NYT Keeps Downplaying Trump’s Past Retribution Tour
Charlie Savage, Maggie Haberman, and Jonathan Swan keep teaming up to write the same story over and over: A second Trump term is going to be bad … really bad.
Just some of these stories, in reverse order from Tuesday’s latest installment, are:
- October 31: If Trump Wins, His Allies Want Lawyers Who Will Bless a More Radical Agenda
- July 17: Trump and Allies Forge Plans to Increase Presidential Power in 2025
- June 21: Few of Trump’s G.O.P. Rivals Defend Justice Dept. Independence
- June 15: The Radical Strategy Behind Trump’s Promise to ‘Go After’ Biden
There are several aspects to these stories: a bid to eliminate civil service protections, a personalization of power, and the elevation of people who proved willing to abuse power in his first term: Russel Vought (who helped obstruct the Ukraine investigation), Stephen Miller, and Johnny McEntee (who even before January 6 was making a willingness to invoke the Insurrection Act a litmus test for hiring at DOD), and Jeffrey Clark.
The series, thus far, skirts the language of authoritarianism and fascism.
At the core of the stories is that Trump is going to use a second term for retribution, to which the June 15 article is dedicated.
When Donald J. Trump responded to his latest indictment by promising to appoint a special prosecutor if he’s re-elected to “go after” President Biden and his family, he signaled that a second Trump term would fully jettison the post-Watergate norm of Justice Department independence.
“I will appoint a real special prosecutor to go after the most corrupt president in the history of the United States of America, Joe Biden, and the entire Biden crime family,” Mr. Trump said at his golf club in Bedminster, N.J., on Tuesday night after his arraignment earlier that day in Miami. “I will totally obliterate the Deep State.”
These stories admit that Trump did some of this in his first term. But they describe a process of retribution by the guy who got elected — with abundant assistance from Maggie Haberman — on a platform of “Lock her up!,” who breached the norm of judicial independence 24 days into office when he asked Jim Comey to “let this” Mike Flynn “thing go,” as something that took a while to “ramp up.”
In his first term, Mr. Trump gradually ramped up pressure on the Justice Department, eroding its traditional independence from White House political control. He is now unabashedly saying he will throw that effort into overdrive if he returns to power.
Mr. Trump’s promise fits into a larger movement on the right to gut the F.B.I., overhaul a Justice Department conservatives claim has been “weaponized” against them and abandon the norm — which many Republicans view as a facade — that the department should operate independently from the president.
Yet even though Savage did some important reporting on some of this (reporting that was counterbalanced by Maggie’s central role in helping Trump obstruct criminal investigations), these pieces always vastly understate how much politicization Trump pulled off in his first term, and never describe how that politicization continues at the hands of people like Jim Jordan.
In the spring of 2018, Mr. Trump told his White House counsel, Donald F. McGahn II, that he wanted to order the Justice Department to investigate his 2016 rival, Hillary Clinton, and James B. Comey Jr., the former head of the F.B.I. Mr. McGahn rebuffed him, saying the president had no authority to order an investigation, according to two people familiar with the conversation.
Later in 2018, Mr. Trump publicly demanded that the Justice Department open an investigation into officials involved in the Russia investigation. The following year, Attorney General William P. Barr indeed assigned a Trump-appointed U.S. attorney, John Durham, to investigate the investigators — styling it as an administrative review because there was no factual predicate to open a formal criminal investigation.
Mr. Trump also said in 2018 and 2019 that John F. Kerry, the Obama-era secretary of state, should be prosecuted for illegally interfering with American diplomacy by seeking to preserve a nuclear accord with Iran. Geoffrey S. Berman, a former U.S. attorney in Manhattan whom Mr. Trump fired in 2020, later wrote in his memoir that the Trump Justice Department pressured him to find a way to charge Mr. Kerry, but he closed the investigation after about a year without bringing any charges.
And as the 2020 election neared, Mr. Trump pressured Mr. Barr and Mr. Durham to file charges against high-level former officials even though the prosecutor had not found a factual basis to justify any. In his own memoir, Mr. Barr wrote that the Durham investigation’s “failure to deliver scalps in time for the election” eroded their relationship even before Mr. Barr refused Mr. Trump’s baseless demand that he say the 2020 election had been corrupt.
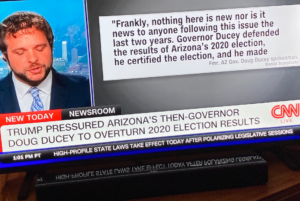
Where Mr. Trump’s first-term efforts were scattered and haphazard, key allies — including Jeffrey B. Clark, a former Justice Department official who helped Mr. Trump try to overturn the 2020 election — have been developing a blueprint to make the department in any second Trump term more systematically subject to direct White House control.
This effort was in no way haphazard!!! Most FBI personnel involved in the Russian investigation, from Jim Comey down to line analysts, had their careers systematically ruined, with Peter Strzok (who, the actual record of the Russian investigation shows, repeatedly took steps to protect Trump and Mike Flynn, even if he disliked Trump) offered up as an example of what will happen to people who don’t meekly just accept their punishment or, better yet, retreat to the private sector. The exceptions were the cyber guys who completely bolloxed the Alfa Bank investigation and people like Bill Barnett, who misrepresented the steps he himself took to provide “proof” of corruption on the Mueller investigation. That precedent has been sustained as right wingers take out other FBI agents deemed insufficiently loyal, like Tim Thibault, who personally opened an investigation into the Clinton Foundation in 2016 but who was targeted last year because in 2020 he didn’t mainline disinformation about Hunter Biden.
Yes, Bill Barr ordered Geoffrey Berman to investigate John Kerry. But he also set up a complex, systematic structure to halt any investigation into Rudy Giuliani so the President’s lawyer could get dirt from Russian spies, feed it to Scott Brady, who would then push that information into the investigations of Hunter Biden and others. When Berman and Jessie Liu refused to break (after a good deal of bending to Barr’s will), he fired them both.
Barr didn’t just pressure John Durham to prosecute high-level people: He skipped, hand-in-hand, with Durham as they used Russian intelligence to fabricate an attack on Hillary Clinton, the organizing logic of an investigation that swept up private sector people and who had the temerity to research Donald Trump or — worse!! — to help Hillary recover from a hack-and-leak. The effort even took out academic researchers who were simply trying to keep the US safe from Russian hacking. Trump did get DOJ to investigate Hillary, with investigations lasting the entirety of his presidency, and that investigation included precisely the kind of fabricated evidence and coached testimony that NYT imagines is a hypothetical left for Trump’s second term.
To the extent these stories talk about Trump’s pardons, they do so prospectively. There’s no discussion of how the pardons of Mike Flynn and Roger Stone rival any of the most corrupt in US history, but were necessary to prevent DOJ from developing proof that Trump conspired with Russia.
These articles don’t describe how Congress has served as a wing of this politicization, from the leaks to Mike Flynn in 2018 about how to undermine his own investigation to sham hearings — like the one with George Papadopoulos unencumbered by the documents that would have provide evidence of “collusion,” in which he spewed out conspiracy theories that Bill Barr and John Durham quickly got on a plane to chase. These articles don’t describe how the current unrelenting attempt to manufacture an impeachment out of the detritus of Hunter Biden’s life could not have happened if Bill Barr hadn’t made very systematic attempts to enable Trump’s retribution tour in 2020.
And these articles don’t describe the violent threats that have become routine for anyone deemed insufficiently loyal to Donald Trump. The threats Trump deployed against Lisa Page and Marie Yovanovitch — “she’s going to go through some things” — exist on an unrelenting continuum as the threats against Ruby Freeman and Lesley Wolf and Fani Willis and Don Bacon’s wife.
Yes, it’s important to warn about what Trump plans to do with a second term. But calling Trump’s past retribution “haphazard” is a journalistic cop-out, a way to avoid admitting that we don’t yet fully understand how systematic Trump’s past retribution was or — worse — don’t want to come to grips with our own central role in it.
For a warning to be effective, we have to show the human costs of all the past retribution — the thousands of Jan6ers who had their lives ruined, the significant degradation in US national security, the fear, especially the fear among Republicans — costs that no one, no matter how loyal, will ultimately escape.