I’ve spent the last few days going through the warrants released the other day in detail. This post attempts to summarize what they show about the Stone investigation.
First, understand the scope of this release. According to a filing the government submitted a year ago, they considered the media request to apply to, “warrants to search Stone’s property and facilities [and] other warrants that were executed as part of the same line of investigation” obtained under both Rule 41 and Stored Communication Act. It does not include warrants from other lines of investigation that happened to yield information on Stone. That said, there is good reason to believe there are either filings that were entirely withheld, or that DOJ’s interpretation of what constitutes the “same line of investigation” is fluid.
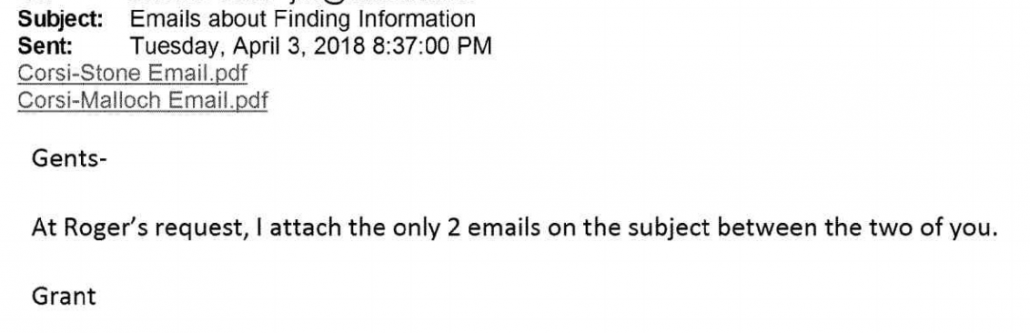
In his order to release the files, Judge Christopher Cooper said that the individual redactions hide, “the private information of non-parties, financial information, and non-public information concerning other pending criminal investigations.” In the hearing on the release, the media coalition suggested that people who had testified at Stone’s trial should not be protected under the guise of privacy, and that seems to have been the standard adopted on redactions of names. In general, then, this post assumes that the redaction of names (such as Ted Malloch) protects the privacy of people who did not testify at trial, but the redaction of entire paragraphs (such as 7 paragraphs of boilerplate describing why Malloch was suspected to be involved) was done to protect ongoing investigations. In the list of warrants below, I’ve marked with an asterisk those that — either because they weren’t for Stone’s property or because they didn’t yield evidence relevant to the the obstruction charges he was prosecuted for — were not provided to Stone in discovery; I’ve based that on the list in this order (see footnote 2).
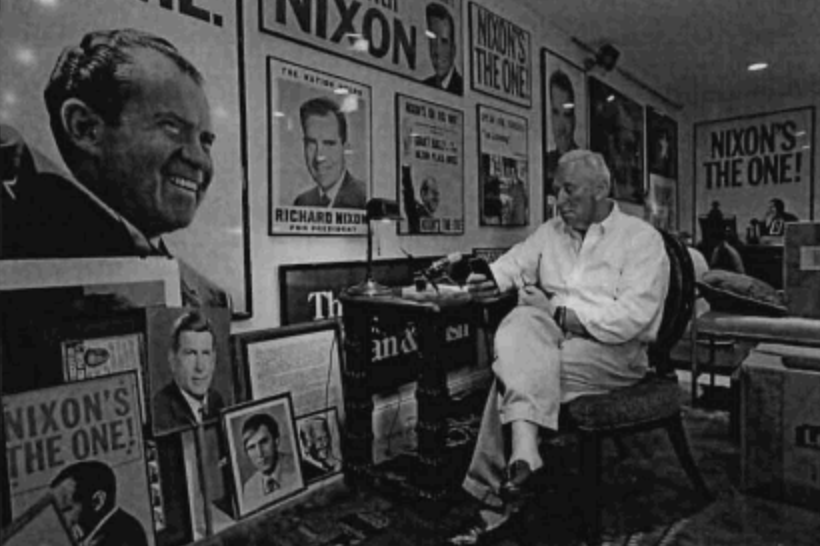
This investigation may well have started as a box-checking exercise, effectively checking whether John Podesta’s allegations that Roger Stone had learned of the hack targeting Hillary’s campaign manager ahead of time. It appears that Mueller’s team slowly came to believe that Roger Stone had gotten advance notice — and possibly advanced possession — of the Podesta email drop. Along the way, it ruled out one after another theory of how he did so.
Two of the most fascinating applications — one pertaining to an Israeli contact and another regarding someone apparently introduced to Stone by Charles Ortel — seem to have fully (the Israeli lead) or partly (the Ortel one) fizzled. (I base that on whether communications described in the affidavits continue to show up in later applications and whether entire paragraphs remain redacted.)
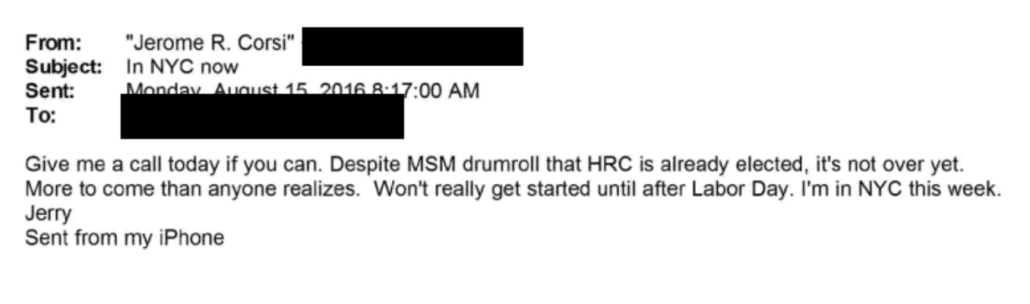
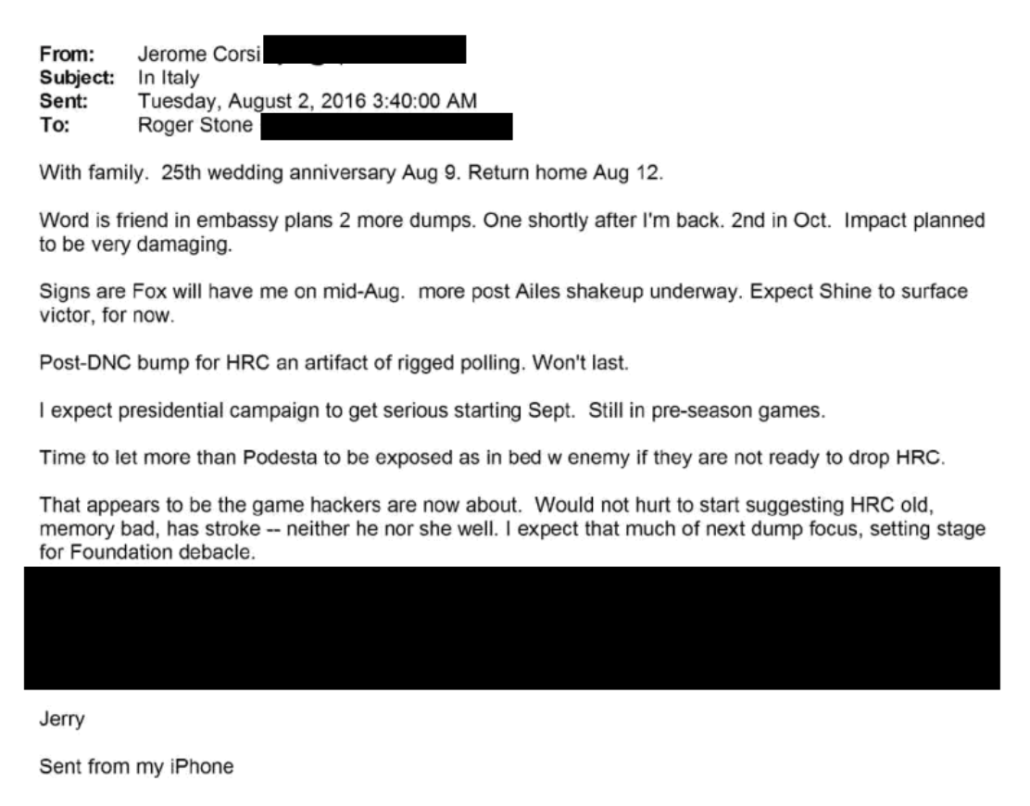
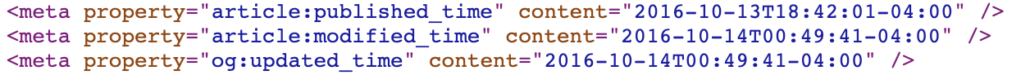
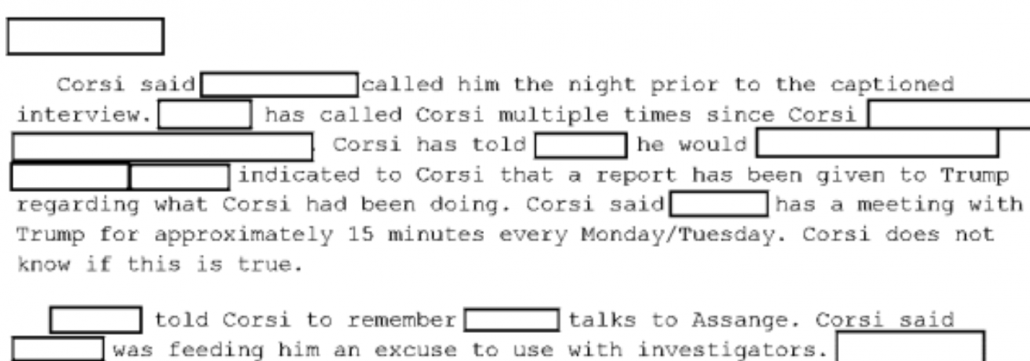
But the government still seems to believe that Stone worked with Corsi and Malloch on these issues. The government is obviously still trying to figure out whether the rat-fuckers and hoaxsters managed to optimize the release of the Podesta emails on October 7, 2016 to drown out the Access Hollywood drop. Mueller’s uncertainty on this point is something explained in redacted sections of the Mueller Report.
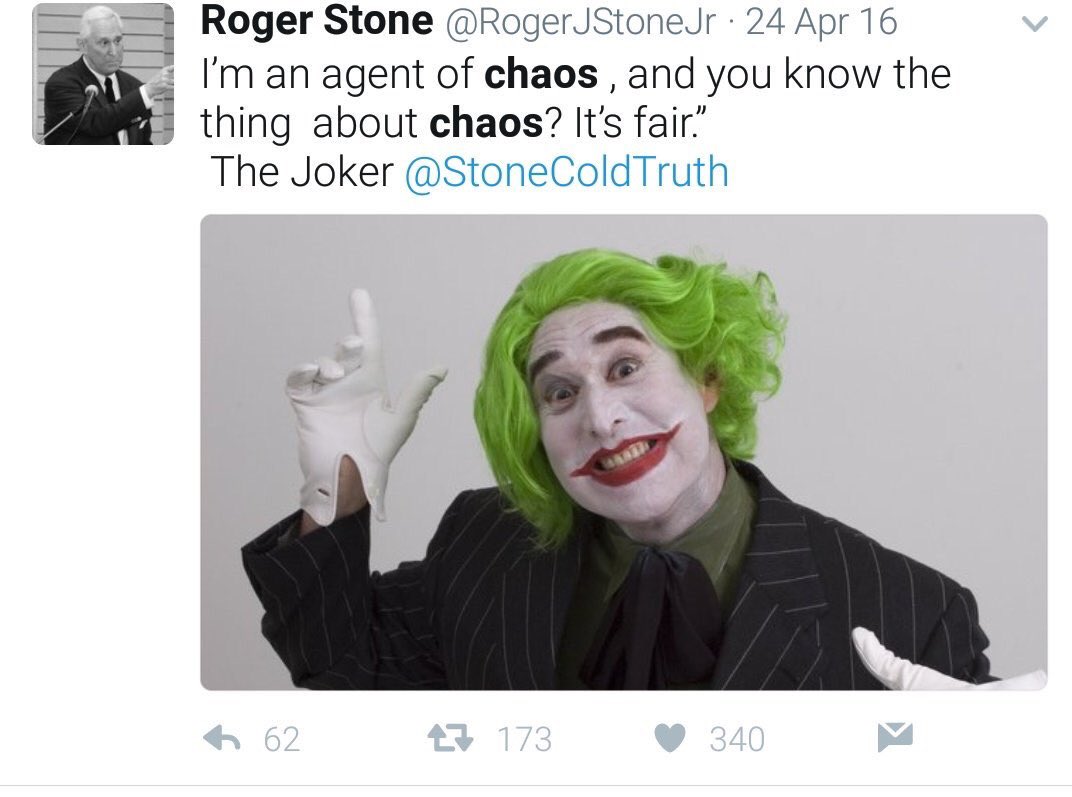
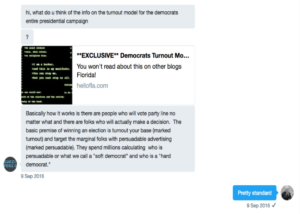
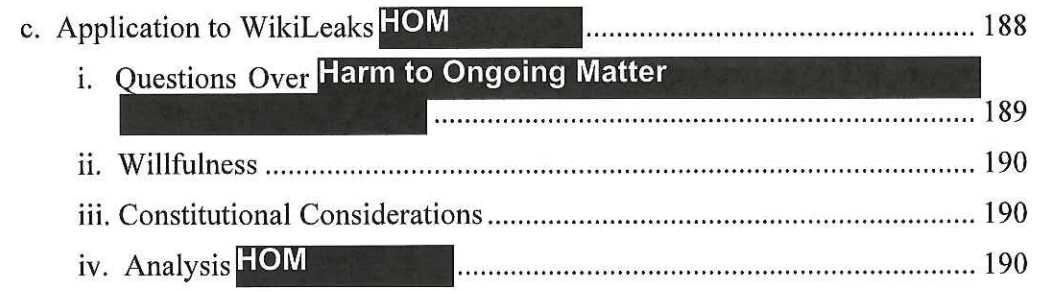
Along the way, Mueller developed two side prongs to the investigation: an examination of how Stone used social media to advertise WikiLeaks documents (it’s likely that investigation came to include ads that may have replicated themes being pushed by Russia and may have involved improper collaboration with the campaign), and the obstruction and witness tampering investigation Stone was prosecuted for.
More interesting still, in fall 2018, Mueller’s team started pursuing several leads (including the Ortel one), most of which — if the rule that entirely redacted paragraphs reflect ongoing investigation — continue to be investigated. Indeed, it appears that the prosecution of Stone for obstruction served partly as a means to initiate a prosecution against him, possibly entice him to flip against Trump or others, but perhaps mainly to obtain Stone’s devices in an attempt to get texts from 2016 to 2017 he had deleted, as well as the content of the encrypted communications he had sent using those devices. That is, the search, arrest, and prosecution of Stone appears to have been just one step in an ongoing investigation, an investigation that may be targeting others (including Julian Assange).
Identify the Malloch and Corsi connection (May 2017 to July 2018)
From May (when Mueller’s team first obtained subscriber records on Stone’s Twitter account) until November 2017, the investigation may have been little more than an effort to assess the spat between Stone and John Podesta over Stone’s August 21, 2016 “time in the barrel tweet.” After the team obtained Stone’s Twitter accounts, they moved to obtain the email accounts on which he conducted conversations started on Twitter. In November, Mueller got a warrant for his own team to access Julian Assange’s Twitter accounts (though the government surely already had obtained that). By December, Stone’s email accounts would have led Mueller’s team to believe that Ted Malloch, who was in London, could have been the back channel Stone kept bragging about, and so got his Gmail account. Mueller gagged Google to prevent Malloch from learning that. As a result, Malloch was presumably surprised when he arrived at Logan airport in March and was searched — a search conducted to obtain his phones, partly in an attempt to get to his UK-hosted email.
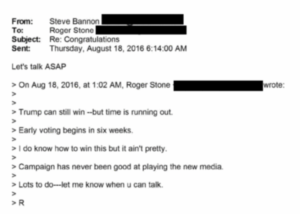
After Steven Bannon was interviewed in February 2018, Mueller’s team used that to obtain Stone’s Apple account; while not indicated anywhere in these applications, that’s where they would discover Stone and Michael Caputo had responded to a Russian offering dirt on Hillary.
In July, Mueller’s team obtained Jerome Corsi’s email and Apple accounts (there’s no record of them obtaining his Gmail account, but Corsi’s description of Mueller’s knowledge of his August 2016 searches suggests they got it). These affidavits begin to include a 7-page redaction that may indicate ongoing investigation into whether Stone or Corsi optimized the October 7 Podesta email release.
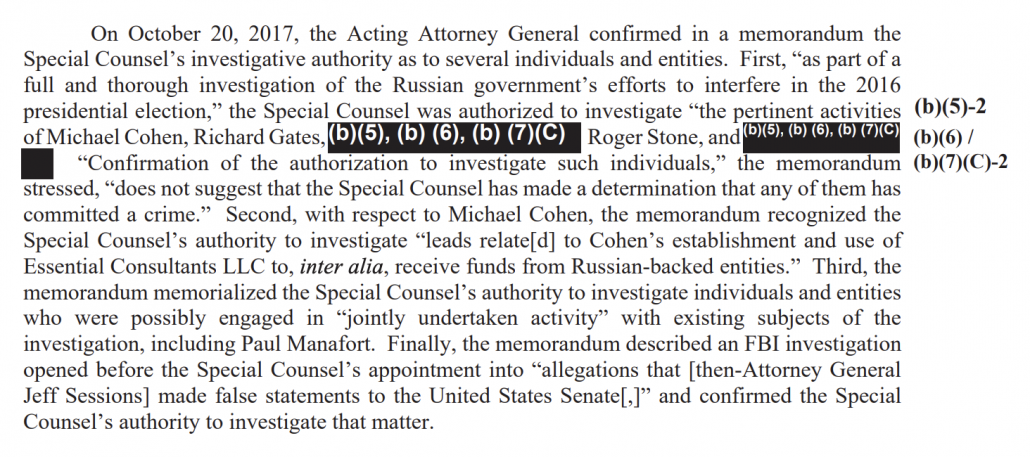
In this phase, the crimes being investigated expanded from just hacking to conspiracy to aiding and abetting. When Mueller got the Assange warrant, he added the illegal foreign contribution charge (one he declined to prosecute in a long redacted passage of the Mueller Report).
Collect materials on Stone’s overt social media campaigns (August 2018)
On May 18, 2018, Mueller’s team interviewed John Kakanis, who had worked on tech issues for Stone during the election. Afterwards, Mueller’s team obtained a series of warrants to collect the social media campaigns Stone had conducted on issues related to the Russian hack-and-leak. Those warrants included one for several Facebook accounts, a Gmail and Twitter account Stone used for such issues, and a Facebook and Gmail account under the Brazilian name Falo Memo Tio. Stone apparently did not receive the Facebook Falo Memo Tio account, and that warrant included a gag.
Track Stone’s efforts to obstruct the investigation (August 2018)
As Mueller’s team started interviewing people loyal to Stone, they became aware that Stone was communicating with witnesses. In May, Mueller obtained a pen register on Stone’s email accounts, allowing them to track with whom Stone was communicating. An August 3, 2018 warrant describes how investigators used those toll records to track such communications:
- In the wake of Michael Caputo’s interview, he and Stone communicated via his Hotmail account (this would have been obvious from the story Stone seeded with the WaPo not long after)
- After FBI Agents approached Andrew Miller, Stone emailed him via Gmail at least 10 times and a over a hundred times after he started challenging his subpoena
- Stone emailed both Corsi and Credico in May 2018
- Stone hired a private investigator to conduct a background investigation into someone who had done IT work for him during the campaign and research where he could serve Credico with legal process; in a June 2018 interview, the PI told investigators he and Stone primarily communicated via iPhone text messages
This affidavit included a section (¶¶64-77), based off texts with Credico stored in Stone’s iCloud account and texts published by the media, describing Stone’s threats to Credico.
In response to Stone’s overt efforts to thwart the investigation, Mueller obtained new warrants on Stone’s Hotmail, Gmail, and Apple accounts, which would yield a great deal of evidence for the obstruction and witness tampering charges against Stone. From this point forward, those charges would be included on warrants targeting Stone. In addition, from that point forward, the government appears to have sought to obtain Stone’s communications with those whose testimony he was obstructing (though the names of others besides Credico are redacted).
Starting with the next warrant, affidavits would include a section (¶¶87-89) comparing what Stone had told the House Intelligence Committee with what his own communication records showed, language that would form the backbone for the obstruction indictment.
Investigate the spooky stuff (May to August 2018)
There’s a number of things in these warrants that are difficult to assess. They didn’t show up in Stone’s trial, and it’s unclear whether they were leads that fizzled or reflect far more damning evidence. For example, the Israeli source who kept trying (and ultimately succeeded, once) to use Stone to get a meeting with Donald Trump doesn’t appear to have amounted to much, at least not with respect to the WikiLeaks releases.
A far more intriguing detail is the FBI claim — that lacks details that would be necessary to assess its accuracy — that Stone was searching for details of the Russian operation before those details were made public. The FBI made that claim twice. First, in a July 28, 2018 affidavit, they described that someone conducted searches on dcleaks and “guccifer june” using IP addresses that might be Stone, starting on May 17, 2016. The suggestion is that Stone may have had advance notice of those parts of the Russian operation. But some journalists learned of dcleaks after it got launched in early June and before it got more attention later in the summer. And the original Guccifer, Marcel Lazar, signed a plea agreement in late May 2016. Given Lazar’s claim to have hacked a Hillary server, it’s not unreasonable to think Stone would be researching him. A later warrant discusses someone — who again could be Stone — searching on Guccifer the day that the site would go up, but before it was public.
During the course of its investigation, the FBI has identified a series of searches that appear to relate to the persona Guccifer 2.0, which predate the public unveiling of that persona. In particular, on or about June 15, 2016 (prior to the publication of the Guccifer 2.0 WordPress blog), records from Google show that searches were conducted for the terms “guccifer” and “guccifer june,” from an IP address within the range 107. 77 .216.0/24.
The same rebuttal may be made — that this was about Marcel Lazar and not Guccifer 2.0. But evidence submitted at the trial suggests that Stone started anticipating the June 2016 dump on June 13, not June 15, making the claim more credible.
That July 28 warrant also describes several accounts that look like the FBI suspect Stone of sophisticated operational security. These include:
- A Gmail account created on July 28, 2016 (right in the thick of Stone’s effort to find out what WikiLeaks had coming next) and used until July 5, 2017
- A Gmail account created on October 26, 2016 and used until August 8, 2017
- A Gmail account created on June 27, 2016 and used in conjunction with Craigslist to communicate
The latter effort may suggest some serious OpSec, a way for Stone to communicate publicly without using his own comms.
Finally, there are matching Gmail and Facebook accounts the government obtained warrants for on August 28, 2018. These were old accounts with the Brazilian name Falo Memo Tio. It appears the government was interested in activity on this account from the last four days before the election. They obtained a gag for the Facebook warrant.
Seal warrants investigating an Agent of Foreign Power (August to September 2018)
The government tried to obtain proof that it was Stone doing those searches on Guccifer — as well as evidence about whom he may have met with in early August 2016 when he told Sam Nunberg he had dined with Assange — by obtaining his cell site location for June 14 through November 15 of that year.
Minutes after FBI Agent Andrew Mitchell (who had been the primary affiant on Stone warrants starting in May 2018) obtained that cell site warrant, FBI Agent Patrick Myers obtained a warrant for a mail.com account that Guccifer 2.0 had created on July 23, 2016 and used until October 18, 2016 (the account kept receiving traffic until February 2017). There are several remarkable things about this warrant. While FBI Agents in San Francisco obtained a warrant for it in August 2016, and someone — possibly Mueller’s team — obtained the headers from the account in September 2017, the government had never before obtained a full warrant on the account for the entire span of its activity. So Myers, seven weeks after Mueller released an indictment against the GRU, obtained that information in hopes it would provide more information about how the Guccifer persona had shared files.
The other FBI Agents investigating Stone, to the extent they described such things, were located in either Washington Field Office or FBI Headquarters in DC. Myers, however, was stationed in Pittsburgh, where the investigation into GRU had been moved (they were also working on an indictment for GRU’s hacking of WADA).
Myers’ involvement with Stone extended beyond this curious warrant for Guccifer 2.0’s account. Over the course of the next month, he obtained warrants for:
- Stone’s Liquid Web server storing old communications
- A Twitter account obtained for redacted reasons
- Multiple Twitter accounts obtained for redacted reasons
- Multiple Facebook and Instagram accounts obtained for redacted reasons
- Multiple Microsoft and Skype accounts obtained for redacted reasons
- Multiple Google accounts obtained for redacted reasons
- A Twitter account for someone, probably referred by Charles Ortel, whose name ends in R and who traveled back and forth from the UK who Stone suggested, in October 2016, was his intermediary
- Multiple Google accounts obtained for redacted reasons
All those warrants, as well as the Guccifer 2.0 account one, included a gag. One of those gag requests — for a warrant for some Twitter accounts — explains,
It does not appear that Stone is currently aware of the full nature and scope of the ongoing FBI investigation. Disclosure of this warrant to Stone could lead him to destroy evidence or notify others who may delete information relevant to the investigation.
Almost all of the warrants (not the R Apple one or the last Google one, though the R Apple one lists perjury) list FARA and 18 USC 951 (Agent of a Foreign Power) as crimes under investigation somewhere in the warrant, though often only in the gag request. To be clear, that doesn’t mean the FBI was investigating Stone as an Agent of a Foreign Power. The Guccifer 2.0 gag says FBI “is investigating WikiLeaks and others” for the listed crimes.
And those gags say the complexity of the investigation means it may extend more than a year from late September 2018. That is, in September 2018, the government took steps in an investigation they expected to last until around the time that Stone would eventually be tried, in November 2019.
Use the obstruction charges to seize Stone’s phones (January to February 2019)
The existence of those mystery warrants, none of which were provided to Stone in discovery and all but the R Apple one which appear to be ongoing, puts what happened in January 2019 in a very different light. At a time when Bill Barr promised to shut down the Mueller investigation as soon as he was confirmed yet while Mueller was still pursuing Andrew Miller’s testimony, the government obtained warrants to search Stone’s two homes, his office, and three devices seized in those searches (the affiants for those warrants had filed for earlier warrants in the investigation).
Unlike all the other warrants, those 2019 warrants listed only the obstruction, false statements, and witness tampering charges against Stone, largely tracking the indictment against him.
Those warrants emphasize the government’s interest in obtaining texts that might be accessed only via a forensic search of Stone’s phone, including texts sent via Apple, but also Signal, Wickr, and WhatsApp texts, as well as ProtonMail emails.
Which is to say, in the context of the warrants released this week, the prosecution of Roger Stone appears to be just one step in a far more serious investigation, one that may well be ongoing.
The warrants
August 7, 2017: Stone’s Twitter Accounts
This warrant only lists CFAA as the suspected crime, and doesn’t allege that Stone was the suspect in it. It also relies on Stone’s own public comments about DMing with Guccifer 2.0 rather than materials already obtained from the account, just the first of an insane number of instances where Stone’s comments to the press formed the basis for probable cause.
September 11, 2017: Stone’s Hotmail Account
When people DMed Stone, he’d refer them to this Hotmail account for further discussion. This affidavit incorporates DMs to Assange (including the June 10, 2017 one discussing a pardon) obtained with the August 7 warrant. It also describes investigating information to be used in the Republican primary. This warrant extended the timeframe of the Stone investigation back to January 1, 2015.
October 17, 2017: Stone’s Gmail
This warrant builds on emails between Corsi and Stone about getting the WikiLeaks releases — including Stone’s “get to Assange” one — to establish the probable cause to get Stone’s Gmail account. Because Corsi would sometimes discuss Podesta related business via both Stone’s Hotmail and Gmail accounts, Mueller’s team was able to get Stone’s Gmail account. This warrant makes it clear the investigation focused on Corsi and Stone’s evolving attacks against John Podesta (which I’ve covered in real time from early on) from the beginning. It also includes a detail about Malloch — that he made a reference in January 2017 about phishing Podesta — that almost certainly remains in the redacted sections pertaining to Malloch.
*November 6, 2017: WikiLeaks and Assange’s Twitter Accounts
This affidavit uses Assange’s DMs with Stone — including another one about a pardon and migration from the WikiLeaks to the Assange account– as well as his sharing of a password with Don Jr to get Mueller his own copy of the WikiLeaks and Assange Twitter accounts, which the government surely already had. The affidavit includes new details on initial communications between Guccifer 2.0 and WikiLeaks, some of which I laid out here. One detail that’s critical is WikiLeaks asked Guccifer 2.0 for Clinton Foundation documents from early on, meaning WikiLeaks and Trump’s people agreed about what they considered the best possible dirt.
*December 19, 2017: Ted Malloch’s Gmail
In addition to extra details about campaign communications (both between Stone and the campaign, and with Malloch and the campaign), this includes details of Turkish dirt Malloch was offering. It reveals that Stone got RNC credentials for Malloch (where, evidence suggests, Stone had meetings where upcoming releases may have been discussed). In addition, because Stone’s order to Corsi to reach out to Malloch is so important, this affidavit has previously unknown details about those days. The affidavit describes Malloch writing Stone on November 13, 2016 while with Jerome Corsi, a detail that may get redacted in subsequent affidavits.
This warrant included a gag on the provider.
This is the first application that introduces Stone, Corsi, and Malloch at the beginning of each affidavit, a practice that would generally continue (though some of these changes reflect different FBI agents writing the affidavit).
March 14, 2018: Two Apple Accounts used by Stone
In February, Steve Bannon was interviewed for two long days. He was asked questions and shared texts with Stone. This application uses some of what he testified about to justify getting Stone’s Apple accounts. Stone had his iCloud account set to full backup, but later warrants would make clear that he had deleted some of his texts from 2016 and 2017. Stone would later blame Sam Nunberg for revealing that he had claimed to have “dined” with Julian Assange while visiting Los Angeles in early August 2016, but this application began to incorporate that email into boilerplate application language (a footnote on what Nunberg told investigators about this is redacted in later warrants).
This application added wire fraud to Stone’s potential charges; it’s not at all clear why.
*March 27, 2018: Malloch’s person and his baggage
This warrant allowed the FBI to search Malloch as he landed in Logan airport. It incorporated details from Malloch’s Gmail obtained in December and was at least in part an effort to get to his UK-based email.
*May 4, 2018: Mystery Israeli Gmail
Over the course of the year, an Israeli exploited a seeming pre-existing relationship with Jerome Corsi to get close to Stone and through him to Trump. The person appeared to offer Stone dirt to save Trump (this story provides some background on potential players). Stone seems to have been reluctant to meet at multiple times, as when he said, in May 2016, “I am uncomfortable meeting without Jerry,” claimed, in June, “to have been poisoned,” in July, came down “with a nasty cold and too ill to travel,” followed later with, “I have pneumonia and may be hospitalized later today,” claimed, “Matters complicated” in August. When, in early November, they tried again, the Israeli deferred claiming, “HAVING a TIA. Early Stroke. … Blury Virson.” These exchanges never show up in later filings, so it’s quite likely Mueller determined they were nothing (or at least, that Stone and Corsi had done nothing wrong) after obtaining the emails. Alternately, a redaction in the affidavit may suggest the Israeli in question got referred and some kind of investigation is ongoing. This warrant included a gag on the provider.
*July 12, 2018: Jerome Corsi’s CSC Holdings, Windstream, and Apple accounts (second version)
This adds language about Russian hacking after the initial compromise (including the September hack of the AWS server). It includes 7 paragraphs of language from after the election that is redacted, possibly because it remains under investigation. This Stone filing describes four of those paragraphs as pertaining to Corsi taking credit for optimizing the Podesta release and Malloch introducing Corsi to Assange after the election (see this post). Some of the redactions (probably the Malloch introduction) repeats the “phishing Podesta” quip. This warrant included a gag on the provider. It limited the scope of the warrant to June 15 through November 10, 2016 and included only CFAA and conspiracy in the crimes being investigated.
July 27, 2018: Roger Stone’s OpSec emails
This warrant obtains the search histories for 3 Gmail accounts Roger Stone set up, possibly for OpSec purposes. They include:
- Target Account 1 created on July 28, 2016 and used until July 5, 2017
- Target Account 2 created on October 26, 2016 and used until August 8, 2017
- Swash Buckler Account created on June 27, 2016 and used to communicate via Craigslist ads
Between May 17, 2016 and June 15, 2016, the affidavit suggests, Stone may have conducted Google searches for DCLeaks and Guccifer (which could be 1 or 2) prior to the publication of the Guccifer 2.0 blog. The FBI connected them to Stone via the IP addresses he used to access Twitter and Facebook, something they would continue to investigate. The affidavit also reveals that Stone deleted the search history for a different Google account between January 18 and July 23, 2016.
August 2, 2018: Roger Stone marketing Facebook accounts
This warrant gets three of Stone’s Facebook accounts, two of which include advertisements pertaining to WikiLeaks or Russia (the description of the third is redacted). Stone used this warrant when signaling to his co-conspirators what was in his warrants, so redacted details are available here. The biggest redaction for an ongoing investigation pertains to whether Corsi and Stone affected the release of the Podesta emails and Malloch offering to set Corsi up with Assange after the election.
August 3, 2018: Renewed warrants for Apple, Hotmail, and Gmail
Partly because the way Stone worked the press and aired the threats he had made against Randy Credico, it became clear he was tampering or comparing notes with witnesses (also including Jerome Corsi, Michael Caputo, and Andrew Miller, as well as one other witness that Stone hired a private investigator to investigate). That gave Mueller the excuse to get new warrants on Stone’s main email and text accounts to get those conversations. This request expanded the focus to include Credico and others (the names of the others are redacted but are likely those with whom Stone was trying to tamper). This warrant also adds obstruction and witness tampering to the crimes being investigated.
August 8: Warrants for a Gmail and Twitter account Stone used for social media campaigns (Twitter)
On May 18, 2018, Mueller’s team interviewed John Kakanis about work he did for Stone during the campaign. He described how Stone conducted social media campaigns — including materials relating to WikiLeaks and the Russian investigation — which both of these accounts played a role in.
August 20, 2018: Warrant for Stone’s cell site information from June 15 to November 15, 2016
Citing the searches probably made by Stone for Guccifer and dcleaks information before those accounts were made public, the government obtained cell site information for the period from the day that the Guccifer 2.0 account first started to a day the week after the election. The affidavit also explained wanting to know if Stone was with the Trump campaign at various times and where he was in Los Angeles when he told Sam Nunberg he had dined with Assange. Note, this affidavit suggests Stone did a Google search on “Guccifer” on June 15, 2016 before the site went up.
*August 20, 2018: Warrant for Guccifer 2.0’s second email account
The same day the government got a warrant to find out where Stone had been when during the election, they got a renewed warrant for one of the email accounts associated with the Guccifer 2.0 site. They had previously gotten everything from that email account in “approximately” August 2016, and then gotten headers for any emails sent in “approximately” September 2017. Getting the full content would give it additional details on any activity with the account between the original warrant — August 2016 — and the final login on October 18, 2016, as well as any email traffic subsequent to that. The stated purpose for obtaining this information was to “assist in identifying additional means by which Guccifer 2.0 shared stolen documents with WikiLeaks and others.” Patrick Myers, an FBI agent located in Pittsburgh (and therefore presumably someone more closely involved in the GRU investigation) obtained this warrant. This warrant included a gag on the provider. Parts of this warrant invoke 18 USC 951 — agent of a foreign power charges — in addition to the other crimes under investigation.
*August 28, 2018: Warrant for Stone’s Falo Memo Tio Facebook account
August 28, 2018: Warrant for Stone’s Falo Memo Gmail account
This incorporates details about Stone’s Facebook accounts used to push the hack-and-leak, found in the earlier August Facebook warrants. It seeks to obtain an old Stone Facebook account that got advertising traffic right before the election. These were Stone-specific warrants that was not turned over in discovery, suggesting it returned nothing pertaining to his prosecution. The Facebook warrant, but not the Gmail one, included a gag on the provider; it also was not included in the warrants provided to Stone in discovery.
August 28, 2018: Warrant for Stone’s rogerstone@mail account
This email account–and the fact that he had been using it to tell his cover story about WikiLeaks–showed up in his Gmail account.
*September 24, 2018: Warrant for Stone’s Liquid Web server
This was a server Stone used to encrypt and back up his data in case the government seized his computers. It was not provided to Stone in discovery so may not have revealed any interesting information. This is the first of these affidavits written by Patrick Myers, an FBI agent located in Pittsburgh.
*September 26, 2018: Mystery Twitter Account
*September 27, 2018: Mystery Facebook and Instagram Accounts
*September 27, 2018: Mystery Microsoft include Skype
*September 27, 2018: Mystery Google
On September 26 and 27, Mueller’s team obtained a bunch of new warrants. All were obtained by Myers, the Pittsburgh FBI agent. All included gags on the provider. Most entirely redact the description of why the FBI needed the accounts, suggesting these investigations are ongoing. They also invoke 951 and FARA in the sealing request.
*September 27, 2018: Mystery Twitter Accounts 2
Like the other warrants obtained on September 27, the explanation for targeting these Twitter accounts is sealed. Like them, Myers obtained the warrant. Like those, it includes a request for sealing that lists 18 USC 951 — acting as an unregistered foreign agent — and FARA. Unlike the other warrants from that day, the justification for sealing this one explains that “It does not appear that Stone is fully aware of the full scope of the ongoing FBI investigation.”
*September 27, 2018: Mystery Apple ends in R
Then there’s another odd September 27 warrant application. Like the other warrants obtained on September 27, Myers wrote the affidavit for this one, and it included a gag. Unlike the others, however, the explanation for targeting this account is not entirely redacted. The affidavit explains that,
- On August 17, 2016, someone (Charles Ortel?) introduced Stone and R
- Between that introduction and November 3, 2016, Stone and R were in contact 60 times
- On October 7, R and Stone spoke during the time between when WaPo alerted him to the Access Hollywood Video and the time it dropped
- On October 10, R and Stone probably met for pizza on the Upper East Side
- On October 12, Stone claimed that he had met his intermediary, who traveled back and forth to London, on October 10
The list of information targeted includes an additional name, probably that of Charles Ortel.
*October 5, 2018: Mystery Multiple Googles
Like the September 27 warrants, the explanation for targeting these accounts remains entirely redacted. Like them, the affidavit was written by Myers and sealed under a Kyle Freeny request. Unlike those, however, this one does not list 951 and FARA in the request to seal. This affidavit also does not include the contacts with “R” in the narrative about October 7, suggesting that lead may have fizzled.
January 24, 2019: Stone’s NY property
January 24, 2019: Stone’s FL property
January 24, 2019: Stone’s FL office
February 13, 2019: Three of Stone’s devices
The warrants for the searches in conjunction with Stone’s arrest on January 24 are fairly similar (one agent wrote the one in NY, another did the two in FL), except for the descriptions of the premises, facilitated by how much media Stone has done at these locations.
The affidavits themselves largely track the indictment, though showing where the government had sourced the evidence that ultimately got introduced at evidence at trial. The affidavits add people named in the indictment — Rick Gates, Steve Bannon, and Erik Prince (whose description is redacted) — premised on the import of proving that Stone had lied about telling these people about his purported link to WikiLeaks. As compared to the earlier warrants, these affidavits have a closer focus on the release (and reliance, exclusively, on the Crowdstrike and GRU indictment attribution, which is something Stone litigated and which I may return to).
These warrants make it clear that one of the things the government was doing was searching Stone’s homes for all his electronic devices in hopes of getting texts from 2016 to 2017 he deleted and his encrypted communications, which include:
- WhatsApp, downloaded on October 5, 2016 to talk to Erik Prince
- Signal and ProtonMail downloaded on August 18, 2016; Stone used Signal to talk to Margaret Kunstler
- Wickr downloaded on August 5, 2017
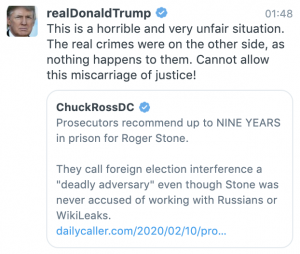
Update: One detail I forgot to add about the 2019 search warrants: They explain that Stone responded to a grand jury subpoena in November 2018 asking for the texts he had with Credico, after he told the press — specifically, Chuck Ross, for a credulous story that spun Stone’s like — that his attorney had them. It’s one of the most hilarious ways that Stone’s blathering to the press hurt him.
Update: One more detail about the 2019 search warrants. The FBI was specifically looking for a “file booklet” recording a meeting Stone had with Trump at Trump Tower during the 2016 election.
60. On or about May 8, 2018, a law enforcement interview of [redacted] was conducted. [redacted] was an employee of Stone’s from approximately June 2016 through approximately December 2016 and resided in Stone’s previous New York apartment for a period of time. [redacted] provided information technology support for Stone but was not formally trained to do so. [redacted] was aware that Stone communicated with Trump during the 2016 presidential campaign, and afterward, both in person and by telephone. [redacted] provided information about a meeting at Trump Tower between Trump and Stone during the time [redacted] worked for him, to which Stone carried a “file booklet” with him. Stone told [redacted] the file booklet was important and no one should touch it. [redacted] also said Stone maintained the file booklet in his closet.
61. On or about December 3,2018, law enforcement conducted an interview of an individual (“Person 2”) who previously had a professional relationship with a reporter who provided Person 2 with information about Stone. The reporter relayed to Person 2 that in or around January and February 2016, Stone and Trump were in constant communication and that Stone kept contemporaneous notes of the conversations. Stone’s purpose in keeping notes was to later provide a “post mortem of what went wrong.”