On the Benefits of Having a Career Diplomat Run CIA: “This Is One Information War that I Think Putin Is Losing”
Thus far during Russia’s invasion of Ukraine, the intelligence community has declassified at least four major reports and a slew of smaller ones:
- The intelligence showing Russia planned a false flag to justify an invasion of Ukraine
- Details of China’s discussions with Russia about the invasion in advance, including that, in December, “Beijing had shared the information with Moscow, telling the Russians that the United States was trying to sow discord”
- More recent preemptive pushback predicting a false Chemical/Biological weapon attack
- Reports last night that Russia has already asked China for military equipment and aid
I would bet a fair amount of money that, when the history of these events is told twenty years from now, we’ll learn of similar, but non-public, selective declassification with NATO-plus-Sweden-and-Finland partners, starting at a NATO summit in February, immediately after which a number of European countries (most spectacularly, Germany) took dramatic and unified action.
There has been a slew of commentary about the aggressive use the US has made of declassified intelligence. The triumphalism of such commentary may yet prove premature.
After all, it’s possible that Putin arrested two FSB officers because he suspects they were sources for some of the intelligence that got shared to undermine Russia’s efforts. It’s possible that Russia’s focus on neutralizing western support for Ukraine in recent days, particularly its attack on the western training base in Yavoriv yesterday, reflects a counterintelligence crackdown responding to declassified US intelligence.
But for now, such declassification has been tremendously successful. It allowed the US and its European partners to repeatedly undercut Russian efforts to gain surprise or legitimize their invasion with disinformation. It has exposed specifics about China’s support for the invasion, raising the costs of such support and, potentially, providing leverage to convince China to distance themselves both publicly and privately from Russia’s efforts. And it seems to have provided a basis for Western countries to unify quickly.
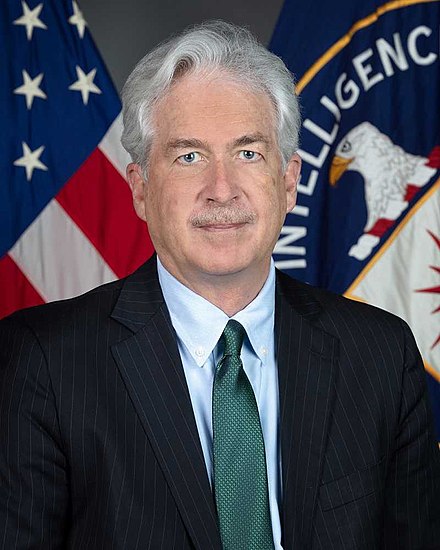
This most recent instance — the organized sharing of information about Russian pleas to China for help just before Jake Sullivan meets with Yang Jiechi in Rome — makes this comment from CIA Director William Burns at least week’s Global Threats hearing resonate.
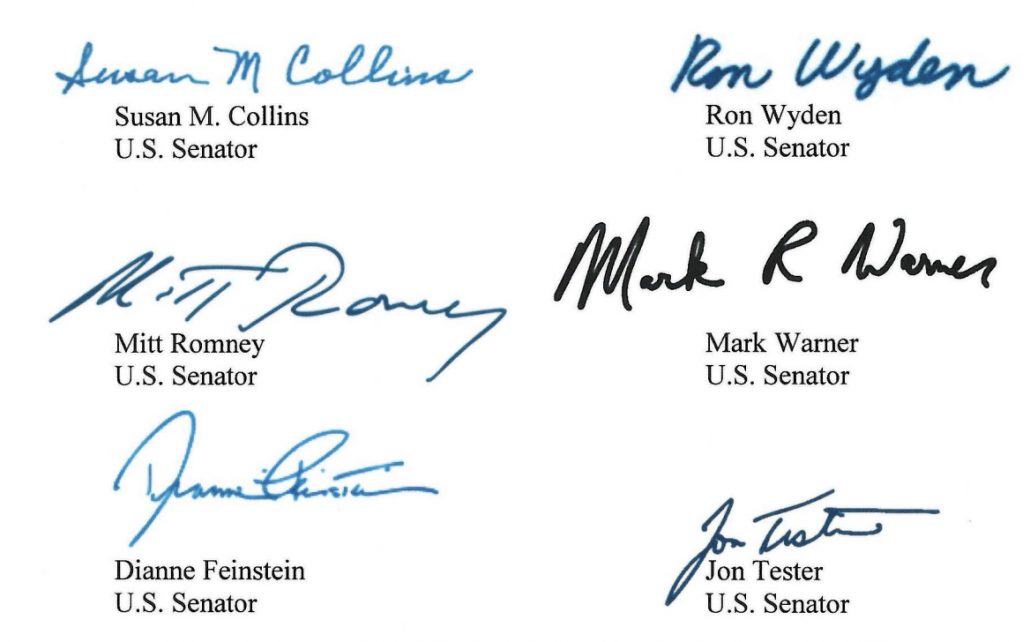
In response to a question from Susan Collins about Russia’s efforts to use false flag attacks, he tied his own years losing information wars with Russia to decisions to declassify information now.
Well, thanks very much Senator. I think it underscores the concern that all of us need to focus on those kind of issues, whether it’s the potential for a use of chemical weapons either as a false flag operation or against Ukrainians. This is something, as all of you know very well, is very much a part of Russia’s playbook. They’ve used those weapons against their own citizens, they’ve at least encouraged the use in Syria and elsewhere, so it’s something we take very seriously, and it’s one of the reasons, as Director Haines said earlier, that I’m convinced that our efforts at selective declassification, to pre-empt those kind of false flag efforts and the creation of false narratives have been so important.
In all the years I spent as a career diplomat, I saw too many instances in which we lost information wars with the Russians. In this case, I think we have had a great deal of effect in disrupting their tactics and their calculations and demonstrating to the entire world that this is a premeditated and unprovoked aggression, built on a body of lies and false narratives. So this is one information war that I think Putin is losing.
Among other posts Burns served in, he was Ambassador to Russia in the final years of the Bush Administration (months before Russia’s invasion of Georgia) and he served as Deputy Secretary of State during Russia’s response to Viktor Yanukovych’s ouster, including its annexation of Crimea.
He knows how successful Russia has been at lying in the last twenty years.
And he explicitly tied his experience of attempting to diplomatically negotiate with Russia and others while Russia’s lies held sway to the decision to declassify information here.
Normally, CIA Directors protect such secrets with knee-jerk obstinance. But under this former diplomat, the Intelligence Community is actually using the intelligence it gathers to gain tactical leverage. After years of Russian intelligence operations designed to split American alliances, that has had the effect of raising US credibility with allies.
This is assuredly not just Burns. Even under Trump, Paul Nakasone was much more aggressive about taking credit for NSA or CYBERCOM operations than past NSA Directors. And Avril Haines, whose background is more diverse, promised a more open Intelligence Community during her confirmation as well.
But after the two decades of paranoid secrecy that followed the Iraq intelligence debacle, the United States is actually using the intelligence it makes such efforts to collect.