Truth Claims, Malaprops, Cows, and the NSA Debate
 I was obviously unexcited about the way last night’s Chiefs-Broncos game went because I made the perhaps ill-advised decision to point out an obvious error in this post from former NSA analyst John Schindler.
I was obviously unexcited about the way last night’s Chiefs-Broncos game went because I made the perhaps ill-advised decision to point out an obvious error in this post from former NSA analyst John Schindler.
He was trying to make a legitimate point — that some of the coverage of the Snowden leaks has conflated total Top Secret/SCI clearance holders with the number of people cleared into the compartments of the documents he took.
As The Guardian has taken center stage in the Snowden drama, serving as the English-language conduit of choice for publishing classified information about the National Security Agency and its partners that was stolen by Edward Snowden, it’s taken heat from the British government about its possibly illegal activities.
As a dodge, Guardian editors have taken to throwing around the “no big deal” excuse because, they claim, 850,000 people in the US, UK, and partner governments had access to this stuff. It was simply Ed, one in an (almost) million, who did the dirty deed. For one of the many iterations of this nonsense see here.
Yet nonsense it is. It plays on the fact the US and Allied governments have given out a lot of high-level clearances in recent years. But it requires a bit of explanation to understand the details – and why The Guardian is lying.
Everybody at NSA – whether military, civilian, or contractor – holds an active TOP SECRET (TS) security clearance with Sensitive Compartmented Information (SCI) access. That’s what it takes to get in the door at NSA.
[snip]
But TS/SCI is just the basic level of clearance at NSA and its partner and Allied agencies. Above that there exist many kinds of caveats and special programs that go (or have gone) by weird names such as GAMMA, VRK (Very Restricted Knowledge), and ECI (Exceptionally Controlled Information). Across DoD they have similar SAPs (Special Access Programs). The bottom line is that nobody at NSA sees “everything.” The entire system is in fact designed to prevent any one person from seeing everything.
The problem, however, is that Schindler made the same kind of stupid error he was accusing the Guardian of. I’ve copied the text above, including the link, as it was first posted and as it remained when I went to bed last night. At both of those times, the link went to this article, which actually didn’t make the claim he said it did (after the several hour exchange we had, he did finally change the link to this letter).
The agencies were supposed to be “selective in which contractors are given exposure to this information”, but it was ultimately seen by Snowden, one of 850,000 people in the US with top-secret clearance.
That is, to prove his case that the Guardian was lying, Schindler originally linked to an article showing the Guardian not making that claim (note, I have no idea what the 850,000 number actually refers to, but the total of TS security clearance holders was 1.4 million this time last year, but that would not include the Brits who had access).
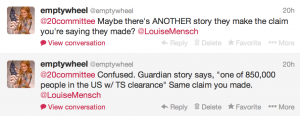
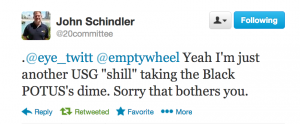
So I asked (tweets are in reverse order),
His immediate response was to accuse me of willful cluelessness. He insisted it was a lie and that I was unable to see what normal people see because I was so lit phd.
it’s a LIE – which you would know if you actually knew anything about NSA & intel. Less lit PhD, more cryptology – #protip
your inability to see what’s clear to normal people is so lit-PhD-cliche it’s terrifying.
He came up with something that was closer to the claim he made, though still not what he accused the Guardian of (though also, I believe, erroneous), but did not change the original erroneous link yet.
The Guardian understands that a total of 850,000 NSA employees and US private contractors with top secret clearance had access to GCHQ databases.
In the middle of it all, he tweeted his “stock phrase,” “This gets easier when you stop lying.”
When I was in #NSA CI I had a stock phrase: “This gets easier when you stop lying.” Now I’m saying it to The Guardian
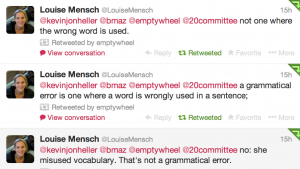
And then it kept going and going and going, punctuated by the troubling comment above and the comedic relief of former Tory MP Louise Mensch coming in to tell me I should respect his expertise and then proceeded to lecture me that “cow” is not a verb (I think she has since deleted these tweets they’re there–I just couldn’t find them) and on what a malaprop isn’t.
While we were all laughing heartily, Schindler added an update and in that update linked to this article, which quoted former Lord Chancellor Falconer making the claim, but did not include such a claim from the Guardian.
Falconer, who also said he deprecated attempts to portray the Guardian as an “enemy of the state”, pointed out that 850,000 people had access to the files leaked by the US whistleblower Edward Snowden.
Falconer, a close ally of Tony Blair who served as lord chancellor from 2003-07, told the Guardian: “I am aware that the three heads of the agencies said what has been published has set back the fight against terrorism for years. Sir John Sawers [the chief of MI6] said al-Qaida would be rubbing their hands with glee. This is in the context of maybe 850,000 people literally having access to this material.”
But still, hours after I first — in what I thought was a fairly polite comment — informed him his link didn’t prove what he said it did.
Several hours into the process, Daveed Garenstein-Ross found several more examples, some of which made the 850K claim, some which didn’t.
Through this entire discussion, I didn’t dispute that Schindler could find an example nor the point of the post — that nowhere near 850K people were cleared for these compartments. I just felt that if Schindler were going to aggressively accuse Guardian of lying, his links ought to back his claims. (See below for the range of other links bandied about last night.)
To me, it served as a metaphor for the larger debate on the NSA, akin to the refusal in some quarters to consider the lies of one’s own side. I suggested Schindler fix an easily fixed error. It took him hours and heaps of insults before he did, before he would hold himself to the same standard he was holding the Guardian to.
Errors happen. Lies do too. All sides have committed both, though clearly the security services seem to be capitalizing on their information asymmetry to try to ensure maximal disinformation and confusion.
But there are still truth claims to be made, with the expectation of evidence. Or there should be. Read more →