 Today’s Inspector General Report on FBI’s use of National Security Letters has set off a bunch of alarm bells in my head.
Today’s Inspector General Report on FBI’s use of National Security Letters has set off a bunch of alarm bells in my head.
At issue are two unexplained problems.
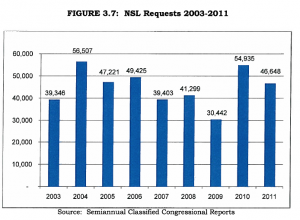
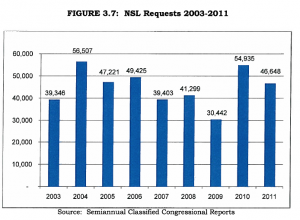
First, the Inspector General identified a huge drop in NSL use for the years covering this report: FBI obtained 49,425 NSLs in 2006, the year before this report. It obtained 54,935 afterwards. The years in-between — the 3 years covered by this report — NSLs dropped off a relative cliff, with 20% fewer in 2007 and even fewer in 2009.
The IG wasn’t able to offer any explanation for this, besides the possibility that increased scrutiny on NSL use led people to use other methods to get this information.
However, two supervisors and a division counsel told us that they believe agents use NSLs less often now than they did five years ago. These individuals told us that because of increased scrutiny on NSL use agents employ alternative investigative tools when possible.
In testimony last year, Jim Comey said FBI agents would just use grand jury subpoenas rather than NSLs if the NSLs became too onerous, so that may be where the activity disappeared to.
Hey, if 20% of FBI NSLs could be grand jury subpoenas without any problem, let’s make them do that!
It’s FBI’s other counting problems — and its non-answers — that have me even worried.
According to the IG, the FBI is not reporting as much as 7.3% [update, 10/16: I think the correct number is 6.8%] of its NSL use to Congress. For example, when the IG tried to pull NSLs by NSL type (that is, toll billing, financial records, electronic transaction records), it found a significant discrepancy between what had been reported to Congress and what FBI’s internal spreadsheets showed.
[T]he NSL data in the itemized spreadsheets does not exactly match the NSL data reported to Congress in 2008 and 2009. The total number of requests reported for each year [by transaction type] is more than the total number of NSL requests reported to Congress by 2,894 and 2,231 requests, respectively. (63)
So for 2009, where FBI requested just 30,442 NSLs, FBI did not report 7.3% of the NSLs it requested.
(I can’t double check my math here because FBI redacted some of these tables, but I guess that’s one of the hazards of overclassifying things.)
That’s troubling enough, as is FBI’s lackadaisical attitude towards correcting the disparity.
After reviewing the draft of this report, the FBI told the OIG that while 100 percent accuracy can be a helpful goal, attempting to obtain 100 percent accuracy in the NSL subsystem would create an undue burden without providing corresponding benefits. The FBI also stated that it has taken steps to minimize error to the greatest extent possible.
Ho hum, we’re just the FBI, why expect us to be able to police ourselves?
But it gets weirder.
First, the one theory the IG came up with to explain the discrepancy is that FBI is not counting all the manual NSLs that bypass their automatic counting system implemented in response to the first IG Reports on NSLs.
In fact, they’re not: FBI’s Inspection Division found they’re not counting some significant (not single digit) percentage number of their manual NSLs (they redact how much they’re not counting on page 39).
But the IG seems to suspect there may be even more manual requests that are not being counted at all.
[T]he total number of manually generated NSLs that the FBI inspectors identified is relatively small compared to the total number of 30,442 NSL requests issued by the FBI that year. What remains unknown, however is, whether the FBI inspectors identified all the manually identified generally NSLs issued by the FBI or whether a significant number remains unaccounted for and unreported.(58)
If you guessed that FBI redacted under what circumstances FBI permits agents to bypass this automatic counting system, you’d be right. That discussion is in footnote 35 on page 17, and again on pages 113-115.
But I worry, given one observation from the IG, that they’re bypassing the automatic system in cases of “sensitive” investigations. Some apparent moron tried to explain why the IG found higher numbers for NSLs than Congress because the NSLs related to sensitive investigations were being reported to Congress but not the IG.
After reviewing the draft of this report, the FBI told the OIG for the first time that the NSL data provided to Congress would almost never match the NSL data provided to the OIG because the NSL data provided to Congress includes NSLs issued from case files marked “sensitive,” whereas the NSL data provided to the OIG does not. According to the FBI, the unit that provided NSL data to the OIG does not have access to the case files marked “sensitive” and was therefore unable to provide complete NSL data to the OIG. The assertion that the FBI provided more NSL data to Congress than to the OIG does not explain the disparities we found in this review, however, because the disparities we found reflected that the FBI reported fewer NSL requests to Congress than the aggregate totals. (58)
Aside from the revelation that FBI doesn’t understand how numbers work — that if Congressional reporting reflected a larger universe of NSLs than what the IG got to see, Congressional numbers should be higher, now lower — this also seems to mean that the IG is not being permitted to review the NSLs relating to sensitive investigations.
Now, it’s not entirely clear what FBI means by “sensitive” in this circumstance. But generally, “sensitive” investigations at FBI are those that investigate reporters, faith leaders, and politicians.
So it seems possible the FBI is not permitting the IG to review precisely the practices he should review.
Which brings me to another matter that is almost entirely redacted.
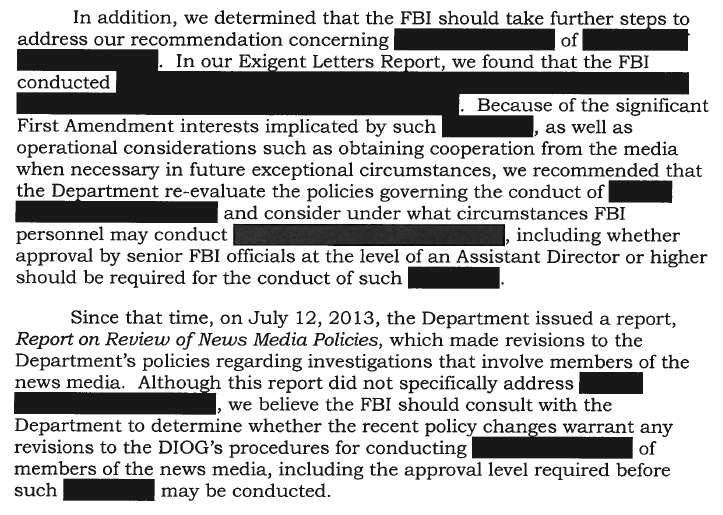
As I’ve reported repeatedly, one thing the last IG report on Exigent Letters showed is that a number of journalists have had their phone records collected by FBI. In addition, the 2011 DIOG made it acceptable to use NSLs to do so. Here’s the section of the executive summary of this report that describes whether FBI has resolved this issue.
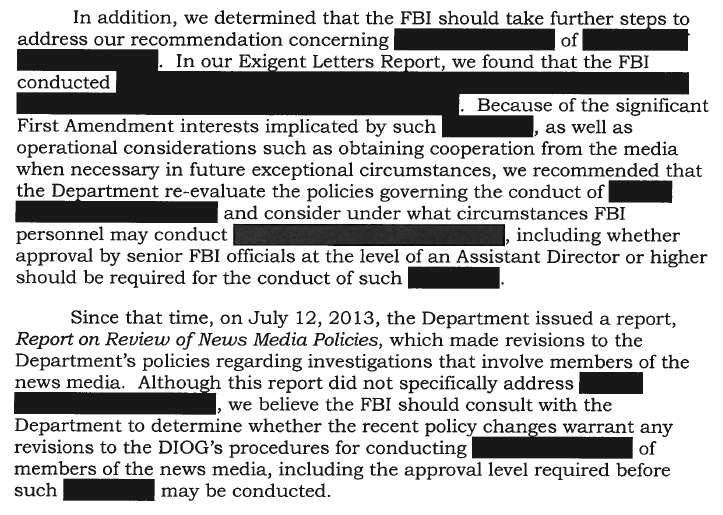
From which I can only assume that FBI is continuing to use NSLs to collect journalist records (if FBI would like to declassify this language to prove me wrong, I welcome their transparency!).
So to sum up:
- FBI can’t figure out why its NSL numbers dropped of a cliff for the years in question
- FBI can’t figure out what happened to up to 7.3% of its NSLs
- The IG thinks it is possible there are even more NSLs missing from those numbers
- When asked, the FBI said maybe discrepancies come from files on sensitive investigations that the IG has no access to
- The FBI does appear to be continuing its use of NSLs to hunt down journalists’ sources, which qualifies under the DIOG as a “sensitive” investigation, along with faith leaders and politicians
All that could be badly wrong — much of this information is redacted from both me, and in some cases, from Congress.
But doesn’t it raise some awfully big questions?