I’ve been home from Europe for less than a day and already I’m thinking of sporting a neck collar for the whiplash I’ve gotten watching the wildly varying Jim Comey opinions.
I’m speaking, of course, of the response to Jim Comey’s highly unusual announcement to sixteen Chairs and Ranking Members of congressional committees (at least some of which Comey did not testify to) that the investigative team — presumably on the Clinton case — briefed him Thursday that FBI discovered additional emails in an unrelated case — now known to be the investigation into Anthony Weiner allegedly sexting a 15 year old — and he approved their request to take the steps necessary to be able to review those emails.
Effectively, the Weiner investigators, in reviewing the content from devices seized in that investigation, found emails from Huma Abedin, told the Hillary investigative team, and they’re now obtaining a warrant to be able to review those emails.
So of course the Republicans that had been claiming Comey had corruptly fixed the investigation for Hillary immediately started proclaiming his valor and Democrats that had been pointing confidently to his exoneration of Hillary immediately resumed their criticism of his highly unusual statements on this investigation. Make up your minds, people!
For the record, I think his initial, completely inappropriate statements made this inevitable. He excuses Friday’s statement as formally correcting the record of his testimony. The claim is undermined by the fact that not all recipients of the letter had him testify. But I think once you start the process of blabbing about investigations, more blabbing likely follows. I don’t mean to excuse this disclosure, but the real sin comes in the first one, which was totally inappropriate by any measure. I’m also very unsympathetic with the claim — persistently offered by people who otherwise cheer Comey — that he released his initial statement to help Loretta Lynch out of the jam created by her inappropriate meeting with Bill Clinton; I think those explanations stem from a willful blindness about what a self-righteous moralist Comey is.
Of course I’ve been critical of Comey since long before it was cool (and our late great commenter Mary Perdue was critical years before that).
But I’d like to take a step back and talk about what this says about our judicial system.
Jim Comey doesn’t play by the rules
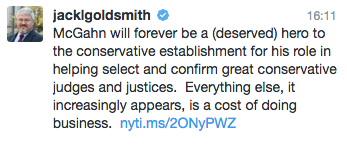
Jamie Gorelick (who worked with Comey when she was in DOJ) and Larry Thompson (who worked with Comey when Comey was US Attorney and he was Deputy Attorney General, until Comey replaced him) wrote a scathing piece attacking Comey for violating the long-standing prohibition on doing anything in an investigation pertaining to a political candidate in the 60 days leading up to an election. The op-ed insinuates that Comey is a “self-aggrandizing crusader[] on [a] high horse” before it goes on to slam him for making himself the judge on both the case and Hillary’s actions.
James B. Comey, put himself enthusiastically forward as the arbiter of not only whether to prosecute a criminal case — which is not the job of the FBI — but also best practices in the handling of email and other matters. Now, he has chosen personally to restrike the balance between transparency and fairness, departing from the department’s traditions. As former deputy attorney general George Terwilliger aptly put it, “There’s a difference between being independent and flying solo.”
But the real meat is that there’s a rule against statements like the one Comey made, and Comey broke it.
Decades ago, the department decided that in the 60-day period before an election, the balance should be struck against even returning indictments involving individuals running for office, as well as against the disclosure of any investigative steps. The reasoning was that, however important it might be for Justice to do its job, and however important it might be for the public to know what Justice knows, because such allegations could not be adjudicated, such actions or disclosures risked undermining the political process. A memorandum reflecting this choice has been issued every four years by multiple attorneys general for a very long time, including in 2016.
If Comey is willing to break this rule in such a high profile case, then what other rules is he breaking? What other judgements has Comey made himself arbiter of? Particularly given Comey’s persistent discussion of FBI’s work in terms of “good guys” and “bad guys” — as opposed to criminal behavior — that seems a really pertinent question.
As with James Clapper, Loretta Lynch can’t control Comey
Gorelick (who has been suggested among potential Clinton appointees) and Thompson go easier on Lynch, however, noting that she didn’t order him to stand down here, but ultimately blaming Comey for needing to be ordered.
Attorney General Loretta E. Lynch — nominally Comey’s boss — has apparently been satisfied with advising Comey but not ordering him to abide by the rules. She, no doubt, did not want to override the FBI director in such a highly political matter, but she should not have needed to. He should have abided by the policy on his own.
But since John Cornyn confronted Lynch in March about who would make decisions in this case — “Everyone in the Department of Justice works for me, including the FBI, sir,” Lynch forcefully reminded Cornyn — it has been clear that there’s a lot more tension than the org chart would suggest there should be.
The NYT provides more details on how much tension there is.
The day before the F.B.I. director, James B. Comey, sent a letter to Congress announcing that new evidence had been discovered that might be related to the completed Hillary Clinton email investigation, the Justice Department strongly discouraged the step and told him that he would be breaking with longstanding policy, three law enforcement officials said on Saturday.
Senior Justice Department officials did not move to stop him from sending the letter, officials said, but they did everything short of it, pointing to policies against talking about current criminal investigations or being seen as meddling in elections.
And it’s not just Lynch that has problems managing FBI.
In a response to a question from me in 2014 (after 56:00), Bob Litt explained that FBI’s dual role creates “a whole lot of complications” and went on to admit that the office of Director of National Intelligence — which is supposed to oversee the intelligence community — doesn’t oversee the FBI as directly.
Because FBI is part of the Department of Justice, I don’t have the same visibility into oversight there than I do with respect to the NSA, but the problems are much more complicated because of the dual functions of the FBI.
Litt said something similar to me in May when we discussed why FBI can continue to present bogus numbers in its legally mandated NSL reporting.
Now these are separate issues (though the Clinton investigation is, after all, a national security investigation into whether she or her aides mishandled classified information). But if neither the DNI nor the AG really has control over the FBI Director, it creates a real void of accountability that has repercussions for a whole lot of issues and, more importantly, people who don’t have the visibility or power of Hillary Clinton.
The FBI breaks the rules all the time by leaking like a sieve
Underlying this entire controversy is another rule that DOJ and FBI claim to abide by but don’t, at all: FBI is not supposed to reveal details of ongoing investigations.
Indeed, according to the NYT, Comey pointed to the certainty that this would leak to justify his Friday letter.
But although Mr. Comey told Congress this summer that the Clinton investigation was complete, he believed that if word of the new emails leaked out — and it was sure to leak out, he concluded — he risked being accused of misleading Congress and the public ahead of an election, colleagues said.
Yet the US Attorney’s Manual, starting with this language on prejudicial information and continuing into several more clauses, makes it clear that these kinds of leaks are impermissible.
At no time shall any component or personnel of the Department of Justice furnish any statement or information that he or she knows or reasonably should know will have a substantial likelihood of materially prejudicing an adjudicative proceeding.
Comey, the boss of all the FBI Agents investigating this case, had another alternative, one he should have exercised months ago when it was clear those investigating this case were leaking promiscuously: demand that they shut up, conduct investigations of who was leaking, and discipline those who were doing so. Those leaks were already affecting election year concerns, but there has been little commentary about how they, too, break DOJ rules.
But instead of trying to get FBI Agents to follow DOJ guidelines, Comey instead decided to violate them himself.
Again, that’s absolutely toxic when discussing an investigation that might affect the presidential election, but FBI’s habitual blabbing is equally toxic for a bunch of less powerful people whose investigative details get leaked by the FBI all the time.
[Update: Jeffrey Toobin addresses the role of leaks more generally here, though he seems to forget that the Hillary investigation is technically a national security investigation. I think it’s important to remember that, especially given Hillary’s campaign focus on why FBI isn’t leaking about the investigation into Trump’s ties to Russia, which would also be a national security investigation.]
Warrantless back door searches do tremendous amounts of damage
Finally, think about the circumstances of the emails behind this latest disclosure.
Reports are currently unclear how much the FBI knows about these emails. The NYT describes that the FBI seized multiple devices in conjunction with the Weiner investigation, including the laptop on which they found these emails.
On Oct. 3, F.B.I. agents seized several electronic devices from Mr. Weiner: a laptop, his iPhone and an iPad that was in large measure used by his 4-year-old son to watch cartoons, a person with knowledge of the matter said. Days later, F.B.I. agents also confiscated a Wi-Fi router that could identify any other devices that had been used, the person said.
While searching the laptop, the agents discovered the existence of tens of thousands of emails, some of them sent between Ms. Abedin and other Clinton aides, according to senior law enforcement officials. It is not clear if Ms. Abedin downloaded the emails to the laptop or if they were automatically backed up there. The emails dated back years, the officials said. Ms. Abedin has testified that she did not routinely delete her emails.
Presumably, the warrant to seize those devices permits the FBI agents to go find any evidence of Weiner sexting women (or perhaps just the young woman in question).
And admittedly, the details NYT’s sources describe involve just metadata: addressing information and dates.
But then, Comey told Congress these emails were “pertinent” to the Clinton investigation, and other details in reports, such as they might be duplicates of emails already reviewed by the FBI, suggest the Weiner investigators may have seen enough to believe they might pertain to the inquiry into whether Clinton and her aides (including Huma) mishandled classified information. Moreover, the FBI at least thinks they will be able to prove there is probable cause to believe these emails may show the mishandling of classified information.
Similarly, there are conflicting stories about whether the Hillary investigation was ever closed, which may arise from the fact that if it were (as Comey had suggested in his first blabby statements), seeking these emails would require further approval to continue the investigation.
The point, though, is that FBI would have had no idea these emails existed were it not for FBI investigators who were aware of the other investigation alerting their colleagues to these emails. This has been an issue of intense litigation in recent years, and I’d love for Huma, after the election, to submit a serious legal challenge if any warrant is issued.
But then, in this case, Huma is being provided far more protection than people swept up in FISA searches, where any content with a target can be searched years into the future without any probable cause or even evidence of wrong-doing. Here, Huma’s emails won’t be accessible for investigative purpose without a warrant (in part because of recent prior litigation in the 2nd Circuit), whereas in the case of emails acquired via FISA, FBI can access the information — pulling it up not just by metadata but by content — with no warrant at all.
[Update: Orin Kerr shares my concerns on this point — with the added benefit that he discusses all the recent legal precedents that may prohibit accessing these emails.]
This is a good example of the cost of such investigations. Because the FBI can and does sweep so widely in searches of electronic communications, evidence from one set of data collection can be used to taint others unrelated to the crime under investigation.
All the people writing scathing emails about Comey’s behavior in this particular matter would like you to believe that this issue doesn’t reflect on larger issues at DOJ. They would like you to believe that DOJ was all pure and good and FBI was well-controlled except for this particular investigation. But that’s simply not the case, and some of these issues go well beyond Comey.
Update: Minor changes were made to this post after it was initially posted.