You’ve no doubt seen the conspiracy theory championed by Tucker Carlson and Glenn Greenwald claiming that the unnamed Oath Keeper associates described in those indictments are actually FBI informants.
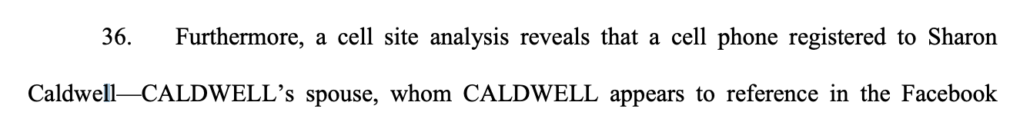
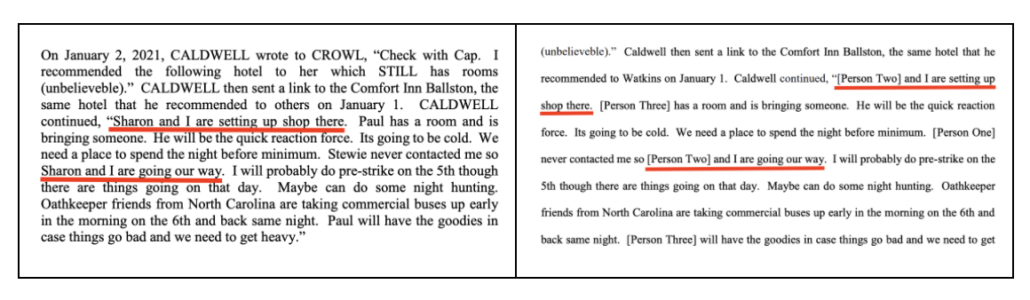
As happened with earlier propaganda campaigns (notably the one downplaying Brian Sicknick’s death), the conspiracy theory started with Revolver News, got magnified by Tucker Carlson, and got normalized by Glenn Greenwald (the latter of whose central role largely escaped attention because commentators don’t identify him, yet, as a right wing propagandist).In his first appearance, Carlson grotesquely accused Sharon Caldwell, who was described in later Oath Keeper documents as Person Two but was identified clearly in earlier documents by her first name and as Thomas Caldwell’s spouse, of being an informant who framed her husband.
Person Two and Person Three were organizers of the riot. The government knows who they are. But the government has not charged them. Why is that? You know why. They were almost certainly working for the FBI. So FBI operatives were organizing the attack on the Capitol on January 6, according to government documents. And those two are not alone! In all Revolver News reported there were, quote, “upwards of 20 unindicted co-conspirators in the Oath Keepers indictments, all playing various roles in the conspiracy, who have not been charged for virtually the exact same activities — and in some cases much, much more severe activities — as those named alongside them in indictments.”
Huh????
So it turns out that this white supremacist insurrection was, again, by the government’s own admission in these documents organized at least in part, by government agents.
This little campaign has led compromised members of Congress to embrace this excuse for the insurrection they previously have claimed was not an insurrection at all.
Thomas Caldwell’s wife, Sharon, is Person Two
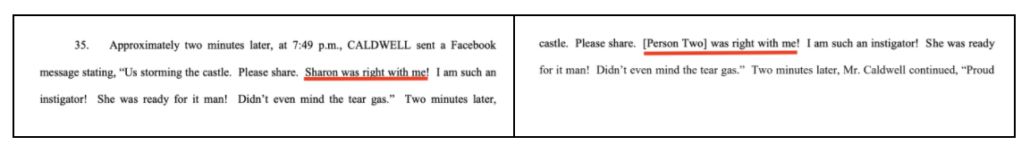
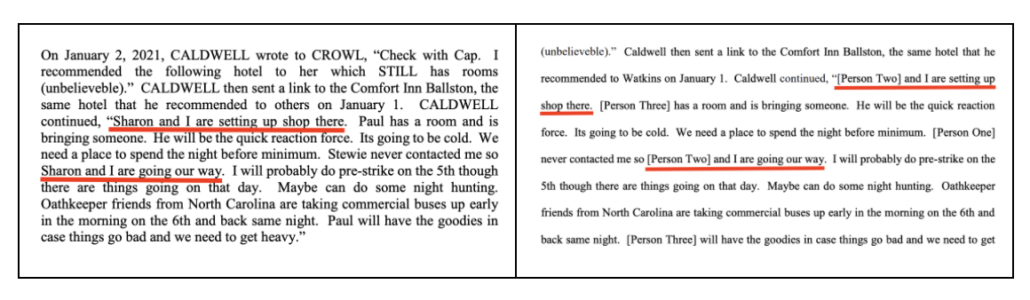
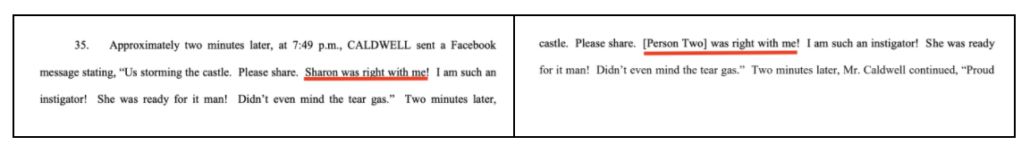
To show that “Person Two,” whom Tucker Carlson alleges for framing Thomas Caldwell, is actually his wife, Sharon, you can compare this filing, where her name is not redacted, with this one, where “Person Two” has substituted for her name.
1. Sharon Caldwell is Thomas’ wife:
2. “Sharon and I are setting up shop there” (at the Comfort Inn Ballston) and then “Sharon and I are going our way.”
3. “Sharon was right with me!”
Later filings over release conditions confirm the selfies posted to Facebook were of Thomas’ wife, describe Thomas agreeing to be accompanied by his wife, Sharon, to Sunday Mass starting on Easter, expressing concern that his wife has to do all the chores on their 30-acre farm which has led to the loss of farm income, and describing that he rarely travels anywhere without his wife, Sharon Caldwell, and she’s willing to go with him every time he does leave their property.
Glenn and Tucker must be outraged that Billy Barr set up Antifa
Parts of this campaign are pathetic, even for the men involved, and may reflect a desperate attempt to repackage their own past claims.
For example, after parroting a bunch of obviously self-serving PR from Parler in the days after the attack (such as that the insurrectionists organized on Facebook, not Parler), Glenn now shows that Parler was actually sharing threats of violence with the FBI in advance, without noting that that undermines several things he said in the past, such as that the insurrectionists didn’t plan on Parler. This must be dizzying and embarrassing for Glenn.
And because Glenn has to package this — like he did his never-ending obsession with Hunter Biden’s laptop — as a failure of Democrats and liberal media, he remarkably claims that the left — which has so relentlessly asked why the FBI was caught unawares that Glenn even screen caps an example of Ryan Goodman linking to Carolyn Maloney doing so — is resistant to questioning the FBI’s role in the riot.
What accounts for this furious liberal #Resistance to questioning the FBI’s role in the January 6 riot and asking whether there are vital facts that are being concealed?
Maybe Glenn has a harder time getting CSPAN in Brazil than I do in Ireland, because when I’ve watched the multiple hearings Democratic Chairs of various committees (including Maloney) have had with FBI Director Chris Wray or now-National Security Branch EAD Jill Sanborn, they question the FBI about it over and over and over. Glenn literally made up this hash-tagged resistance out of thin air because he needs it to be true, when in fact the opposite is true.
But it’s important to look at what this propaganda campaign obscures.
Probably, this campaign got started because a number of people implicated in the investigation, now realizing that it won’t go away, are trying to absolve themselves of any responsibility. It has already happened with those charged for crimes committed on January 6. Dominic Pezzola suggested that a key witness against him was actually more involved in the riot than he was, only to learn he guessed wrong and that the government was going to invoke a terrorism enhancement with him. Similarly, top Proud Boys were hinting at challenges to the UCC-1 described in their indictment, before they grew conspicuously silent about it, as if they learned something that undercut such claims. [see update below]
The other reason people are talking about informants is that (FBI’s failure to respond notwithstanding) it’s not that far-fetched. Importantly, multiple Proud Boys have claimed to be informants, though Glenn only mentions Enrique Tarrio. Maybe that’s because the implication of the claims from the others leads to a place Glenn and Tucker don’t want to go. Of the four Proud Boys that Aram Rostom described as being FBI informants prior to January 6, three claimed to be sharing information about Antifa.
Reuters interviewed two Proud Boys members who spoke on the condition of anonymity about some members’ interactions with the FBI. Reuters also interviewed Proud Boys leader Enrique Tarrio, examined court records and interviewed sources close to the federal investigation.
The reporting showed:
– One Proud Boy left the group in December after telling other members he was cooperating with the FBI by providing information about Antifa, say Tarrio and two other Proud Boy sources. The former member, whom Reuters was unable to identify, insisted to group leaders that he had not revealed information about the Proud Boys, these people say.
– A second Proud Boy leader bragged in 2019 about sharing information with the FBI about Antifa, according to private chats leaked on social media. The chats’ authenticity was confirmed by a source familiar with the Proud Boys and the Jan. 6 case.
– A third Proud Boy leader, Joseph Biggs, who was indicted and charged with conspiracy in the January attack, has said in court papers he reported information to the FBI about Antifa for months. Reuters spoke to Biggs two days before the riot. In that interview, he said he had specific plans for Jan. 6, but declined to disclose them. But, he volunteered to Reuters in that call, he was willing to tell his FBI contact of his plans for the coming rally, if asked. Reuters wasn’t able to determine whether such a contact took place. [my emphasis]
What this suggests is not that the FBI set up the Proud Boys with paid informants, but the opposite: that under a President who “denounced” the Proud Boys by saying they should “Stand back and stand by,” and under an Attorney General who dismissed threats against a judge involving the Proud Boys as a technicality, the Proud Boys were viewed not as an equivalent (or greater) threat than Antifa, but instead were able to disguise their use of Antifa as a foil to sow violence by serving as informants against them.
If these three self-proclaimed informants are right (there’s good reason to doubt them), then it means under Bill Barr, the FBI was using informants not to set up the Proud Boys, but instead to set up Antifa.
If Tucker and Glenn were good faith actors and not paid propagandists, you would fully expect them to be outraged that the FBI set up Antifa.
Especially because of the possibility that the FBI didn’t take the Proud Boys threat seriously because (on top of being endorsed by the President and downplayed by the Attorney General), they prioritized investigating Antifa over investigating the Proud Boys. With that possibility in mind, read the framing of Glenn’s Substack post:
The original report, published by Revolver News and then amplified by Fox News’ Tucker Carlson, documented ample evidence of FBI infiltration of the three key groups at the center of the 1/6 investigation — the Oath Keepers, the Proud Boys, and the Three Percenters — and noted how many alleged riot leaders from these groups have not yet been indicted. While low-level protesters have been aggressively charged with major felonies and held without bail, many of the alleged plot leaders have thus far been shielded from charges.
The implications of these facts are obvious. It seems extremely likely that the FBI had numerous ways to know of any organized plots regarding the January 6 riot (just as the U.S. intelligence community, by its own admission, had ample advanced clues of the 9/11 attack but, according to their excuse, tragically failed to “connect the dots”).
[snip]
What would be shocking and strange is not if the FBI had embedded informants and other infiltrators in the groups planning the January 6 Capitol riot. What would be shocking and strange — bizarre and inexplicable — is if the FBI did not have those groups under tight control.
It is fucking insane that Glenn claims to be mystified by the possibility that a group endorsed in the President’s first Presidential debate and dismissed by the Attorney General would not get the proper scrutiny by the FBI. Trump very effectively punished people — especially at the FBI — for investigating entities close to him. And on September 29, 2020, Donald Trump made it quite clear the Proud Boys should get special treatment. That’s all the explanation you need. Though it is, indeed, reason for closer scrutiny, the kind of scrutiny that Democrats have been demanding, Glenn’s false claims to the contrary notwithstanding.
But if you want to raise the possibility that FBI had informants in the group, then the explanation may be equally as damning: That the FBI didn’t see January 6 coming because it was too busy treating Antifa as a terrorist threat.
Indeed, everything we know about the threat reporting on that day — which claimed the big risk of violence arose from the possibility of clashes between counter-protestors and right wing militias — suggests that may be what happened: that the FBI was looking the other way, possibly in conjunction with the militia that played a key role in planning the attack. That certainly accords with Acting Secretary of Defense Christopher Miller’s claim that Trump told him to use the National Guard to protect Trump supporters.
Since Glenn claims to be very familiar with the role of informants, surely he knows that multiple terrorists — definitely David Headley and allegedly Tamerlan Tsarnaev and Omar Mateen — have planned attacks under the cover of serving as informants (or in the case of Mateen, his father doing so). There were also at least two former FBI informants that played key parts in the Russian operation in 2016. The most logical answer to the questions that Glenn pretends to entertain is that the FBI didn’t look too closely at what Joe Biggs was planning (as part of a Kelly Meggs-brokered Florida alliance of militia groups with ties to Roger Stone), because they treated him as a credible source of reporting on Antifa.
The propaganda that goes unnoticed
The absurdity of accusing Sharon Caldwell of entrapping her spouse has, justifiably, gotten all the attention from this campaign.
But there’s a piece of propaganda that it incorporates — one parroted by Members of Congress — that deserves focus of its own: in framing his piece, Glenn not only claims that the plot leaders have been shielded from charges, he also states as fact that, “low-level protesters have been aggressively charged with major felonies and held without bail.”
While low-level protesters have been aggressively charged with major felonies and held without bail, many of the alleged plot leaders have thus far been shielded from charges.
In making this claim, Glenn is mindlessly parroting something that appears in the original Revolver piece.
The first category is the group of mostly harmless tourists who walked through already opened doors and already-removed barricades, and at most were guilty of minor trespassing charges and light property offenses. The second group consists of those who were violent with police officers, broke down barricades, smashed windows, belonged to a “militia” group engaged in military-style planning prior to the event, discussed transporting heavy weaponry, and so forth.
Up until now, the overwhelming (perhaps exclusive) share of counter-establishment reporting on 1/6 has focused on absolving the first group. And this is a valuable thing. The notion that these harmless “MAGA moms” wandering around the Capitol were domestic terrorists engaged in an insurrection is absurd. That many of these people are being held in prison, without bail, under harsh conditions, amounts to an unacceptable and outrageous abuse of basic human rights.
The only way to sustain a claim that “low-level protestors” have been charged with major felonies and held without bail is to claim that alleged plot leaders — people like Ethan Nordean, Joe Biggs, Billy Chrestman, and Kelly Meggs — were actually just protestors.
That’s because with perhaps two exceptions (people like Karl Dresch whose criminal records were cited as the reason for their detention), the only people who remain in jail are either those charged with planning the insurrection, or people who engaged in violence or came armed. And even many of those people were released. Just going in alphabetical order, Christopher Alberts brought a gun and a magazine to the insurrection but was released on bail. John Anderson is accused of assault but is out on bail. Richard Barnett, who entered Nancy Pelosi’s office with a high voltage stun gun, was initially jailed but has since been released. Bradley Bennett, whom the government argued went on the lam for weeks and destroyed his phone, got released on bail. Craig Bingert, involved in one of the conflicts with cops at a barricade, was released on bail. Gina Bisignano, accused of inciting violence and destruction with a bullhorn, was released on bail. Joshua Black, who was involved in confrontations with cops before heading to the Senate Chamber and said God ordered him to riot, was released on bail. James Breheny, an Oath Keeper who allegedly lied to the FBI and attended a key inter-militia planning event, is out on bail. Both men who brought zip ties to the Senate Chamber on the day of the riot, Eric Munchel and Larry Brock, are out on bail (and Brock isn’t even charged with a felony).
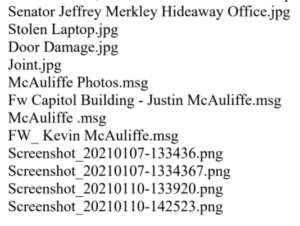
Even Brandon Fellows, charged with obstruction and present when Jeff Merkley’s office was trashed and laptop stolen, thus far remains out on bail, even after several bail violations.
Perhaps the only two people who remain in custody who weren’t either associated with a group being treated as a militia or involved in assault are Doug Jensen and Jacob Chansley. Both, though, played a kind of leadership role during the attack, both brought blades with them to the insurrection, both had direct confrontations with cops, and the government has argued (Jensen, Chansley) both exhibit the kind of fervor in their QAnon beliefs that pose a particular danger.

Given that QAnon had better success placing bodies where they were useful during the insurrection, I’m not sure it even makes sense to treat them differently than the more traditional militia.
Other than that, the men detained pre-trial are accused of leading the insurrection, precisely the people that this conspiracy theory falsely claims have been shielded from charges. Among the Proud Boys, Ethan Nordean, Joe Biggs, Charles Donohoe, Zack Rehl, and Kansas City cell leader Billy Chrestman remain jailed. Among the Oath Keepers, Kelly Meggs, Kenneth Harrelson, and Jessica Watkins remain jailed. All are accused of playing key leadership roles in the insurrection.
There were some questionable detention decisions early on. At this stage, however, there are no cases where people still detained are simply protestors on the wrong side of the law.
And yet even Glenn makes that false claim without any evidence.
Donald Trump’s FBI Director and Bill Barr’s hand-picked US Attorney called these defendants terrorists
There’s one more aspect of this conspiracy that is confounding.
Tucker Carlson and Glenn Greenwald suggest this is a Deep State plot to harm Trump and his supporters. Even Andrew McCarthy, who wrote a long and worthwhile piece debunking Tucker and Glenn’s conspiracies, nevertheless claims the prosecutorial decisions in this case reflect Democratic politicization.
Although Schaffer is plainly a member of the Oath Keepers conspiracy, the Biden Justice Department did not have him plead guilty to the conspiracy charge in the Oath Keepers indictment. That’s undoubtedly because, for the purposes of helping Democrats hype a white-supremacist terrorism narrative, the conspiracy charge is too minor. Although that charge has been portrayed by the media and the Justice Department as if it were a terrorism allegation, it actually involves a statute that criminalizes comparatively minor conspiracy offenses, fit for a maximum penalty of just five years’ imprisonment (with the possibility of no jail time at all).
So instead, DOJ had Schaffer plead guilty to a two-count criminal information, charging him with the substantive crimes of obstructing Congress and illegally carrying a dangerous weapon (bear spray) on restricted federal grounds. That allowed government officials to bray that Schaffer could be looking at 30 years in prison, which sure sounds a lot worse than five years. But it’s a feint. The 30-year level is just an aggregation of the maximum sentences prescribed by the two statutes in Schaffer’s guilty plea — i.e., the highest possible sentence that could potentially apply to anyone who violated these laws. The sentence a judge actually imposes within that 30-year range depends on the circumstances, with only the worst offenders getting the maximum sentence. Realistically, then, what matters in Schaffer’s case are the federal sentencing guidelines that apply specifically to him. In the plea agreement’s fine print, prosecutors concede that the guidelines call for a relatively paltry 41- to 51-month term, which may be reduced if his cooperation proves to be valuable.
I suspect that Schaffer is one of the unnamed, numbered “Persons” referred to in the Oath Keepers indictment.
[snip]
To be clear, Carlson is right that it is ridiculous for Attorney General Merrick Garland to portray the Capitol riot as if it were a terrorist attack and the people behind it as the most dangerous national-security threat we face. As noted above, the conspiracy allegation is not a terrorism charge: It carries a penalty of no more than five years. Carlson is right to point out that, despite the government’s and the media’s claims to the contrary, there is no indication that racism motivated the riot (the Oath Keepers, for example, are not a white-supremacist organization, and the indictment does not even hint that race had anything to do with January 6). Carlson is right that, even as congressional Democrats posture about the supposed need for a commission to fully expose the events of January 6, the government is withholding mounds of information — including the identity of the security official who killed rioter Ashli Babbitt, a concealment that would be unfathomable in a case where a police officer killed an African-American criminal suspect or a Black Lives Matter rioter. And Carlson was right to call out the ludicrous suggestion by Frank Figliuzzi, a former top FBI national-security official, that congressional Republicans who cynically supported Trump’s scheme to overturn the election result are the equivalent of a terrorist organization’s “command and control element.”
Christopher Wray — the FBI Director chosen by Donald Trump — has, from day one, called this a terrorist attack.
More importantly, the person leading this investigation for the first two months was the US Attorney Bill Barr installed with no input from Congress, Michael Sherwin. If Sherwin had his way, these people would be charged with seditious conspiracy. Under Sherwin, Proud Boy Dominic Pezzola’s crimes were labeled terrorism. Under Michael Sherwin, Jessica Watkins’ crimes were labeled terrorism. And while the Jon Schaffer cooperation agreement that McCarthy disdains was finalized after Sherwin left, signs of it were already evident before Sherwin left (note, McCarthy is probably wrong in his belief that Schaffer is one of the people identified thus far in the Oath Keepers conspiracy, and he misunderstands why prosecutors charged Schaffer like the did). A Sherwin-friendly article written after his departure quotes him stating these were not close cases (and also taking credit for making the bulk of the cases).
“These were not complicated cases,” Sherwin said of the Capitol breach probe. “What made these cases so unusual were the scope and scale of the crime,” reaching into almost every state in the country, including Florida.
Sherwin’s tour of duty as acting U.S. Attorney ended soon after the Biden administration took over the Justice Department. He was asked to stay on as the lead prosecutor in the Capitol breach probe, but Sherwin said it was time to move on after making the bulk of the cases in the investigation.
If you have a problem with the way this investigation unfolded, you have a problem not with Joe Biden’s DOJ, but instead with the guy Bill Barr installed into a politicized US Attorney role with no input from Congress.
Which may be why those who need to downplay the seriousness of the attack have instead resorted to baseless conspiracy theories.
Update: Because some dead-enders still don’t believe that Tucker Carlson has accused Sharon Caldwell of entrapping her husband Thomas, I’ve done an entire section showing how the same references to Person Two in a later filing show up as Thomas’ wife Sharon in an earlier one. I also describe all the efforts Sharon is making to keep her husband out of jail.
Update, July 25: Above, I noted that the Proud Boy leaders seem to have learned something that sated their curiosity about whether UCC-1 was an FBI informant. Indeed they did. At a recent hearing, one of the AUSAs on the case revealed that they had been provided this person’s identity and confirmation he was not an informant.
Several more relevant updates: First, Larry Brock has since been charged with obstruction, a felony, but remains out on bail. Doug Jensen, one of the last remaining people who wasn’t either a leader or charged with assault still being detained, was released on bail. Michael Curzio, one of just a few exceptions who got jailed because of past crimes, got released after serving a six month time served sentence for his misdemeanor trespass charge. Two non-violent defendants — Brandon Fellows and Thomas Robertson — have since had pretrial released revoked for violating their conditions.
Finally, the friend of former DEA officer Mark Ibrahim — who may himself serve as an FBI informant — not only debunked Ibrahim’s excuse for being at the insurrection, but made it clear that the FBI did not formally ask him to attend the event.
IBRAHIM said he went along with his friend, who had been asked by the FBI to document the event, and that he went along with his friend to assist with that effort.
Your affiant also interviewed IBRAHIM’s friend. According to the friend, IBRAHIM crafted this story about how his friend was at the Capitol to assist the FBI and that IBRAHIM was there helping him. IBRAHIM’s friend told your affiant that he was not there in any formal capacity for the FBI and that the FBI was not giving him directions or marching orders. He said that IBRAHIM crafted this story in an effort to “cover his ass.” According to IBRAHIM’s friend, IBRAHIM went to the rally in order to promote himself—IBRAHIM had been thinking about his next move after leaving the DEA and wanted the protests to be his stage for launching a “Liberty Tavern” political podcast and cigar brand.
Ibrahim, who brought another of the guns that Glenn claims no one brought to January 6 and displayed it publicly, is out on bail.