Rat-Fucker Rashomon: Trolling for Russia
With one exception, the SSCI Report does a tremendous job cataloging how people with a stake in the 2016 hack-and-leak operation undermined the Russian attribution of it. It includes an entire section on Russia’s efforts to undermine the Russian attribution, in which Konstantin Kilimnik plays a starring role and Manafort significantly follows. It describes WikiLeaks’ false attribution, mentioning the Seth Rich hoax explicitly. It includes several paragraphs describing the campaign’s claimed ignorance about the source of the stolen emails, framing it in terms of the October 7 DHS/ODNI assessment.
The Campaign tried to cast doubt on the October 7 joint DHS/ODNI assessment formally attributing the activity to Russia, and was indifferent to the significance of acquiring, promoting, or disseminating materials from a Russian intelligence services hack-and-leak campaign.1436
1436 (U) In contrast to the Campaign’s decision, other lawmakers refused to engage in such exploitation of the stolen material. For example, in an October 2016 interview, Senator Marco Rubio said that he would “not discuss any issue that has become public solely on the basis of WikiLeaks,” noting that “these leaks are an effort by-a foreign government to interfere with our electoral process, and I will not indulge it.” Jonathan Karl and Benjamin Siegel, “Exclusive: Rubio Won’t Talk About WikiLeaks, and Neither Should Donald Trump,” ABC News, October 19, 2016.
[snip]
(U) While the Campaign was using the WikiLeaks documents, Trump cast doubt on the assessment that Russian government hackers were responsible for the hack-and-leak campaign. At the second presidential debate on October 9, Trump asserted: “maybe there is no hacking.” 1704 In testimony to the Committee, Stephen Miller claimed that the Campaign did not know who was responsible for the hacks “one way or the other.”1705 But this uncertainty did not stop Trump or Campaign officials from minimizing Russian involvement at other times, suggesting that it was an “absurd claim” to say that the Kremlin was promoting the Trump Campaign1706; that “the DNC did the ‘hacking”‘ as a distraction1707; that the Democrats were “putting [it] out” that the Russians were responsible; and that it was “unlikely” that the Russians did it1708 or that nobody knew it was Russia, and it “could also be China” or “lots of other people.”1709 According to Gates, the Campaign was “not concerned with how or who hacked” the documents, but just sought to release emails as quickly as possible. 1710
(U) Among the theories espoused by Trump Campaign officials, Manafort expressed a belief that the Ukrainians were responsible, not the Russians. 1711 Gates said that this “parroted a narrative [Konstantin] Kilimnik often supported.” 1712 According to Gates, Kilimnik also asserted that the hack could have been done by “Russian operatives in Ukraine.” 1713 Gates was not aware of Manafort asking Kilimnik “to reach out to his Russian contacts” about the source of the leaked materials, and was not himself asked to contact Kilimnik about it. 1714 The Committee has determined that this theory espoused by Kilimnik and Manafort has no factual basis.1715 Gates and others also decided to promote the story that a DNC insider had been involved in the hacks.1116
SSCI’s invocation of the doubts Trump aired in the October 9, 2016 debate is of particular note, coming as it did just days after the John Podesta release. Trump’s comment was something that Mueller’s team asked numerous witnesses about.
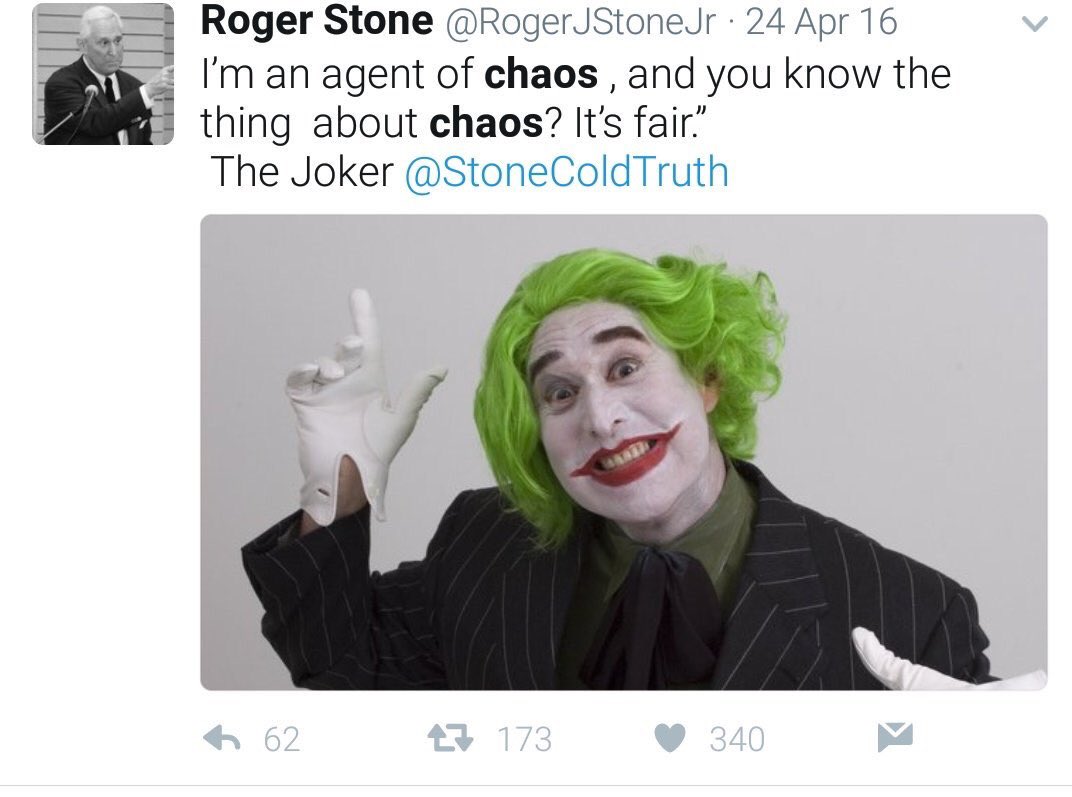
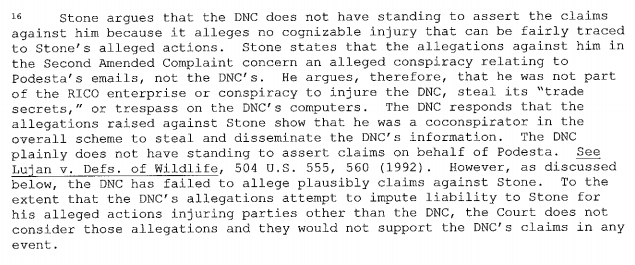
Yet SSCI doesn’t include a focused discussion of all the ways Roger Stone — who appears to have met with Trump on October 8, 2016 — undermined the Russian attribution. As noted in this post of this series, one of the affidavits targeting Stone suggests Stone optimized the release of the John Podesta emails to overwhelm any attention to that October 7 attribution statement.
Perhaps the closest the SSCI Report comes to describing Stone’s efforts to troll for Russia is where — in entirely different sections of the report — the SSCI Report documents Stone’s flip flop on the Russian role in hacking the DNC. On page 224 of the SSCI Report, it describes how Stone told Gates (in July 2016) that the stolen files may have come from Russia.
In one call during that period, Stone also told Gates that the WikiLeaks information could be from the Russians. However, Gates did not recall Stone suggesting a connection between WikiLeaks and Russia. Gates also thought that Stone could have based his theory of Russian involvement on publicly available information. 1452
On pages 194-195, the SSCI Report describes how days later, Stone started claiming that Guccifer 2.0, whom he did not treat as Russian, had hacked the DNC.
On August 5, 2016, Stone penned an opinion piece asserting that Guccifer 2.0, not the Russians, had hacked the DNC, and repeating the false claims made by the GRU on the Guccifer 2.0 website and Twitter account. 1250 On August 12, the GRU released DCCC records, including the cell phone numbers and email addresses of almost all Democrats in the House of Representatives through the Guccifer 2.0 persona, 1251 and tweeted publicly at Stone: “thanks that u believe in the real #Guccifer2.”1252 When Twitter then suspended the Guccifer 2.0 account, WikiLeaks complained: “@Guccifer _ 2 has account completely censored by Twitter after publishing some files from Democratic campaign #DCCC.”1253 Stone also tweeted at WikiLeaks and the Guccifer 2.0 persona in response to the suspension, calling it “outrageous”1254 and referring to Guccifer 2.0 as a “HERO.”1255
Yet even though it includes this flip flop across two places thirty pages apart without noting it, the SSCI report doesn’t describe how, in the same period, Stone started pushing the Seth Rich hoax. Nor does it describe how long he continued to argue there was no proof that Guccifer 2.0 was Russian.
Perhaps the SSCI Report’s silence about Stone’s efforts to undermine the Russian attribution is a focus adopted from the Mueller Report. Like the SSCI Report, the Mueller Report describes WikiLeaks’ efforts to undermine the Russian attribution of the hack by pinning it on Seth Rich.
Beginning in the summer of 2016, Assange and WikiLeaks made a number of statements about Seth Rich, a former DNC staff member who was killed in July 2016. The statements about Rich implied falsely that he had been the source of the stolen DNC emails. On August 9, 2016, the @WikiLeaks Twitter account posted: “ANNOUNCE: WikiLeaks has decided to issue a US$20k reward for information leading to conviction for the murder of DNC staffer Seth Rich.” 180 Likewise, on August 25, 2016, Assange was asked in an interview, “Why are you so interested in Seth Rich’s killer?” and responded, “We’re very interested in anything that might be a threat to alleged Wikileaks sources.” The interviewer responded to Assange’s statement by commenting, “I know you don’t want to reveal your source, but it certainly sounds like you’re suggesting a man who leaked information to WikiLeaks was then murdered.” Assange replied, “If there’s someone who’s potentially connected to our publication, and that person has been murdered in suspicious circumstances, it doesn’t necessarily mean that the two are connected. But it is a very serious matter … that type of allegation is very serious, as it’s taken very seriously by us.”181
But neither describes Stone’s parallel and in many ways far more systematic efforts to sow the Rich hoax, efforts which extended well beyond the election and recruited involvement from the likes of Sean Hannity (who will be deposed by Joel Rich’s lawyers on this subject on October 30) and Alex Jones.
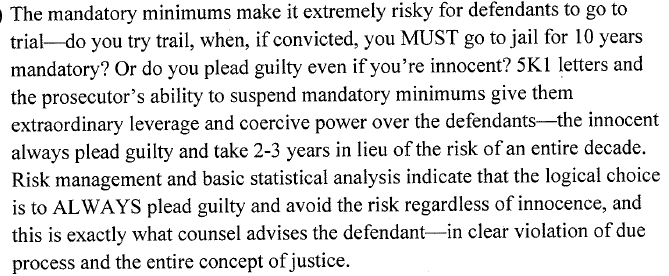
On this point as most others, the Stone prosecution unsurprisingly adopts the same general scope as the Mueller Report; like it, the indictment did not touch on Stone’s role in fostering the Seth Rich conspiracy. That said, prosecutors expended significant effort preventing Stone from using the prosecution to sow propaganda in the court room about Russian attribution (as Yevgeniy Prigozhin’s trolls succeeded in doing).
But the affidavits in the Stone investigation (as we’ve seen elsewhere) break from the pattern. They focus closely on Stone’s social media activity — activity which would ultimately get Stone gagged by Amy Berman Jackson, the judge presiding over his trial, and activity that would get fake accounts created for him starting during the election removed by Facebook. At least eight of the warrants obtained towards the end of the Stone investigation targeted Internet infrastructure used to support social media campaigns.
It’s unclear exactly what investigators were looking for, though. After all, using fake accounts, while a violation of social media terms of service, is not illegal by itself.
For some of these accounts, investigators were collecting forensic data in an effort to tie Stone’s known online activity to very damning Google searches — indicating knowledge of the Russian hack-and-leak while the hackers were still in DNC servers — they believed to be Stone. In addition, the warrant where the investigation started to incorporate evidence and testimony from Steven Bannon listed wire fraud among the crimes under investigation, which prosecutors sometimes charge if someone raises money for one purpose — say, purporting to fund a PAC supporting one cause — and use it for another purpose (this is precisely what got Bannon indicted by SDNY).
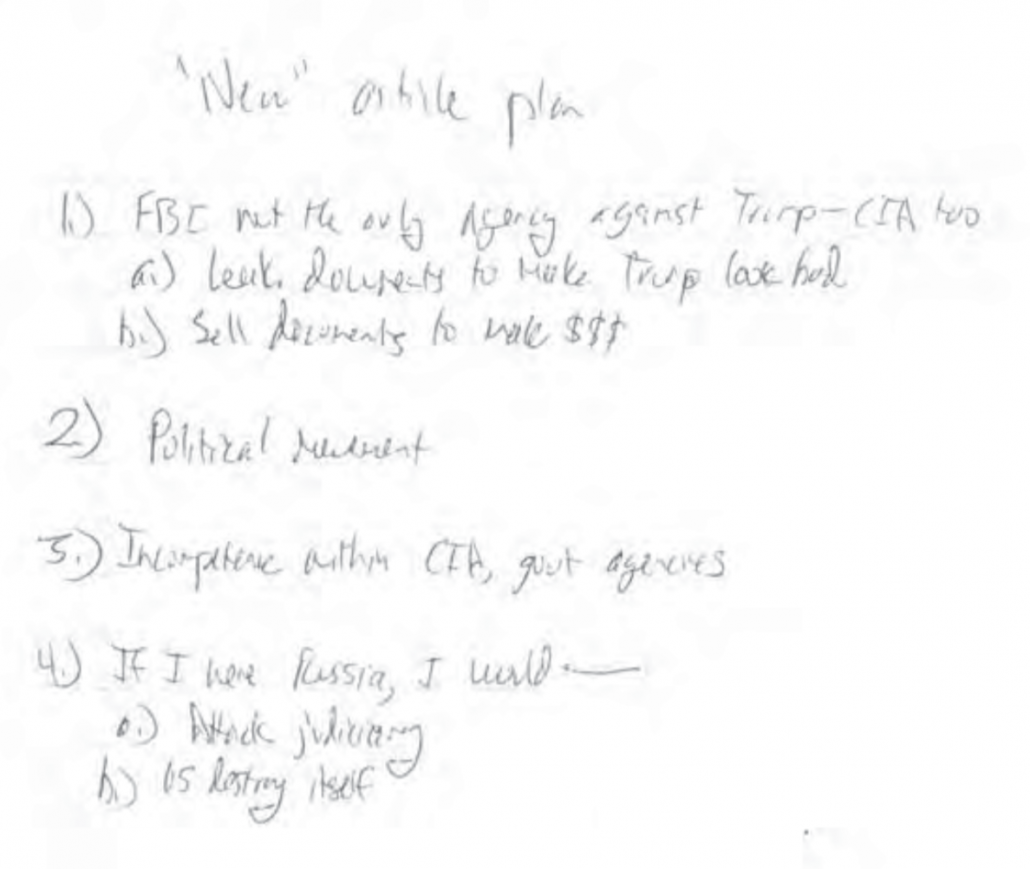
But some of investigators’ focus appears to pertain to the content Stone pushed, his efforts to undermine the Russian attribution, including his sustained claims that Guccifer 2.0 wasn’t Russian. After one of the guys who did social media for him provided details of the effort, investigators started incorporating Stone’s social media activity into affidavits.
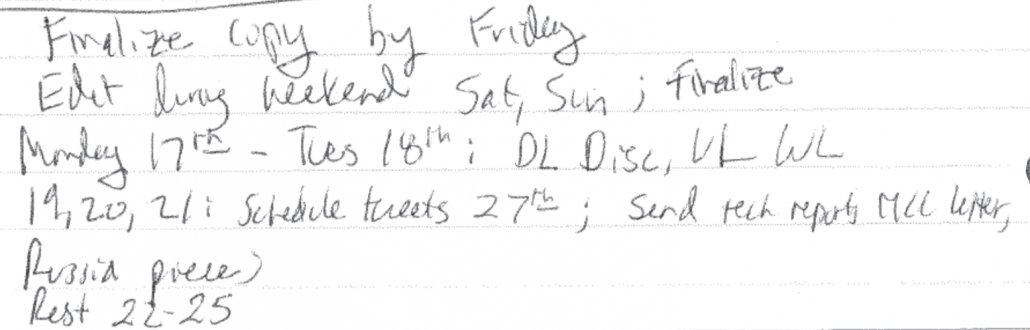
Based on search warrant returns for STONE’s account [redacted], between on or about October 31, 2016 and November 3, 2016, [redacted] received receipts from Facebook for the purchase of a number of advertisements associated with the Target Account, including advertisements with the following excerpted titles (as set forth in the receipts):
- “BREAKING: New #Wikileaks emails prove that Team … “
- “Roger Stone talked about WikiLeaks, Donald Trump, … “
90. Additionally, on or about March 31, 2017, STONE received a Facebook receipt at his Hotmail account for advertisements associated with Target Account 1, with the following excerpted titles (as set forth in the receipt):
- “Stone Rebuts Charge of Russian Collusion”
- “I am not in touch with any Russians, don’t have … ,”
- “The charge that I am working for Russian … ,”
- “In fullest statement yet on DNC hacking … “
- “ROGER STONE – NO consensus that Guccifer 2.0 is a … “
Mueller’s investigators might simply have been tracking the Podesta effort and the later cover-up (though, again, none of it showed up in a trial on the cover-up). But some of the later warrants that included gags, including the one that specifically said prosecutors were trying to keep Stone in the dark about the scope of their investigation, targeted social media, too.
Whatever the point of that investigative focus, Stone at least believed that his efforts to optimize the stolen files could make the difference in getting Trump elected. Moreover, he played a role at key moments in how others understood the provenance of the documents, possibly even in Trump public doubts in the second debate. Stone had more incentive than anyone to claim that Russia wasn’t behind the hack, his efforts to push that narrative were in many ways more sustained than other efforts, and the way in which he tried to rebrand Guccifer 2.0 as something other than a Russian persona was a key claim in his false HPSCI testimony. Indeed, Trump appears to have picked up some of the attacks on Russian attribution that his rat-fucker first pushed, which has since snowballed into a systematic effort to dismantle any part of the government with expertise in Russian operations and organized crime.
And yet the SSCI Report, completed in the wake of and incorporating the affidavits, which incorporated some of the Ukrainian based disinformation still being chased by Republicans, makes little mention of Stone’s campaign to undermine the Russian attribution, and how closely it tied to WikiLeaks’ own such campaign.
The movie Rashomon demonstrated that any given narrative tells just one version of events, but that by listening to all available narratives, you might identify gaps and biases that get you closer to the truth.
I’m hoping that principle works even for squalid stories like the investigation into Roger Stone’s cheating in the 2016 election. This series will examine the differences between four stories about Roger Stone’s actions in 2016:
- The Mueller Report
- The Stone prosecution
- The SSCI Report
- The affidavits from the investigation
As I noted in the introductory post (which lays out how I generally understand the story each tells), each story has real gaps in one or more of these areas:
- While the Mueller Report made it clear Trump’s pardon dangles to keep details of his conversations with Roger Stone secret amounted to obstruction, it didn’t tell just just how many conversations they had
- Rather than telling us whether, how, and why Roger Stone optimized the release of John Podesta’s emails on October 7, 2016, the Mueller Report instead gave us Jerome Corsi slapstick
- Just one story presents the significant amounts of evidence suggesting that on August 14, 2016, when he started a file called “Podesta,” Jerome Corsi had or knew the contents of the Podesta files that would become public on October 11, 2016
- The later stories focus on Podesta, rather than the evidence that Stone learned of the hack-and-leak while the burglary was still ongoing
- Stone pitched both Manafort and Bannon on a way to win ugly–but none of the Stone stories tell us what that was
- Trolling for Russia
- The “highest levels of government” attempt to shut down an investigation into Julian Assange
- Guccifer 2.0 as go-between
My hope is that by identifying these gaps and unpacking what they might say about the choices made in crafting each of these stories, we can get a better understanding of what actually happened — both in 2016 and in the investigations. The gaps will serve as a framework for this series.