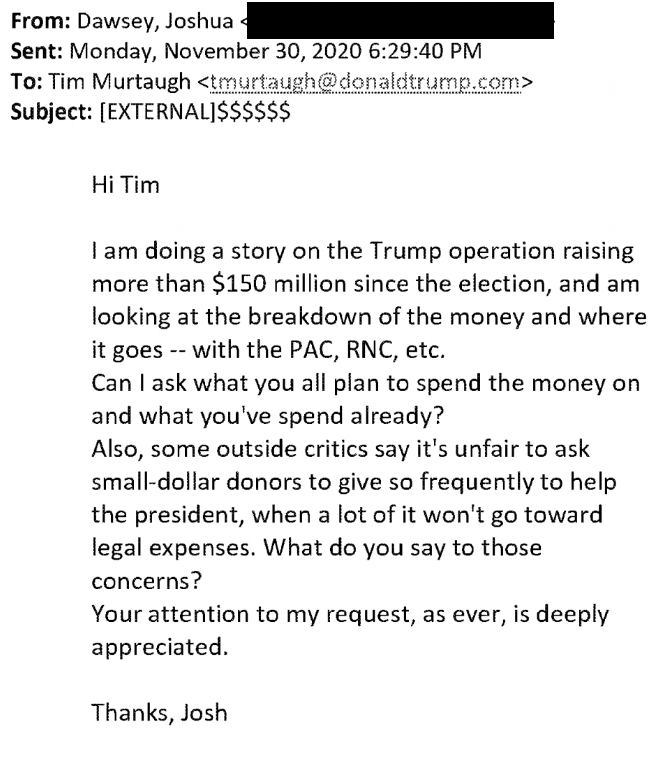
There’s a really sordid aspect regarding the timing of the indictment of Robert Menendez unveiled yesterday. Its timeline starts in February 2018, when Nadine Arslanian first starts dating the senior Senator from New Jersey. That was just weeks — possibly days! — after the last bribery case against Menendez ended.
So weeks after DOJ decided not to retry Menendez on his first bribery case, a then-unemployed woman, Nadine Arslanian, started dating the disgraced Senator and, within weeks of that, she alerted an Egyptian friend, Wael Hana, that she was dating him. That set off the most alarming — but probably not the stongest — part of the case: that Menendez was feeding Egypt information and ultimately set up a back channel with an Egyptian intelligence official, meeting at his home in Egypt in October 2021. Those are alarming allegations, but not allegations as clearly tied to financial payoffs to Menendez as some other things.
It’s like some TV producer decided to renew a series for a second season based off an entirely new story line slapped on the older story. “I know! We’ll throw a woman in the mix!”
Aside from that 2021 trip, much of the Egyptian influence operation happened before Nadine and Menendez were married in October 2020. For much of the period, Nadine complained she wasn’t being paid (in a no-work job at Hana’s Halal company). And some of the meetings between Menendez and the Egyptians would not be that far outside the norm for a Senate Foreign Relations Member, much less the Chair. The trip to Egypt, probably accidentally, was made official, giving Menendez legal cover for it. And the seeming bribery immediately upon his return — like a lot of the other payments in this period — came from a long-time Menendez fundraiser, Fred Daibes, or from a Hana associate, Jose Uribe, not directly from Hana.
In other words, this story appears to start with Nadine’s friends exploiting the access she got through her relationship with Menendez. That, as alleged, is largely her corruption. And to prove the corruption, DOJ will need to prove that the payments she only belatedly got were not part of a legitimate job. It’s sketchy as hell. It raises questions about Foreign Agent laws (especially for Hana). But at least as presented in the indictment, that’s not the strongest evidence, certainly not against Menendez.
The stuff that more directly implicates Menendez is his intervention in several criminal investigations, first in the case of an Uribe associate, then in the case of Daibes, Menendez’ longtime fundraiser. Menendez allegedly tried to intervene with prosecutors to help an Uribe associate beat a state charge, and Daibes beat a federal charge, but as described, both cases resolved in probation plea deals without his interference having any effect.
The items DOJ claims must be forfeited as fruits of the crime provide a sense of how much more Daibes allegedly paid Menendez than Hana:
- The Menendez’ residence in Englewood Cliffs (this may have originally belonged to Nadine, in which case the forfeiture stems from mortgage payments of $23,000 IS EG Halal made on the residence in July 2019)
- The $75,000 2019 Mercedes C300 José Uribe paid for starting in 2019, which the Menendez’ tried to make look like a loan retroactively in July 2022; it’s not clear — and DOJ doesn’t say — whether the Mercedes was payoff for the Egyptian influence or for Menendez’ attempt to influence the prosecution of Uribe’s associate
- $486,461 in cash, some of which bore Daibes’ DNA or fingerprints, one envelope of which had Menendez’ DNA, some of which was stashed in a Menendez jacket
- $79,760 in cash seized in Nadine’s safe deposit box
- 2 1-KG bars of gold seized on June 16, 2022; these — and at least two others that Nadine sold for around $120,000 in March 2022 — likely came from Daibes
- 11 1-ounce bars of gold seized on June 16, 2022; these were likely what remained of 22 ounces total, originally valued at around $39,600, purchased by Hana after some meetings with Egyptian officials on June 23, 2021
- An account tied to Strategic International Business Consultants, which Nadine formed in June 2019 after IS EG Halal got its monopoly and to which IS EG Halal paid three $10,000 payments in August, September, and November 2019
So the Mercedes (worth $75,000) at least appears to be payoff for Menendez’ efforts to help an Uribe associate beat a state case. As noted, the indictment says prosecutors shielded the investigative team from Menendez’ interference, but Uribe and the associate nevertheless had a celebratory dinner with Menendez attributing his legal good fortune to Menendez.
Because the roughly $100,000 in payments from Hana — with the exception of the one-ounce gold bars — came through IS EG Halal, DOJ will need to prove that Nadine’s no-work job really wasn’t a job or at least not a legal one.
The bulk of the payments, around $720,000 in cash and gold (the indictment also references checks not itemized here), came from Daibes. While he had financial ties to Hana, he also had a long-lasting relationship as a fundraiser for Menendez, and DOJ doesn’t lay out when the money came in. Given the extent of that relationship, Menendez’ intervention with the US Attorney’s office (and his equivocations about supporting Phil Sellinger’s appointment) are corrupt as hell but not unusual for Washington.
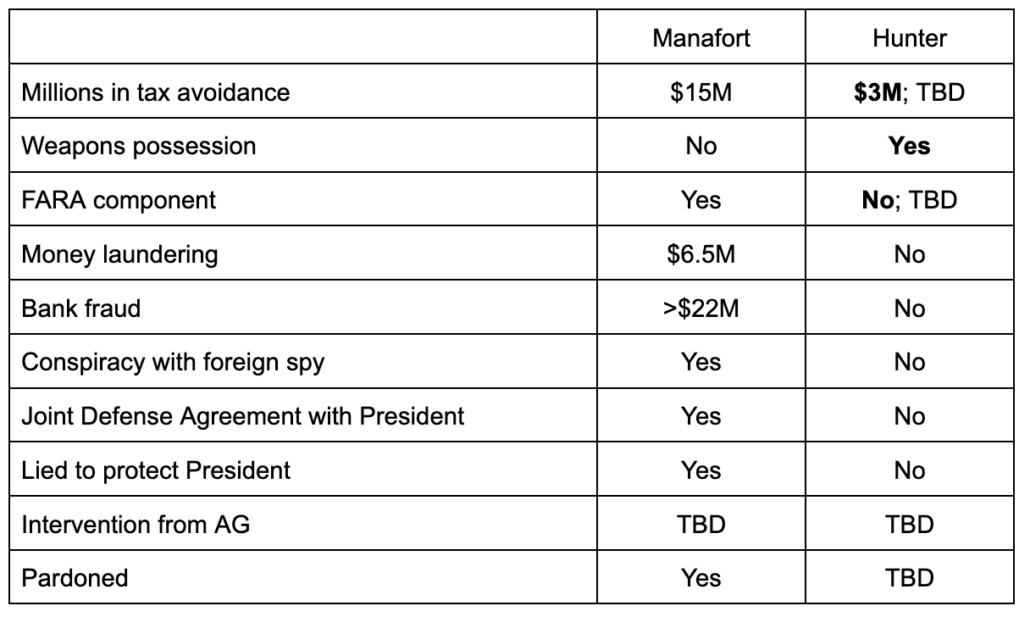
After all, Attorney General Garland only got confirmed after assuring Lindsey Graham and other Senators that he would continue the politically influenced criminal investigations into Hunter Biden and (by John Durham) of Hillary Clinton and her associates. And the entire House GOP is continuing such demands to this day, in part because their Sugar Daddy, Donald Trump, demands it.
There has to be something more to the Daibes’ money, something not laid out in this indictment. Particularly given that there are no campaign finance allegations, DOJ has not ruled out that Menendez was just on a regular take from Daibes. It simply doesn’t account for the amount of money Daibes allegedly gave Menendez, nor does it tie that money to specific quid pro quos.
(Daily Beast reports that Daibes has or had ties with the Italian mafia.)
Similarly, there must be more explanation to the Daibes’ plea deal. This indictment suggests that Sellinger’s First AUSA, Vikas Khanna, rebuffed Menendez’ efforts to intervene in the Daibes case, just like NJ state prosecutors rebuffed his efforts to intervene in the case of the Uribe associate who nevertheless attributed his plea to Menendez. The NJ USAO only belatedly clarified that Sellinger was recused and the plea had been approved by Khanna on the day of the indictment. And it’s hard to explain the repeated continuances of Daibes’ sentencing, first in September 2022, then in December 2022, then in March 2023, then in July 2023; sentencing for Daibes and his co-defendant is currently set for October 23, 2023. The sentencing submissions submitted in August 2022 remain sealed. If Daibes started cooperating in this case after the June 2022 searches of the other co-defendants, it might make sense, but there’s no hint of that.
Likewise, there’s no ready explanation for why SDNY is prosecuting this instead of NJ USAO. Rather than any mention that this got referred from one of those NJ offices, which is what you would hope happened if a politician attempted to influence a prosecution, the indictment establishes venue in fairly tangential acts (marked in blue in the timeline below): Two dinners Menendez and Nadine had in Manhattan, the loan payments Uribe arranged through a bank in the Bronx, and a text Nadine sent on September 5, 2019.
Finally, it’s not clear whether this investigation arose out of an investigation — perhaps for being a foreign agent, which inexplicably is not included in this indictment — into Hana, which led up to the search of his phone in November 2019 but which doesn’t appear to have alarmed anyone, or out of further scrutiny of Daibes.
Or maybe, after the prosecution failed the last time, DOJ Public Integrity (which was heavily involved in the first prosecution of Menendez) just kept watching, knowing he’d stumble again.
Some of the overt acts in this indictment — most notably when Menendez provided sensitive information about embassy staffing to the Egyptians — happened more than five years ago, so they’re only included as part of a conspiracy that continued for years after that. But I wouldn’t rule out that we get more clarity about all this money in a superseding indictment.
Update: Added the detail that the June 21, 2021 meeting with Egypt’s Intelligence head pertained to Egypt’s role in the Jamal Khashoggi assassination.
Timeline
Below, I’ve bolded key payments (there are other payments that DOJ does not date in the indictment). I’ve marked in pink the engagement and marriage of Nadine and Menendez, which may change the legal import of Nadine’s actions with Menendez. I’ve marked the acts that SDNY uses to establish venue in blue.
April 1, 2015: DOJ indicts Menendez and longterm associate, Salomen Melgen.
June 27, 2016: US v McDonnell decision.
July 17, 2017: Menendez moves to dismiss in light of US v McDonnell decision.
August 2017: State Department withholds $195 million in military support for Egypt and cancels $65.7 million in other financing.
November 16, 2017: Jury hangs in Salomon Melgen trial.
January 19, 2018: DOJ notices intent to retry case.
January 24, 2018: Judge William Walls grants Menendez’ Rule 29 motion on 7 of 18 counts.
January 31, 2018: DOJ moves to dismiss first bribery case.
February 2018: Nadine Arslanian, at the time unemployed, starts dating Menendez.
Early 2018: Nadine tells Hana she is dating Menendez.
March 2018: Menendez meets with Egyptian Official-1, Nadine, and Hana, without his professional staffers, in his DC Senate office and discusses foreign military funding.
April 2018: Uribe tells Hana that “the deal is to kill and stop all investigation”‘ of associate investigated for insurance fraud.
May 6, 2018: After meeting with Nadine and Hana (location uncertain), Menendez seeks out number and nationality of peoeple working at US Embassy in Cairo.
May 7, 2018: Menendez texts details of Embassy staffing to Nadine, who forwarded it to Hana, who forwarded it to Egyptian Official-2.
May 2018: Menendez has fancy dinner with Hana after which Hana texts Egyptian Official-1 that “the ban on small arms and ammunition to Egypt has been lifted.”
May 2018: Nadine gets Menendez to ghost write letter asking other Senators to release $300 million hold. He sends ghost-written letter to her via personal email; she sends it to Hana. Both delete the email.
Several months after March 2018: Nadine expresses hope that Egypt “replace him,” meaning Hana.
June 30, 2018: Menendez, Nadine, and Hana meeting in Manhattan restaurant.
July 2018: After meeting with Egyptian Official-1 set up by Nadine and Hana, Menendez tells Nadine he will sign off on $99 million sale to Egypt, stating that they have had such arms for many years and use them for counterterrorism in the Sinai.
October 30, 2018: Fred Daibes charged by US Attorney for obtaining loans under false pretenses.
December 2018: Nadine has car accident and starts complaining to Hana that she does not have a car.
January 27, 2019: Menendez, Nadine, and Hana meet at dinner (Uribe was invited but did not attend), after which Hana starts sending Nadine texts about Uribe associate’s criminal case. Nadine deleted those messages.
January 29, 2019: After reviewing texts with Nadine (which both deleted), Menendez attempts to pressure Official-2 to resolve the prosecution of Uribe’s associate. Official-2 does not intervene.
February 3, 2019: Nadine texts Hana, “I’m so excited to get a car next week !!”
2018 to 2019: Hana’s halal firm, which had no revenue, did not deliver on payments promised to Nadine.
March 12, 2019: Nadine and Uribe speak for 21 minutes, after which Uribe texts, “I am real. I will stand by my word.”
March 27, 2019: Uribe directs Nadine to a Mercedes dealer, after which she sends Menendez pictures to help pick a color.
April 2019: Uribe associate resolves case with guilty plea that was more favorable than prosecutors’ initial plea offer.
April 3, 2019: Nadine texts dealer saying Uribe told her to pick up car on April 5.
April 3, 2019: Uribe tells associate, “I need 15k cash this afternoon.”
April 4, 2019: Nadine texts Menendez that she’s going “to meet Jose for five minutes;” in the parking lot of a restaurant, he hands her $15,000 in cash.
April 5, 2019: Nadine uses the $15,0000 as a down payment to get the Mercedes, paying the rest with a loan based on false financing claims.
April 7, 2019: Egyptian government official informs Hana he’ll become sole certifier for halal imports.
April 8, 2019: Nadine texts Menendez, “seems like halal went through. It might be a fantastic 2019 all the way around.”
Spring 2019: Egypt grants Hana’s halal company, IS EG Halal, exclusive monopoly on certifiying meat exported from the US to Egypt as halal.
April and May 2019: USDA complains to Egypt about monopoly grant to IS EG Halal.
May 2019: Uribe starts paying off Nadine’s loan, via an associate’s Bronx business account, keeping his name out of it.
May 3, 2019: Uribe causes associate to pay off Nadine’s loan through bank in the Bronx.
May 21, 2019: Menendez, Hana, and Egyptian Official-3 meet twice, the second time at steakhouse in DC. They discuss human rights issue. Hana requests Menendez’ intervention on USDA objections to IS EG Halal monopoly.
May 22 and 23, 2019: Hana provides Nadine information on USDA objections. She texts them to Menendez, and later deletes them.
May 23, 2019: Menendez intervenes with USDA Official-1, asking him to stop interfering with IS EG Halal’s monopoly. Official-1 did not accede to demand, but IS EG Halal kept monopoly.
June 2019: Nadine forms Strategic International Business Consultants, LLC, explaining to a relative she would use it to get paid. “Every time I’m in a middle person for a deal I am asking to get paid and this is my consulting company.”
July 2019: After mortgage company moves to foreclose on Nadine, IS EG Halal pays $23,000 to bring Nadine’s mortgage current. As part of those discussions, Nadine said, “When I feel comfortable and plan the trip to Egypt [Hana] will be more powerful than the president of Egypt.” [DOJ does not allege Menendez was part of this discussion.]
July 2019: A New Jersey detective asks to interview Uribe’s associate, leading Menendez to attempt to intervene again.
July 31, 2019: Uribe contacts Nadine saying “We need to move fast” … “We can stop this.” Nadine responds that she will “address itfirst thing tomorrow morning or tonight depending on when he is home.” Menendez does Google search on State agency employing insurance fraud investigator.
August 30, 2019: IS EG Halal pays Nadine $10,000.
September 3, 2019: Uribe texts Nadine saying, “Please don’t forget about me. I will never forget about you” … “I need peace.”
September 4, 2019: Menendez sets up meeting with NJ prosecutor for September 6.
September 5, 2019: Menendez, Nadine, and Uribe meet at Nadine’s house.
September 5, 2019: Nadine sends Uribe a text sent through cell tower in Manhattan.
September 6, 2019: Prosecutor meets with Menendez, Menendez informs Uribe the meeting was “very positive.”
September 9, 2019: Egyptian Official-3 texts Hana relaying that a State Department official told an Egyptian diplomatic official that “Senator Menendize put a hold on a billion $ of usaid to Egypt before the recess !!!!” Hana attempted to contact Nadine, then forwarded the Egyptian text to Daibes, who called Menendez and then responded that it wasn’t true.
September 2019: Menendez offered to provide assistance to Hana and Egypt during official trip to India, then later meets with Daibes, Hana, and Egyptian Official-3.
September 2019: Nadine complains to Daibes that Hana had not paid her. Daibes responds, “Nadine I personally gave Bob a check for September.”
September 2019: Nadine texts Menendez complaining that Hana has not left her an envelope, referencing a meeting Menendez had with senior Egyptian officials “last Saturday.” Nadine called Daibes.
September 21, 2019: Menendez, Hana, Daibes, and Egyptian Official-4 meet at restaurant in Manahattan.
September 28, 2019: IS EG Halal pays Nadine $10,000.
October 2019: Menendez and Nadine get engaged.
October 29, 2019: Uribe texts Nadine for an update. Menendez calls Uribe, after which he tells Nadine he is “a very happy person.”
After October 29, 2019: Menendez, Nadine, Uribe, and associate have celebratory dinner.
November 5, 2019: Uribe texts Nadine about automatic payments for Mercedes Benz.
November 5, 2019: IS EG Halal pays Nadine $10,000.
November 9, 2019: Uribe sets up automatic payments through another trucking company, ultimately paying $30,000 in addition to the cash down payment.
November 2019: Search of Hana’s cell phone reveals thousands of text messages with Nadine, many of which she had deleted.
March 2020: Nadine texts Egyptian Official-3 and offers to help, then setting up meeting with “the general,” after which Menendez intervenes to pressure State to increase its engagement on Grand Ethiopian Renaissance Dam.
October 2020: Menendez, Nadine, Egyptian Official-3 ,and Egyptian Official-4 meet for dinner in Edgewater, NJ.
October 2020: Menendez and Nadine get married.
December 2020: Menendez and Nadine have dinner meeting with Egyptian Official-3.
December 2020: Menendez meets with US Attorney candidate and complains about prosecution of Fred Daibes. US Attorney candidate tells Menedez he might have to recuse. Menendez told US Attorney candidate he would not recommend him.
Early 2021: IS EG Halal delivers two exercise machines and air purifier to Menendez home.
May 2, 2021: Advisor intervenes with US Attorney candidate about recusing, tells Menendez “you’ll be comfortable with what he says.” Menendez recommends candidate. After confirmation, he recuses.
June 21, 2021: Nadine and Egyptian Official-4 organized meeting between Menendez and Egyptian Intelligence Head Abbas Kamel, in advance of meeting with other Senators that day. Both Nadine and Menendez alert Egyptian Official-4 that other Senators were going to raise a human rights issue. Per this thread (ThreadReader is down right now but it’s here) and this Isikoff story, the human rights issue was Egypt’s involvement in the execution of Jamal Khashoggi.
June 23, 2021: Hana purchases 22 one ounce gold bars, each worth $1,800. Two were found at Menendez residence in June 2022 search.
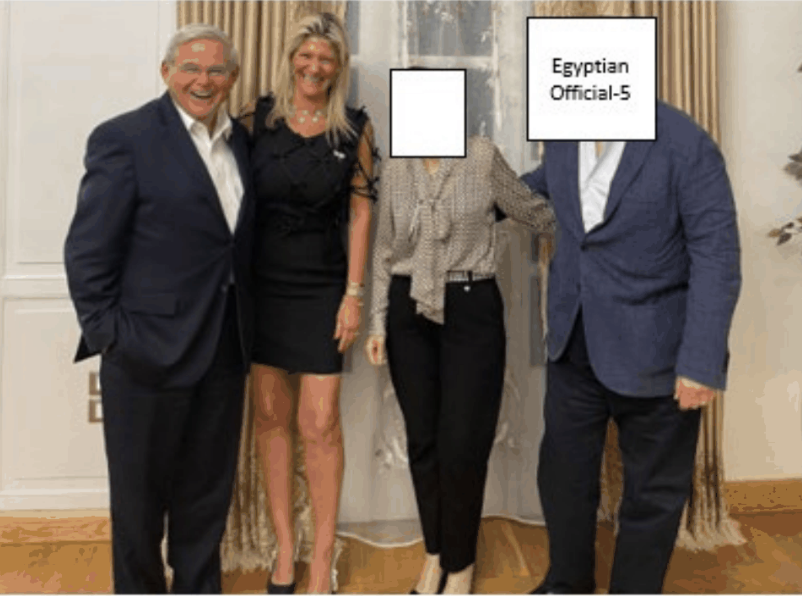
October 2021: Nadine arranges trip for her and Menendez to Egypt, originally planned as unofficial visit. When a SFRC took steps that made it an official visit, Egyptian Official-4 said he might lose his job. During the trip, Menendez had meeting at home of Egyptian Official-5 (the intelligence official).
October 17, 2021: Driver for Fred Daibes picks up the Menendezes from trip to Egypt; the next day Menendez searches, “how much is one kilo of gold worth.”
December 23, 2021: Daibes’ trial adjourned. Daibes asks about Menendez’ shoulder injury. Nadine responds that Menendez is fixated on trial date. Daibes sent recliner to Menendez.
December 2021 through February 2022: Menendez asks Advisor to ask why US Attorney recused himself.
January 2022: Menendez sends Nadine a link about military sales to Egypt totally $2.5 billion; Nadine forwards ot Hana, saying that Menendez had to sign off on it.
January 21, 2022: Menendez called NJ US Attorney and asked for First AUSA name.
January 22, 2022: Menendez complains to Daibes that his attorney has not been aggressive enough.
January 24, 2022: Nadine has two calls with Daibes’ driver. “Christmas in January.” Thousands in cash with Daibes’ DNA later found at residence.
January 29, 2022: Menendez searches for “kilo of gold price.”
January 31, 2022; Menendez calls First AUSA, then calls Daibes.
March 2022: Menendez asks Advisor to bring up Daibes at lunch with US Attorney, Advisor declines to do so.
March 30, 2022: Nadine thanks Daibes, then sells 2 1-KG gold bars to jeweler, each worth $60,000.
March 31, 2022: Two 1-KG gold bars Nadine provided to jeweler sold in Manhattan.
April 2022: Daibes pleads guilty to plea agreement providing probationary sentence. Sentencing has been continued repeatedly since plea.
June 2022: Federal agents approach Menendez, Nadine, and Uribe, after which Menendez pays Nadine $23,000 and Nadine pays Uribe $21,000.
June 16, 2022: Search discovers:
- 2 1-KG gold bars
- 9 1-ounce gold bars
- 10 envelopes of cash, each with 10s of 1000s of dollars, bearing Daibes’ fingerprints, one which included fingerprints of Menendez
July 14, 2023: Sentencing for Daibes and co-defendant reset, for fourth time, for October 23, 2023.
September 21, 2023: DOJ amends sentencing agreement to note that Phil Sellinger was recused and Vikas Khanna oversaw the Daibes prosecution.
September 21, 2023: Indictment