Rat-Fucker Rashomon: Steve Bannon and Dirty Tricks
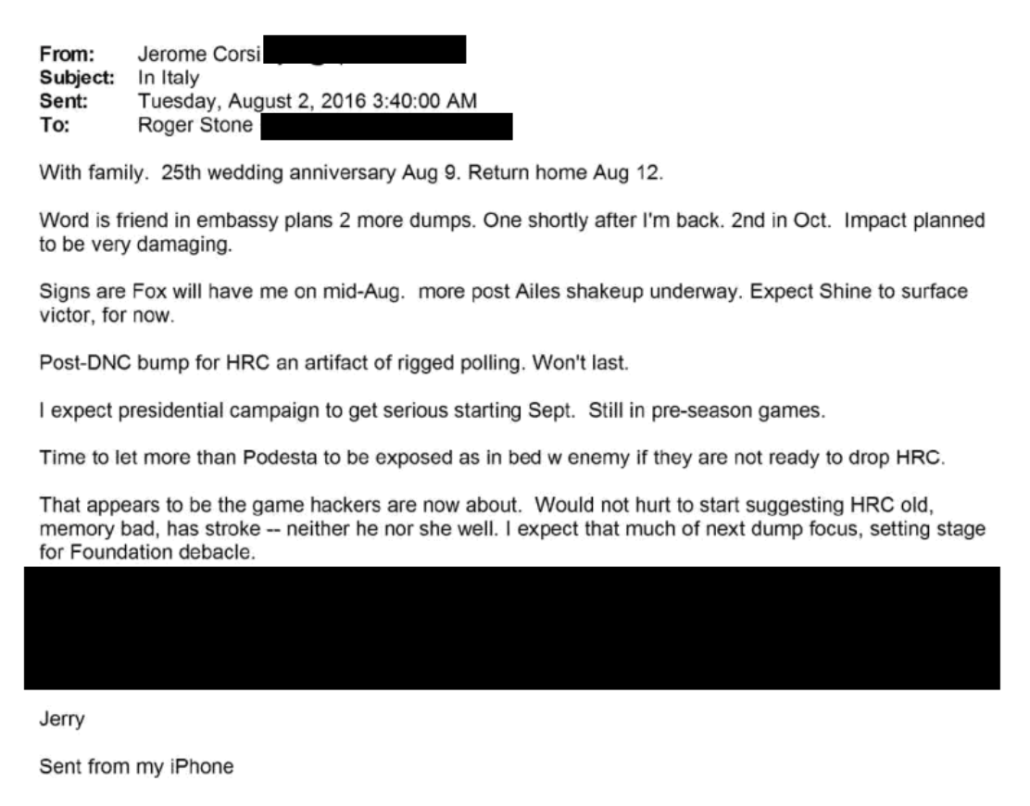
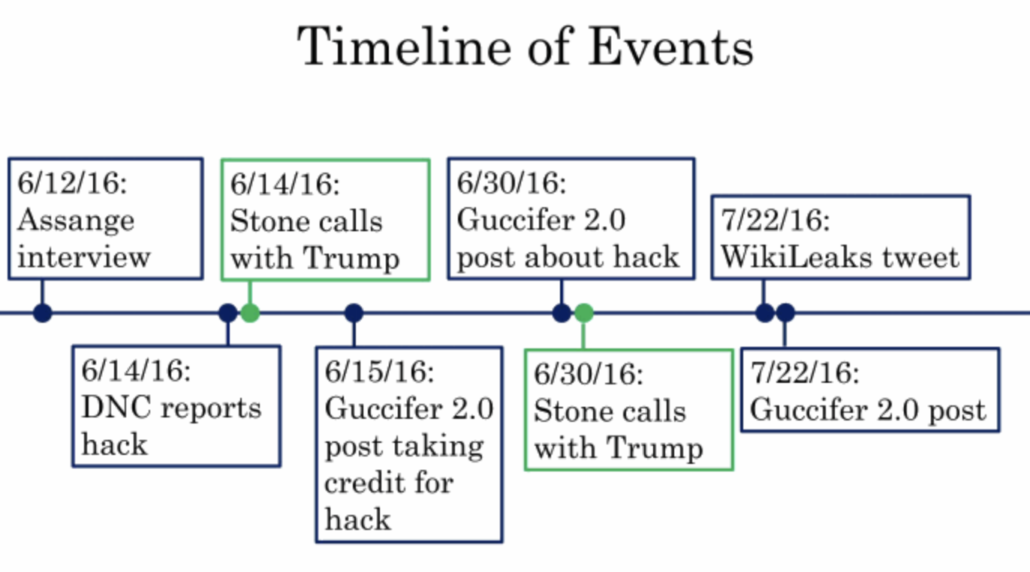
Thus far in my Rat-Fucker Rashomon story, I’ve shown strong evidence that Roger Stone not only knew that John Podesta’s emails were coming, but knew or had the contents of some documents pertaining to an attack he had already been making on John Podesta. I showed that the timing of that release — via whatever means — likely served more to drown out the Russian attribution than the Access Hollywood tape, which has important implications for how he might have coordinated with WikiLeaks. And I suggested that the evidence Stone had far earlier knowledge of what the Russians were doing, even during the period when they were still hacking the DNC’s servers, makes some of all this focus on Podesta less important.
But there’s a limit to that claim. That’s because we still don’t know whether, when Stone promised he knew how to get Trump elected in the same period he was pursuing the Podesta files, that plan consisted just of optimizing the Podesta files, or whether there was something more. That makes the stories not told at Roger Stone’s trial all the more exasperating.
One of the most unsatisfying aspects of the Roger Stone trial, particularly for inattentive watchers, was that prosecutors never told us how Stone had gotten advance knowledge of what stolen emails would be released — nor even asserted as fact that he did.
As I keep noting, that’s not what they had to prove to win a guilty verdict.
But even more frustrating is the way DOJ proved its case that Stone had discussed WikiLeaks with the campaign. On at least three different occasions, the prosecution pointed to far more enticing communications about what really happened, but did not tell us what those communications meant.
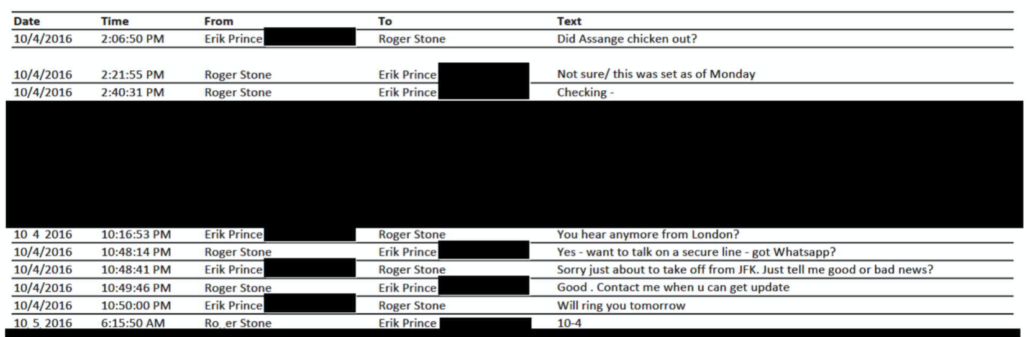
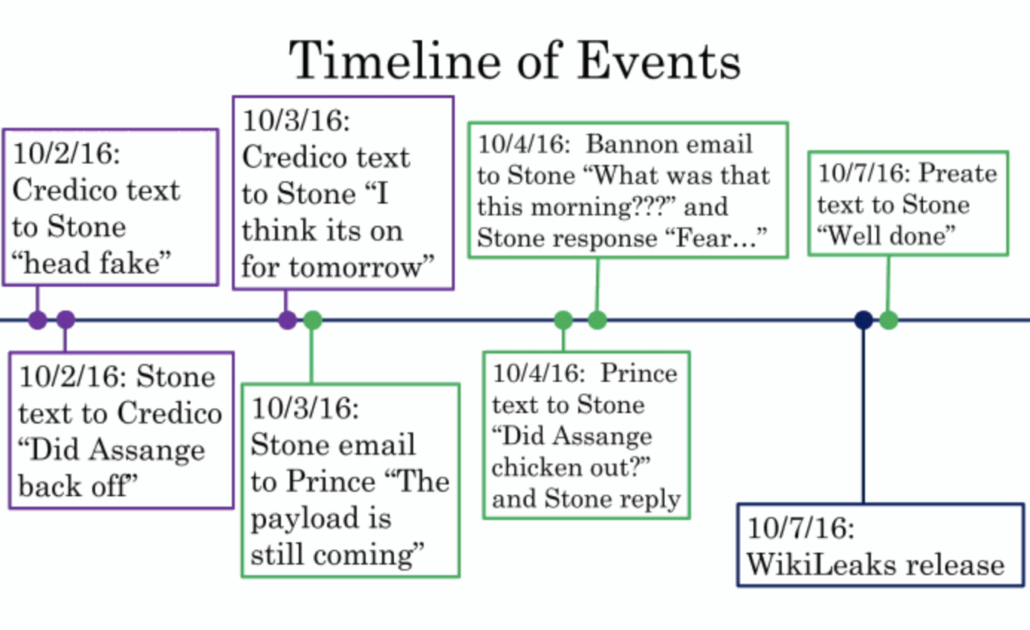
The texts between Stone and Erik Prince on October 4, 2016 are one innocuous example.
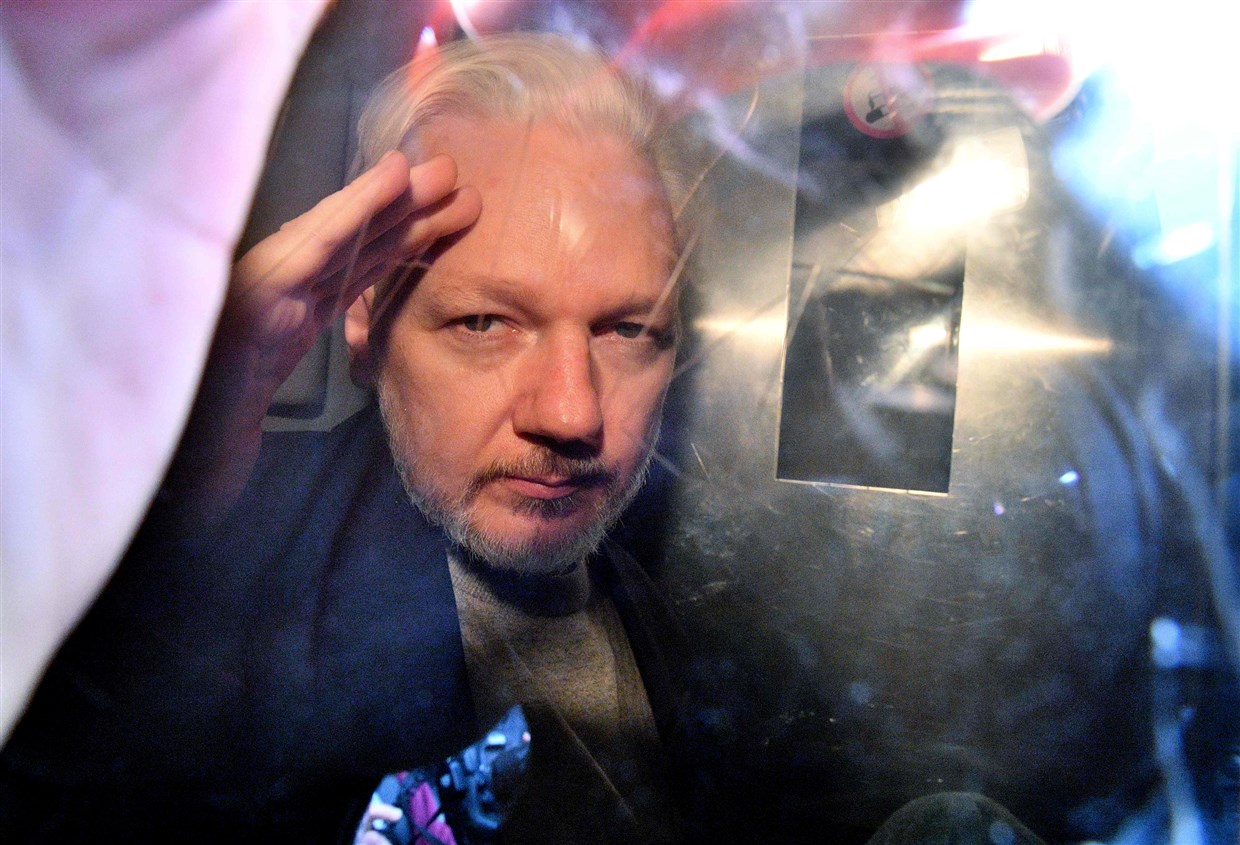
They clearly pertain to WikiLeaks, which is all the prosecution needed to prove — that Stone had communications with people like Prince about advance knowledge of WikiLeaks that he subsequently lied about to cover up. But in the exhibit (which was entered by the FBI Agent; Prince was not called as a witness) there’s a reference — “Yes,” Stone confirmed he had heard more “from London” in the interim 7.5 hours since he had told Prince he was “checking” whether Assange had chickened out, then said, “want to talk on a secure line — got Whataspp?” to something far more interesting.
Affidavits obtained in early 2019 show that Stone first downloaded WhatsApp on October 4, suggesting he downloaded it solely to communicate with Prince (even though Stone already had Signal on his phone).
This is one of the rare areas where the Mueller Report provided more evidence than appeared at the trial. It revealed that Prince testified that,
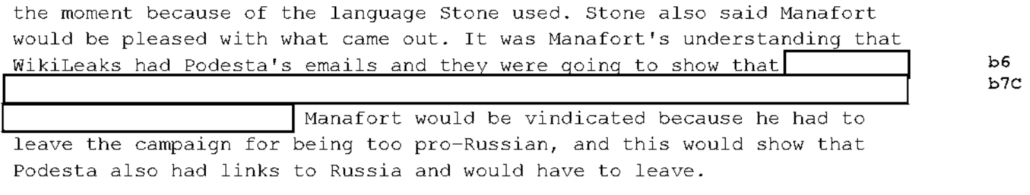
Stone and Prince did speak subsequently, and Stone said that WikiLeaks would release more materials that would be damaging to the Clinton campaign. Stone also indicated to Prince that he had what Prince described as almost “insider stock trading” type information about Assange.
But Prince didn’t testify at the trial, and it would be beyond the scope of what prosecutors needed to prove, and so we didn’t get to hear more about this “insider stock trading” information. Damnit.
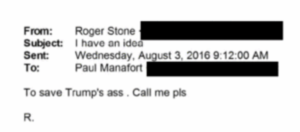
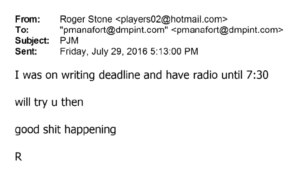
In two other cases, though, prosecutors pointed to more substantive discussions that weren’t clearly labeled as WikiLeaks discussions, but which prosecutors presented as evidence that Stone was talking to the campaign about the upcoming releases. One was the August 3, 2016 email to Paul Manafort where he floated “an idea … to save Trump’s ass.”
As I noted in this post, Manafort seemed to try to hide this email and any follow-up conversation up in an interview with Mueller. And while Stone’s defense challenged whether this email was really related to WikiLeaks, in his closing argument, Jonathan Kravis argued that the plan was to use WikiLeaks releases to discredit Hillary.
On August 3rd, 2016, Stone writes to Manafort: “I have an idea to save Trump’s ass. Call me please.” What is Stone’s idea to save Trump’s ass? It’s to use the information about WikiLeaks releases that he just got from Jerome Corsi. How do know that’s what he had in mind; because that’s exactly what he did. As you just saw, just days after Stone sends this email to Paul Manafort, “I have an idea to save Trump’s ass,” he goes out on TV, on conference calls and starts plotting this information that he’s getting from Corsi: WikiLeaks has more stuff coming out, it’s really bad for Hillary Clinton.
Tactically, introducing the email was not at all necessary. Prosecutors had more than proven that Stone had lied about talking to the campaign. And the SSCI Report makes clear there was a shit-ton of other evidence that made this clear they could have used instead. But for whatever reason, they did include it, tying Stone’s attempts to cover up these conversations with the way Trump won.
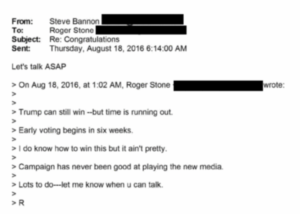
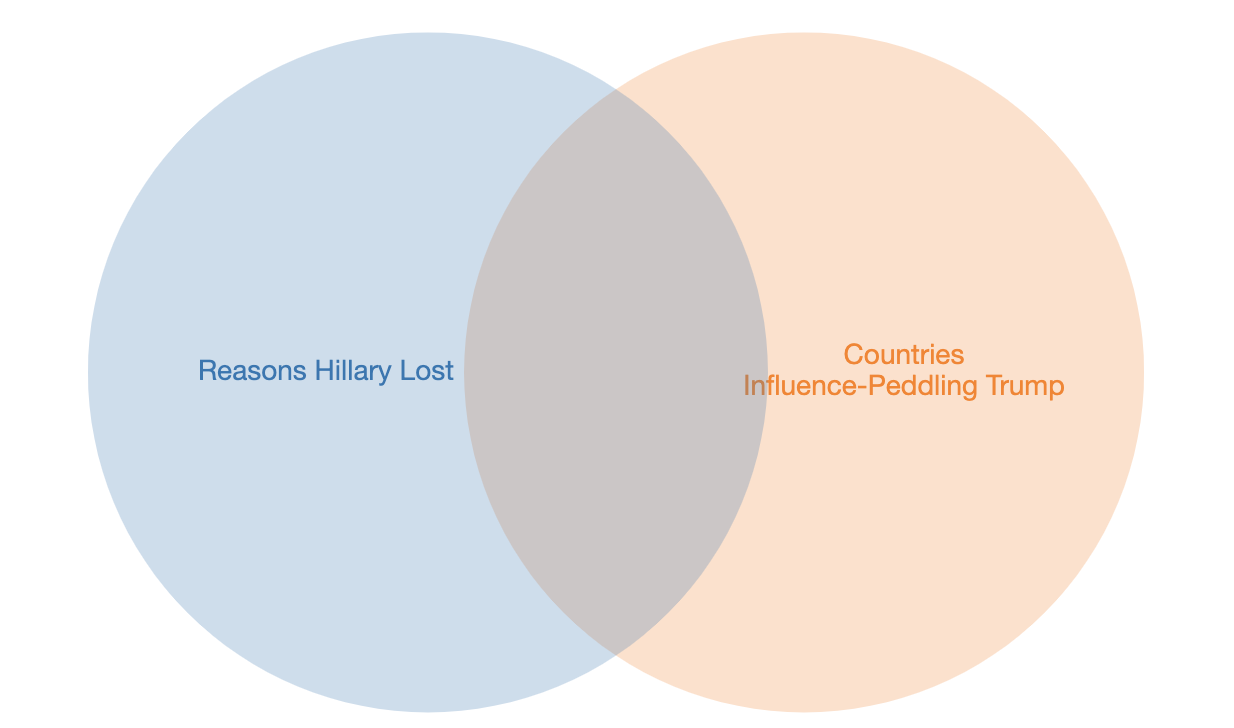
Prosecutors introduced a similar exchange with Steve Bannon, the guy who took over from Manafort weeks later: an August 18, 2016 email exchange where Stone claimed Trump could “still win” … “but it ain’t pretty,” and Bannon responded by asking to talk ASAP.
Manafort didn’t testify at Stone’s trial. But Bannon did. Prosecutors had Bannon sitting there on the stand, forcing him to repeat what he had said to a grand jury earlier in the year, yet they only asked him to say this much about what all this means, in which he begrudgingly admitted he believed this discussion about using social media to win was about WikiLeaks:
Q. At the bottom of this email Mr. Stone states, “Trump can still win, but time is running out. Early voting begins in six weeks. I do know how to win this, but it ain’t pretty. Campaign has never been good at playing the new media. Lots to do, let me know when you can talk, R.” Did I read that correctly?
A. That’s correct.
Q. Then you respond, “Let’s talk ASAP”; am I correct?
A. That’s correct.
Q. When Mr. Stone wrote to you, “I do know how to win this but it ain’t pretty,” what in your mind did you understand that to mean?
A. Well, Roger is an agent provocateur, he’s an expert in opposition research. He’s an expert in the tougher side of politics. And when you’re this far behind, you have to use every tool in the toolbox.
Q. What do you mean by that?
A. Well, opposition research, dirty tricks, the types of things that campaigns use when they have got to make up some ground.
Q. Did you view that as sort of value added that Mr. Stone could add to the campaign?
A. Potentially value added, yes.
Q. Was one of the ways that Mr. Stone could add value to the campaign his relationship with WikiLeaks or Julian Assange?
A. I don’t know if I thought it at the time, but he could — you know, I was led to believe that he had a relationship with WikiLeaks and Julian Assange.
Even though prosecutors didn’t lay out precisely what happened next — something that other evidence suggests may have implicated Jared Kushner — Stone’s team never challenged the prosecution claim that this email and the subsequent exchanges did pertain to WikiLeaks. Perhaps, because they had reviewed Bannon’s grand jury and more recent testimony, they knew how he would respond and thought better off leaving it unchallenged.
Perhaps, too, they didn’t want to have to explain how long this exchange persisted. For example, the Stone affidavits — starting with one obtained after Bannon’s first testimony — showed this particular email exchange lasted two more days, through August 19 and 20 (the day before the Podesta “time in the barrel” tweet).
On August 19, 2016, Bannon sent Stone a text message asking if he could talk that morning. On August 20, 2016, Stone replied, “when can u talk???”
And those discussions may have continued into face-to-face meetings in September.
On September 4, 2016, Stone texted Bannon that he was in New York City for a few more days, and asked if Bannon was able to talk.
[snip]
On September 7, 2016, Stone and Bannon texted to arrange a meeting on September 8, 2016 at the Warner Center in New York.
On September 7, 2016, Bannon texted Stone asking him if he could “come by trump tower now???”
On September 8, 2016, Stone and Bannon texted about arranging a meeting in New York.
This is a lot of back-and-forth to discuss the “the tougher side of politics.”
The August exchange is one of the most substantive things presented at Stone’s trial that doesn’t appear in the Mueller Report.
It does show up, in abbreviated form, in the SSCI Report, but given what else SSCI includes, how the bipartisan report described Trump’s campaign manager eagerly responding to the rat-fucker deserves note. The SSCI Report describes how Gates and Manafort responded to Stone’s proposal — amid these promises of additional WikiLeaks releases — of a plan “to save Trump’s ass” right in the body of the report.
Stone spoke by phone with Gates that night, and then called Manafort the next morning, but appeared unable to connect. 1559 Shortly after placing that call, Stone emailed Manafort with the subject line “I have an idea” and with the message text “to save Trump’s ass.”1560 Later that morning, Manafort called Stone back, and Stone tried to reach Gates again that afternoon. 1561
Bizarrely, the SSCI Report relegates the parallel conversation with Stone involving Steve Bannon, just two weeks later, to a footnote.
1589 (U) Ibid.; Testimony of Steve Bannon, United States v. Stone, pp. 850, 857- 861. In an email on August 18, Stone wrote to Bannon: “I do know how to win this but it ain’t pretty.” Email, Stone to Bannon, August 18, 2016 (United States v. Stone, Gov. Ex. 28). Bannon responded, “Let’s talk ASAP.” Ibid.
This is the guy who was in charge when the Podesta emails dropped. And yet the SSCI Report buries the fact that with Bannon, too, Stone pitched a plan to win using WikiLeaks. Moreover, the SSCI Report doesn’t mention that that plan focused on social media at all, or that discussions about it may have extended over three weeks.
And yet, having buried this pitch from Stone about using social media to win in a footnote, the SSCI Report then provides six pages of detail about how central the Podesta files were to the campaign, including in their social media campaign.
Before it presents that, however, the SSCI Report provides important context to an email exchange involving Stone and Bannon included in the Mueller Report, the Stone indictment, and released at the trial, context none of the other stories provide. It shows that before Breitbart reporter Matthew Boyle emailed Stone to find out what was up with Assange on October 4, Bannon had already reached out to Breitbart’s editors to track the release.
(U) The Trump Campaign tracked Stone’s commentary and the news about WikiLeaks. On October 2, Andrew Surabian, who ran the Campaign’s war room, emailed Stone’s Twitter prediction about a Wednesday release to Bannon, Kellyanne Conway, and the Trump Campaign press team. 1643 On October 3, Dan Scavino emailed the October 3 WikiLeaks Twitter announcement to Bannon.1644 That evening, Bannon reached out to two Breitbart editors, Wynton Han and Peter Schweizer, to ask if they would be awake “to get what he [Assange] has live.”I.645
(U) Separately, also on October 3, Bannon received an email from Matthew Boyle, another Breitbart editor, forwarding Boyle’s correspondence from earlier that day with Stone. In it, Boyle had asked Stone, “Assange-what’s he got? Hope it’s good.” Stone responded, “It is. I’d tell Bannon but he doesn’t call me back.” In his email to Bannon, Boyle advised Bannon to call Stone, and when Bannon said he had “important stuff to worry about,” Boyle replied, “Well clearly he knows what Assange has. I’d say that’s important.”1646
[snip]
(U) Trump was frustrated with the absence of a WikiLeaks release on October 4. Gates recalled that Trump had anticipated something would be released and later asked: “When is the other stuff coming out?”1653
(U) Following the announcement, Bannon complained to Stone by email about the lack of any new releases, asking “what was that this morning???”1654 Bannon wrote to Stone because Stone had said he “knew WikiLeaks and knew Julian Assange.”1655 Stone responded, echoing information he had received from Credico and Assange’s own announcement: “Fear. Serious security concern. He thinks they are going to kill him and the London police are standing done ” [sic]. However-a load every week going forward.” 1656
That Bannon used Breitbart as a cut-out to track what Assange was doing is important for several reasons. Bannon had had to ask the Mercers for permission before leaving Breitbart and joining the campaign, in part to avoid tying the Breitbart brand to any possible Trump loss. In August, Breitbart reporter Lee Stranahan had been in direct contact with Guccifer 2.0 and had gotten early access to a file on Black Lives Matter. Stone would use Breitbart as a platform for some of his own releases after the Podesta emails dropped. And there’s good reason to believe that whatever files Corsi prepped got shared with Breitbart itself.
Plus, in his first interview (one the SSCI Report treats, inexplicably, as credible), Bannon made a slew of claims denying enthusiasm regarding the Podesta release, claims utterly disproven by the documentary evidence. It’s possible Bannon believed he had hidden this enthusiasm from Mueller’s gaze at Breitbart.
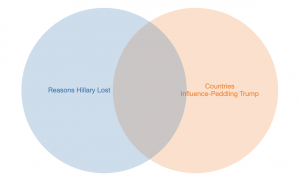
Nevertheless, as the SSCI Report makes clear, there’s a great deal of evidence showing what a concerted focus the campaign paid to the stolen emails, how much of it focused on social media, and how the campaign couldn’t care less that this windfall had come from Russia. (The footnotes of this section of the SSCI Report are particularly valuable for the way they expose precisely who was involved in this campaign.)
(U) Despite the contemporaneous statement by the U.S. Government warning of Russian responsibility for the hacking and leaking of the DNC, DCCC, and Clinton Campaign documents and emails, the Trump Campaign considered the release of these materials to be its “October surprise.”1691 The Trump Campaign’s press team first found out about the WikiLeaks release when it “hit the press” on October 7,1692 and the Campaign quickly turned to capitalize on the Podesta emails: the following morning, October 8, the communications team began compiling information from the release that it could use to attack Clinton. 1693 WikiLeaks information was later integrated with Trump’s tweets, 1694 into his speeches, 1695 and into his press releases. 1696 Other members of the Trump family also scrutinized the news. 1697 And, the Campaign tracked WikiLeaks releases in order to populate a fake Clinton Campaign website, clintonkaine.com. 1698
[snip]
(U) Within the Campaign, there was no policy that governed using materials released by WikiLeaks.1717 To the contrary, the Campaign treated the releases as just another form of opposition research. 1718 Bannon’s view was that “anything negative that comes out [against an opponent] is clearly helpful to a campaign.”1719 According to Stephen Miller, “[i]t would have been political malpractice not to use the WikiLeaks material once it became public.” 1720 Gates described a “growing belief’ within the Campaign that Assange was, in fact, assisting their effort.”1721
(U) Rather than regulating the Campaign’s use ofWikiLeaks materials, Trump praised and promoted WikiLeaks repeatedly in the closing month of the campaign1722:
- (U) October 10, 2016: “This just came out. WikiLeaks, I love WikiLeaks.”
- (U) October 12, 2016: “This WikiLeaks stuff is unbelievable. It tells you the inner heart, you’·gotta read it.”
- (U) October 13, 2016: “It’s been amazing what’s coming out on WikiLeaks.”
- (U) October 31, 2016: “Another one came in today. This WikiLeaks is like a treasure trove.”
- (U) November 2, 2016: “WikiLeaks, it sounds like, is going to be dropping some more . . Ifwe met tomorrow. I’d tell you about it tomorrow.”
- (U) November 4, 2016: “Getting off the plane, they were just announcing new WikiLeaks, and I wanted to stay there, but I didn’t want to keep you waiting. Boy, I love reading those WikiLeaks.”
(U) Using Trump to promote WikiLeaks was a deliberate strategy employed by the Campaign, not only in his remarks, but also on social media. In mid-October, Ivanka Trump tasked the Campaign’s senior officials (including Bannon, Scavino, Stephen Miller and Jason Miller) with preparing two Trump tweets every day linking to WikiLeaks content, which, she said, would help “refocus the narrative.”1723 Trump tweeted direct references to WikiLeaks throughout October and November 2016, including on October 11, 12, 16, 17, 21 (twice), 22, 24, 27 and November 1.1724
[snip]
(U) The Campaign’s preoccupation with WikiLeaks continued until the general election. As the general election approached, Scavino, a member of the communications team who also had a role in administering Trump’s Twitter account during the campaign, 1739 increasingly forwarded updates relating to WikiLeaks to other Campaign officials, using subject lines like · “WIKI ABOUT TO DROP SOME BOMBS … 4 pmE” and “The WikiLeaks BOMB!” and linking to the latest WikiLeaks twitter post or its website. 1740 To one, Donald Trump Jr. responded: “Blow it out.” 1741
1691 (U) FBI, FD-302, Gates 4/19/2018.
1692 (U) Epshteyn Tr., p. 212.
1693 (U) See, e.g., Email, Shah to Ditto, Cheung, J. Miller, and Hicks, October 8, 2016 (DJTFP00019278) (attaching document titled “Wikileaks October 7, 2016 John Podesta Email Release”); Email, Epshteyn to Ellis, October 8, 2016 (DJTFP00019302-19304) (requesting “talkers on this asap” in reference to leaked speech excerpts). In his testimony, Bannon downplayed the relative importance of the WikiLeaks release in light or the Access Hollywood tape. Bannon recalled that the Campaign learned of the tape approximately 60 minutes before it was released, in the middle of debate preparation with Trump. See Bannon Tr., p. 206. According to Bannon, the tape was an “extinction level event,” and precipitated Republican Party efforts to “remove the candidate” the following day .. Ibid., pp. 207-208. Bannon claimed that he not recall finding out about the WikiLeaks release or speaking about it with Trump until the evening after the debate. Ibid., pp. 206-207.
1694 (U) Email, J. Miller to Giuliani, Hicks, Scavino, and S. Miller, October 11, 2016 (DJTFP00019376) (linking to WikiLeaks story in the LA Times).
1695 (U) Email, Gabriel to S. Miller and Ditto, October 27, 2016 (DJTFP00020051) (providing teleprompter script for Springfield, Ohio speech referencing WikiLeaks).
1696 (U) Email, Gates to Bannon, October 27, 2016 (SKB_SSCl-0001369-1370) (stating “This is good and exactly what we need,” and forwarding written Trump statement using WikiLeaks releases to attack Clinton under the subject line, “FW: Donald J. Trump Statement.”).
1697 (U) Email, J. Miller to Shah, et al., October 9, 2016 (DJTFP00024165) (discussing Eric Trump’s question about the WikiLeaks release, “Are we discussing Hillary selling weapons to Isis [sic] as per WikiLeaks email dump?”).
1698 (U) Email, Hemming to Parscale, Bannon, and Hall, “Re: Top Twenty-Five Wikileaks Revelations,” October 15, 2016 (SKB_SSCl-0001528-1530).
[snip]
1717 (U) Bannon Tr., p. 177; S. Miller Tr., p. -110.
1718 (U) For example, Hope Hicks told the Committee: “[E]veryone has opposition research, and this just happened to be available to everyone.” Hicks Tr., pp. 66–67. Kushner described the releases as a “popular topic” that “everyone was talking about.” Kushner II Tr., pp. ’52-54.
1719 (U) Bannon Tr., p. 171-172.
1720 (U) S. Miller Tr., p. 91.
1721 (U) FBI, FD-302, Gates 3/1/2018.
1722 (U) Some of these are reproduced in a video by The Washington Post. “Watch Trump Praise WikiLeaks,” The Washington Post, April 11, 2019. Public tabulations of the number of references in speeches, interviews, rallies, and debates Vary, but place it in excess of 100 mentions. See, e.g., Gabrielle Healy, “Did Trump really mention WikiLeaks over 160 times in the last month of the election cycle?” PolitiFact, April 21, 2017; David Choi and John Haltiwanger, “5 times Trump praised WikiLeaks during his 2016 election campaign,” Business Insider, April 11, 2019.
[snip]
1739 (U) Epshteyn.Tr,, p. 135.
1740 (U) Email, Scavino to Bannon; E. Trump, Trump Jr., Kushner, S. Miller, and Hicks, October 31, 2016 (TRUMPORG_69_016159); Email, Scavino to Bannon, Hicks, Kushner, S. Miller, Trump Jr., and E. Trump, (TRUMPORG_69_016934). See also Email, Scavino to Bannon, Hicks, Conway, and S. Miller, November 4, 2016 (TRUMPORG_69_017232) (“Tweet by WikiLeaks on Twitter”); Email, Scavino to Scavino, November 6, 2016 (TRUMPORG_69 _017455) (“8,263 DNC EMAILS RELEASED” and linking to WikiLeaks tweet); Email, Scavino to Bannon, S. Miller, Kushner, E. Trump, Trump Jr., November 7, 2016 (TRUMPORG_ 69 _ 017463) (subject “Wiki – CIIlCAGO PROTESTS COSTS” and linking to WikiLeaks documents).
1741 (U) Email, Trump Jr. to Scavino, Bannon, E. Trump, Kushner, S. Miller, and Hicks, October 31, 2016 (TRUMPORG _ 69_016164).
In light of Bannon’s meetings with Stone, his trial testimony, and the details of how the campaign exploited the stolen emails, the most obvious explanation for Stone’s “how to win this but it ain’t pretty” comment is that this response to the Podesta drop was prepared starting in August (which makes the timing of Stone’s “time in the barrel” comment, coming in the wake of the Stone and Bannon discussions, all the more intriguing).
Particularly given the timing of Stone’s meeting or meetings with Bannon in NY, that’s not the only possibility. The other ones are far more damning.
But the trial and affidavits both tell stories that suggest there’s far more to Stone’s proposals, to two consecutive Trump campaign managers, on how to win the campaign. The SSCI Report provides one answer, the most obvious answer, for what that plan was. And yet the SSCI Report, which frowns at the campaign for its embrace of emails stolen by Russia but consistently backs off the most damning conclusions regarding Trump, fails to connect whether there’s a tie between Stone’s promise, which it hides in a footnote, and the massive effort to capitalize on the emails.
Or worse.
The movie Rashomon demonstrated that any given narrative tells just one version of events, but that by listening to all available narratives, you might identify gaps and biases that get you closer to the truth.
I’m hoping that principle works even for squalid stories like the investigation into Roger Stone’s cheating in the 2016 election. This series will examine the differences between four stories about Roger Stone’s actions in 2016:
- The Mueller Report
- The Stone prosecution
- The SSCI Report
- The affidavits from the investigation
As I noted in the introductory post (which lays out how I generally understand the story each tells), each story has real gaps in one or more of these areas:
- While the Mueller Report made it clear Trump’s pardon dangles to keep details of his conversations with Roger Stone secret amounted to obstruction, it didn’t tell just just how many conversations they had
- Rather than telling us whether, how, and why Roger Stone optimized the release of John Podesta’s emails on October 7, 2016, the Mueller Report instead gave us Jerome Corsi slapstick
- Just one story presents the significant amounts of evidence suggesting that on August 14, 2016, when he started a file called “Podesta,” Jerome Corsi had or knew the contents of the Podesta files that would become public on October 11, 2016
- The later stories focus on Podesta, rather than the evidence that Stone learned of the hack-and-leak while the burglary was still ongoing
- Stone pitched both Manafort and Bannon on a way to win ugly–but none of the Stone stories tell us what that was
- Trolling for Russia
- The “highest levels of government” attempt to shut down an investigation into Julian Assange
- Guccifer 2.0 as go-between
My hope is that by identifying these gaps and unpacking what they might say about the choices made in crafting each of these stories, we can get a better understanding of what actually happened — both in 2016 and in the investigations. The gaps will serve as a framework for this series.