Yesterday, Magistrate Judge Bruce Reinhart found that, “the Government has not met its burden of showing that the entire [Trump search warrant] affidavit should remain sealed.” He ordered DOJ to provide a sealed version of proposed redactions for the warrant affidavit for Trump’s search by August 25 at noon.
Two days after the search of Mar-a-Lago I did a post laying out the likely content of what’s in that search warrant (which pretty accurately predicted what we’ve seen since). Because a warrant affidavit is one of the best ways to show how DOJ and the FBI think of the events of the last 18 months, I wanted to do a second version including all the things we have learned since.
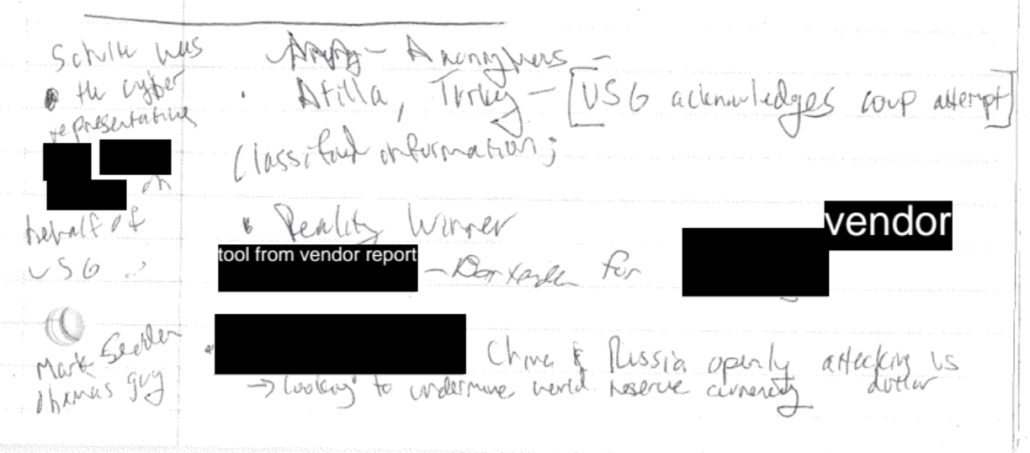
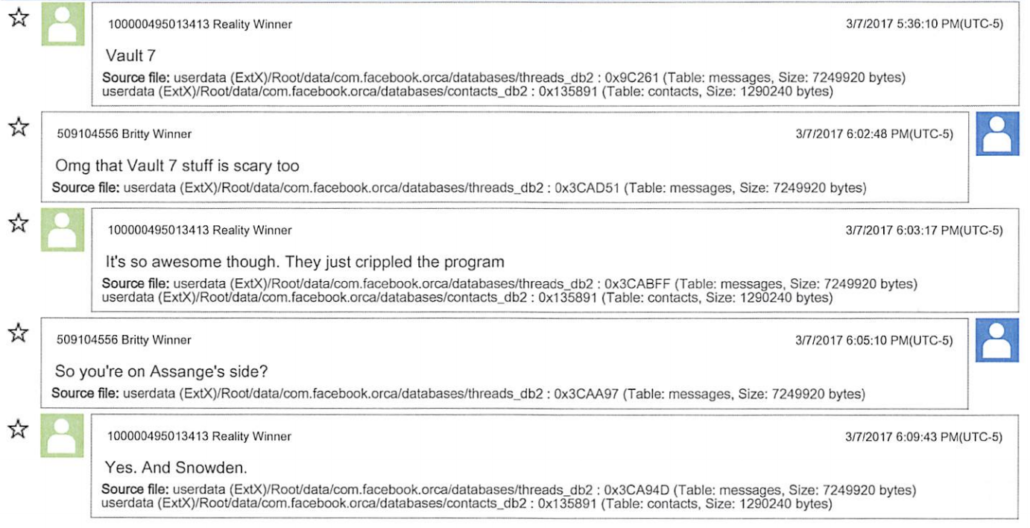
For comparison, here are the warrants for Reality Winner and Josh Schulte, both of which were also, at least in part, warrants for a 793 investigation. Here are warrants to search Roger Stone and Oath Keeper Jeremy Brown’s houses, both Federal searches in Florida related to investigations conducted in DC (the search of Brown’s house even found allegedly classified documents, albeit only at the Secret level). Stone’s showed probable cause for a different part of the obstruction statute. Here’s the warrant Robert Mueller’s team used to get Michael Cohen’s Trump Organization emails from Microsoft.
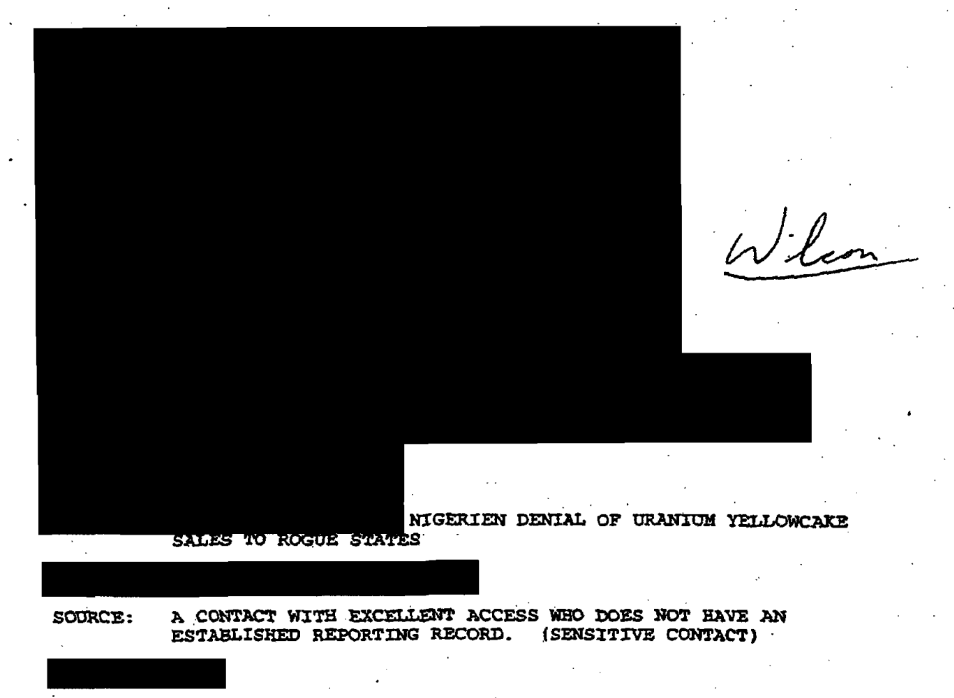
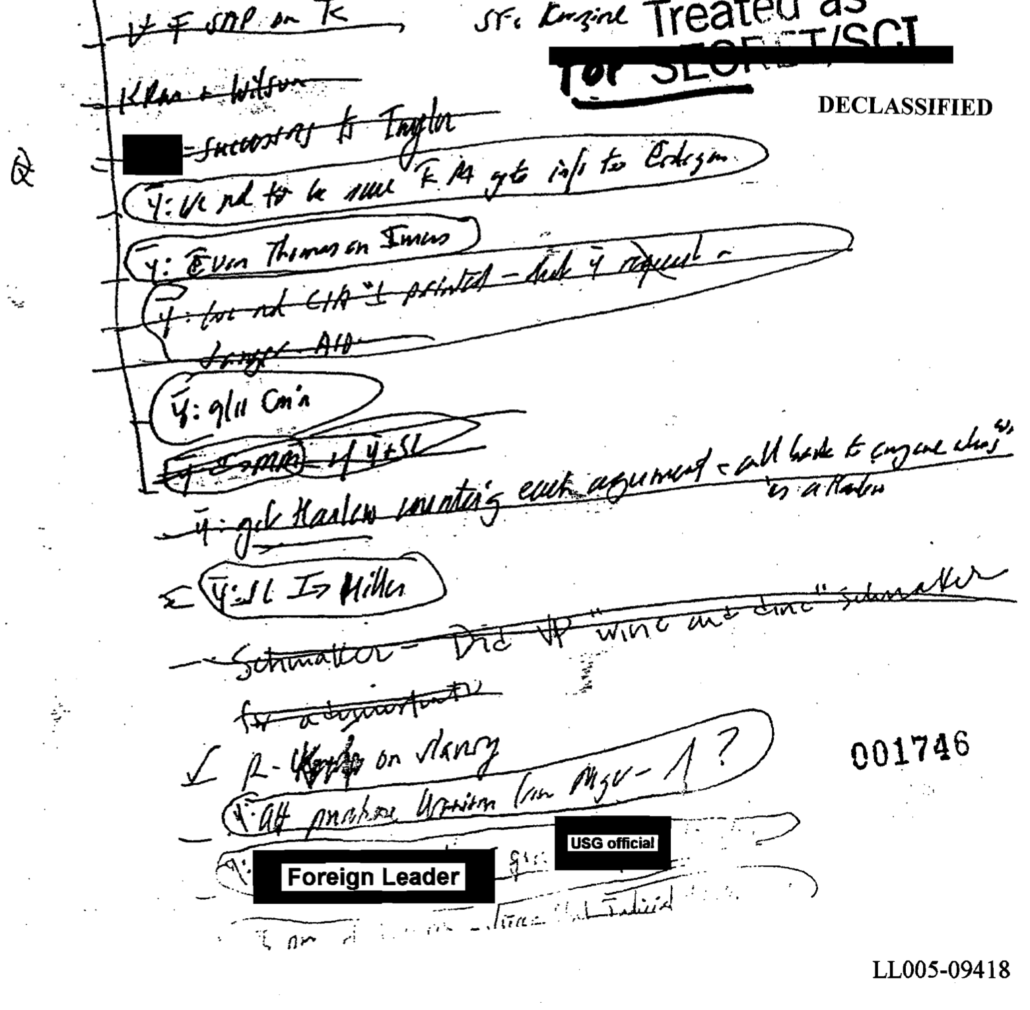
Cover Sheet to Warrant Application
[link]
This cover sheet shows that DOJ swore out the affidavit to Magistrate Judge Bruce Reinhart over WhatsApp, who signed it on August 5.
It describes applying for a warrant to search for evidence of crimes and for contraband (a reference to the illegally possessed Presidential records). It doesn’t permit the seizure of property used in the commission of a crime so, unsurprisingly, the FBI didn’t have authority to seize Mar-a-Lago.
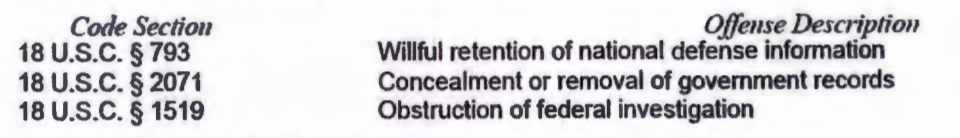
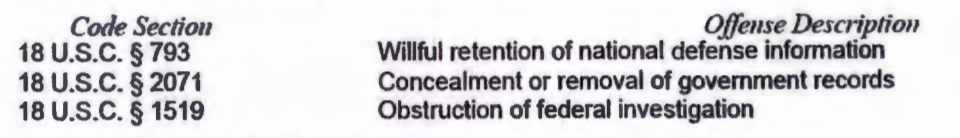
The cover sheet describes the three crimes under investigation this way.
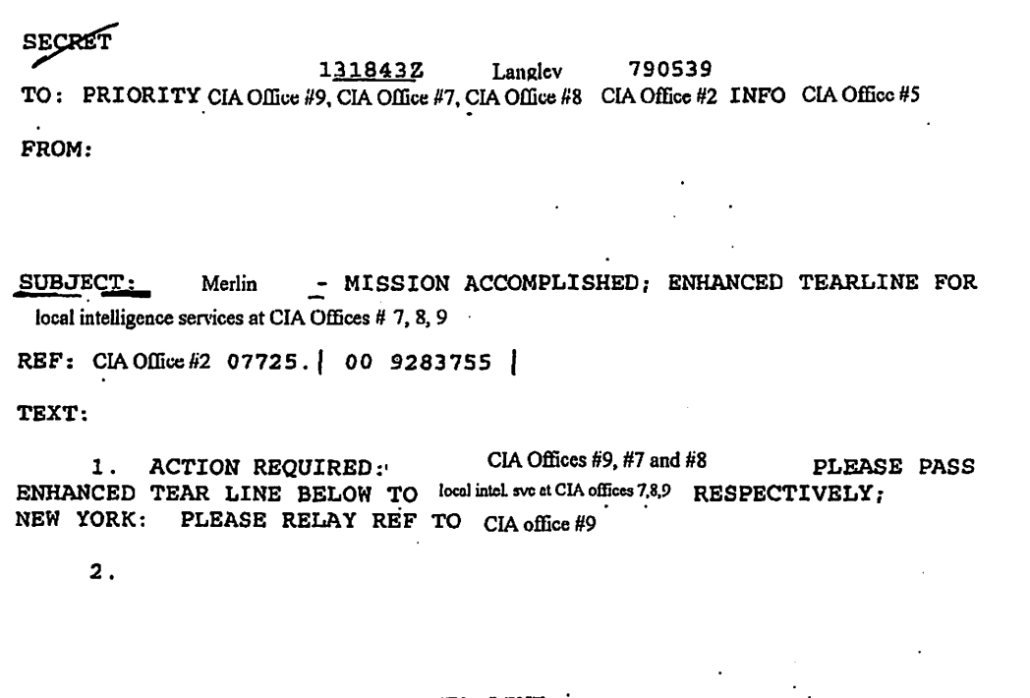
The Search Warrant
[link]
The search warrant notes the docket number 22-mj-8332 that the entire country has been watching for 10 days now.
The search warrant authorizes the FBI to conduct a search of 1100 S. Ocean Blvd., Palm Beach, FL.
It was signed by Reinhart, who was the Duty Magistrate, at 12:12PM on August 5.
The warrant gave the FBI two weeks, until August 19, to conduct the search and limited the search to daytime hours (defined as 6AM to 10PM, which Trumpsters often complain amounts to a pre-dawn raid).
Attachment A
[link]
Attachment A describes Mar-a-Lago as a “resort, club, and residence” with approximately 58 bedrooms and 33 bathrooms. The warrant permitted the FBI to search all parts of Mar-a-Lago accessible to Trump (whom they refer to as FPOTUS) and his staff, except those currently occupied (at the time of the search) by Members or guests. It mentioned the “45 Office” explicitly and storage rooms, but did not describe the storage room at the center of much reporting on the search.
Attachment B
[link]
Attachment B authorized the FBI to seize “documents and records constituting evidence, contraband, fruits of crime, or other items illegally possessed” in violation of 18 USC 793, 18 USC 2071, or 18 USC 1519.
This post describes the search protocol authorized in Attachment B, with nifty graphic.
Return
Search warrant forms have a return form (describing what was seized) included in them. But here, the FBI provided that list to Trump in the form of two receipts, one signed by a Supervisory Special Agent, and one signed by a Special Agent; I’ve dubbed the latter the “CLASS receipt,” because all the classified documents described are included on that one.
The receipt lists:
- 27 boxes, one of which is described as leatherbound; 11 are described to contain documents marked classified
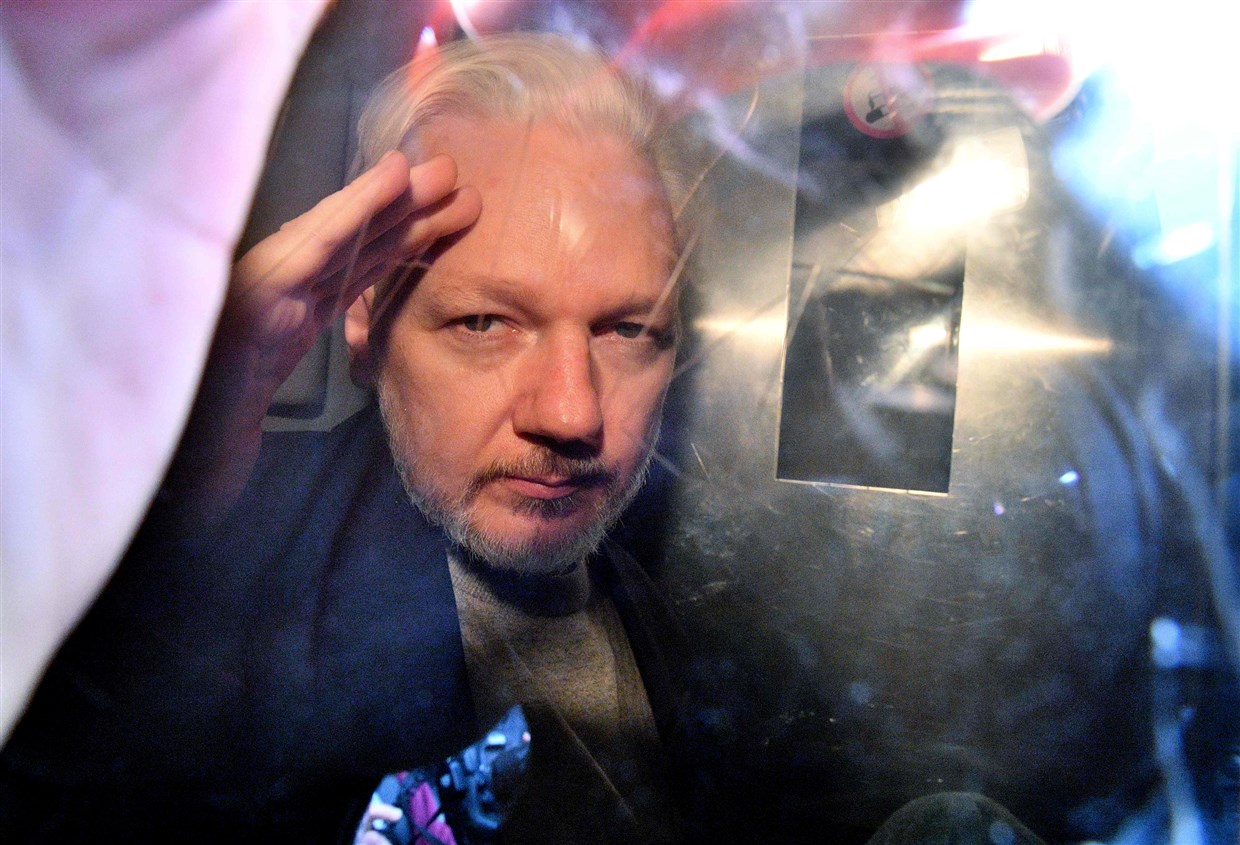
- Executive grant of clemency for Roger Stone
- Potential Presidential record
- 2 binders of photos
- Handwritten note
- Other documents catalogued on the SSA receipt
See these two posts for more on the significance of the two different receipts.
Christina Bobb signed for both receipts at 6:19PM on August 8.
Affidavit
This would start with:
- Several paragraphs describing the affiant’s background and training
- An assertion that the affiant believed there was probable cause that the FBI would find evidence of violations of 18 USC 793, 18 USC 2071, and 18 USC 1519 at Mar-a-Lago.
Particularly given the novel legal issues implicating a search of the former President, I think there’s likely a section describing the statutes involved. It’s likely to include:
Note: If there’s a version of this statutory language, it may be among the things DOJ would acquiesce to releasing, particularly if it implied that Trump was under investigation for stealing nuclear documents. But they might be unwilling to do that if they’re not yet sure they’ve gotten all known nuclear documents back.
Then there’d be a section describing who was involved (the Roger Stone warrant has such paragraphs). There will be a paragraph about Trump that looks like:
Donald J. Trump (Former President of the United States, FPOTUS) is a businessman who owns and resides at 1100 S. Ocean Blvd., Palm Beach, FL. From January 20, 2017 at 12:00PM until January 20, 2021 at 12:00PM, he was the President of the United States. He ceased exercising the constitutional authorities of the President at 12:00PM on January 20, 2021. On February 5, 2021, the current President of the United States, Joe Biden, discontinued classified briefings for FPOTUS.
In addition, there are likely descriptions of the National Archives and its statutory duties.
There may be descriptions of Patrick Philbin, Pat Cipollone, Mark Meadows (all of whom were involved in negotiations with NARA over retrieving the documents), anyone caught on surveillance video entering or exiting the storage closet, of Kash Patel and John Solomon (including past security concerns raised about both), and the Trump lawyers involved in the June meeting.
There may be a paragraph describing MAL in more depth. It might describe the SCIF used during Trump’s presidency and its apparent removal. It might describe the arrest and prosecution of Yujing Zhang, who breached MAL and might include other known foreign intelligence targeting of MAL. It might describe Trump’s refusal to use secure facilities at MAL, including a 2017 meeting with Shinzo Abe, though it would likely rely on public reports for this, not classified intelligence. It might describe the tunnels underneath and — and the public availability of historic diagrams of them. It might describe the known employees at MAL, including any foreign citizens. Finally, it might describe both the terms of membership and the ease with which others could access the golf club.
Timeline
The rest is probably a timeline of the investigation. The following known details are likely to appear.
On December 30, 2020, DOJ provided Trump a binder of material from the Russian investigation.
On January 8, 2021, Mike Ellis attempted to retain a compartmented NSA report for White House archives, initially refusing efforts to return it.
On January 14, 2021, the White House returned the compartmented NSA report to NSA.
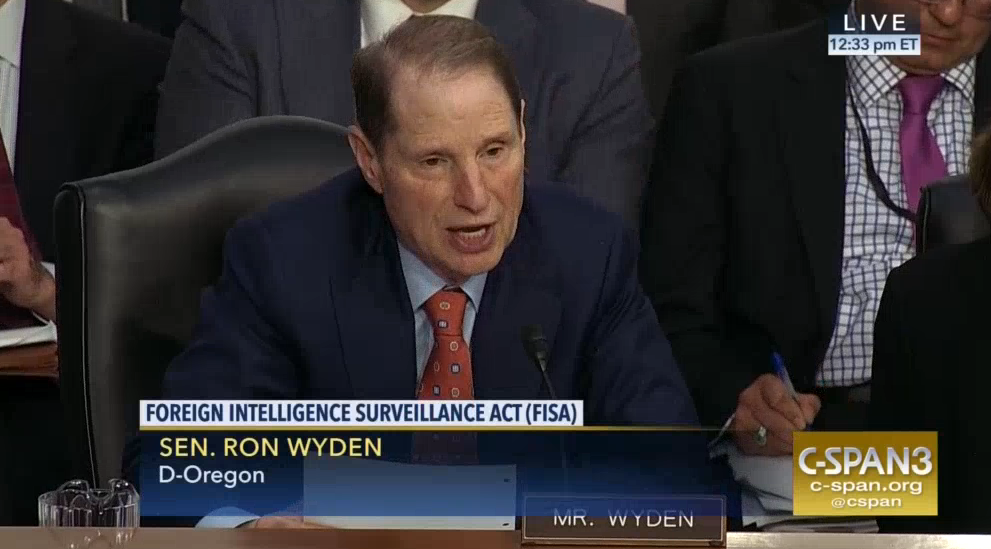
On January 17, 2021, the FBI provided a list of continuing objections to Trump’s declassification of Crossfire Hurricane materials.
On January 19, 2021, via letter to Archivist of the United States David Ferriero, FPOTUS designated (among others) Pasquale (Pat) Cipollone and Patrick Philbin as his representatives with the NARA.
On January 19, 2021, FPOTUS wrote a letter authorizing the declassification of records pertaining to FBI’s investigation into Russian ties with FPOTUS’ campaign that had not yet been declassified. Patel later described the materials to include:
transcripts of intercepts made by the FBI of Trump aides, a declassified copy of the final FISA warrant approved by an intelligence court, and the tasking orders and debriefings of the two main confidential human sources, Christopher Steele and Stefan Halper, the bureau used to investigate whether Trump had colluded with Russia to steal the 2016 election.
Patel’s description appears to conflict with Trump’s order, which explicitly, “does not extend to materials that must be protected from disclosure pursuant to orders of the Foreign Intelligence Surveillance Court.”
On January 20, 2021, Meadows sent “The Attorney General” a memo, citing the January 19 order from FPOTUS, ordering “the Department must expeditiously conduct a Privacy Act review under the standards that the Department of Justice would normally apply, redact material appropriately, and release the remaining material with redactions applied.”
On January 20, 2021, FPOTUS ceased exercising the authorities of the President of the United States.
On January XX, records deemed to be the final production of Presidential Records arrived at NARA.
The affidavit would describe the inventorying process and then describe known documents that were not included.
- Love letters from Kim Jong Un
- Altered map of Hurricane Dorian
It would also include a description of evidence of document destruction, including any evidence those records pertained to a Congressional investigation, impeachment, or a criminal investigation.
Starting on May 6, 2021, NARA General Counsel Gary Stern communicated with Philbin regarding the missing records. [This will cite the date of each communication and quote anything that captures Trump’s refusal to return the documents.]
Having not secured identified records, starting in Fall 2021, Stern communicated with Trump attorney (probably Cipollone) to arrange turning over the records.
October 18, 2021: Trump sues to prevent the Archives from complying with January 6 Committee subpoena.
November 10, 2021: Judge Tanya Chutkan denies Trump’s motion for an injunction against NARA. (While it wouldn’t appear in the affidavit, in recent days Paul Sperry has claimed that Trump withheld documents to prevent NARA from turning them over to the January 6 Committee.)
On December XX, 2021, XX informed NARA certain missing records had been located.
December 9, 2021: DC Circuit upholds Judge Chutkan’s decision releasing Trump records to the January 6 Committee.
On January 17, 2022, NARA retrieved 15 boxes of Records from 1100 S. Ocean Blvd, Palm Beach, FL.
January 19, 2022: SCOTUS upholds Chutkan’s decision.
On January 31, 2022, NARA completed an initial inventory of the retrieved documents. It discovered over 100 documents with classification markings, comprising more than 700 pages. Some include the highest levels of classification, including Special Access Program (SAP) material.
On February xx (possibly February 8), 2022, NARA reported FPOTUS’ failures to comply with the Presidential Records Act to the Department of Justice and requested an investigation.
DOJ and FBI likely conducted interviews between February and May, which would be listed.
On April 11, 2022, Biden’s White House Counsel instructed NARA provide FBI access to the 15 boxes of materials returned from Mar-a-Lago.
On April 12, 2022, NARA instructed the Trump team of that decision, and informing him that the FBI would start to access the documents on April 18.
On April XX, Trump’s attorneys ask the White House counsel for more time before the review of the documents; Biden extends the date to April 29.
On May 5, 2022, Corcoran proposed reviewing the records at NARA.
On May 5, 2022, Kash Patel made public claims that the contents of materials returned to NARA had been declassified, describing that FPOTUS wanted to release,
information that Trump felt spoke to matters regarding everything from Russiagate to the Ukraine impeachment fiasco to major national security matters of great public importance — anything the president felt the American people had a right to know is in there and more.
FBI conducted early interviews during this period, likely including Philbin, Scott Gast, Derek Lyons, and Cipollone, and possibly Mark Meadows. Philbin and Cipollone would have described their own inspections of records, including their knowledge that identified missing records had been at MAL when they had conducted records searches.
FBI would include multiple interviews of people describing Trump saying the Presidential Records belonged to him.
On May 10, 2022, Acting Archivist informed Evan Corcoran the FBI would get access to the records on May 12.
On May 11, 2022, FBI subpoenaed Trump for documents remaining at Mar-a-Lago bearing classification marks.
On May 12, pursuant to a subpoena, FBI accessed the 15 boxes turned over in January.
From May 16-18, FBI conducted a preliminary review of. the documents and discovered:
- 67 Confidential documents
- 92 Secret documents
- 25 Top Secret documents
- Documents marked HCS, FISA, ORCON, NOFORN, and SI
- Handwritten notes
On May XX, 2022, DOJ subpoenaed FPOTUS for any remaining documents bearing classification marks.
Surveillance video from this period, later obtained with a subpoena, showed people moving documents in and out of the storage room. The people and dates would be included.
On June 3, 2022, Jay Bratt and three investigators met with Evan Corcoran and Christina Bobb to collect the subpoenaed materials.
- FPOTUS joined the meeting and acknowledged the effort to retrieve classified materials.
- Bobb and Corcoran provided XX documents marked with classification marks.
- One of the lawyers signed an attestation that all classified documents had been turned over.
- Bratt informed Bobb and Corcoran all records covered by the Presidential and Federal Records Act were US government property.
- Bratt informed Bobb and Corcoran about the regulations guiding storage of classified records.
- Bratt and investigators inspect storage facility, find storage facility fails to meet required standards for storage.
On June 8, Bratt emailed Corcoran. He said, in part, that,
We ask that the room at Mar-a-Lago where the documents had been stored be secured and that all the boxes that were moved from the White House to Mar-a-Lago (along with any other items in that room) be preserved in that room in their current condition until further notice
It’s likely either at the meeting on June 3 or in the email, Bratt also informed Corcoran that the storage closet did not comply with CFR guidelines.
On June 9, Corcoran wrote saying only, “I write to acknowledge receipt of this letter.”
On June 19, FPOTUS sent a letter to NARA designating Patel and Solomon as representatives to access “Presidential records of my administration.”
NARA, possibly Gary Stern, likely informed DOJ of the designation of Patel and Solomon and (probably) Trump’s reference to “Presidential records,” generally, not records at NARA.
On June 22, DOJ subpoenaed surveillance video of the storage closet for a 60-day period. Analysis of the video showed uncleared people entering in and out of the storage closet.
DOJ likely had follow-up interviews after the Bratt meeting and the surveillance video return, in part to identify who had access to the storage closet and to identify documents believed to remain outstanding.
The affidavit would include a description of known documents that remain extant, including documents that were altered or mutilated (perhaps transcripts of Trump’s meetings with Russia) and known classified documents, including those pertaining to nuclear weapons.
Finally, the affidavit would include a conclusion stating that all this amounts to probable cause that Trump was in possession of documents that were covered by the PRA, some subset of which were believed to be classified and some other subset of which had either been hidden or damaged in an effort to obstruct either this or other investigations.
emptywheel Trump Espionage coverage
Trump’s Timid (Non-Legal) Complaints about Attorney-Client Privilege
18 USC 793e in the Time of Shadow Brokers and Donald Trump
[from Rayne] Other Possible Classified Materials in Trump’s Safe
Trump’s Stolen Documents
John Solomon and Kash Patel May Be Implicated in the FBI’s Trump-Related Espionage Act Investigation
[from Peterr] Merrick Garland Preaches to an Overseas Audience
Three Ways Merrick Garland and DOJ Spoke of Trump as if He Might Be Indicted
The Legal and Political Significance of Nuclear Document[s] Trump Is Suspected to Have Stolen
Merrick Garland Calls Trump’s Bluff
Trump Keeps Using the Word “Cooperate.” I Do Not Think That Word Means What Trump Wants the Press To Think It Means
[from Rayne] Expected Response is Expected: Trump and Right-Wing DARVO
DOJ’s June Mar-a-Lago Trip Helps Prove 18 USC 793e
The Likely Content of a Trump Search Affidavit
All Republican Gang of Eight Members Condone Large-Scale Theft of Classified Information, Press Yawns
Some Likely Exacerbating Factors that Would Contribute to a Trump Search
FBI Executes a Search Warrant at 1100 S Ocean Blvd, Palm Beach, FL 33480
The ABCs (and Provisions e, f, and g) of the Espionage Act
Trump’s Latest Tirade Proves Any Temporary Restraining Order May Come Too Late
How Trump’s Search Worked, with Nifty Graphic
Pat Philbin Knows Why the Bodies Are Buried
Rule of Law: DOJ Obtained Trump’s Privilege-Waived Documents in May
The French President May Be Contained Inside the Roger Stone Clemency
Which of the Many Investigations Trump Has Obstructed Is DOJ Investigating?
The Known and Likely Content of Trump’s Search Warrant