On the Sessions and Trump Interviews: It’s Not Just Obstruction of Justice
There are two stories out (in addition to this piece I did for TNR) renewing the frenzy around the Mueller investigation.
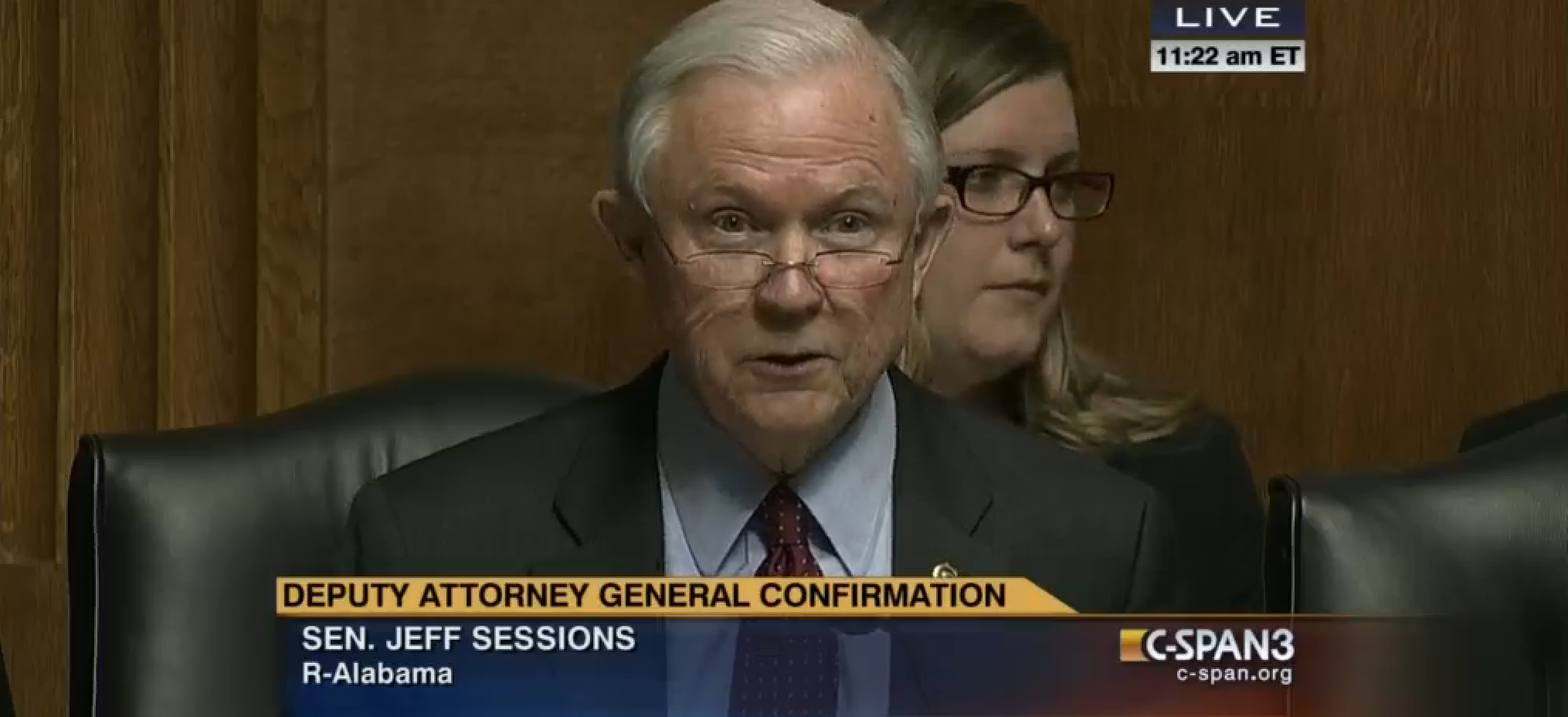
First, NYT reveals that Mueller interviewed Jeff Sessions for a few hours last week.
Attorney General Jeff Sessions was questioned for several hours last week by the special counsel’s office as part of the investigation into Russia’s meddling in the election and whether the president obstructed justice since taking office, according to a Justice Department spokeswoman.
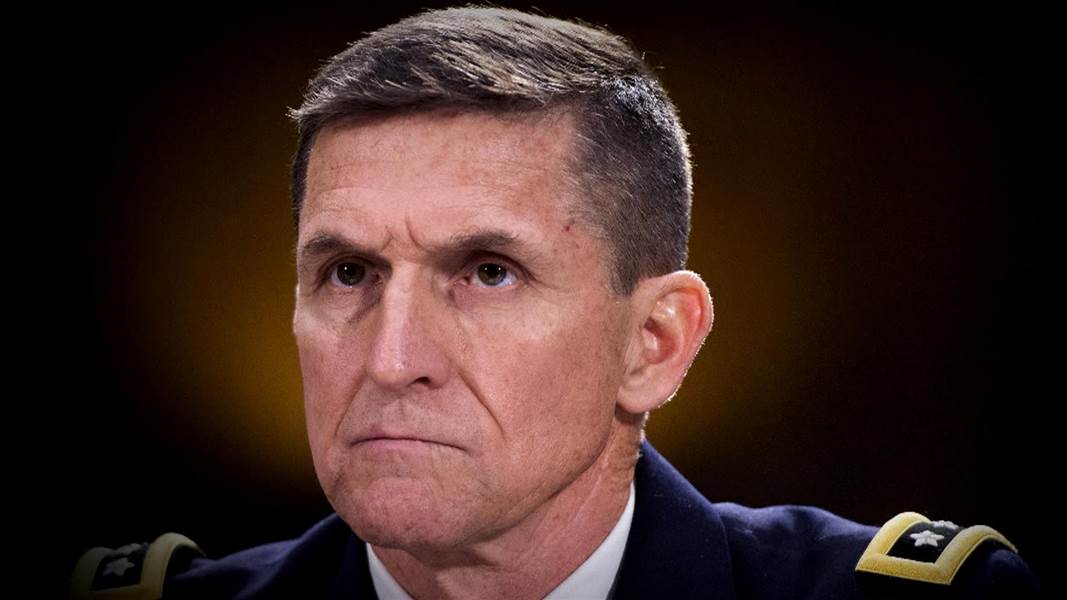
Then, WaPo reports that Mueller wants to interview Trump about the Mike Flynn and Jim Comey firings.
Within the past two weeks, the special counsel’s office has indicated to the White House that the two central subjects that investigators wish to discuss with the president are the departures of Flynn and Comey and the events surrounding their firings.
Commenters and the WaPo piece (which cites information that should only be available from a member of Trump’s legal team) suggest these developments mean Trump is looking at obstruction.
Mueller’s interest in the events that led Trump to push out Flynn and Comey indicates that his investigation is intensifying its focus on possible efforts by the president or others to obstruct or blunt the special counsel’s probe.
I’m sure obstruction absolutely is one of the things Mueller is assessing when interviewing Sessions and Trump.
But neither of these interviews, particularly not the Sessions one, is necessarily focused exclusively on obstruction.
Sessions, for example, was in a key early meeting where setting up a meeting between Putin and Trump was discussed (though Sessions claims he opposed the idea). I have noted, for example, how Sessions played dumb when asked whether he had any discussions about emails and that key Sessions aide Stephen Miller is a top candidate to have heard about emails from George Papadopoulos.
[I]t seems highly likely that on April 27 (or whenever Papadopoulos was next in DC), Miller learned that Russia had some kind of emails from Hillary.
[Stephen] Miller, recall, is Jeff Sessions’ close aide, his installment in the Administration. The NYT makes clear that Miller was interviewed by Mueller’s team recently, which means he was one of the people the government planned to interview just after locking in Papadopoulos’ plea.
Which makes this exchange from Jeff Sessions’ most recent congressional appearance, on October 18, all the more interesting. First, Patrick Leahy got the Attorney General to admit that there was a difference between not recalling something and affirmatively denying something. Leahy then pointed out that, once the meetings he had denied were disclosed, Sessions started not recalling certain things about the meetings that he had previous affirmatively denied.
Leahy: Later in March, when you did disclose such meetings, you said you could not recall what was said at the meetings. Your answer to my question was an emphatic no. It wasn’t, “I don’t recall.” You are a lawyer, I am a lawyer. You are, in fact, our nation’s top lawyer. Is there a difference between responding “no” and “I do not recall”?
Sessions: Yes.
Leahy: Thank you.
Sessions: Certainly it is, Senator Leahy.
Leahy: So if you could not recall, then you could not answer have answered my first question, yes or no, if later you said that you don’t recall what was discussed. The reason I ask is that, US intelligence intercepts reported in July that it would appear you did in fact discuss campaign issues with the Russian Ambassador.
Leahy then asked Sessions whether he had, since the election, had conversations with Russian officials about a slew of things, starting with emails. Sessions got even squirrelier than he normally is, and first attempted to answer a question Leahy didn’t ask.
Sessions: I have never had a meeting with any Russian officials to discuss any kind of coordinating campaign efforts.
So then Leahy asked about each item in turn.
Leahy: Let’s take this piece by piece. Did you discuss any of the following: Emails?
Sessions: Repeat the question again about emails.
Leahy: Since the 2016 campaign, have you discussed with any Russian connected official anything about emails?
Sessions: Discuss with them. I don’t recall having done any such thing.
Right after this exchange, Sessions totally balks when Leahy asks him if he has been interviewed or asked for an interview by Mueller, saying he should clear it with the Special Counsel.
Now, there was some imprecision in this questioning. It’s clear that Sessions believed he was answering the question about during the campaign, not since it.
But of the things Leahy asked about — emails, Russian interference, sanctions, or any policies or positions of the Trump campaign or presidency — Sessions ultimately not-recalled in response to just one question: the emails.
Based on the past practice Leahy had just laid out, Sessions claimed to not recall issues that he had actually done. Which would suggest Sessions is worried that there’s evidence he has discussed emails — with someone. It’s just not clear how he interpreted that question.
And while Trump’s firing of Comey after attempting him to drop the Flynn investigation is a key prong in any obstruction case, his role in Flynn’s non-firing is far more interesting, especially given the likelihood, given Republican efforts to claim privilege, that he was on the Mar-a-Lago side of orders directing Flynn to ask Sergey Kislyak to hold off on a response to Obama’s sanctions. While it’s certainly possible that Mueller may hold off on any examination of Trump’s personal role in any hypothetical quid pro quo with the Russians, there’s plenty of reason to believe Trump was in the loop.
And in early discussions about Sally Yates’ testimony, Adam Schiff had said she might explain why Trump waited so long to fire Mike Flynn after she warned Don McGahn he had been compromised. One obvious reason is that it allowed Flynn, who had helped set up a meeting days later, attend it. That might change the connotation of the timing of the Comey firing, just in time to report back to Russia that the firing had “taken off” the pressure created by the investigation.
President Trump told Russian officials in the Oval Office this month that firing the F.B.I. director, James B. Comey, had relieved “great pressure” on him, according to a document summarizing the meeting.
“I just fired the head of the F.B.I. He was crazy, a real nut job,” Mr. Trump said, according to the document, which was read to The New York Times by an American official. “I faced great pressure because of Russia. That’s taken off.”
Mr. Trump added, “I’m not under investigation.”
It’s crystal clear that Trump fired Comey in an attempt to stave off investigation of Mike Flynn.
But the why behind that obstruction led to the rest of the guts of the Russia investigation. And the why may implicate both Trump (as unindicted co-conspirator) and Sessions (most likely as witness) more directly in any quid pro quo pertaining to the election.