chairman and Vice Chairman of the Senate Select Committee on Intelligence, acting jointly, are authorized to provide to the United States Department of Justice copies of Committee records sought in connection with a pending investigation arising out of allegations of the unauthorized disclosure of information, except concerning matters for which a privilege should be asserted.
June 7, 2018: Grand jury indicts Wolfe.
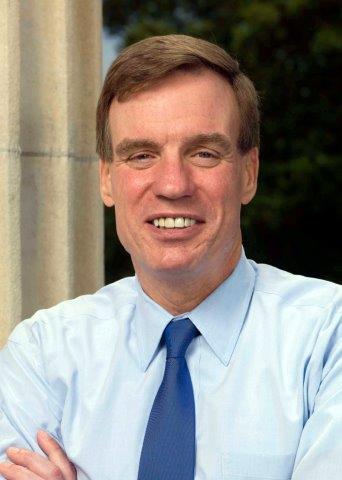
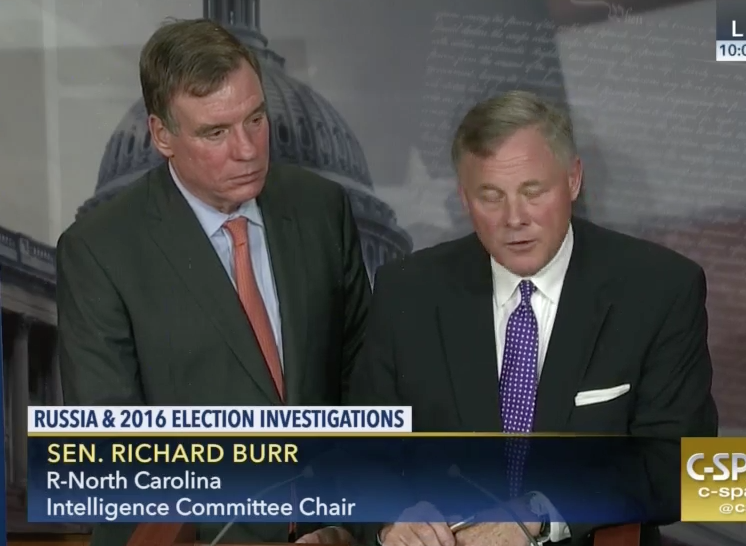
June 7, 2018: Richard Burr and Mark Warner release a statement:
We are troubled to hear of the charges filed against a former member of the Committee staff. While the charges do not appear to include anything related to the mishandling of classified information, the Committee takes this matter extremely seriously. We were made aware of the investigation late last year, and have fully cooperated with the Federal Bureau of Investigation and the Department of Justice since then. Working through Senate Legal Counsel, and as noted in a Senate Resolution, the Committee has made certain official records available to the Justice Department.
June 13, 2018: Wolfe arraigned in DC. His lawyers move to prohibit claims he leaked classified information.
The indictment is quite clear: the investigation leading to Wolfe’s indictment started as an investigation into “multiple unauthorized disclosures of classified information” to the press. It’s clear from Burr and Warner’s statement that they were a bit surprised that the “charges do not appear to include anything related to the mishandling of classified information.” The indictment doesn’t charge Wolfe with leaking classified information.
And the timeline laid out in the indictment suggests that the document provided SSCI in March 2017 led to Watkins confirming that Page was Male-1 in the Victor Podobnyy complaint, the complaint itself is probably not classified. Nor would it, with its reference to Page as Male-1 (also used in this indictment!), be enough to ID Page as the guy Podobnyy was trying to recruit.
As I suggested in this post, for all the focus on Watkins, the indictment actually seemed to prioritize Reporter #1, including on the questionnaire the FBI gave Wolfe when they interviewed him in December. It first asked if Wolfe knew any of the reporters behind that still unidentified story, then asked a question that his relationship with Watkins would clearly refute, which agents contextualized even further by asking specific questions about details they had already confirmed about their relationship, including the international travel Rambo had identified as early as June. Then, after asking a question that would clearly pertain to Wolfe’s undeniable relationship with Watkins, the questionnaire asked whether he had given classified or unclassified documents to any of the journalists he might have admitted to contacting in Question 10, covering the basis for that Podobnyy story.
c. During the interview, FBI agents showed WOLFE a copy of a news article authored by three reporters, including REPORTER #1, about an individual (referred to herein as “MALE-l)”, that contained classified information that had been provided to the SSCI by the Executive Branch for official purposes.
d. Question 9 of the lnvestigative Questionnaire asked “Have you had any contact with” any of those three reporters. As to each reporter, WOLFE stated and checked “No.”
e. Question 10 of the Investigative Questionnaire asked, “Besides [the three named reporters], do you currently have or had any contact with any other reporters (professional, official, personal)?” Before answering this question, WOLFE stated orally to the FBI agents that although he had no official or professional contact with reporters, he saw reporters every day, and so to “feel comfortable” he would check “Yes.” He did so, and initialed this answer.
f. Question 10 of the Investigative Questionnaire further asked, “If yes, who and describe the relationship (professional, official, personal).” In the space provided, WOLFE hand wrote “Official – No” and “Professional – No.” WOLFE then orally volunteered that he certainly did not talk to reporters about anything SSCl-related. FBI agents orally asked WOLFE if he had traveled internationally with any reporter, gone to a baseball game or to the movies with a reporter, or had weekly or regular electronic communication with a reporter. To each question WOLFE verbally responded ‘No.” WOLFE then wrote “Personal – No” on the Investigative Questionnaire.
g. Question 11 of the lnvestigative Questionnaire asked, “If yes to question ten, did you discuss or disclose any official U.S. government information or documents whether classified or unclassified which is the property of the U.S. government without express authorization from the owner of the information?” WOLFE stated and checked “No” and initialed this answer.
Now consider the vote to release official SSCI documents to DOJ, which DOJ appears to have needed before they presented the indictment to the grand jury the next day, but which DOJ knew enough about to already be prepped to indict. That is, DOJ surely already knew what those records showed; what the vote did was permit DOJ to use the records in a prosecution. There are surely records pertaining to the SSCI SCIF that DOJ wanted, including the specific treatment of the Classified Document delivered to SSCI in March 2017.
On or about March 17,2017,the Classified Document was transported to the SSCI. As Director of Security, WOLFE received, maintained, and managed the Classified Document on behalf of the SSCI.
It’s also possible (though unlikely) that SSCI, and not the Executive Branch, counts as custodian of Wolfe’s Non-Disclosure Agreements.
But the only actual SSCI record described in the indictment is the email account he used to communicate with Reporter #1, as well as emails that Page sent to the committee to complain about leaks.
For example, between in or around December 2015 and in or around June 2017, WOLFE and REPORTER #1 communicated at least five times using his SSCI email account.
[snip]
26. On or about October 18, 2011, MALE-1 sent an email to the SSCI, complaining that the news organization had published REPORTER #3’s news article of the previous day, reporting that he had been subpoenaed.
27. On or about October 24,2017, at 7:00 a.m., WOLFE informed REPORTER #3, using Signal, that MALE-1 would testify in closed hearing before the SSCI “this week.” At 9:58 a.m., REPORTER #3 sent an email to MALE-I, asking him to confirm that he would be ‘paying a visit to Senate Intelligence staffers this week.” At 9:23 p.m., MALE-I sent an email to the SSCI, forwarding the email he had received from REPORTER #3, and complaining that the details of his appearance had been leaked to the press.
So it’s possible that, having had SSCI’s cooperation since the time FBI was interviewing Wolfe, DOJ only needed to ensure it could access these email records. It’s possible that DOJ believes convicting Wolfe of false statements charges, and avoiding the hassle of exposing classified information at a trial charging that he leaked classified information, is sufficient punishment.
Or it’s possible that this indictment is just the next step in an investigative process that aims to get confirmation — public or tacit, the latter obtained via a guilty plea with cooperation — regarding the source for that other, still unidentified story that incorporated classified information. I also think FBI may be particularly interested that Wolfe was approaching journalists offering to be a source, as he did in October with Reporter #4, and not vice-versa.