Trials of Insurrectionists are Not Simply an American Thing
While Donald Trump is defending himself in a NY courtroom (with other pre-trial battles being fought in other courtrooms), and while hundreds of January 6th insurrectionists sit in prison serving their sentences after their trials, and while other “Stop the Steal” related indictments move toward their own courtrooms, and while SCOTUS Justice Samuel Alito blames his wife for flying a US flag upside down for several days in the immediate aftermath of the January 6th insurrection, news of other trials of accused insurrectionists comes in from Deutsche Welle:
The most high-profile of three trials linked to a far-right coup plot begins on Tuesday in a newly erected courtroom on the outskirts of Frankfurt. The defendants are alleged to be the 10 ringleaders of a group led by German aristocrat Heinrich XIII Prince Reuss, and stand accused of preparing to commit high treason and of membership in a terrorist organization.
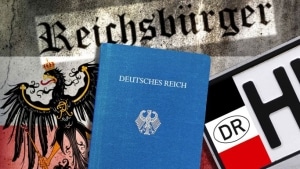
All the suspects, part of the so-called “Reichsbürger” movement, were allegedly plotting to overthrow the German government. They were allegedly planning to storm the German parliament and detain prominent politicians, including Chancellor Olaf Scholz, Foreign Minister Annalena Baerbock and conservative opposition leader Friedrich Merz.
The Reichsbürger, or “citizens of the Reich,” reject Germany’s postwar state, claiming it was installed and controlled by the Allied powers who won World War II.
[snip]
The alleged military arm of this group has been facing court in Stuttgart since April 29. A further eight suspected members of the alleged association will have to stand trial in Munich from June 18 . . .
There’s more at the link, but a lot of it sounds disturbingly familiar:
- Weapons: in raids during December 2022, “more than 380 firearms were confiscated, along with almost 150,000 pieces of ammunition.”
- Support in the national parliament: “Birgit Malsack-Winkemann, a judge and former representative of the far-right Alternative for Germany (AfD) party in the federal parliament, the Bundestag, . . . was allegedly to become justice minister after the coup.”
- Dream of support within the military
- Fantastic conspiracy theories about the deep state: “The prosecution has alleged that Reuss and his supporters believe that a “deep state” runs Germany and was planning to murder hundreds of children and teenagers. The group apparently believed the floods in Germany’s Ahr Valley in 2021 were an attempt to cover up murders already committed by flooding old government bunkers. Among Reuss’ supporters, there was talk of 600 dead children.”
- Anger at COVID restrictions and plans to kidnap political leaders
- Ties to Russia and plans for a future alliance.
The Guardian makes the parallels even more clear in their distillation of the 621 page indictment:
On trial are the group’s alleged ringleader, a self-styled aristocrat estate agent known as Prince Heinrich XIII, his Russian girlfriend, and seven other founding members including a former policeman and a former judge who is now an MP for the far-right AfD party.
According to federal prosecutors, the group planned to storm the Reichstag in Berlin with armed support via its paramilitary wing, to arrest members of the Bundestag, and to parade a shackled Olaf Scholz on German television in the hope and expectation of winning ordinary Germans around to their coup.
Call me crazy, but that sounds like a group of the January 6th plotters, doesn’t it?
Could it have worked? That’s apparently not a high possibility, but they were certainly heavily invested in making it happen:
Police say the group had amassed more than half a million euros in gold and cash, as well as hundreds of firearms, tens of thousands of rounds of ammunition and explosives. They had acquired satellite phones to stay in touch after the paramilitary wing had carried out plans to cut off the national communications networks and electricity.
The group had waited for “day X” to start the coup, with one believing the signal was the death of Queen Elizabeth II. When police stormed the house of one member, he shot at them, injuring two police officers.
Sophie Schönberger, an expert in constitutional law at Heinrich Heine University in Düsseldorf, and co-author of the book Reichsbürger, said: “The chances of such a putsch actually succeeding were not all that high, but it could have unleashed a considerable level of violence and was capable of sending shock waves through the system.”
CNN did an explainer of the Reichsbürger in March 2023, which included this:
Werner Patzelt, a political scientist and former professor at TU Dresden, believes the Reichsbürger is less of a “movement” but rather “a loosely coupled network of political stupids who believe that, or at least behave as if, the Federal Republic of Germany does not exist.”
“They claim that Germany is still an occupied country under US control, or a business enterprise registered in Frankfurt,” he told CNN.
“From such fictitious ‘facts’ they derive both a ‘right’ not to pay taxes and penalties, or to establish ‘provisional political authorities.’
“Much of this is operetta-like. In some cases, however, criminal energy goes hand in hand with political nonsense, leading to attacks on financial or police officers.”
Followers refuse to cooperate with the German state in a number of ways including not paying taxes or choosing to print their own currency and identity cards.
Tobias Ginsburg is a German journalist who reported undercover on Germany’s far-right scene.
“You meet people there of all walks of life,” Ginsburg said. “I met the stereotypes, but also normal people, the dentist from downtown, someone working with the tax revenue service, just normal people. Some had no idea what they had entered.”
What we are fighting in the US is not specific to the US. Whether these groups are coordinated (Russia, anyone?) or simply people in both countries being filled with nationalist gingoism, hatred and fear of The Other(s), and nostalgic views of a triumphant history that never was, those who dream fascist fantasies and work to bring them to life are alive and well around the world.
What bmaz says about the Trump trials here is true about the Reichsbürger trials in Germany. In and of themselves, these trials are not “magic bullets” that will immaculately solve the problems presented by these folks. “We tried them, found them guilty, and now everything is peachy keen” is no way to declare an insurrection over. While the trials are necessary part of addressing these problems, true solutions need to go much deeper and need to address the attractiveness of the AfD in Germany and the MAGA wing of the GOP in the US.



 public domain
public domain