Glenn Greenwald is making factually unsupported defenses of Russia on Twitter again.
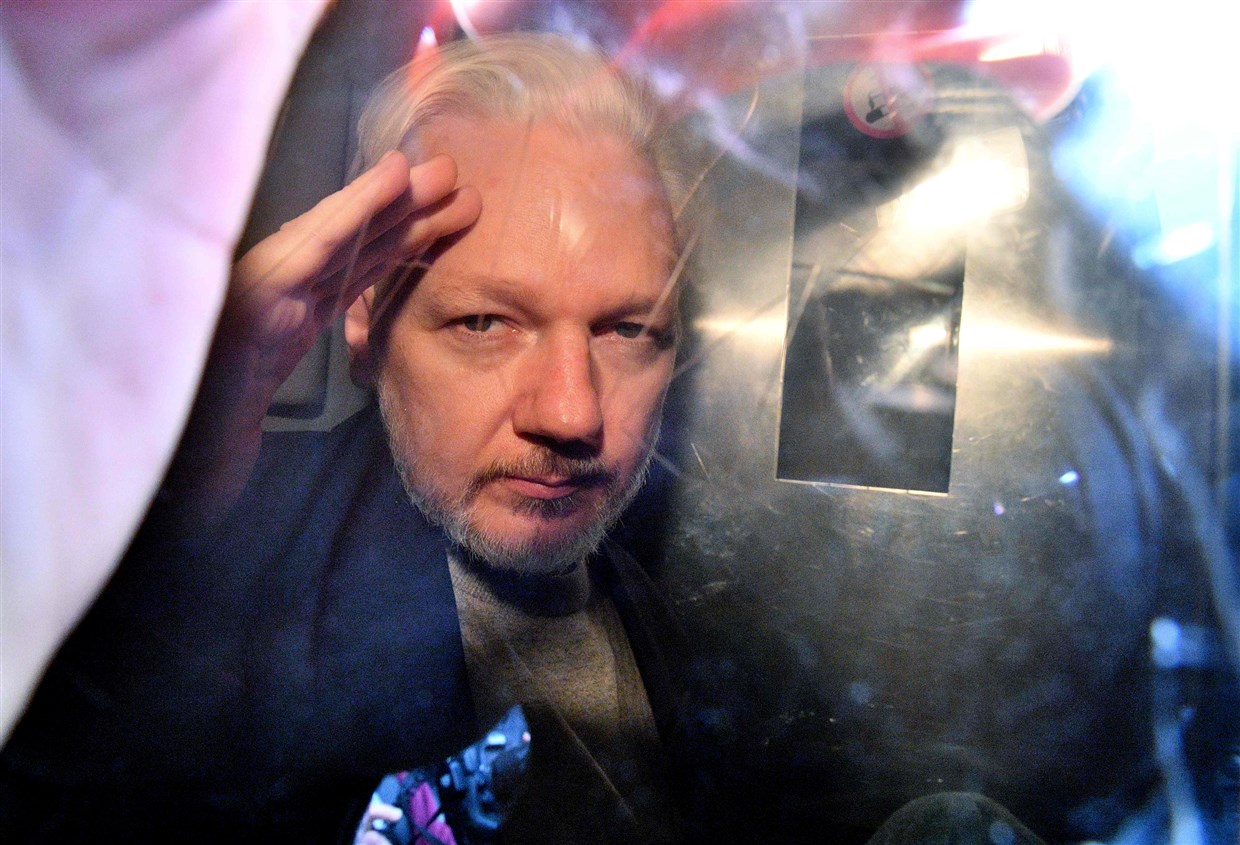
Yesterday, he made an argument about what he sees as one of the most overlooked claims in the Yahoo piece suggesting there was an assassination plot against Julian Assange and then, 100-something paragraphs into the thing, admitting that discussions of killing Assange were really regarded in the CIA as, “a crazy thing that wastes our time.”
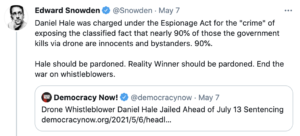
Glenn doesn’t, apparently, think the overlooked detail is that the timeline in the story describing the changing US government understanding towards Assange, including Edward Snowden’s central role in that, shows that Assange’s defense lied shamelessly about the timeline in his extradition hearing.
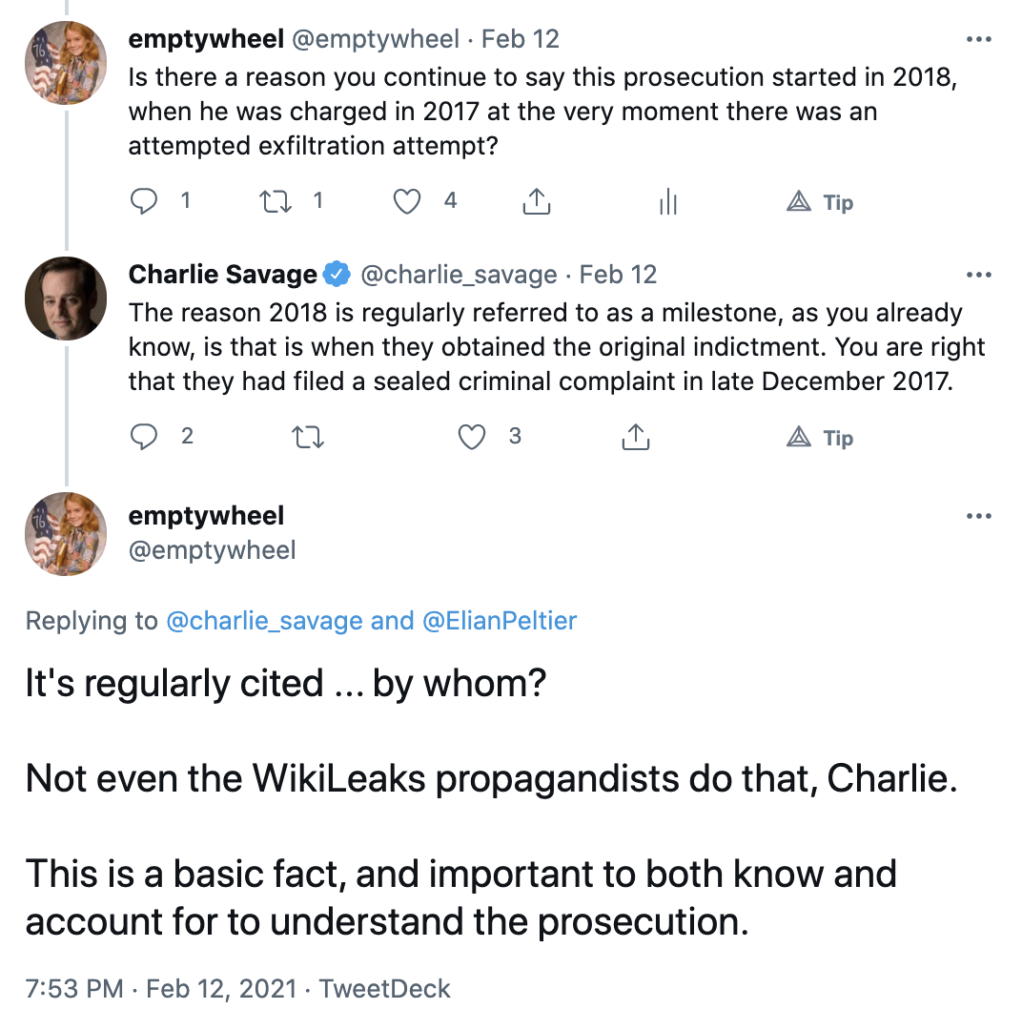
Nor does Glenn seem interested that DOJ didn’t charge Assange during the summer of 2017 after Mike Pompeo started plotting against the Australian, but only did so on December 21, 2017, as the US and UK prepared for what they believed to be an imminent exfiltration attempt by Russia.
Intelligence reports warned that Russia had its own plans to sneak the WikiLeaks leader out of the embassy and fly him to Moscow, according to Evanina, the top U.S. counterintelligence official from 2014 through early 2021.
The United States “had exquisite collection of his plans and intentions,” said Evanina. “We were very confident that we were able to mitigate any of those [escape] attempts.”
[snip]
Narvaez told Yahoo News that he was directed by his superiors to try and get Assange accredited as a diplomat to the London embassy. “However, Ecuador did have a plan B,” said Narvaez, “and I understood it was to be Russia.”
Aitor Martínez, a Spanish lawyer for Assange who worked closely with Ecuador on getting Assange his diplomat status, also said the Ecuadorian foreign minister presented the Russia assignment to Assange as a fait accompli — and that Assange, when he heard about it, immediately rejected the idea.
On Dec. 21, the Justice Department secretly charged Assange, increasing the chances of legal extradition to the United States. That same day, UC Global recorded a meeting held between Assange and the head of Ecuador’s intelligence service to discuss Assange’s escape plan, according to El País. “Hours after the meeting” the U.S. ambassador relayed his knowledge of the plan to his Ecuadorian counterparts, reported El País.
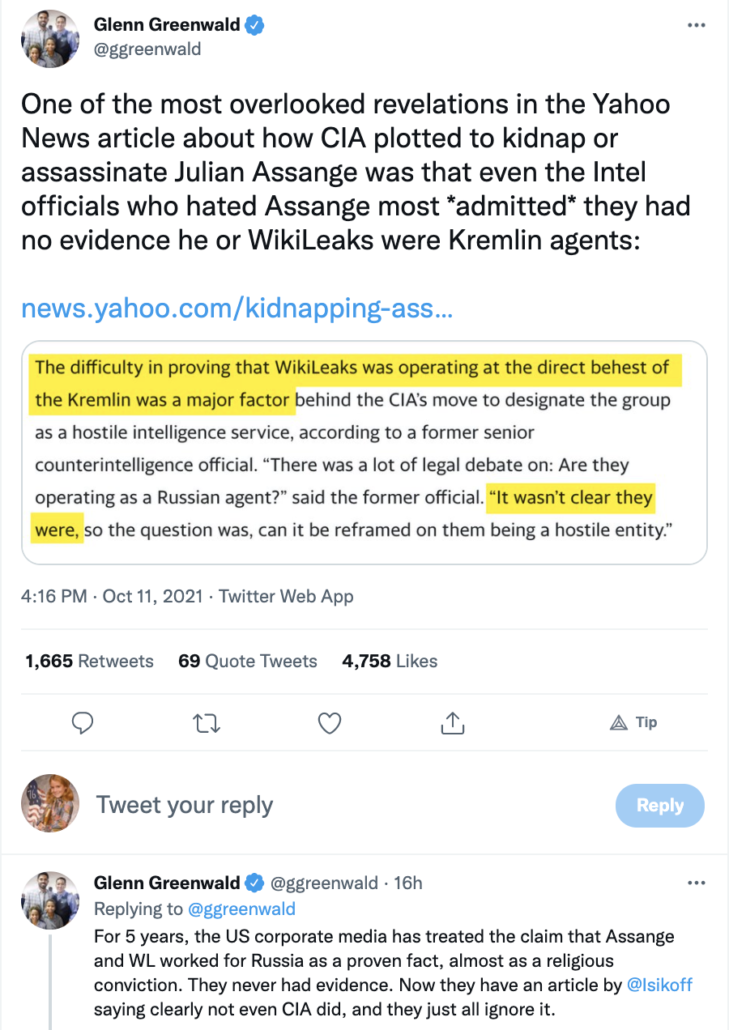
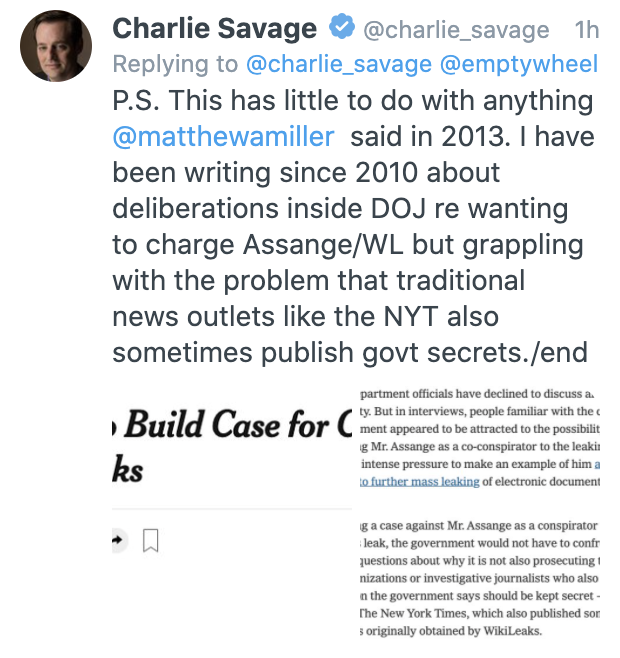
What Glenn thinks is important is that, on April 13, 2017, when Mike Pompeo labeled WikiLeaks a non-state hostile intelligence service, the CIA did not yet have proof that “WikiLeaks was operating at the direct behest of the Kremlin,” though of course Glenn overstates this and claims that they had “no evidence.”
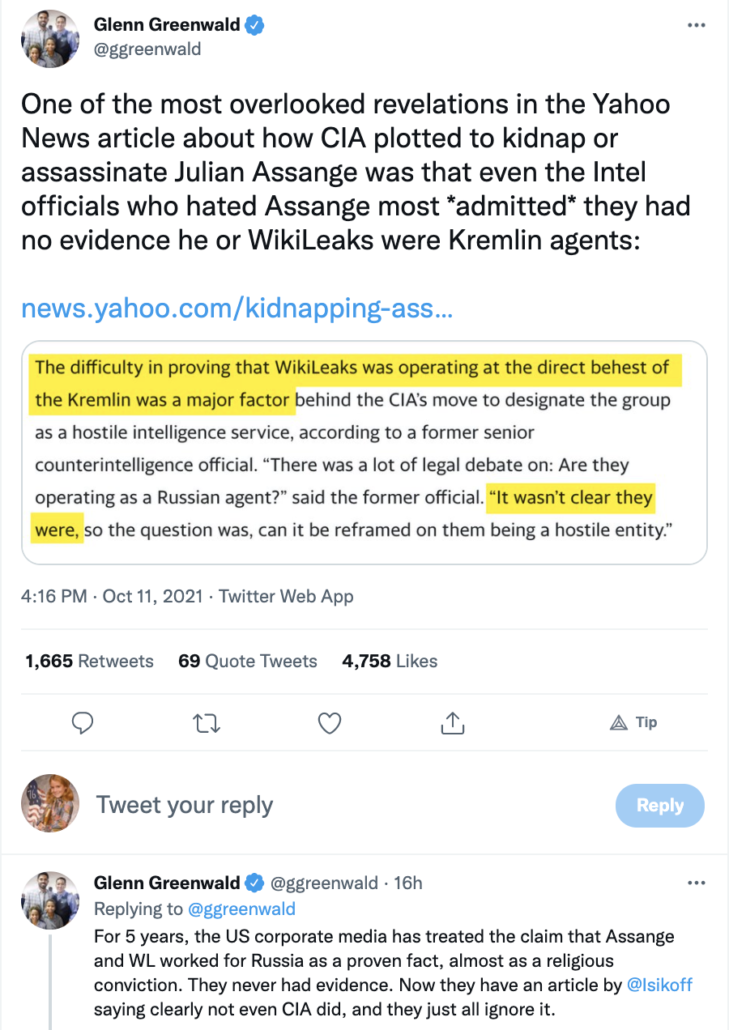
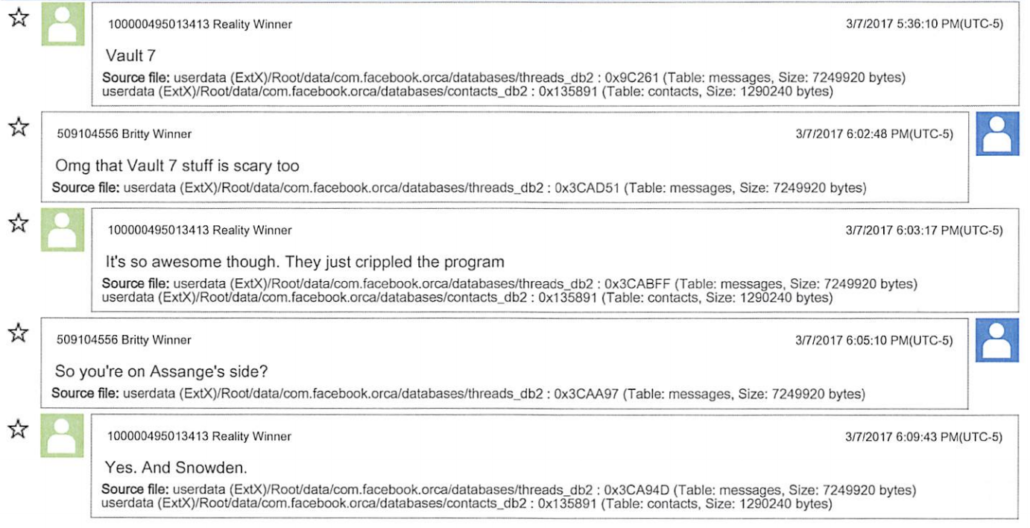
Glenn then claimed that CIA’s lack of proof on April 13, 2017 is proof that all claims about Assange’s ties with Russia made in the last five years — that is, from roughly October 7, 2016 through October 12, 2021 — lacked (any!) evidence. In other words, Glenn claims that CIA’s lack of proof, before UC Global ratcheted up surveillance against Assange in June 2017 and then ratcheted it up much more intensively in December 2017, and before US intelligence discovered the Russian exfiltration attempt, and before they had enough evidence to charge Joshua Schulte in 2018, and before they seized Assange’s computer in 2019, and before Snowden wrote a book confirming WikiLeaks’ intent in helping him flee, is proof that they never acquired such proof in the 1600 days since then.
At the time Pompeo made his comments, FBI was just five weeks into the Vault 7 investigation. They were chasing ghosts in the Shadow Brokers case, which also implicated Assange. Robert Mueller had not yet been appointed and, perhaps a month after he was, Andrew Weissmann discovered that, “the National Security Division was not examining what the Russians had done with the emails and other documents they’d stolen from those servers.” Pompeo’s comments came four months before Mueller obtained the first warrant targeting Roger Stone. They came seven months before Mueller obtained a warrant targeting Assange’s Twitter account. They came sixteen months before Mueller obtained a warrant describing a hacking and foreign agent investigation into WikiLeaks and others. They came 25 months before Mueller released his report while redacting the revelation that multiple strands of the investigation into Stone were ongoing (though also stating they did not have enough admissible evidence to prove Assange knew that Russia continued to hack the DNC). They came three years before DOJ kept the warrants reflecting the foreign agent investigation into WikiLeaks and others largely redacted, presumably because that investigation remained ongoing. They came three and a half years before the government withheld almost all of WikiLeaks lawyer Margaret Kunstler’s two interviews with Mueller’s team because of an ongoing investigation.
And all that’s separate from the long-standing WikiLeaks investigation at EDVA that led to Assange’s charges, which Rod Rosenstein has said never fully moved under Mueller.
On April 13, 2017, the investigation into Assange’s activities in 2016 had barely begun. Yet the fact that CIA couldn’t prove Assange was a Russian agent before most investigation into these things had started, Glenn claims, is proof that Assange is not a Russian agent.
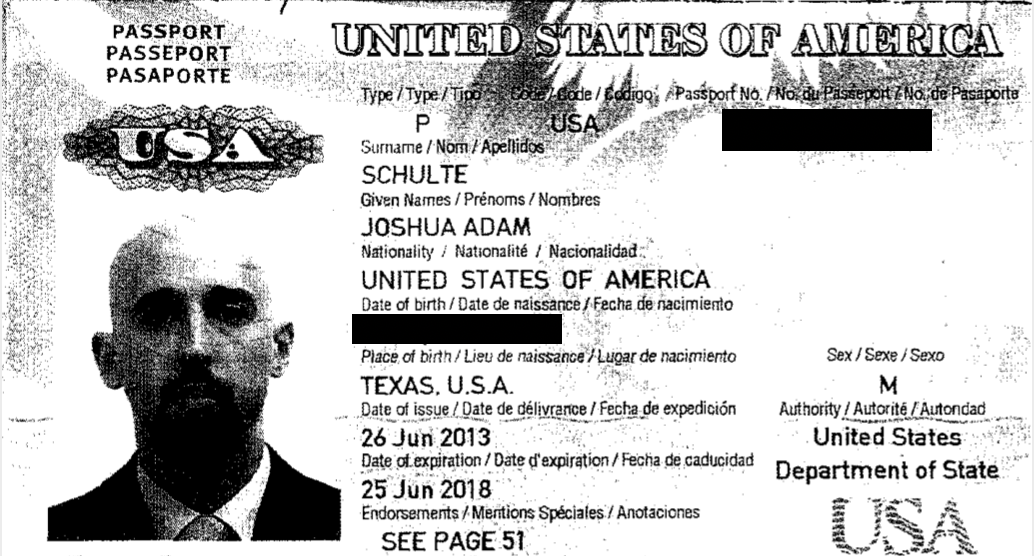
It’s a logically nonsensical argument, but because certain gullible WikiLeaks boosters don’t see the flaws in the argument, I’d like to point to something fascinating disclosed just recently in the Joshua Schulte case: as late as September 2019, DOJ was still trying to get a full forensic image of the the phone Schulte was using when he was first interviewed on March 15, 2017.
That was revealed in the government’s response to a Schulte motion to suppress evidence from the Huawei he used at the time, in the early stages of the FBI’s investigation. We saw many of these warrants from Schulte’s first attempt to get these early warrants suppressed (in which his attorney noted that the government got a second device-specific warrant). But Schulte is challenging the search on a basis that even Sabrina Shroff didn’t raise two years ago.
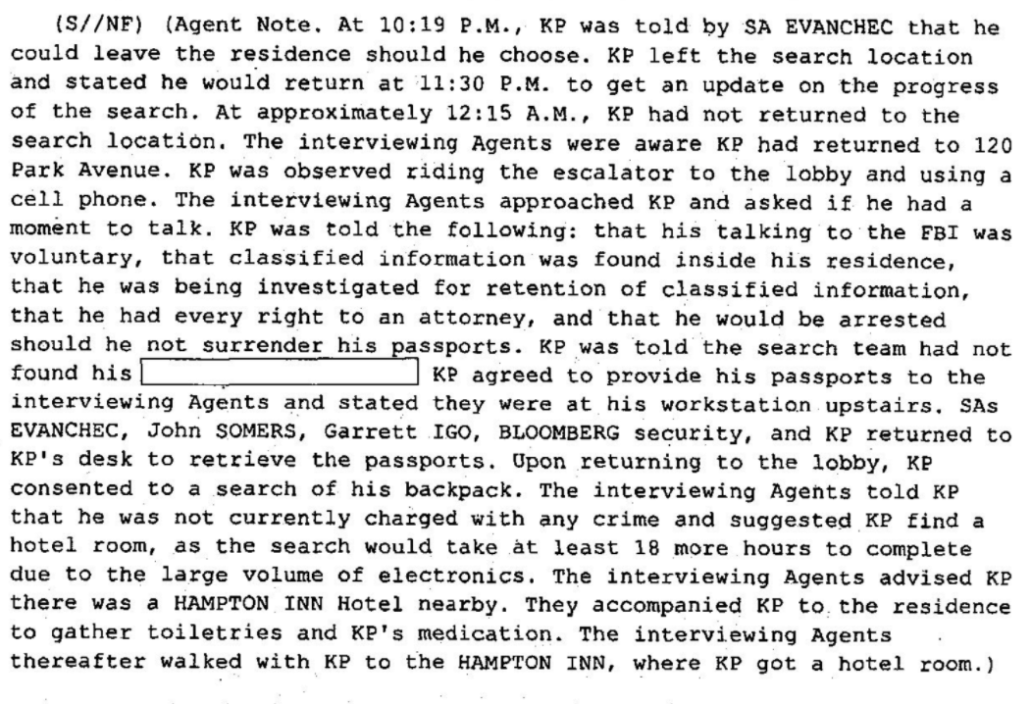
As the government tells it, FBI agents used a subpoena to get Schulte to hand over his phone during the interview on March 15 before they all returned to his apartment where they had a warrant for all his devices, then got a separate warrant at 1:26AM that night to search the phone specifically. They were unable to do so because it was locked, so in an interview on March 21 — at which time the search warrant was still valid — they got Schulte to open his phone (something his attorney at the time boasted he did voluntarily during a 2017 bail hearing).
Someone must have lost their job at FBI, though, because after Schulte opened the phone, it rebooted, preventing them from obtaining a full forensic copy of the device.
On March 20 and 21, 2021, the defendant, accompanied by his attorneys, was interviewed by the Government and law enforcement agents at the U.S. Attorney’s Office. At the interview on March 21, 2021, the defendant, in the presence of counsel, consented to a search of the Cellphone and entered his password to unlock it. (Id. ¶ 13(b)). When the Cellphone was unlocked, however, it rebooted, and FBI was able to obtain only a logical copy of the Cellphone rather than a complete forensic image. (Id. ¶ 13(c)).
However, in its response to Schulte, the government is relying on two documents that it released for the first time. First, a location warrant/pen register targeting three different phones, which the government submitted to show that Schulte’s Google history obtained on March 14 showed that he searched for ways to delete files in the time period he is accused of stealing the CIA files and deleting evidence of doing so. The affidavit is useful for explaining how Schulte was using phones in that period of 2017. In addition to the Huawei, for example, Schulte had a phone with a Virginia number he used to call at least one of his CIA colleagues between March 7 and when he canceled the phone on March 12. Then, after he gave the FBI his Huawei phone, he bought one that night he used to call Bloomberg (his employer), and another on March 17.
More importantly, the government released the affidavit and warrant from September 9, 2019, providing more explanation why they weren’t able to fully exploit the phone in 2017.
After Schulte unlocked the phone, FBI personnel attempted to forensically image the Subject Device so that the FBI could review its contents. However, because the Subject Device rebooted during that process, the FBI was able to obtain only a logical forensic image of the Subject Device (the “Logical Forensic Image”). Although the Logical Forensic Image contains some content from the Subject Device, the Logical Forensic Image does not contain all data that may be on the Subject Device, including deleted information and data from applications. The data and information from the Subject Device that is missing from the Logical Forensic Image would likely be captured on a complete forensic image of the phone (“Complete Forensic Image”). However, in March 2017, the FBI was unable to obtain a Complete Forensic Image of the Subject Device because the Subject Device locked after it rebooted and the FBI did not know the password to unlock the phone again to attempt to obtain a Complete Forensic Image.
On or about August 12, 2019, FBI personnel involved in this investigation successfully unlocked the Subject Device using a portion of a password identified during the course of the investigation (“Password-1”). Forensic examiners with the FBI believe that they will be able to obtain a Complete Forensic Image of the Subject Device using Password-1.
After unlocking the Subject Device using Password-1, an FBI agent promptly contacted the Assistant United States Attorneys involved in this investigation to inform them of this development, and the decision was made to seek a warrant to search the Subject Device for evidence, fruits, and instrumentalities of the Subject Offense.
The affidavit explains, among other things, that Schulte first obtained the phone on September 21, 2016 and logged into Google right away (somewhere in the vast paperwork released in the case, Schulte admitted that Google was his big weakness — and how!).
In the government response, they describe that the government did search the phone. They say the phone contains images of a woman Schulte lived with that he was charged, in Virginia, with assaulting in 2015.
The FBI searched the Cellphone pursuant to that warrant. The Cellphone contains, among other things, images of an individual identified as Victim-1 in the Government’s prior filings.
It’s an interesting defense of the import of the warrant. As the government explained in 2017 when it first informed Judge Paul Crotty of the Virginia assault charge, the incriminating photos had already been found on one of Schulte’s phones (it’s unclear whether these were found on the Huawei or the phone shut down on March 12), so the State of Virginia presumably doesn’t need any images discovered after 2019 to prosecute him on the assault charge.
As relevant here, the Government discussed several photographs recovered from the defendant’s cellphone that depicted an unknown individual using his hands to sexually assault an unconscious female woman (the “Victim”). (See Exhibit A, Aug. 24, 2017 Tr. at 12-13). At the time, the Government was aware that the Victim knew the defendant and had lived in his apartment as a roommate in the past. (Id.) Magistrate Judge Henry B. Pitman, who presided over the presentment, did not consider the information proffered by the Government regarding the Victim, explaining that “facts have [not] been proffered that . . . tie Mr. Schulte to the conduct in that incident.” (Id. at 48-89). Nevertheless, Judge Pitman detained the defendant concluding that the defendant had not rebutted the presumption that he was a danger to the community. (Id. at 47-49).
[snip]
On or about November 15, 2017, the defendant was charged in Loudoun County Virginia with two crimes: (i) object sexual penetration, a felony, in violation Virginia Code Section 18.2-67.2; and (ii) the unlawful creation of an image of another, a misdemeanor, in violation of Virginia Code Section 18.2-386.1. The Government understands that these charges are premised on the photographs of the Victim. Specifically, the Loudoun County Commonwealth’s Attorneys Office has developed evidence that the defendant was the individual whose hands are visible in the photographs sexually penetrating the Victim.
But whatever they found on the phone, the government made an effort to make clear that even this 2019 search — which might have obtained deleted WhatsApp or Signal texts, both of which Schulte has used — was covered by a search warrant, something Schulte is currently trying to suppress only on a poison fruit claim.
This wasn’t the only evidence the government obtained years after Schulte became the primary suspect, though. They didn’t obtain full cooperation from Schulte’s closest buddy from when he was at the CIA, Michael, until January 2020, just before his first trial (which is one of the reasons the government provided fatally late notice to Schulte that the friend had been placed on leave at CIA). Michael helped Schulte buy the disk drives the government seems to suspect Schulte used in the theft, he also knew of Schulte’s gaming habits, and the CIA believed he might know more about Schulte’s theft from CIA.
So it’s clear that for most of the time that Glenn says the investigation as it stood in April 2017 must reflect all the evidence about Schulte, Assange, and Russia, the government continued to investigate.
None of that says DOJ obtained information from Schulte in that time implicating Assange in ties with Russia (though, as I’ve noted, someone close to WikiLeaks told me Schulte reached out to Russia well before ambiguous references to Russia showed up at Schulte’s trial). But to suggest all the evidence the government might now have was already in their possession on April 13, 2017, requires ignoring everything that has happened since that time.
Timeline
October 7, 2016: In statement attributing DNC hack to Russia, DHS and ODNI include documents released by WikiLeaks; an hour later WikiLeaks starts Podesta release
January 6, 2017: Intelligence Community Assessment assesses, with high confidence, that GRU released stolen documents via exclusives with WikiLeaks
March 7, 2017: First Vault 7 release, including unredacted names of key CIA developers
March 13, 2017: Affidavit supporting covert warrant approving search of Schulte’s apartment, including the devices found there
March 14, 2017: Affidavit supporting overt warrant approving search of Schulte’s apartment, including devices
March 14, 2017: Search warrants for Schulte’s Google account and other electronic accounts
March 15, 2017: 302 from interview with Schulte and testimonial subpoena and cell phone subpoena handed to him at interview
March 16, 2017: Affidavit supporting search warrant authorizing search of Schulte’s Huawei smart phone
March 31, 2017: Warrant and pen register for three different Schulte phones — one serviced by Sprint that he had used through all of 2016 but canceled on March 12, 2017, one he obtained after his phone was seized on March 15, 2017 serviced by Virgin, another he bought on March 17, 2017 serviced by AT&T
April 13, 2017: Mike Pompeo declares WikiLeaks a non-state hostile intelligence service
May 17, 2017: Robert Mueller appointed
August 7, 2017: Mueller obtains first warrant targeting Stone, covering hacking
August 23, 2017: Schulte charged with possession of child pornography
September 6, 2017: Schulte indicted on child pornography charges
September 26, 2017: Roger Stone testifies before HPSCI, lies about source for advance knowledge
October 19, 2017: Stone falsely claims Credico is his intermediary with WikiLeaks
November 6, 2017: Mueller obtains warrant targeting Assange’s Twitter account, citing hacking, conspiracy, and illegal foreign political contribution
November 8, 2017: Schulte claims to have been approached by foreign spies on Subway between his house and court appearance
November 9, 2017: WikiLeaks releases source code, billing it Vault 8
November 14, 2017: Assange invokes CIA’s source code (Vault 8) in suggesting Don Jr should get him named Ambassador to the US
November 16, 2017: Schulte tells FBI story about approach on Subway, accesses Tor
November 17, 2017: Schulte accesses Tor
November 26, 2017: Schulte accesses Tor
November 30, 2017: Schulte accesses Tor
December 5, 2017: Schulte accesses Tor
December 7, 2017: Schulte detained pursuant to charges of sexual assault in VA and violating release conditions
December 12, 2017: Randy Credico invokes the Fifth
December 21, 2017: Assange first charged with CFAA charge
March 6, 2018: Assange indicted on single CFAA charge
June 18, 2018: Superseding Schulte indictment adds Vault 7 leak charges
June 19, 2018: WikiLeaks links to Schulte diaries
August 20, 2018: Mueller obtains warrant describing investigation of WikiLeaks and others into conspiracy, hacking, illegal foreign contribution, and foreign agent charges
September 25, 2018: Schulte posts diaries from jail
October 31, 2018: Second Schulte superseding indictment adds charges for leaking from MCC
April 11, 2019: Assange seized from Embassy
May 23, 2019: Superseding Assange indictment adds Espionage Act charges
August 16, 2019: After FBI interview, CIA places Schulte buddy, “Michael” on leave
September 9, 2019: Affidavit in support of warrant authorizing search of Huawei phone
February 4, 2020: Schulte trial opens
February 12, 2020: Schulte attorneys reveal “Michael” was put on paid leave in August 2019
March 6, 2020: In effort to coerce Jeremy Hammond to testify, AUSA twice tells Hammond that Julian Assange is a Russian spy
March 9, 2020: Judge Paul Crotty declares mistrial on most counts in Schulte case
April 28, 2020: DOJ continues to redact Foreign Agent warrants targeting WikiLeaks and others because of ongoing investigation
June 8, 2020: Third superseding Schulte indictment adds clarification to the charges
June 24, 2020: Second superseding Assange indictment extends CFAA conspiracy through 2015, citing efforts to use Snowden to recruit more leakers
November 2, 2020: BuzzFeed FOIA reveals that Mueller referred “factual uncertainties” regarding possible Stone hacking charge to DC US Attorney for further investigation, but also finding that it did not have admissible evidence that Assange knew Russia continued to hack the DNC
September 3, 2021: Schulte submits motion to suppress cell phone content
September 31, 2021: Schulte’s motion to suppress docketed
October 1, 2021: Government response to Schulte motion to suppress