I have three things cluttering up my notes — just big enough to give pause but not big enough for a full post. I’ll toss them out here for an open thread.
~ 3 ~Aluminum -> Aeronautics -> Stock Market and Spies
I’ve spent quite a while researching the aeronautics industry over the couple of years, trying to make sense out of
a snippet in the Buryakov spy case indictment. The three spies were at one point digging into an aeronautics company, but the limited amount of information in the indictment suggested they were looking at a non-U.S. company.
You can imagine my surprise on December 6, 2016, when then-president-elect tweeted about Boeing’s contract for the next Air Force One, complaining it was too expensive. Was it Boeing the spies were discussing? But the company didn’t fit what I could see in the indictment, though Boeing’s business is exposed to Russia, in terms of competition and in terms of components (titanium, in particular).
It didn’t help that Trump tweeted before the stock market opened and Boeing’s stock plummeted after the opening bell. There was plenty of time for dark pool operators to go in and take positions between Trump’s tweet and the market’s open. What an incredible bonanza for those who might be on their toes — or who knew in advance this was going to happen.
And, of course, the media explained this all away as Trump’s “Art of the Deal” tactics, ignoring the fact he wasn’t yet president and he was renegotiating the terms of a signed government contract before he took office. (Ignoring also this is not much different than renegotiating sanctions before taking office…)
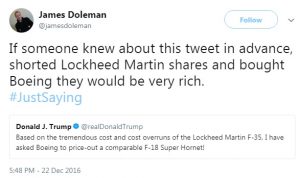
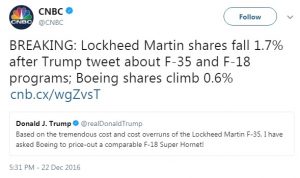
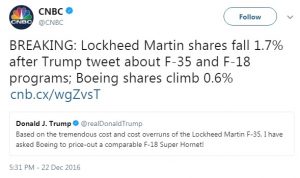
I was surprised again only a couple weeks later about Boeing and Lockheed; this time I wasn’t the only person who saw the opportunity, though the timing of the tweet and market opening were different.
Again, the media took note of the change in stock prices before rolling over and playing dead before the holidays.
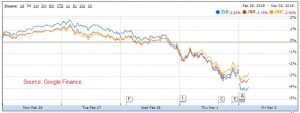
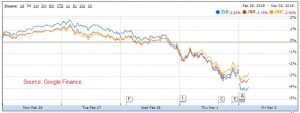
There have been a few other opportunities like this to “take advantage of the market,” though they are a bit more obscure. Look back at the NYSE and S&P trends whenever Trump has tweeted about North Korea; if one knew it was coming, they could make a fortune.
A human would only need the gap as long as that between a Fox and Friends’ mention of bad, bad North Korea and a corresponding Trump tweet to make the play (although one might have to watch that vomit-inducing program to do this). An algorithm monitoring FaF program and Trump tweets would need even less time.
Yesterday was somebody’s platinum opportunity even if Trump was dicking around with U.S. manufacturers (including aeronautics companies) and global aluminum and steel producers. His flip-flop on tariffs surely made somebody beaucoup bucks — maybe even an oligarch with a lot of money and a stake in one of the metals, assuming he knew in advance where Trump was going to end up by the close of the market day. The market this morning is still trying to make sense of his ridiculous premise that trade wars are good and winnable; too bad the market still believes this incredibly crappy businessman is fighting a war for U.S. trade.
Just for the heck of it, go to Google News, search for [trump tariffs -solar], look for Full Coverage, sort by date and not relevance. Note how many times you see Russia mentioned in the chronologically ordered feed — mine shows exactly zero while China, Korea, Germany are all over the feed. I sure hope somebody at the SEC is paying as much attention to this as cryptocurrency.
I suppose I have to spell this out: airplanes are made of aluminum and steel, capisce?
~ 2 ~Italian Son
One niggling bit from Glenn Simpson’s testimony for Fusion GPS before the Senate Intelligence Committee has stuck with me. I wish I could time travel and leave Simpson a note before testimony and tell him, “TELL US WHAT YOU SEE, GLENN!” when he is presented with Paul Manafort’s handwritten notes. The recorder only types what was actually said and Glenn says only the sketchiest bit about what he sees. Reading this transcript, we have only the thinnest amount of context to piece together what he sees.
Q. Do any of the other entries in here mean anything to you in light of the research you’ve conducted or what you otherwise know about Mr. Browder?
A. I’m going to — I can only speculate about some of these things. I mean, sometimes —
MR. LEVY: Don’t speculate.
A. Just would be guesses.
Q. Okay.
A. I can skip down a couple. So “Value in Cyprus as inter,” I don’t know what that means.”Illici,” I don’t know what that means. “Active sponsors of RNC,” I don’t know what that means. “Browder hired Joanna Glover” is a mistaken reference to Juliana Glover, who was Dick Cheney’s press secretary during the Iraq war and associated with another foreign policy controversy. “Russian adoptions by American families” I assume is a reference to the adoption issue.
Q. And by “adoption issue” do you mean Russia prohibiting U.S. families from adopting Russian babies as a measure in response to the Magnitsky act?
A. I assume so.
Bold mine, to emphasis the bit which has been chewing away at me. “Illici” could be an interrupted “illicit”; the committee and Simpson use the word or a modifier, illicitly, eight times during the course of their closed door session. It’s not a word we use every day; the average American Joe/Josie is more likely to use “illegitimate” or the even more popular “illegal” to describe an unlawful or undesirable action or outcome.
(I’m skeptical Manafort was stupid enough to begin scratching out “illicit” and catch himself in time, but then I can’t believe how stupid much of this criminality has been.)
But the average American Joe/Josie doesn’t travel abroad, speak with Europeans often, or speak second languages. The average white Joe/Josie may be three or more generations from their immigrant antecedents.
Not so Mr. Manafort, who is second generation Italian on both sides of his family. He may speak some Italian since his grandfather was an immigrant — and quite likely Catholic, too. Hello, Latin masses in Italian American communities.
Did Manafort mean “illici,” a derivative of Latin “illicio,” which means to entice or seduce? Or was it a corrupted variant of Latin “illico,” which means immediately?
Or is Manafort a bad speller who really meant either “elici”, “elicio,” or “elicit,” meaning to draw out or entice?
Like Simpson, these are just guesses. Only Manafort really knows and I seriously doubt he’ll ever tell what he meant.
~ 1 ~If you haven’t checked your personal online privacy and cybersecurity recently, give
Privacy Haus’s checklist a look. Nearly all of the items I’ve already addressed but I tried one of the items suggested as a fix to an ongoing challenge. Good stuff!
~ 0 ~That’s it, have at it in this open thread! One last thing: if you didn’t read Marcy’s op-ed,
Has Jared Kushner Conspired to Defraud America? in Wednesday’s NYT, you should. You’re going to need it as part of a primer going forward.