The Tommy Tuberville Gap in the Trump Indictment
The release of details about Dan Scavino’s testimony in Trump’s January 6 case made me realize something: Trump’s call to Tommy Tuberville around 2:26PM on January 6 isn’t in the indictment.
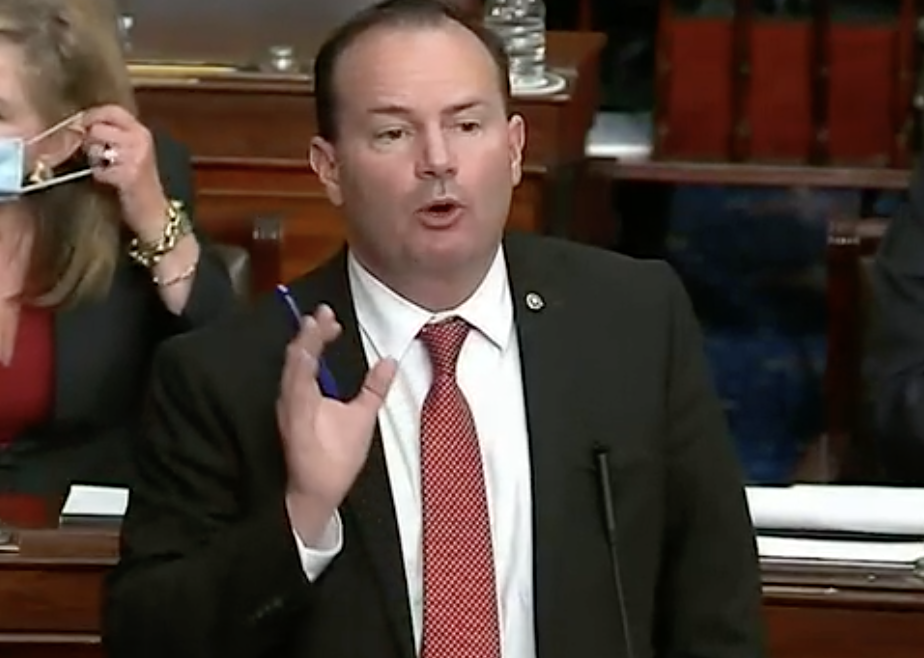
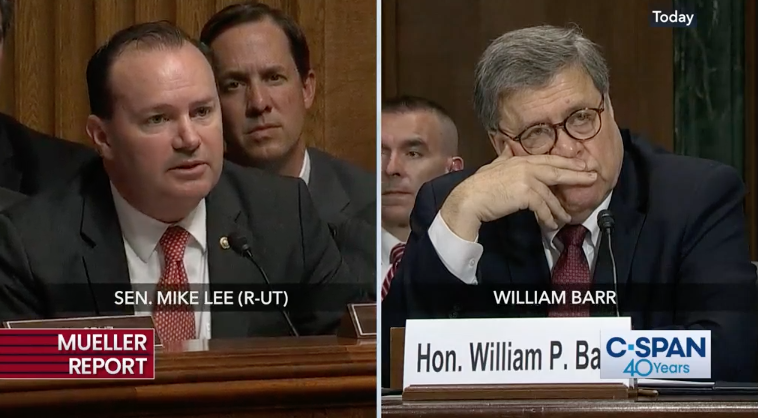
As you’ll recall, Trump attempted to call Tommy Tuberville, but instead got Mike Lee’s phone. Back before he became Based Mike Lee, the Utah Senator told the local UT press what happened next.
With a mob of election protesters laying siege to the U.S. Capitol, Sen. Mike Lee had just ended a prayer with some of his colleagues in the Senate chamber when his cellphone rang.
Caller ID showed the call originated from the White House. Lee thought it might be national security adviser Robert O’Brien, with whom he’d been playing phone tag on an unrelated issue. It wasn’t O’Brien. It was President Donald Trump.
“How’s it going, Tommy?” the president asked.
Taken a little aback, Lee said this isn’t Tommy.
“Well, who is this? Trump asked. “It’s Mike Lee,” the senator replied. “Oh, hi Mike. I called Tommy.”
Lee told the Deseret News he realized Trump was trying to call Sen. Tommy Tuberville, the newly elected Republican from Alabama and former Auburn University football coach. Lee walked his phone over to Tuberville who was talking to some colleagues.
“Hey, Tommy, I hate to interrupt but the president wants to speak with you,” Lee said.
Tuberville and Trump talked for about five to 10 minutes, Lee said, adding that he stood nearby because he didn’t want to lose his cellphone in the commotion. The two were still talking when panicked police ordered the Capitol to be evacuated because people had breached security.
As police were getting anxious for senators to leave, Lee walked over to retrieve his phone.
“I don’t want to interrupt your call with the president, but we’re being evacuated and I need my phone,” he said.
Tuberville said, “OK, Mr. President. I gotta go.”
Tuberville, in real time with impeachment, confirmed the substance of the call.
Sen. Tommy Tuberville revealed late Wednesday that he spoke to Donald Trump on Jan. 6, just as a violent mob closed in on the the Senate, and informed the then-president directly that Vice President Mike Pence had just been evacuated from the chamber.
“I said ‘Mr. President, they just took the vice president out, I’ve got to go,’” Tuberville (R-Ala.) told POLITICO on Capitol Hill on Wednesday night, saying he cut the phone call short amid the chaos.
During impeachment, Lee released call records that (at the time) undercut something Democrats were suggesting about the call: that Trump may have been told by Tuberville about the mob before he sent the Tweet targeting Pence. Lee also tried to get any mention of the call — the call he had revealed — stricken from the Congressional Record.
Back on February 14, 2021 — a good ten months before Liz Cheney and through her the TV lawyers discovered Trump’s exposure on this count — I argued that was compelling evidence that Trump had obstructed the vote certification.
Trump’s indictment does describe efforts he and Rudy Giuliani and Co-Conspirator 6 (who is most likely Boris Epshteyn) made to get Congress to further delay the vote count, later in the day (perhaps hoping the Coffee County caper would provide cause to create more delay). But it places those efforts later, during the evening.
119. On the evening of January 6, the Defendant and Co-Conspirator 1 attempted to exploit the violence and chaos at the Capitol by calling lawmakers to convince them, based on knowingly false claims of election fraud, to delay the certification, including:
[Per ABC report, Trump showed Nick Luna a draft Tweet here]
a. The Defendant, through White House aides, attempted to reach two United States Senators at 6:00 p.m.
[Tweet released, an hour later Trump cut off Twitter]
b. From 6:59 p.m. until 7:18 p.m., Co-Conspirator 1 placed calls to five United States Senators and one United States Representative.
c. Co-Conspirator 6 attempted to confirm phone numbers for six United States Senators whom the Defendant had directed Co-Conspirator 1 to call and attempt to enlist in further delaying the certification.
d. In one of the calls, Co-Conspirator 1 left a voicemail intended for a United States Senator that said, “We need you, our Republican friends, to try to just slow it down so we can get these legislatures to get more information to you. And I know they’re reconvening at eight tonight but the only strategy we can follow is to object to numerous states and raise issues so that we get ourselves into tomorrow-ideally until the end of tomorrow.”
e. In another message intended for another United States Senator, CoConspirator 1 repeated knowingly false allegations of election fraud, including that the vote counts certified by the states to Congress were incorrect and that the governors who had certified knew they were incorrect; that “illegal immigrants” had voted in substantial numbers in Arizona; and that “Georgia gave you a number in which 65,000 people who were underage voted.” Co-Conspirator 1 also claimed that the Vice President’s actions had been surprising and asked the Senator to “object to every state and kind of spread this out a little bit like a filibuster[.]”
There’s no mention of the call that Trump made at around 2:26.
111. At 2:24 p.m., after advisors had left the Defendant alone in his dining room, the Defendant issued a Tweet intended to further delay and obstruct the certification: “Mike Pence didn’t have the courage to do what should have been done to protect our Country and our Constitution, giving States a chance to certify a corrected set of facts, not the fraudulent or inaccurate ones which they were asked to previously certify. USA demands the truth!”
112. One minute later, at 2:25 p.m., the United States Secret Service was forced to evacuate the Vice President to a secure location.
[Tommy Tuberville call took place here]
113. At the Capitol, throughout the afternoon, members of the crowd chanted, “Hang Mike Pence!”; “Where is Pence? Bring him out!”; and “Traitor Pence!”
114. The Defendant repeatedly refused to approve a message directing rioters to leave the Capitol, as urged by his most senior advisors-including the White House Counsel, a Deputy White House Counsel, the Chief of Staff, a Deputy Chief of Staff, and a Senior Advisor. [my emphasis]
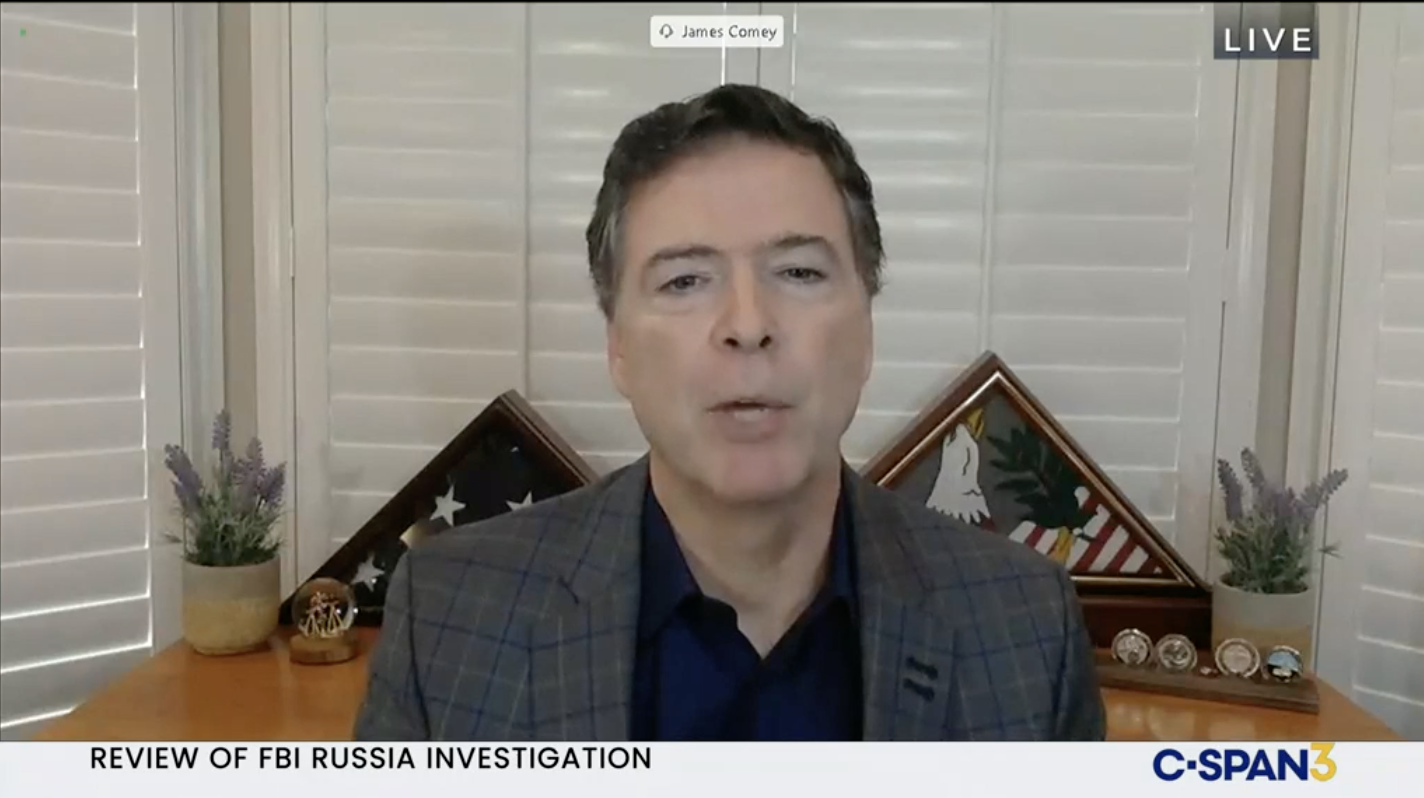
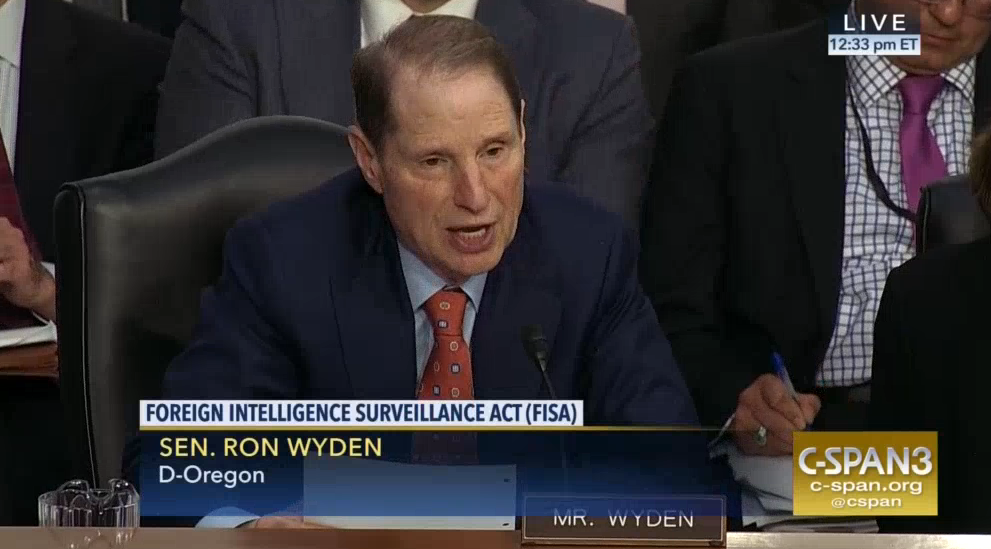
Two people who might be interested in the Scavino testimony released the other day, then, are Senators Lee and Tuberville. They’ve now been told that Scavino testified that he was not in the room when that call was placed (consistent with the indictment’s claim that Trump had been left alone in the dining room), meaning there’s no witness to the call besides Trump and the two Senators, both of whom would be protected from compelled testimony under Speech and Debate.
If Scavino’s testimony ever were to change, if Scavino ever were to recall witnessing that call, it would be among the most damaging evidence available: proof that in the wake of Pence’s evacuation, Trump turned immediately to stalling doubling down on the advantage he had won.
Instead, prosecutors are left with the later calls, which can be introduced under a co-conspirator hearsay exception.
Still, it’s telling: While Trump’s advisors were someplace else squabbling about whether Scavino was responsible for that Tweet that might get Mike Pence killed, Trump was (presumably still alone) seeking more delay.